Rhymetec is proud to announce the promotion of Kyle Jones to the newly created role of Chief AI Officer (CAIO). Since joining Rhymetec on October 17, 2022, Kyle has been a driving force behind our rigorous security standards. His elevation to the executive leadership team marks a bold new chapter for Rhymetec as we solidify our position as a deeply tech-forward organization dedicated to pioneering the future of cybersecurity operations.
Meeting the AI Uprising Head-On
The rapid, unprecedented uprising of artificial intelligence has fundamentally altered how industries operate. For forward-thinking organizations, AI is no longer a peripheral tool; it is a foundational shift. Navigating this new era requires a rare blend of leadership, someone who deeply understands the uncompromising world of information security, yet possesses the cutting-edge technical mastery required to harness advanced AI responsibly.
Kyle Jones is uniquely qualified to bridge these two worlds. Already a highly respected industry professional holding the prestigious CISSP (Certified Information Systems Security Professional) credential, Kyle anticipated the AI wave early. Over the last few years, he has focused heavily on the practical applications of machine learning, recently completing a suite of advanced certifications from IBM, including their Generative AI Engineering Specialization, as well as rigorous frameworks covering Generative AI Applications with RAG and LangChain, and LLM Architecture.
This powerful combination of elite security expertise and advanced AI engineering makes Kyle the ideal visionary to guide Rhymetec into a hyper-efficient, tech-driven future.
Driving Internal Efficiency to Elevate the Customer Experience
At Rhymetec, our technology investments are always guided by a single, customer-centric mission: How can we make our clients’ security and compliance journeys smoother, faster, and more robust? As Chief AI Officer, Kyle’s mandate is not isolated to a development sandbox. Instead, he has been actively working across every corner of the company: collaborating cross-functionally with Sales, Customer Success, Marketing, Operations, and Security teams. By architecting and deploying sophisticated internal AI systems and intelligent workflows, Kyle is transforming how Rhymetec operates from the inside out.
For our customers, this internal optimization delivers immediate, tangible competitive advantages:
- Accelerated Project Timelines: By leveraging internal AI efficiencies to automate repetitive data synthesis and administrative bottlenecks, our security experts can execute projects faster than ever before.
- Supercharged Response Times and SLAs: Optimized internal workflows mean our teams can exceed service level agreements (SLAs), providing lightning-fast communication and support when clients need it most.
- High-Value Strategic Focus: With AI handling manual, time-consuming processes behind the scenes, Rhymetec’s experts can dedicate their energy to what matters most: delivering tailored, high-level strategic counsel to protect your business.
While these internal advancements serve as our primary efficiency engine, they also naturally lay the foundational groundwork for our broader technological ecosystem, including the future evolution of Rhymetec’s internal platforms.
"We are living through a tech revolution, and staying ahead means being willing to disrupt your own workflows for the benefit of your clients. Kyle has been the mastermind behind our internal AI evolution. Appointing him as Chief AI Officer ensures Rhymetec remains an industry trailblazer, delivering a premier, tech-forward experience to every business we secure,"
— Justin Rende, founder and CEO of Rhymetec.
Charting the Path Forward
In his executive role, Kyle will oversee the holistic integration of intelligent systems across Rhymetec while maintaining an ironclad commitment to risk management. His core focus areas include:
- Cross-Functional Orchestration: Partnering with department leaders to audit operational friction points, designing custom internal AI systems that eliminate redundancies and maximize output.
- SLA and Timeline Optimization: Measuring and continuously tuning internal AI implementations to ensure they directly correlate to faster project delivery and enhanced service accuracy for clients.
- AI Platform Strategy & Development: Leading the strategic roadmap, architecture, and development of Rhymetec’s next-generation AI platform, focused on scalable automation, secure multi-tenant infrastructure, and AI-driven cybersecurity operations ahead of its planned late 2026 release.
- Enterprise AI Governance: Developing a world-class internal AI risk management framework, establishing rigorous data-handling policies that guarantee all internal AI utilization aligns perfectly with global privacy and cybersecurity best practices.
By appointing a Chief AI Officer with Kyle’s unique caliber of security and machine learning expertise, Rhymetec is doing more than just adopting technology, we are redefining how modern cybersecurity services are delivered.
The federal government is one of the largest buyers of cloud services in the world, representing a massive opportunity for Cloud Service Providers (CSPs). But to do business with federal agencies, you need to meet their stringent security standards. Enter FedRAMP.
If you are a cloud provider looking to unlock unprecedented growth, achieving FedRAMP compliance is your golden ticket. However, the framework is known for being complex, rigorous, and ever-evolving with the highly anticipated rollout of the FedRAMP 20x modernization initiative.
Here is your modern guide to understanding exactly what is FedRAMP, navigating its requirements, and preparing your business for the sweeping FedRAMP 20x changes on the horizon.
What is FedRAMP?
The Federal Risk and Authorization Management Program (FedRAMP) is a United States federal government-wide compliance program. It provides a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services.
Instead of agencies conducting redundant, individual security assessments for the same cloud product, FedRAMP establishes a "do once, use many times" framework. Once your cloud service is certified, any federal agency can leverage your solution with confidence, saving time and resources for both the government and your business.
How FedRAMP Authorization Works
At Rhymetec, we know firsthand that the road to FedRAMP can feel overwhelming. We streamline each phase to reduce friction and accelerate your journey to compliance. Typically, the authorization process involves:
- Scope Assessment: Defining your system boundaries and determining the exact scope of your cloud environment.
- Gap Assessment & Planning: Assessing your current controls against FedRAMP requirements and building a project plan to close any gaps.
- Policy & Control Implementation: Creating and operationalizing all required FedRAMP-aligned policies, procedures, documentation, and technical safeguards.
- Audit Preparation & Authorization: Coordinating with a Third-Party Assessment Organization (3PAO) to complete the formal assessment and achieve your certification.
What are the FedRAMP Requirements?
FedRAMP requirements are based on the National Institute of Standards and Technology (NIST) Special Publication 800-53. To meet these requirements, organizations must develop comprehensive documentation and implement strict technical controls.
Key deliverables include:
- A complete System Security Plan (SSP) detailing how every control is implemented.
- A Security Assessment Plan (SAP) and Security Assessment Report (SAR) generated during the 3PAO audit.
- A Plan of Action and Milestones (POA&M) to track and remediate any vulnerabilities.
- Policy and procedure development across all NIST control families.
- A robust continuous monitoring framework to maintain compliance post-certification.
CMMC vs. FedRAMP: What’s the Difference?
If your organization is navigating the federal compliance landscape, you’ve likely heard of CMMC (Cybersecurity Maturity Model Certification) alongside FedRAMP. While both frameworks are rooted in NIST standards and share the goal of protecting government data, they apply to very different types of businesses:
- FedRAMP applies to Cloud Service Providers (CSPs) that want to sell their cloud software or infrastructure to federal agencies.
- CMMC applies to defense contractors and subcontractors within the Department of Defense (DoD) supply chain to ensure they are protecting Controlled Unclassified Information (CUI).
The two frameworks collide when a defense contractor uses a cloud service to store or process CUI. Under CMMC mandates, that contractor can only use a cloud service if the CSP is either fully FedRAMP Moderate Certified or has achieved 100% FedRAMP Moderate Equivalency (which requires a rigorous 3PAO assessment of its own).
In short: If you provide cloud services, you need FedRAMP. If you provide goods, services, or research to the DoD, you need CMMC.
Check out our complete guide on CMMC vs. FedRAMP here.
Understanding FedRAMP Levels (and New Naming Conventions)
FedRAMP categorizes cloud systems based on the potential impact of a security breach.
Important Update: If you haven't been following the latest FedRAMP updates, the terminology is shifting. To align with other industry frameworks and reduce market confusion, the term FedRAMP "Authorized" is changing to FedRAMP "Certified." Furthermore, the traditional impact levels are transitioning to a streamlined Class-based system.
Here is how the new naming conventions break down:
- Class A (Formerly FedRAMP Ready): Indicates that a 3PAO has attested to your readiness and you are listed on the FedRAMP Marketplace, making it easier for an agency to sponsor you.
- Class B (Formerly FedRAMP Low): Designed for systems where the loss of confidentiality, integrity, or availability would have a limited adverse effect on an agency.
- Class C (Formerly FedRAMP Moderate): The most common level. This applies to systems where a breach would have a serious adverse effect on an agency's operations or assets.
- Class D (Formerly FedRAMP High): Reserved for the government’s most sensitive, unclassified data (e.g., law enforcement, emergency services, financial systems) where a breach could have severe or catastrophic consequences.
