Justifying the return on cybersecurity investments can be hard. Some things are relatively easy, especially with the help of tools like compliance automation platforms. You have to comply with legal requirements and customer demands to see your SOC 2 report, but what about security that goes beyond regulatory requirements?
In a business full of competing interests, managers asking for new hires, and the marketing team wanting to spend additional money, security often falls by the wayside - but it shouldn't.
That's one of the reasons at Rhymetec we love checking out Verizon's annual Data Breach Investigation Report (DBIR). Verizon's DBIR shows exactly why companies need to move beyond compliance and implement proactive controls.
Regulators are often years behind the latest trends in the industry - companies that just focus on compliance often fail to implement safeguards and controls that could save their business millions of dollars in lost business, fines, and legal fees.
So, what are the big takeaways from this year's DBIR? Well, there are quite a few:
Generative AI, Compliance, and Accidental Leaks
You almost certainly have employees at your company feeding data into AI models that you don't know about. One of the findings that should be the most alarming to information security leaders is that, according to the DBIR:
"15% of employees were routinely accessing GenAI systems on their corporate devices (at least once every 15 days). Even more concerning, a large number of those were either using non-corporate emails as the identifiers of their accounts (72%) or were using their corporate emails without integrated authentication systems in place (17%), most likely suggesting use outside of corporate policy."
Many organizations pick one or two AI vendors and work with those, and accept a certain degree of risk. However, employees signing up directly for generative AI applications can pose severe risks, particularly to organizations that deal with highly sensitive intellectual property, regulated data such as health records, or even national security and classified data.
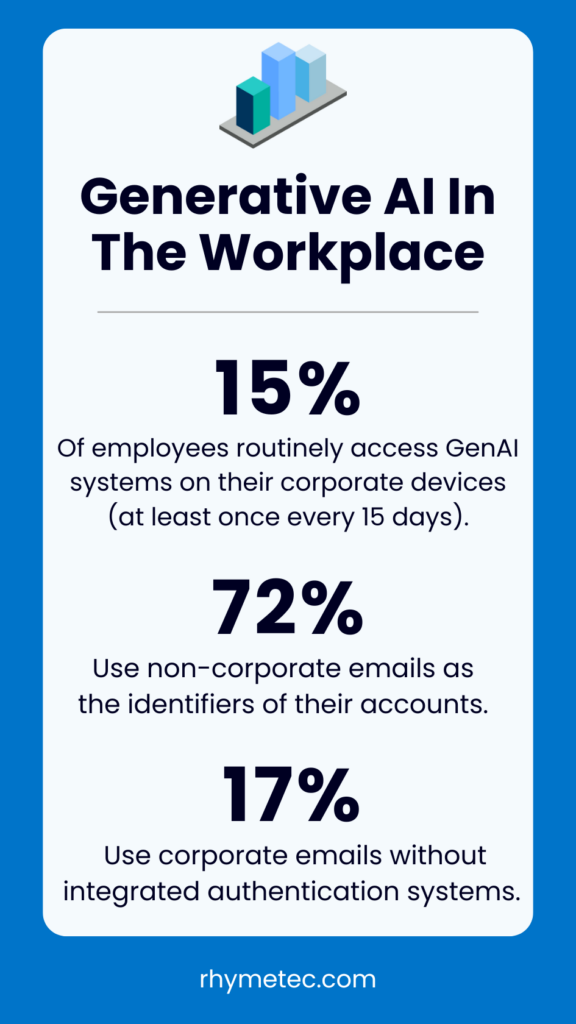
For example, imagine an employee at a defense contractor decides to use DeepSeek to analyze CUI (controlled unclassified information) that a contractor sends them. They likely unknowingly just sent that data directly to China.
Getting a handle on "shadow SaaS", and particularly which AI applications employees may be sending sensitive data, is likely to be one of the most important issues vexing information security teams in the next five years.
Third-Party Risk Remains Highly Relevant in The 2025 Verizon Data Breach Report
Another key finding in the 2025 DBIR that security professionals should be paying close attention to is the dramatic increase in third-party involvement in breaches. According to Verizon's analysis, third-party involvement in breaches doubled from 15% to 30% in just one year. This isn't merely a statistical blip - it represents a fundamental shift in how attackers are approaching your organization's security perimeter.
As in all things in life, there are tradeoffs. As organizations increasingly adopt convenient SaaS solutions to solve various business challenges, in many cases, they unwittingly dramatically expand their attack surface (sometimes even the business doesn't know what their attack surface is, such as with shadow generative AI use).
The report specifically highlights how several high-profile breaches in services like Change Healthcare, CDK Global, and Blue Yonder exposed sensitive data and created substantial business interruption events across entire industries:
Healthcare providers couldn't process claims, auto dealerships lost access to their systems, and retailers and food services companies found themselves unable to manage inventory. When your critical business functions rely on third-party SaaS providers, their security posture becomes your operational vulnerability.
While compliance frameworks like SOC 2 have recognized third-party risk for years, the real-world impact is growing faster than many organizations' vendor management programs can adapt.
This data should serve as a wake-up call: Today's interconnected business ecosystem requires a much more proactive approach to vendor security assessment, continuous monitoring, and contingency planning. Organizations that fail to evolve beyond "check the box" vendor management will increasingly find themselves dealing with the consequences of their partners' security failures.
Malware Is Fueling Identity-Based Attacks
On page 54 of the report is perhaps one of the most interesting insights of the 2025 DBIR. In a section titled "Infostealers Galore", Verizon discusses one of the most prominent threats to organizations today - infostealer malware.
Infostealers are a type of malware that infects a victim's computer and siphons all of the passwords and session cookies the victim has saved on their browser, sessions for applications such as Discord, crypto wallet keys, autofill data, and basically any other sensitive or valuable lightweight data from the device. This data is then sent back to the threat actor's infrastructure, where individual victims' information is sold as an "infostealer log" containing one victim's data.

As you can imagine, there is a trove of high value information for threat actors to leverage within this data to include session cookies which can be used to hijack active sessions to facilitiate account takeover attacks for major web applications and e-commerce companies, crypto wallet keys which can allow the threat actor to steal currency, and even credit card data from autofills which can facilitate fraud.
However, this malware can also grab corporate emails and passwords for SaaS applications, VPN's, corporate bank accounts, and other critical information. Verizon estimates that 30% of the tens of millions of logs out there come from devices that are corporate-owned, an absolutely astounding figure.
A discerning observer might ask an obvious question: Does the prevalence of corporate credentials, session cookies, and information available in the stealer log ecosystem enable ransomware groups and other similar threat actors?
Well, Verizon has the answer there, too.
"By examining some of the victims posted to the ransomware extortion sites, we found that 54% of the victims had their domains show up in at least one infostealer log or in marketplace postings, and 40% of those logs contained corporate email addresses." - Verizon Data Breach Report 2025, page 57.
This type of analysis is critical, as threat actors are continuously evolving their tactics, techniques, and procedures in response to improvements in organizational cybersecurity. Oftentimes, threat actors will use whatever is easiest, and active sets of corporate credentials and session cookies floating around in the criminal ether is indeed a pretty easy way to get access to some high-value systems.
Ransomware Is On the Rise, Sort Of
Speaking of ransomware, many organizations make the mistake of believing that they are too small for ransomware groups and threat actors to target.
However, this belief couldn't be further from the truth. One of the most interesting and relevant findings from the DBIR was the data around ransomware attacks in 2024. While attacks continue to rise, victim behavior and attacker strategies are evolving in notable ways.
Ransomware incidents jumped dramatically, showing a 37% increase from last year. These attacks now represent 44% of all data breaches analyzed - up from 32% in the previous report. Nobody expected ransomware to go away, but this data shows that even the notable law enforcement takedowns of Lockbit, Black Cat, and other high-profile ransomware groups has at best dented this highly financially lucrative criminal operation.