How Long Does FedRAMP Certification Take?
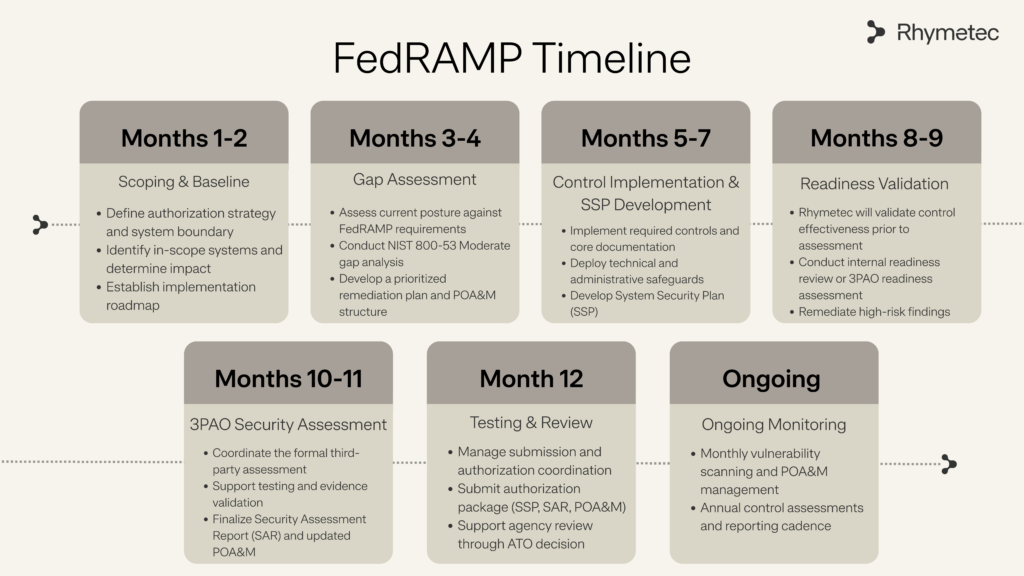
The timeline to achieve FedRAMP certification varies significantly depending on your organization's current security posture, the complexity of your system, and the Class (A-D) you are pursuing. Generally, the entire process, from initial scoping to final certification, can take anywhere from 9 to 12+ months.
A note on existing frameworks: If you already hold a SOC 2 or ISO 27001 certification, you have a great foundation. There is notable overlap in governance and basic security policies. However, FedRAMP requires a much more rigorous, technical implementation of controls. Having SOC 2 will speed up your gap analysis, but expect to invest significant engineering time to meet FedRAMP’s exacting architectural and technical standards.
How Does FedRAMP Pricing Work?
Achieving FedRAMP certification is a strategic investment. Costs are typically broken down into three buckets:
- Engineering & Infrastructure: Upgrading your cloud environment to meet stringent federal standards (e.g., dedicated GovCloud environments, FIPS-validated encryption).
- Consulting & Preparation: Partnering with experts to handle gap assessments, policy creation, and SSP development.
- 3PAO Audit Fees: Paying the accredited third-party auditor to conduct the official assessment.
While the upfront cost is higher than commercial certifications, the ROI is substantial. A FedRAMP certification essentially unlocks the entire federal marketplace for your sales team.
What's Changing: FedRAMP 20x
As the cyber landscape evolves, so does FedRAMP. The upcoming "FedRAMP 20x" updates focus on modernizing the framework, improving automation, and accelerating the authorization timeline.
Here is what the FedRAMP 20x modernization means for cloud providers today:
A Shift to "FedRAMP Validated”
While legacy authorizations are shifting to the "FedRAMP Certified" label, 20x introduces the new FedRAMP Validated designation. This proves to agencies that your security isn't just a point-in-time audit, but a continuously monitored and automatically enforced reality.
No Agency Sponsor Required
Traditionally, CSPs had to secure a federal agency sponsor before beginning the authorization process, a massive hurdle. FedRAMP 20x opens a direct-to-PMO authorization path, removing the sponsor bottleneck.
Automation Replaces Prose
Instead of writing hundreds of pages explaining your security controls, 20x focuses on machine-readable data and automated continuous monitoring feeds. If you already have a strong commercial security framework in place, you can inherit many of those policies to reduce redundant documentation.
Unprecedented Speed to Market
By removing the red tape and relying on automated validation, the 20x initiative has slashed approval times during its pilot phases. What once took well over a year is actively being streamlined down to a matter of months or even weeks. These changes aim to get secure, commercial cloud technologies into the hands of federal agencies faster than ever. However, making the leap to a fully automated, machine-readable compliance posture requires serious technical maturity.
What This Means for Your Strategy
For cloud service providers, these changes mean that getting FedRAMP Certified is becoming a more structured, logical process, but the technical bar remains as high as ever.
Your strategy should focus on proactive preparation. Don't wait for a federal agency sponsor to ask for your SSP to start building it. Begin your scoping and gap assessment now. Determine whether your target market requires Class B, C, or D certification, and build a roadmap to close those technical gaps.
Most importantly, don't do it alone. Navigating the transition from commercial security to federal compliance requires specialized expertise.
Ready to Speak to a FedRAMP Consultant?
At Rhymetec, we deliver the clarity, documentation, and expertise needed for successful certification. With a decade of trusted delivery and a 100% in-house team (never outsourced), we help you every step of the way, making an otherwise complex process clear, structured, and achievable.
From gap assessment and policy development to control implementation and 3PAO audit coordination, we simplify the journey so you can focus on unlocking new growth.
Contact us today to speak with one of our compliance experts.
As technology, software, and AI become deeply ingrained in our everyday operations, cybersecurity threats are evolving at an unprecedented pace. The need for proactive, strategic cybersecurity leadership has never been greater. The role of the vCISO, or Virtual Chief Information Security Officer, has emerged to meet this demand.
But what is a vCISO, and what do they do exactly?
In this guide, we'll break down the roles and responsibilities of a virtual CISO and help you decide if hiring one is the strategic move your business needs to stay secure and compliant.
What is a vCISO?
A Virtual Chief Information Security Officer (vCISO)—often referred to as CISO as a service—is a highly skilled cybersecurity executive hired to manage and lead an organization’s information security program remotely or on a contract basis. A vCISO provides top-tier cybersecurity expertise, strategic guidance, and hands-on support without the overhead required for a full-time, in-house CISO. Typically, a vCISO acts as a fractional member of an organization’s executive team, working closely with the board of directors, executive management, and any internal security personnel.
vCISOs are armed with a deep understanding of business objectives, modern cloud-native architectures, and compliance standards, helping to bridge the gap between technical execution and business strategy. They help organizations develop intelligent security strategies, establish continuous monitoring controls, assess and manage risks, and ensure regulatory compliance.
Traditionally, organizations relied exclusively on in-house CISOs to manage their security posture. However, with the rapidly changing landscape of AI-driven cyber threats, along with the complex compliance demands of modern businesses, the flexible, scalable vCISO role has become a critical asset.
What Does a vCISO Do?
Acting as the anchor between strategy and execution, a vCISO wears multiple hats—advisor, strategist, and guardian—to ensure an organization's digital assets remain impenetrable and compliant with strict security and privacy regulations.
Every organization has unique cybersecurity and compliance requirements. Depending on the level of support required, a vCISO typically performs a strategic combination of the following tasks:
- Strategic Security Planning: At the heart of a vCISO's responsibilities is devising a security strategy that aligns with your business goals. By assessing your technology stack, business demands, and data security requirements, a vCISO identifies vulnerabilities and architects defense mechanisms to keep the business resilient.
- Risk Assessment and Management: Virtual CISO services include conducting thorough risk assessments, prioritizing threats, and crafting detailed mitigation plans rooted in industry best practices and global telemetry.
- Compliance and Regulatory Oversight: With global data protection regulations constantly shifting, and complex new AI frameworks emerging, companies must stay vigilant. A vCISO ensures your organization is not only compliant with privacy standards like GDPR today but is also prepared for recent regulatory changes, stricter data governance, and the frontier of AI compliance, such as navigating the EU AI Act or achieving ISO 42001 certification.
- Incident Response Management: A vCISO ensures you have a robust incident response plan ready. When a threat materializes, they take charge, manage the crisis, and minimize operational damage.
- Security Awareness Training Programs: Cybersecurity isn't just about tools; it's about people. A vCISO fosters a security-first culture, organizing regular training so every team member acts as an active line of defense.
- Addressing Stakeholder Security Requests: B2B organizations need to prove a solid security posture to win new business. A vCISO assists in these high-stakes conversations, tackling lengthy security questionnaires to speed up the sales cycle, attract investment, and build absolute trust with potential clients.
"At its core, cybersecurity... will be about establishing and maintaining trust. This includes demonstrating to customers, regulators, and internal stakeholders that the organization in question consistently upholds its controls. Trust will become a competitive differentiator."
— Justin Rende, Founder and CEO of Rhymetec
The 6 Cybersecurity Trends That Will Shape 2026
What Are The Advantages of Hiring a vCISO?
Cost-Effective Expertise
Startups and Small to medium enterprises can't always afford the multi-six-figure salaries of top-tier CISOs. A vCISO provides the exact same executive-level expertise without the traditional employment costs and overhead.
Unbiased Advice
External vCISOs come to your organization without legacy biases or internal politics. Their fresh, objective perspective can unveil vulnerabilities that an internal team might overlook.
Extensive Experience
An in-house CISO generally focuses on a single environment, while a vCISO manages a diverse portfolio of clients across various industries. Having navigated the hurdles that other businesses face at different growth stages, a vCISO is able to use their past expert experience to foresee and prevent issues long before they impact your operations.
Niche Expertise
Many vCISOs specialize in a particular sector. For example, Rhymetec primarily works with SaaS companies and startups. We have current, firsthand experience solving the exact compliance and data privacy issues facing cloud-native organizations.
Scalability and Flexibility
A startup’s cybersecurity requirements are vastly different from those of an enterprise, and your security posture must scale rapidly alongside your revenue. vCISOs allow for true scalability, adapting to your changing requirements without the need to continuously expand your in-house headcount.
Rhymetec client, Orum, a live-conversations platform experiencing hyper-growth. Orum handles vast amounts of client CRM data to power their AI-driven dialing technology. They needed an adaptive security co-pilot to help their solo internal security expert achieve SOC 2 Type 2 compliance, unlocking enterprise-level sales opportunities, and lay the groundwork for ISO 27001 to support international expansion.
Rather than slowing down to hire more full-time staff, Orum leveraged a Rhymetec vCISO. This provided them with tailored security services and expertise that offered full-time expert guidance during critical audit windows and part-time maintenance in between.
"We were moving fast, and I needed someone to move fast with me. Leveraging your services has helped me speed up, not slow down."
— Rolland Miller, Vice President of Security and Compliance, Orum
Access to Highly Skilled Mentorship
With a vCISO, businesses tap into a wealth of strategic knowledge that can mentor and elevate the existing IT and security staff.
Signs a vCISO is Right for Your Business
Deciding between a full-time CISO and a vCISO can be challenging. Based on our experience, here are the core indicators that a vCISO is the right choice:
- Your budget can’t accommodate a full-time CISO: If your budget doesn’t have room for an executive salary plus overhead, a vCISO is your smartest bet for securing top talent efficiently.
- You only need help with a specific task or framework: If your goal is strictly to implement a specific compliance framework (like SOC 2 or ISO 27001), hiring a fractional CISO is far faster and more efficient than onboarding a new executive.
- Your team needs cybersecurity mentorship: If your employees don’t need a full-time manager but could benefit from the strategy, goal-setting, and operational mentorship of an expert, a vCISO is a highly effective way to develop your team.
- You need an expert to get you started: Building an InfoSec program from scratch is a massive undertaking. Because vCISOs build security programs continuously for multiple organizations, they bring a level of speed and efficiency that traditional CISOs cannot.
- You don’t have enough work for a full-time CISO: If you’re unsure if you have 40 hours of executive security work a week, hiring a vCISO to assess your needs and lay the groundwork is a smart way to make the decision.
- You’re an early-stage startup: Startups benefit immensely from vCISOs because the services scale precisely with the company's trajectory.
"One strategy tech leaders can use to maximize digital transformation outcomes is to automate wherever possible. By embedding automation into repetitive or manual processes... leaders can dramatically cut hours spent on a process, reduce errors and redirect talent to higher-value initiatives. Smart automation amplifies impact without adding headcount or overspending."
— Metin Kortak, CTO, Rhymetec
Digital Transformation: How To Drive High Impact With A Low Budget
vCISO vs CISO: What’s the Difference?
A vCISO is a seasoned expert who offers strategic guidance and leadership on a fractional basis. A CISO is a traditional, full-time employee who works exclusively for one organization on-site. The vCISO approach gives modern companies the flexibility to access world-class cybersecurity strategies and leadership without the massive salary and overhead of a full-time executive.
Why Are vCISOs Becoming So Popular?
The barrier to entry for cyberattacks is lowering due to AI, while global data privacy regulations are only getting stricter. Today, cybersecurity is a board-level priority, especially as modern startups build exclusively in cloud-native architectures where continuous monitoring is the default.
Despite this urgency, the cybersecurity workforce is facing a massive talent gap. Recent ISACA reports show that over half of organizations feel understaffed in cybersecurity professionals and struggle to retain qualified talent.
When you combine sophisticated threats, complex compliance requirements, and a global talent shortage, it’s clear why the demand for vCISOs is skyrocketing. A vCISO bridges the talent gap by acting as an intelligent co-pilot, offering defense mechanisms that are effective, adaptable, and completely aligned with the future of digital trust.
Looking for a vCISO? We can help.
Contact Rhymetec to learn how our vCISO services can help you build a bespoke security program, navigate emerging frameworks, and win enterprise trust, all without the overhead of a full-time executive hire.
With 88% of organizations now using AI in at least one business function, the race to innovate has never been faster. But as these applications scale, they drastically expand the web application attack surface. Without the right security frameworks, deploying generative AI can introduce severe model, prompt, and integration risks that traditional security tools simply weren't built to catch.
This guide breaks down what every organization needs to know about LLM penetration testing, how it differs from standard security assessments, and how to build a resilient AI ecosystem that supports compliance and growth.
What Is LLM Penetration Testing And Why Is It Different?
LLM penetration testing is a specialized security assessment designed to evaluate how generative AI systems behave under adversarial conditions.
Traditional web application penetration testing was designed to uncover vulnerabilities like SQL injection, cross-site scripting (XSS), and server misconfigurations. It focuses heavily on static infrastructure.
LLM penetration testing evaluates the logic, behavior, and integration layers of generative AI systems. Traditional automated scanners like Burp Suite or Nessus were not designed to test the probabilistic nature of AI. Instead of attacking the infrastructure alone, LLM testing uses adversarial tactics to manipulate prompts, bypass guardrails, and attempt sensitive data extraction.
To understand the scope of an LLM penetration test, it helps to break down the core components of the AI ecosystem:
- The Model: The underlying backend intelligence (e.g., Claude, OpenAI, Gemini).
- The Agent: An API-hooked action the AI can perform, such as sending an email, querying a database, or creating a support ticket.
- The Message Prompt: The user-facing text input, which serves as the primary entry point for most attack vectors.
Even if you are utilizing a highly secure, third-party foundational model, your specific implementation layer, like system prompts, plugins, agents, and data handling workflows, creates new points of exposure.
The Regulatory Push for AI Security
Compliance frameworks and international regulations are rapidly catching up to generative AI. Security is no longer just a best practice; it is a legal requirement.
The EU AI Act is already fundamentally shifting how companies approach AI risk. With Article 5 prohibitions in effect and the strict compliance deadline for high-risk models looming on August 2, 2026, companies handling EU resident data must prove their AI systems are safe, unbiased, and secure.
In addition to European regulations, comprehensive LLM penetration testing supports emerging governance frameworks like the NIST AI Risk Management Framework (AI RMF) and ISO/IEC 42001. Delivering structured reporting that demonstrates validated safety testing is now a prerequisite for passing enterprise procurement reviews and maintaining executive confidence.
Top AI Vulnerabilities You Need to Assess
A robust LLM penetration test aligns directly with the OWASP Top 10 for Large Language Model Applications. Because LLMs are probabilistic, meaning the exact same prompt can generate different answers on different days, testing requires highly manual, creative, and persistent adversarial prompt engineering.
A thorough assessment should target these critical vulnerabilities:
- Prompt Injection: The most common attack vector, where an attacker uses clever wording to bypass instructions, override guardrails, or force the system to execute unintended commands.
- Sensitive Information Disclosure: Manipulating the model to reveal restricted content, PII, or sensitive data about other users.
- System Prompt Leakage: Tricking the AI into revealing its own backend instructions, guardrails, or safety features, allowing attackers to map out loopholes.