However, it's worth digging in a bit on the ransomware piece of the report because the increase in ransomware as a proportion of all attacks doesn't tell the whole story. The reports section on ransom payments shows a potential silver lining:
Both the frequency and size of ransom payments are decreasing. The median ransom payment dropped to $115,000 in 2024, down from $150,000 in 2023. More significantly, 64% of victims now refuse to pay ransoms altogether - a substantial increase from 50% just two years ago.
While the report doesn't directly make the connection, organizations improving backup and recovery combined with defensive measures may be fueling another trend - the increased targeting of small and midsize businesses by ransomware operators.
Perhaps the most alarming finding is how severely ransomware affects smaller organizations. While ransomware appears in 39% of breaches at large enterprises, it's present at a staggering 88% of breaches at SMBs.
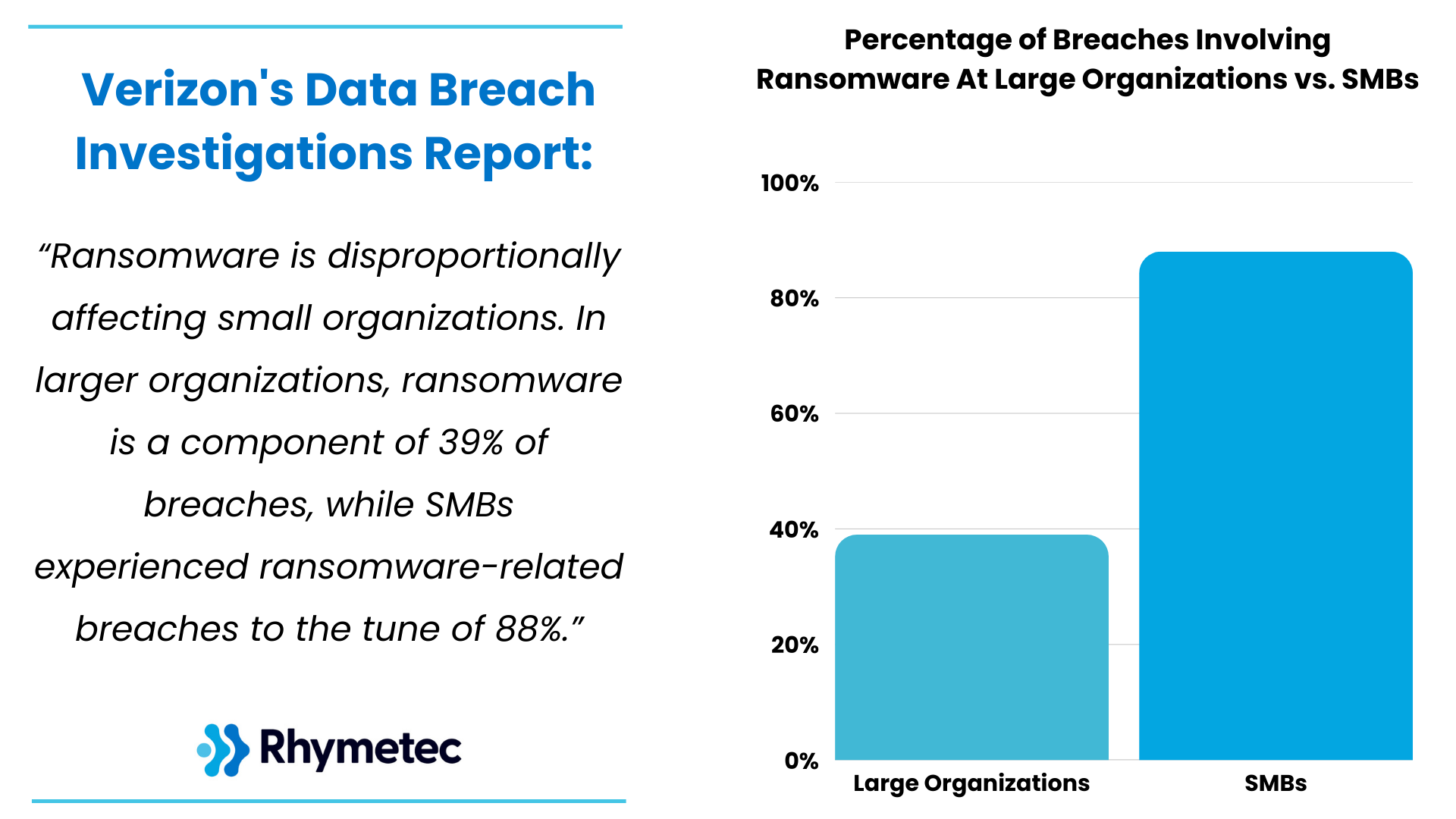
This disparity likely reflects the resource gap in cybersecurity preparedness. Smaller organizations typically have less robust backup solutions, fewer security controls, and limited incident response capabilities, making them both easier targets and more likely to suffer catastrophic impacts.