- Vector Embedding Weakness (RAG Assessments): Exploiting a Retrieval Augmented Generation (RAG) pipeline to force the AI to retrieve unauthorized internal data.
- Unbounded Consumption: Testing system limits to ensure an attacker cannot abuse the AI to trigger massive cloud infrastructure costs or a Denial-of-Service (DoS) state.
How Rhymetec Approaches LLM Penetration Testing
At Rhymetec, our methodology combines adversarial prompt engineering, automated red-teaming, and expert manual logic validation to assess risk across your entire generative AI lifecycle. Each engagement aligns with the OWASP Top 10 for Large Language Model Applications, ensuring your testing reflects the latest standards in generative AI security.
Rather than a one-size-fits-all approach, we scope our testing to match your specific AI architecture:
Evaluating Core Models and Chat Interfaces: For standard public-facing or internal assistants, we focus heavily on foundational vulnerabilities. Using manual, creative prompt injection, we test the system's resilience against sensitive data leakage, system prompt extraction, and unbounded consumption attacks aimed at exhausting your cloud resources.
Assessing RAG Pipelines and Internal Knowledge Bases: If your application retrieves contextual data from an internal database (Retrieval-Augmented Generation), the stakes are significantly higher. We conduct deep-dive assessments to identify vector embedding weaknesses, ensuring your system cannot be manipulated into bypassing guardrails to access or expose compartmentalized proprietary data.
Validating Agents and Integrations: As your AI ecosystem grows, so does your attack surface. We thoroughly evaluate agentic workflows, such as API-hooked actions that allow the AI to send emails, query databases, or create tickets, to ensure tool and plugin access stays strictly within intended controls.
Expanding the Scope: To ensure complete security from the database to the chat interface, we highly recommend pairing your LLM assessment with a standard Web Application Penetration Test. This guarantees that your surrounding implementation layer does not become the weak entry point for attackers.
Insights That Speed Up Innovation
Your AI systems deserve more than surface-level testing. By actively hunting for prompt injection, jailbreak risks, and guardrail evasion before public exposure, you can strengthen trust in your customer-facing AI systems without degrading performance.
At the end of a Rhymetec engagement, you receive an executive presentation and a comprehensive report featuring validated prompt-based exploits, prioritized severity ratings, and prescriptive remediation guidance.
Looking for LLM Penetration Testing Services? We can help.
Accelerate your AI deployment without compromising security. Contact Rhymetec to learn how our LLM Penetration Testing services can secure your generative AI architecture and keep your innovation moving forward.
NEW YORK, Apr. 7, 2026 – Rhymetec, the industry leader in cloud security that provides innovative cybersecurity, compliance, and data privacy services to modern-day SaaS businesses, today announced a partnership as an Official Small Business Partner of the Brooklyn Nets.
This Small Business Partner Program empowers New York-based businesses by unlocking collaboration opportunities with one of the NBA’s most iconic teams. The collaboration merges Rhymetec’s mission to provide seamless, premium security partnerships with the Brooklyn Nets' dedication to community and team excellence.
Partnership Highlights
- Barclays Center Presence: Rhymetec will showcase its brand at Barclays Center, home of the Nets, reaching fans through high-impact digital signage and dynamic gameday branding.
- Community and Networking: Rhymetec will participate in exclusive experiential moments and networking events designed to empower and strengthen the local New York business ecosystem.
- Enhanced Digital Exposure: The partnership extends Rhymetec's reach year-round through targeted social media marketing and digital exposure on non-gamedays, transforming team pride into a powerful community asset.
For Rhymetec, the partnership represents continued growth and expansion of its presence in New York, where the company was founded in 2015. What began as a penetration testing company serving local startups has grown into a global cybersecurity and compliance partner supporting more than 1,000 organizations worldwide.
"In 2015, I was riding around New York City on my bike, delivering Google Homes to the offices of companies I wanted to work with. To go from those local roots to partnering with an iconic New York institution like the Brooklyn Nets is a massive milestone for our team," — Justin Rende, founder and CEO of Rhymetec.
What started in New York City with a single client has quickly grown into a global operation. Today, Rhymetec has served more than 1,000 clients, ranging from early-stage startups to established enterprises. Rhymetec removes cloud security complexities so innovative companies can grow faster and achieve their goals without limits.
Through the Brooklyn Nets Small Business Partnership, Rhymetec reinforces its commitment to the city where it all began, bringing its message of seamless, proactive cybersecurity to the NBA arena stage.
About Rhymetec
Rhymetec delivers premium cybersecurity and data privacy solutions for modern SaaS businesses, combining human expertise with innovative technology. The company builds, deploys, and manages offensive security, compliance, and data privacy programs directly within clients' environments, enabling organizations to move fast, operate confidently, and focus on what matters most. With Rhymetec as a partner, companies can move freely, grow without limits, and focus on building the business they envision. For more information, visit www.rhymetec.com and follow Rhymetec on LinkedIn.
In the early stages of building a SaaS company, security and regulatory requirements often take a back seat to product development and user acquisition. But as you scale, ignoring SaaS compliance quickly becomes a major liability. Without the right frameworks in place, enterprise deals stall, procurement reviews drag on, and investor confidence drops. Compliance is no longer just a box to check, it’s a prerequisite for growth.
This guide breaks down what every startup needs to know about navigating compliance frameworks, overcoming common scaling challenges, and building a security program that actively drives your business forward.
Defining SaaS Compliance (And Why It’s Different From Traditional IT Compliance)
Traditional IT compliance was created for companies that owned their infrastructure and operated within a fixed network. These types of environments were easier to protect in many ways because data remained inside physical systems.
Your modern SaaS company now works in a shared environment where customer data moves through hosted platforms, third-party integrations, and multiple geographic regions. Control depends heavily on coordination between the provider and the SaaS company, not on direct ownership of the systems involved.
This model requires constant attention to how data flows, where it is stored, and who can access it. Cloud vendors manage the infrastructure, but SaaS providers remain responsible for how their own applications handle customer information.
Modern frameworks such as SOC 2 and ISO 27001 reflect this reality. They assess whether a company’s security and privacy controls operate within a constantly changing environment. A mature SaaS compliance program aligns daily operations with controls and allows companies to scale while maintaining trust with customers and partners.
Why Compliance Matters For SaaS Companies
Compliance is no longer a nice-to-have for SaaS companies. Enterprise customers, investors, and partners now expect proof that their data is being handled securely and in line with recognized standards.
Voluntary frameworks like SOC 2 and ISO 27001, along with laws such as GDPR, have become prerequisites for closing deals, especially in regulated industries or when selling across international markets.
Compliance also serves to strengthen operational resilience. A well-defined security program reduces the risk of breaches, downtime, and regulatory penalties, ultimately driving better control over areas that often expand faster than a startup’s internal oversight can keep up such as vendor relationships.
Compliance provides SaaS providers a substantial competitive advantage. Companies with more mature security postures move faster through procurement reviews, shorten sales deals, and retain customer trust.
In short, compliance signals reliability. It shows customers that your company is built for longevity and with security top-of-mind.
Common SaaS Compliance Frameworks and Regulations
SaaS companies operate in a complex regulatory environment where customers, auditors, and investors expect proof of strong security and privacy practices.
The right framework(s) depend on a company’s size, geographic reach, and industry, but they all share the same overarching goal: To provide objective evidence that data is protected and risks are managed. So, what are some of the most commonly needed frameworks for SaaS compliance?
SOC 2
SOC 2 is the most common starting point for SaaS companies in North America. The aim is to assess how a company safeguards data based on five trust principles: security, availability, processing integrity, confidentiality, and privacy.
SOC 2 reports have become standard in procurement reviews for B2B SaaS vendors seeking to work with larger enterprises.
ISO 27001
ISO 27001 provides an international framework for managing information security.
To meet the requirements, organizations must build out an ISMS (Information Security Management System) that guides a company’s internal processes and controls. Many global SaaS providers pursue ISO 27001 certification to meet European client expectations or to operate across multiple regions.
HIPAA
HIPAA applies to healthcare-related SaaS platforms that handle protected health information. Compliance requires both technical and procedural safeguards that are designed to limit access and prevent unauthorized disclosure.
GDPR
GDPR defines strict data protection and privacy obligations for any company handling personal information from individuals in the EU. It impacts how SaaS providers collect consent from users, store personal data, and transfer information outside the EU.
For startups, GDPR compliance often feels complex because obligations extend beyond technical safeguards. Even small teams must document processing activities, manage data subject requests, and maintain extensive records.