Concluding Thoughts: The Verizon Data Breach Report 2025
The 2025 Verizon Data Breach Report paints a clear picture of an evolving threat landscape that demands more than just a checkbox approach to security. Compliance frameworks like SOC 2 and ISO 27001 provide a valuable foundation, but going beyond them is essential for organizations to protect themselves from sophisticated ransomware groups and other threat actors.
The data tells a compelling story: Third-party risks have doubled, credential theft via infostealers is directly fueling ransomware attacks, and shadow AI usage presents entirely new vectors for data loss. These threats are often moving faster than regulatory and best practice frameworks can adapt.
At Rhymetec, we recommend that organizations build their compliance foundation with targeted security investments that address these emerging threats:
- Implement continuous monitoring for external threats.
- Develop comprehensive controls for third-party risk management that go beyond questionnaires.
- Establish clear policies and technical controls for AI platform usage.
- Prioritize edge device security given their increased targeting by threat actors.
- Develop security strategies that account for the human element, which remains involved in 60% of breaches.
The most successful organizations will be those that view compliance as the starting point, not the destination, of their security journey. And most importantly, those who stay educated on how the threat landscape is shifting over time.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
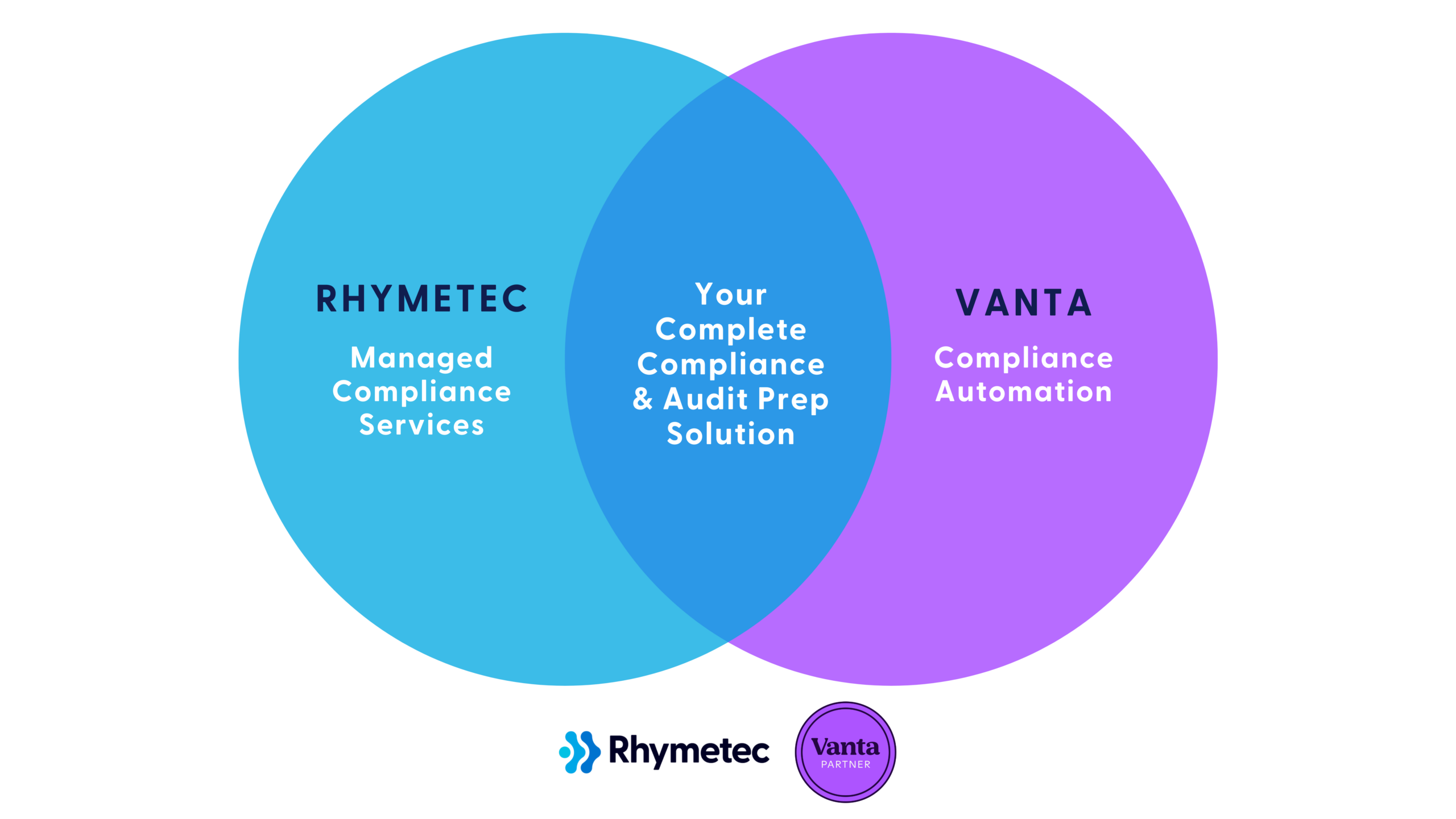
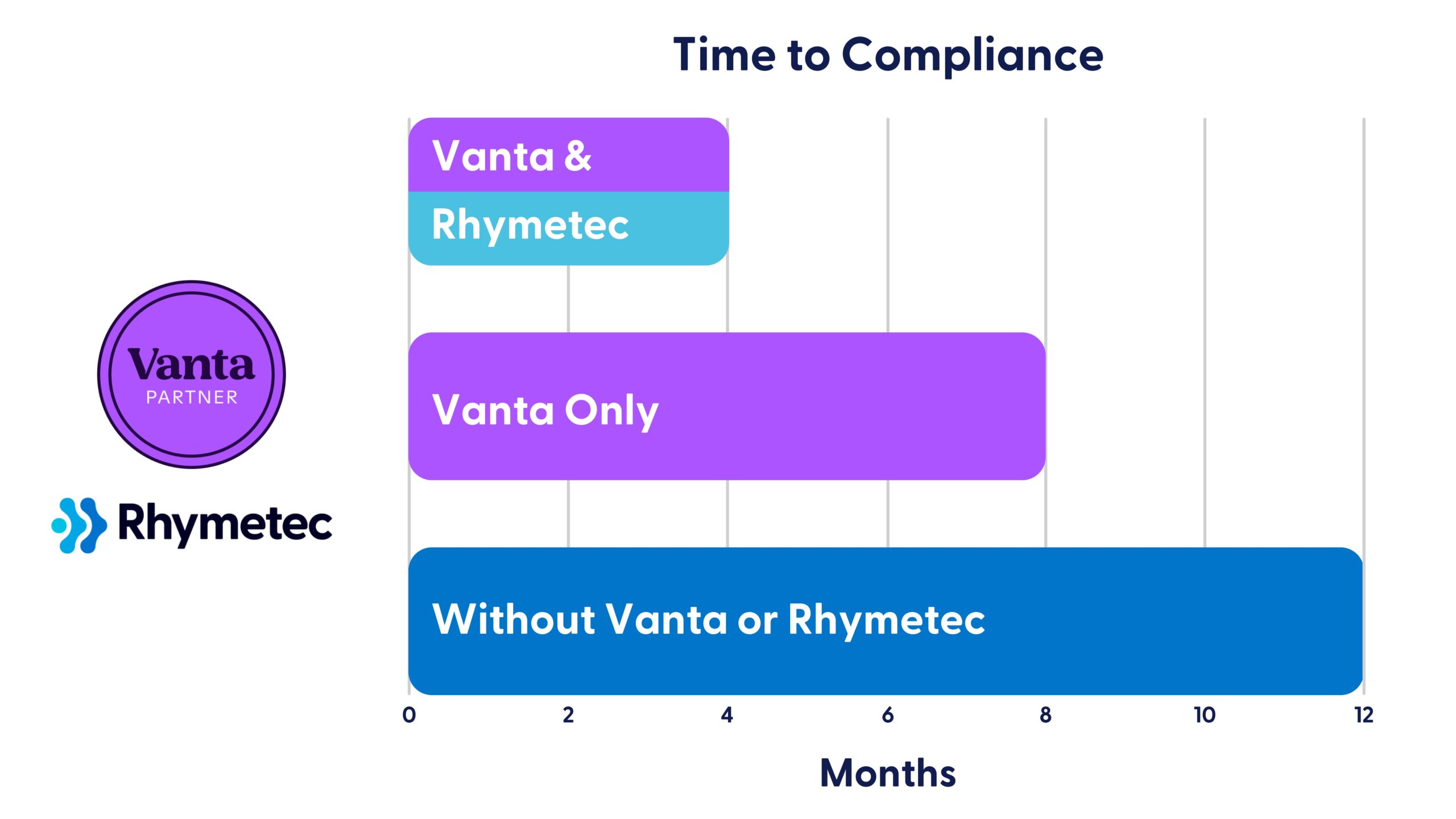
So, you're considering SOC 2 or ISO 27001 for the first time - and realizing just how much time and expertise it takes to actually get there. That's where Vanta (and Rhymetec!) comes in:
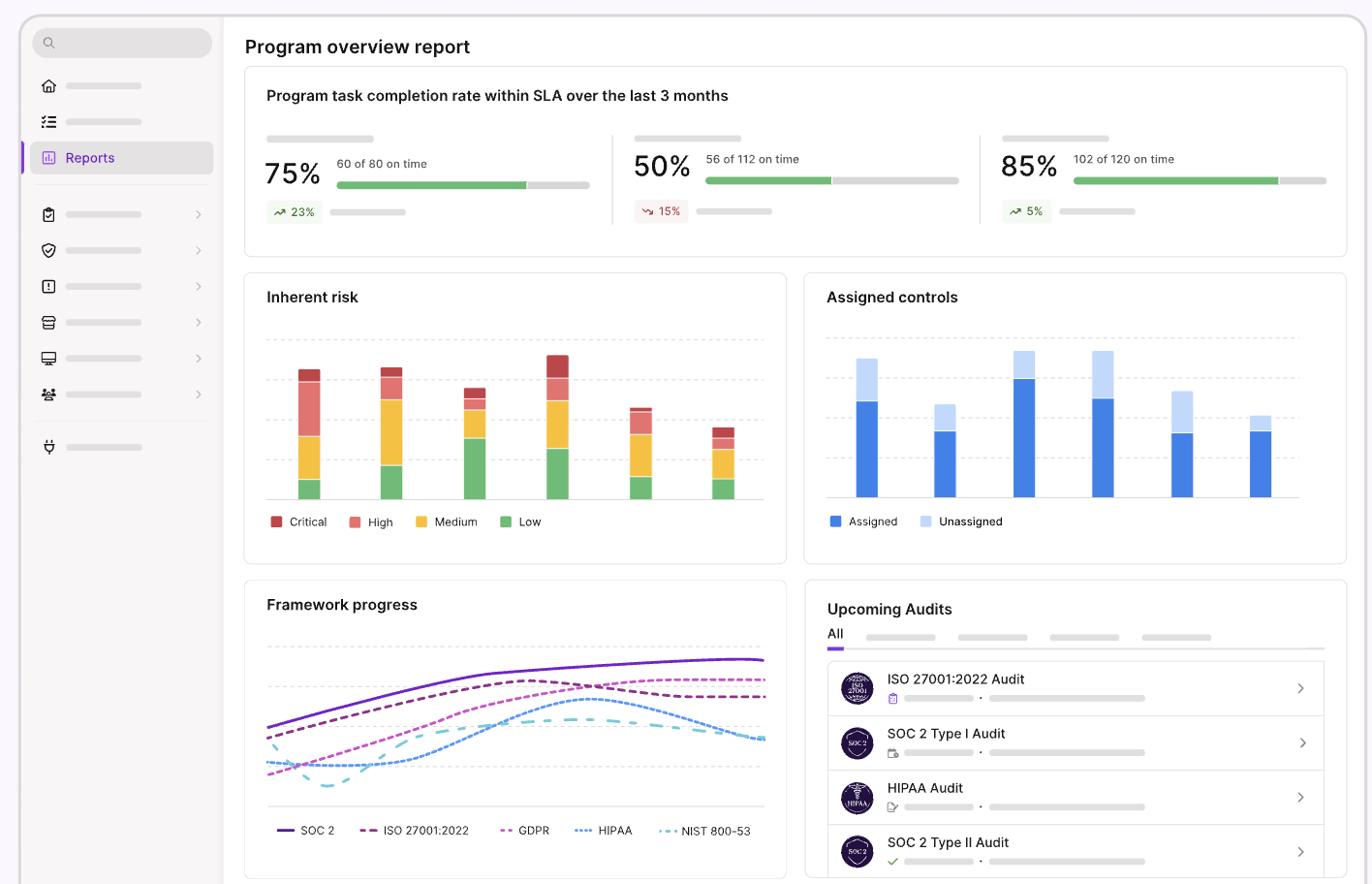
Vanta automates 90% of compliance monitoring through integrations with 300+ systems, real-time control insights, and automated evidence collection—enhancing your visibility into your security posture. Rhymetec handles the hands-on readiness tasks for you. The combination of Vanta with our tailored services delivers a faster, more manageable path to audit success.
Our team of experts at Rhymetec, by leveraging Vanta for you, accelerates every step of your compliance journey from the initial scoping phase to auditor handoff. We've helped over 1,000 organizations efficiently meet their security and compliance goals with this method. Here's how Vanta works in conjunction with our services, and how the platform can benefit you immediately, especially if you are early on in the process of compliance:
Vanta Automates Compliance Workflows
Vanta automates the visibility into tasks required to build a compliance program. One of the main value adds of Vanta is that it will handle the repetitive work for you and give you back your time to focus on what really matters - growing your business. Here's how it works, particularly for organizations early in their compliance journey:
Using Vanta circumvents the need to even get started on tedious manual spreadsheets and checklists. Instead, Vanta enables organizations to jump right in and leverage its capabilities, including system integrations and automated collection of evidence.
For instance, a startup pursuing SOC 2 may need to prove that it restricts employee access to production systems, monitors for security incidents, and keeps its asset inventory up-to-date and in line with SOC 2 requirements. Vanta connects to systems including AWS, GitHub, Google Workspace, and Okta to automatically accomplish the following:
- Display passing controls.