Even early-stage SaaS companies with limited EU customers are expected to show compliance readiness when raising capital or entering enterprise contracts. Working with an experienced GDPR consultant helps startups prioritize risk area and implement controls that satisfy both regulators and potential clients.
PCI DSS
PCI DSS (Payment Card Industry Data Security Standard) is a non-negotiable framework for any SaaS platform that handles, processes, or stores credit card information. Even if your startup leverages third-party payment processors like Stripe or PayPal to offload the heaviest security burdens, you still have compliance obligations to ensure your environment is secure and that cardholder data isn't exposed during transmission.
Maintaining PCI DSS compliance not only protects your customers from devastating financial data breaches but also protects your startup from severe non-compliance fines or the complete loss of credit card processing privileges.
Meanwhile, recently emerged DORA requirements and NIS 2 requirements further expand compliance expectations for SaaS companies that serve European financial or critical infrastructure sectors.
The Biggest Compliance Challenges For SaaS Startups
Achieving SaaS compliance is rarely a straightforward journey, particularly for scaling startups trying to balance security with rapid growth. Some of the most common hurdles include:
- Resource Constraints and Lack of Expertise: Most early-stage startups don't have the budget for a full-time, in-house compliance team. Security often falls onto the plate of a CTO or lead engineer who is already stretched thin, leading to rushed or incomplete policy implementations.
- Third-Party Vendor Risk: SaaS companies rely on a vast web of third-party tools (AWS, GCP, specialized APIs). Managing the risk of these vendors and proving to auditors that you have a handle on your supply chain is incredibly difficult without a structured process.
- The "Check-the-Box" Trap: Startups often treat compliance as a one-time project to close a specific enterprise deal. This leads to a frantic scramble before an audit, followed by a lapse in controls, rather than building a sustainable security culture.
- Rapidly Changing Environments: In a CI/CD (Continuous Integration/Continuous Deployment) environment, code changes daily. Maintaining compliance means ensuring that security controls keep pace with rapid development without slowing down engineering momentum.
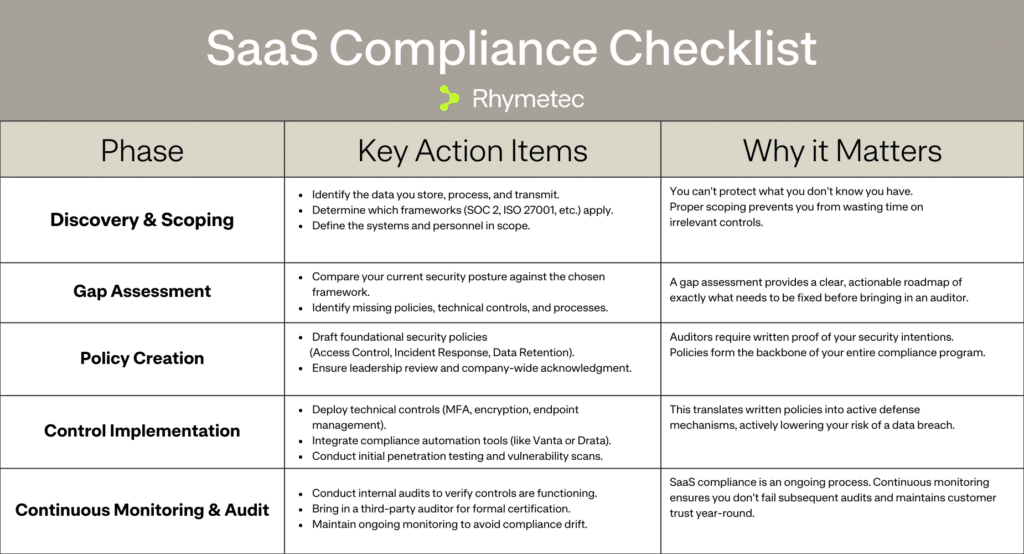
SaaS Compliance Checklist
To keep your team organized, we’ve broken down the SaaS compliance journey into distinct, actionable phases. Use this checklist as a blueprint for your own compliance roadmap.
How Compliance Automation Tools Fit In
Compliance automation platforms like Drata, Vanta, and Secureframe have become standard tools in the SaaS ecosystem.
They simplify evidence collection, automate recurring tasks, and give teams a centralized view of their compliance status. For fast-growing startups managing common frameworks like SOC 2 or ISO 27001, these tools reduce the administrative burden that typically would slow down audits and reporting cycles.
However, compliance automation tools are not a substitute for governance or expertise.
They work based on predefined templates and checklists, which don’t always reflect the unique risks or control environments of each organization. A platform might confirm that a policy exists, but it can’t fully determine whether it is effective, accurate, or aligned with how the business actually operates.
Automation accelerates progress but is limited without a strategy.
Human oversight is still critical. A vCISO can interpret the data surfaced by automation tools and align technical controls with regulatory obligations and business goals. With the right support and expertise, compliance is transformed from a one-time project into an ongoing security program that scales with your business.
The Role of a vCISO in SaaS Compliance and Maintaining Compliance As You Scale
While automation platforms manage the evidence, a Virtual Chief Information Security Officer (vCISO) manages the strategy. For SaaS startups, partnering with a vCISO bridges the gap between software tools and actual security maturity.
A vCISO acts as an extension of your team, bringing executive-level security expertise without the overhead of a full-time hire. They are instrumental in scoping your audit correctly, customizing policies so they actually fit your startup's workflow, and translating complex regulatory requirements into actionable engineering tasks. When an automation tool flags a failing control, a vCISO doesn't just check a box, they help you remediate the root cause.
More importantly, a vCISO helps you maintain SaaS compliance as you scale. As your company adds new features, enters new geographic markets, or targets larger enterprise customers, your threat landscape evolves.
By combining the efficiency of automation tools with the strategic oversight of a vCISO, SaaS companies can turn compliance from a stressful administrative burden into a powerful driver for growth and enterprise trust.
Take the Guesswork out of SaaS Compliance
Contact Rhymetec to learn how our vCISO services can help you build a scalable security program, ace your next audit, and win enterprise trust.
The defense industrial base is entering a new era of accountability. With the DoD’s Cybersecurity Maturity Model Certification (CMMC) requirements becoming mandatory, organizations handling Controlled Unclassified Information (CUI) must demonstrate a security posture that is not only compliant, but operationally sustainable.
Complying with the 110 NIST 800-171 controls is essential for maintaining and winning contracts, but for many defense contractors, achieving compliance feels like a costly, complex, and disruptive overhaul.
That’s why Rhymetec is partnering with PreVeil, the leading CMMC and ITAR compliance solution for small and midsize businesses. Together, we bring defense contractors a complete, streamlined path to CMMC readiness and certification:
- Compliant handling of CUI by design: PreVeil's end-to-end encrypted email and file sharing protects CUI with FIPS 140-3 validated modules, meets DFARS 7012 c-g, and is FedRAMP Moderate Equivalent.
- Seamless integration: Keep using Outlook, Gmail, File Explorer, and Mac Finder. PreVeil deploys in hours using your existing email addresses without forcing a massive IT migration.
- Accelerated compliance: PreVeil’s platform and assessment-ready documentation support 102 of the 110 CMMC Level 2 controls out of the box, perfectly complementing Rhymetec’s compliance management.
"We're thrilled to partner with Rhymetec to support defense contractors. Their expertise in managed IT services combined with our proven CMMC encryption solutions creates
a powerful offering for organizations navigating the compliance journey.” — Jamie Leupold, Director of Channel Sales and Alliances, PreVeil.
A New Standard for CMMC Readiness
Meeting DoD standards takes more than just buying software: it requires gap assessments, System Security Plans (SSPs), and continuous monitoring.
This partnership brings organizations an integrated solution designed for both compliance and operational continuity:
- Purpose-built without the overhead: Save up to 77% compared to deploying legacy solutions like GCC High by using fewer licenses and eliminating costly deployments.
- Achieve audit readiness: Tap into PreVeil’s C3PAO-validated documentation, backed by Rhymetec’s structured CMMC readiness methodology, reducing friction on the road to certification.
- Eliminate central points of attack: All files and emails are automatically encrypted end-to-end. No one other than intended recipients can read your sensitive information.
For Defense Startups and SMBs
For smaller defense contractors, maintaining contract eligibility is business-critical, but heavy IT migrations are often out of reach. With this partnership, SMBs no longer have to compromise on security or budget.
- Cost-efficient enterprise-grade security: Skip the complex and expensive GCC High migration. Get the compliance you need at a fraction of the cost.
- Zero learning curve: PreVeil integrates directly into existing workflows such as Outlook, Gmail, mobile, and file systems, so your team can keep using the tools they already know, minimizing operational downtime.
- Accelerate your path to contract eligibility: Fast-track your path to meeting DFARS 7012 and NIST 800-171 requirements, building immediate trust with the DoD and prime contractors.
For Mid-Market and Enterprise Organizations
As your organization grows, so does the complexity of your supply chain and the flow of CUI. Protecting sensitive data across a larger attack surface requires proven, scalable solutions.
With Rhymetec and PreVeil, security leaders get:
- A validated path to 110/110: PreVeil has already been used by over 50 defense contractors and C3PAOs to achieve perfect scores on their CMMC assessments.
- Complete tech stack design: Rhymetec integrates PreVeil alongside endpoint hardening, network security, penetration testing, and ongoing awareness training.
- Audit coordination: Get comprehensive evidence preparation and liaison support for C3PAO or government-led assessments so you can walk into your audit with absolute confidence.
A Smarter Way Forward
CMMC is the mechanism the DoD is using to determine who can participate in the future of the defense supply chain.
This partnership ensures organizations don’t approach it as a checklist, but as a strategic capability.
By aligning PreVeil’s compliant collaboration platform with Rhymetec’s end-to-end CMMC readiness program, defense contractors gain the clarity, control, and confidence to move into assessment, and beyond it, with momentum.
Contact us to move toward CMMC readiness with Rhymtec and PreVeil.
About PreVeil
PreVeil’s encrypted Email & Drive platform is used by over 2,000 organizations to improve their security & achieve CMMC & ITAR compliance. PreVeil can be deployed in hours & integrates directly with Gmail, Outlook, File Explorer, & Mac Finder. All files & emails are automatically encrypted end-to-end, which eliminates central points of attack & means no one other than intended recipients can read your sensitive information—not even PreVeil. PreVeil has been used by over 50 defense contractors & C3PAOs to achieve perfect 110 scores on their CMMC assessments.
About Rhymetec
Rhymetec is the trusted partner of over 1,500 organizations globally in all of their cybersecurity and compliance needs. Founded in NYC in 2015, Rhymetec delivers information security programs that enable organizations to move faster, meet regulatory demands, and scale with confidence. Our fully in-house team of dedicated vCISOs and seasoned penetration testers manages every phase of your cybersecurity and compliance journey, enabling you to focus on what matters most: growing your business.
Artificial intelligence is accelerating software development and reshaping the security expectations that surround it. Developers are shipping code faster than ever, often with the assistance of AI tools.
However, this same technology has also changed the economics of attacking software. Adversaries are using AI to lower the cost of reconnaissance and iterate through exploits at scale.
In a recent webinar hosted by Rhymetec and XBOW, Christian Mouer, Director of Offensive Security at Rhymetec and Bill Nichols, Head of Customer Success at XBOW explored how an AI-powered penetration testing model allows organizations to increase testing velocity, validate real attack paths faster, and gain broader visibility across modern applications, while maintaining the depth and context required for meaningful risk reduction.
Why Traditional Penetration Testing Timelines No Longer Match Modern Development
Many organizations still rely on annual or semi-annual point-in-time tests, an engagement begins, a snapshot is taken, and a report is delivered weeks later. That approach worked when applications changed slowly and release cycles were measured in quarters.
Today, development moves continuously. New features, endpoints, and integrations are introduced on a weekly, sometimes daily, basis. By the time a traditional test is completed, the environment it assessed has already evolved.
To keep pace, defenders cannot simply scale humans linearly with software output: it is cost and time-prohibitive. This is where autonomous offensive security comes in.
From Theoretical Exposure to Proven Exploitability
One of the most consistent pain points for security teams is the volume of unverified findings produced by automated tools. Large scan outputs require significant internal effort to determine what is real, what is exploitable, and what actually matters to the business.
The approach demonstrated in the webinar prioritizes validation. Exploits are executed against the live environment, attack paths are confirmed, and results are correlated before they are ever delivered.
That shift changes the nature of the final report. Instead of a backlog of potential issues, organizations receive a focused set of confirmed vulnerabilities with clear evidence of impact.
“Hypotheses are cheap. Proof isn’t. We don’t surface a finding unless the system can validate that it’s real.” — Bill Nichols, XBOW
For security and engineering teams, this significantly reduces the time spent reproducing issues and allows remediation efforts to begin immediately.
Expanding Coverage Without Extending Engagement Length
Application ecosystems have grown far beyond a single web interface. Modern environments include large API surfaces, multiple user roles, third-party integrations, and complex authorization logic.
Manually mapping and testing that entire landscape within a standard engagement window forces difficult tradeoffs. Teams must choose between depth in a few areas or lighter coverage across the whole application.
Autonomous execution removes that constraint. Continuous attack surface mapping and parallel exploit testing allow a far greater portion of the environment to be assessed in the same timeframe.
“It’s another pen tester on the team. If we work together, we're able to cover so much more ground than we would have otherwise." — Christian Mouer, Rhymetec
This expanded coverage is what makes deeper, human-led analysis possible later in the engagement.
Reallocating Human Expertise to High-Value Security Work
When the most time-intensive phases of testing, such as reconnaissance, enumeration, and initial exploitation, are handled autonomously, the role of the tester changes.
Instead of spending the majority of the engagement identifying entry points, offensive security experts are able to focus on:
- Chaining multi-step attack paths
- Analyzing real business impact
- Validating complex authorization scenarios
- Working directly with developers on practical remediation strategies
“When we’re cutting down that investigative time, it gives us additional days to validate, find more vulnerabilities, and explore more deep-dive attack paths.” — Christian Mouer, Rhymetec
This is where the greatest risk reduction occurs and where human experience delivers the most value.
The Hybrid Approach: Why AI Doesn't Replace Humans
A common misconception about AI powered penetration testing is that it aims to replace human testers. In practice, the model works as an extension of the testing team rather than a substitute for it.
While XBOW can map an attack surface and execute exploits 24/7, it lacks the business context and nuance that a Rhymetec offensive security expert provides.
Business Logic and Context
AI might flag that a user can see all emails in a system. However, a human tester understands the context: if that user is an HR Administrator, that access is intended. Rhymetec’s team supplies the critical business logic to ensure findings are relevant to the organization's specific operations.
Complex Remediation
Finding a bug is only half the battle. Fixing it without breaking the application is the other half. Rhymetec provides the "human element" of advising on remediation strategies that align with the client’s tech stack and resources.
Parallelism and Depth
The ideal workflow involves running XBOW in parallel with manual testing.
Real-World Impact: Speed and Scalability
The combination of XBOW’s automation and Rhymetec’s expertise delivers results that were previously difficult to obtain in both timeline and scope.
During the webinar, the team shared a case study of a massive web application containing approximately 650 endpoints.
- Traditional Timeline: A thorough manual test would typically take 10 to 15 business days.
- AI-Accelerated Timeline: The XBOW agent mapped and tested the environment in roughly 48 hours.
This acceleration allowed the Rhymetec team to spend the remaining time validating complex findings and exploring deep-dive attack paths that the AI surfaced, ultimately delivering a comprehensive report in five days rather than three weeks.
“We’re able to turn around that pen test confidently within five business days rather than going 10 to 15 days out.” — Christian Mouer, Rhymetec
In Conclusion: AI as a Force Multiplier
As 76% of CISOs anticipate a material cyber attack in the next 12 months, the need for speed and accuracy in testing has never been higher.
Rhymetec’s AI-Powered Penetration Testing partnership with XBOW offers the perfect balance of intelligence and intuition. By automating the reconnaissance and vulnerability identification phases, we allow our certified penetration testers to focus on what they do best: validating impact, analyzing business risk, and guiding remediation.
Key Benefits of the Rhymetec x XBOW Partnership:
- Accelerated Timelines: Reduce testing time from weeks to days.
- Reduced Noise: AI-driven validation eliminates false positives common in traditional scanners.
- Deeper Coverage: Test vast attack surfaces and thousands of endpoints simultaneously.
- Actionable Intelligence: Receive reports validated by expert human testers, not just automated logs.
Contact us to learn more about how to integrate AI-powered testing into your security strategy.
Watch the Full Webinar
For many organizations, navigating GDPR on their own feels overwhelming and simply isn’t feasible to carry out in-house. The seemingly endless acronyms, regulations that are constantly changing, and the looming threat of fines make it a difficult task to begin to tackle.
The role of a GDPR consultant is to step in to help you break it down into manageable pieces and take the work off your team’s plate. A consultant translates the regulation into practical steps tailored to your organization. With the right guidance, organizations can save enormous amounts of time, effectively reduce risk, and give you and your buyers confidence that customer data is handled the right way.
Why Work With A GDPR Consultant?
Many companies make the mistake of assuming they can figure it out as they go, but the reality is that GDPR compliance is an enormous lift impacting nearly every part of a business. Data collection, vendor contracts, employee training, and incident response are just some of the areas that need attention.
A GDPR consultant brings expertise that shortens the learning curve and helps you avoid costly missteps. A consultant can provide a roadmap specifically tailored to your operations, location, and industry. This serves to reduce risk while also improving efficiencies. A good consultant will keep your business needs top-of-mind and align compliance with your broader goals.
A GDPR consultant enables you to avoid hefty fines, reduce risk in meaningful ways, and help position your organization as trustworthy, customer-centric, and competitive in markets where data protection is non-negotiable. If your team sells into the EU or UK, privacy questions now land in every enterprise review as well.
So, what are some signals that working with a GDPR consultant might be the right move for your business? Keep reading to learn more.
When Do You Need A GDPR Consultant?
Not every organization needs full-time compliance staff, but most will hit a point where outside expertise will mean the difference between a ‘check the box’ approach and building a defensible, long-term compliance program.
Here are some signals that it may be the right time to seek help:
- Your team is stretched thin and struggling to keep up with compliance tasks on top of their day-to-day responsibilities.
- You’re expanding into Europe and need to understand how GDPR applies to your customer data, vendors, and contracts.
- You’ve received customer or partner questionnaires about your data protection practices and aren’t sure how to respond.
- You’ve experienced a security incident or data breach and need guidance on notification obligations and remediation.
- You’re preparing for an audit or certification (such as ISO 27001 or SOC 2) and want to align your GDPR program with those efforts.
In short, if compliance questions are slowing down sales, creating friction with customers, or keeping leadership awake at night, it’s a clear signal that a GDPR consultant could bring structure and peace of mind.
What Do GDPR Consulting Services Entail?
An end-to-end GDPR consultant will operate as a partner, guiding your organization from its current state all the way through to demonstrate compliance.
Some consultants will provide a different level of support depending on the engagement and act in a more advisory capacity. At Rhymetec, we pride ourselves on not just advising but delivering everything you need. Here is what a typical engagement would look like with our own GDPR consultants:
Step 1 Of a GDPR Consultant Engagement: Initial Gap Assessment
The initial gap assessment process typically begins with a deep dive into your current practices on areas to include vendor contracts, data flows, security measures, and employee awareness. This serves to show where you are versus where you need to be, and which gaps to prioritize filling first.
Step 2: Creating A Customized Roadmap
After the gap assessment, your GDPR consultant will build on it to create a practical, customized roadmap for your organization. Instead of generic advice and checklists, you’ll know what exactly to prioritize, have a clear path forward, and timelines mapped directly to your business operations.
Step 3: Policy and Procedure Development
Consultants create or refine a wide range of policies and procedures to show alignment with GDPR. These include consent management processes, privacy notices, data subject rights procedures, and other internal policies. A good consultant will work closely with your team to ensure policies are not only legally compliant but are also workable for your teams and supportive of broader business goals.
Step 4: Vendor and Contract Review
Because working with third parties can introduce compliance risks, consultants will review contracts, DPAs (Data Processing Agreements), and vendor management practices to close liability gaps.
Step 5: Implementation Support
At this phase, all of the prior planning and groundwork laid out with policies turns into action.
A GDPR consultant helps implement new processes, train staff, configure tools, and create governance structures so compliance becomes a part of your daily operations.
Step 6: Ongoing Monitoring and Guidance From Your GDPR Consultant
Regulations evolve, enforcement priorities shift, and your business with continue to grow.
By working with a consultant, you can access ongoing support - whether that’s preparing for an audit, managing a regulator inquiry, or simply checking that your program stays continually aligned with the law.
What Does A GDPR Consultant Cost?
Understandably, one of the first questions organizations will ask is, what will this actually cost us?
The answer depends on the scope of work, the size of your company, and the level of involvement you need. There are three main types of support with varying levels of investment you can expect with a GDPR consulting engagement:
Hourly or Project-Based Engagements
Smaller companies or those with very specific needs or gaps to fill (such as drafting a privacy notice or reviewing a contract) may pay an hourly rate, typically ranging from €150 - 350 per hour, or a flat project fee in the €5,000-€20,000 range.
Ongoing Support or Fractional DPO Services
Some organizations opt for monthly retainers when they need ongoing support. These arrangements generally start around €2,000 - €5,000 per month and can scale up if the consultant is acting as your outsourced Data Protection Officer.
Comprehensive Programs With A GDPR Consultant
For a fully managed engagement that starts with a gap assessment and ends with full implementation, costs often range from €20,000 €75,000, depending on complexity, number of systems, and international data transfers involved.
These may feel like hefy investments, but they are often modest compared to the alternative: In 2024 alone, regulators issued over €1.25 billion in GDPR fines across Europe, according to the European Data Protection Board’s annual report.
A consultant helps lower the risk of fines, investigations, costly remediations, and the risk of losing customer trust. Ultimately, you’re paying for peace of mind, smoother operations, and a stronger reputation in a market where data protection is a must-have.
How Does GDPR Relate To ISO 27001 and SOC 2?
GDPR is a law defining how organizations must handle personal data, while ISO 27001 and SOC 2 are voluntary frameworks designed to help organizations implement and demonstrate information security practices.
They overlap in meaningful ways, and an experienced consultant will help you build out your information security practices in a way that addresses multiple requirements.
At a high level, ISO 27001 requires companies to create an Information Security Management System (ISMS) that is continually improved and backed by risk assessments and documented controls.
SOC 2 is an attestation that demonstrates whether an organization’s controls meet some combination of the 5 SOC 2 Trust Services Criteria (security, availability, confidentiality, processing integrity, and privacy).
The overlap between GDPR and these two frameworks is not enormous, but still evident:
What Are The Main Differences?
GDPR requires lawful bases for processing, Data Protection Impact Assessments, Article 30 records, and mechanisms for cross-border transfers. None of these items are explicitly covered by ISO 27001 or SOC 2.
ISO 27001 demands the creation of an ISMS and a Statement of Applicability, which GDPR does not. SOC 2 is delivered as an attestation report covering a point in time or over a defined period, whereas GDPR compliance cannot be ‘certified’ and must instead be demonstrated continuously.
What Are The Main Similarities?
GDPR’s requirement to secure personal data under Article 32 can align with ISO 27001 controls around risk management and access security, and with SOC 2’s criteria for system security. GDPR obligations around vendor contracts and data processing agreements tie directly into ISO 27001’s supplier management and SOC 2’s third-party control requirements.
Breach responses and notification, which GDPR sets at seventy-two hours, also depend heavily on the incident response planning and evidence capture that ISO 27001 and SOC 2 enforce. Even concepts like data minimization and retention are reflected in the asset inventories and disposal practices required by both frameworks.
A GDPR consultant can work with you to help tie these threads together and map data flows to ISO 27001 asset registers, bolt data subject request workflows onto customer service processes, align incident response with GDPR’s reporting timeline, and standardize vendor agreements to cover both contractual and regulatory risks.
Together, GDPR combined with SOC 2 and/or ISO 27001 creates a highly defensible posture that protects customer trust and reduces risk to your organization.
Ready To Speak To A GDPR Consultant?
If compliance questions are slowing down deals, raising concerns with leadership, or leaving your team unsure of what comes next, it may be time to get expert support.
A GDPR consultant can help you move from uncertainty to clarity with a clear roadmap, tailored guidance, and hands-on implementation. Whether you need a one-time assessment or a long-term partner, working with a consultant gives you confidence that your data protection program can stand up to regulatory scrutiny and customer expectations alike.
If you’re ready to take the next step, start the conversation today. The sooner you bring in the right expertise, the sooner you can shift GDPR from a burden into a competitive advantage.
The attack surface has changed. Organizations rely on dozens of cloud apps, APIs, and third-party integrations, and attackers are already using AI to find and exploit weaknesses at machine speed. Demand for penetration tests is at an all-time high. This means pentesters need to arm themselves with new ways to get the job done to keep pace with AI attacks.
That’s why Rhymetec is partnering with XBOW, the world’s leading autonomous pentesting platform. Together, we bring clients a new standard of security:
- AI-powered and fully autonomous: XBOW deploys hundreds of specialized agents in parallel working side by side with human penetration testers.
- On demand: Run tests as often as you need, integrated directly into your development cycle.
- Surgically precise: Every vulnerability XBOW discovers comes with a full proof of concept for exploitation, eliminating false positives.
“The threat landscape isn’t static. Attackers are already leveraging automation, and defenders must respond in kind. By partnering with XBOW, we can now give our clients the speed of autonomous testing with the human guidance and compliance expertise they trust Rhymetec for.” — Justin Rende, CEO, Rhymetec
“The rise of AI-powered offense demands that defenders move much faster, while also increasing the depth of their analysis. The solution is to automate all routine work with XBOW's autonomous AI hacker, so human experts can focus on the deep security design questions. This way, the human security team gains super powers, being able to move with unprecedented speed and depth. We're delighted to partner with the team of experts at Rhymetec, perfectly complementing XBOW to deliver a complete security solution.” — Oege de Moor, CEO, XBOW
What to Expect
According to Verizon’s 2025 Data Breach Investigations Report, it still takes a median of five weeks for known flaws to be remediated, and nearly half of critical edge-device vulnerabilities remain unpatched. This lag time is untenable when adversaries are exploiting at AI speed.
With Rhymetec and XBOW, organizations gain the ability to:
- Continuously validate security posture across web apps, APIs, and third-party integrations.
- Accelerate compliance readiness by feeding validated findings directly into Rhymetec’s compliance services.
- Scale offensive testing affordably with on-demand automation, reserving human experts for complex, business-logic vulnerabilities.
For Startups and Growth-Stage Companies
For early-stage teams, every security decision feels like a trade-off between speed, cost, and credibility. With this partnership, startups no longer have to choose.
- Accelerated Security Reviews: XBOW completes penetration tests in hours, helping founders meet buyer and investor security expectations without waiting weeks.
- Built-In Compliance Readiness: Validated findings flow directly into Rhymetec’s compliance services, reducing audit stress and building customer trust from day one.
- Enterprise-Grade Security at Startup Speed: On-demand AI-driven testing delivers enterprise-level assurance at a fraction of the cost, giving startups security maturity without slowing growth.
For Mid-Market and Enterprise Organizations
As organizations scale, so does the complexity of their attack surface — more applications, more integrations, and more pressure to deliver secure products without slowing down. Traditional testing simply can’t cover it all.
With XBOW and Rhymetec, security leaders get:
- Expanded Coverage Across Applications: Autonomous agents extend testing across web apps and APIs, including the third-party integrations that are often overlooked.
- Human Expertise Where It Counts: Automated testing handles the routine, giving Rhymetec’s security experts more time to focus on complex business-logic vulnerabilities.
- Ongoing Validation: Findings arrive pre-validated with exploit proof, and fixes can be retested on demand — ensuring vulnerabilities are truly closed, not just logged.
A Smarter Way Forward
Our combined approach blends autonomous agents that never tire with human experts who bring judgment, context, and compliance guidance. The result: faster closure of common vulnerabilities, stronger defenses against subtle flaws, and the confidence that your security program can keep pace with modern development velocity.
[video width="1920" height="1080" mp4="https://rhymetec.com/wp-content/uploads/2025/09/XBOW_Clip.mp4%22][/video]
Your attack surface has changed. Your pentesting strategy should too.
👉 Contact Rhymetec to learn how AI-powered penetration testing with XBOW can strengthen your security program and accelerate compliance.
XBOW is an AI-powered penetration testing platform that scales offensive security in hours. Delivering human-level security testing at machine speed, XBOW helps organizations discover vulnerabilities before attackers can exploit them. Ranked as #1 on the HackerOne leaderboard in the U.S., XBOW was founded by the creators of GitHub Copilot and GitHub Advanced Security, and is backed by Sequoia and Altimeter.
Rhymetec is the trusted partner of over 1,500 organizations globally in all of their cybersecurity and compliance needs. Founded in NYC in 2015, Rhymetec delivers information security programs that are effective, compliant, and built to scale with your business. Our fully in-house team of dedicated vCISOs and seasoned penetration testers manages every phase of your cybersecurity and compliance journey, enabling you to focus on what matters most — growing your business.
The attack surface has changed. Organizations rely on dozens of cloud apps, APIs, and third-party integrations, and attackers are already using AI to find and exploit weaknesses at machine speed. Demand for penetration tests is at an all-time high. This means pentesters need to arm themselves with new ways to get the job done to keep pace with AI attacks.
That’s why Rhymetec is partnering with XBOW, the world’s leading autonomous pentesting platform. Together, we bring clients a new standard of security:
- AI-powered and fully autonomous: XBOW deploys hundreds of specialized agents in parallel working side by side with human penetration testers.
- On demand: Run tests as often as you need, integrated directly into your development cycle.
- Surgically precise: Every vulnerability XBOW discovers comes with a full proof of concept for exploitation, eliminating false positives.
“The threat landscape isn’t static. Attackers are already leveraging automation, and defenders must respond in kind. By partnering with XBOW, we can now give our clients the speed of autonomous testing with the human guidance and compliance expertise they trust Rhymetec for.” — Justin Rende, CEO, Rhymetec
“The rise of AI-powered offense demands that defenders move much faster, while also increasing the depth of their analysis. The solution is to automate all routine work with XBOW’s autonomous AI hacker, so human experts can focus on the deep security design questions. This way, the human security team gains super powers, being able to move with unprecedented speed and depth. We’re delighted to partner with the team of experts at Rhymetec, perfectly complementing XBOW to deliver a complete security solution.” — Oege de Moor, CEO, XBOW
What to Expect
According to Verizon’s 2025 Data Breach Investigations Report, it still takes a median of five weeks for known flaws to be remediated, and nearly half of critical edge-device vulnerabilities remain unpatched. This lag time is untenable when adversaries are exploiting at AI speed.
With Rhymetec and XBOW, organizations gain the ability to:
- Continuously validate security posture across web apps, APIs, and third-party integrations.
- Accelerate compliance readiness by feeding validated findings directly into Rhymetec’s compliance services.
- Scale offensive testing affordably with on-demand automation, reserving human experts for complex, business-logic vulnerabilities.
For Startups and Growth-Stage Companies
For early-stage teams, every security decision feels like a trade-off between speed, cost, and credibility. With this partnership, startups no longer have to choose.
- Accelerated Security Reviews: XBOW completes penetration tests in hours, helping founders meet buyer and investor security expectations without waiting weeks.
- Built-In Compliance Readiness: Validated findings flow directly into Rhymetec’s compliance services, reducing audit stress and building customer trust from day one.
- Enterprise-Grade Security at Startup Speed: On-demand AI-driven testing delivers enterprise-level assurance at a fraction of the cost, giving startups security maturity without slowing growth.
For Mid-Market and Enterprise Organizations
As organizations scale, so does the complexity of their attack surface — more applications, more integrations, and more pressure to deliver secure products without slowing down. Traditional testing simply can’t cover it all.
With XBOW and Rhymetec, security leaders get:
- Expanded Coverage Across Applications: Autonomous agents extend testing across web apps and APIs, including the third-party integrations that are often overlooked.
- Human Expertise Where It Counts: Automated testing handles the routine, giving Rhymetec’s security experts more time to focus on complex business-logic vulnerabilities.
- Ongoing Validation: Findings arrive pre-validated with exploit proof, and fixes can be retested on demand — ensuring vulnerabilities are truly closed, not just logged.
A Smarter Way Forward
Our combined approach blends autonomous agents that never tire with human experts who bring judgment, context, and compliance guidance. The result: faster closure of common vulnerabilities, stronger defenses against subtle flaws, and the confidence that your security program can keep pace with modern development velocity.
Your attack surface has changed. Your pentesting strategy should too.
👉 Contact Rhymetec to learn how AI-powered penetration testing with XBOW can strengthen your security program and accelerate compliance.
XBOW is an AI-powered penetration testing platform that scales offensive security in hours. Delivering human-level security testing at machine speed, XBOW helps organizations discover vulnerabilities before attackers can exploit them. Ranked as #1 on the HackerOne leaderboard in the U.S., XBOW was founded by the creators of GitHub Copilot and GitHub Advanced Security, and is backed by Sequoia and Altimeter.
Rhymetec is the trusted partner of over 1,500 organizations globally in all of their cybersecurity and compliance needs. Founded in NYC in 2015, Rhymetec delivers information security programs that are effective, compliant, and built to scale with your business. Our fully in-house team of dedicated vCISOs and seasoned penetration testers manages every phase of your cybersecurity and compliance journey, enabling you to focus on what matters most — growing your business.