- Simplify policy management.
- Collect the evidence needed for an audit.
It also includes pre-built policy templates for every framework, so teams can work from a baseline and avoid having to write everything from scratch. Leadership is able to track compliance status in real time and improve visibility tied to audit preparation for employees—resulting in efficiency and reduced time to compliance.
Who Uses Vanta And Why
Vanta is primarily used by fast-growing, cloud-native organizations that are seeking to meet relevant security and data privacy requirements in the most efficient way possible. Often, these organizations are trying to avoid dedicating excessive internal resources to manual compliance work. However, we’ve seen companies from all sizes—startup to enterprise—with varying environments—such as multi-cloud and hybrid—utilize Vanta to streamline their compliance efforts.
Some of the main reasons companies opt to use Vanta are to help them:
- Reduce their audit timelines.
- Improve visibility into their security posture.
- Lower the overall cost of compliance.
Vanta connects to the tools you use via API, the cloud infrastructure you're set up in, and your internal systems to give you a complete view of your security and compliance.
This eliminates the need for fragmented spreadsheets and manual checklists, providing leadership more control over compliance progress and unburdening technical teams that are already stretched thin.
Another core value add is that Vanta enables a single source of truth for audit readiness, helping leaders and your sales team demonstrate you're where you need to be in terms of security and compliance to auditors, customers, your partners, and other stakeholders.
What Does Vanta Do? Vanta Supports Continuous Compliance
It's important to know going into your compliance journey that compliance doesn’t stop after one audit.
Frameworks like SOC 2, ISO 27001, and HIPAA require ongoing evidence of control effectiveness, which means you need continuous monitoring rather than only point-in-time documentation.
Vanta is built precisely to support this model. It runs in the background, constantly monitoring your infrastructure and systems for changes that could impact compliance. It will flag any issues in real time, such as expired access, unapproved software, or missing security training. The platform centralizes the evidence you'll need to show controls are operating continuously.
This approach replaces manual check-ins and periodic reviews with continuous visibility. Combined with Rhymetec's guidance and remediation support, clients stay audit-ready year-round without having to rebuild compliance work from scratch each cycle.
Vanta Streamlines The Work of Cybersecurity & Compliance Experts
Vanta automates the visibility into tasks (While Rhymetec can support the completion of them) that are most likely to slow down compliance teams, allowing the experts to focus on higher-impact and more specific work. Tasks like collecting screenshots, tracking evidence, and managing spreadsheets shift to automated processes within the platform.
For Rhymetec's team, the platform provides a centralized source of truth and allows us to spend more time analyzing results and guiding clients through control implementation. Our team uses Vanta in every step of the compliance automation process on your behalf. By handling repetitive tasks and bringing issues to our attention automatically, Vanta allows us to carry out a more efficient process to compliance readiness for your organization.
How Rhymetec Leverages Vanta To Deliver Compliance - Fast
Rhymetec leverages Vanta as a core part of our compliance delivery model.
Our approach combines all of the benefits of automation with hands-on cybersecurity expertise to shorten the path to audit readiness. Our team configures Vanta for your systems and selected framework. We work hard to eliminate common setup delays and create alignment between compliance goals and actual business operations.
Once deployed, Vanta automatically monitors your cloud infrastructure and systems for compliance-related activities. But automation alone doesn’t get you audit-ready. That’s where Rhymetec comes in. After the initial setup, our team steps in to:
- Interpret and prioritize Vanta’s findings based on your unique business needs
- Remediate flagged issues with hands-on support — not just advice
- Tackle all remaining manual components like policy creation, access reviews, evidence collection, and control implementation
The combination of automated and manual work keeps the momentum going and gets clients through readiness assessments and audits on a much faster timeframe. By managing both Vanta and the 'hands-on' components of compliance readiness work on your behalf, we’re able to accelerate every phase of the compliance process.
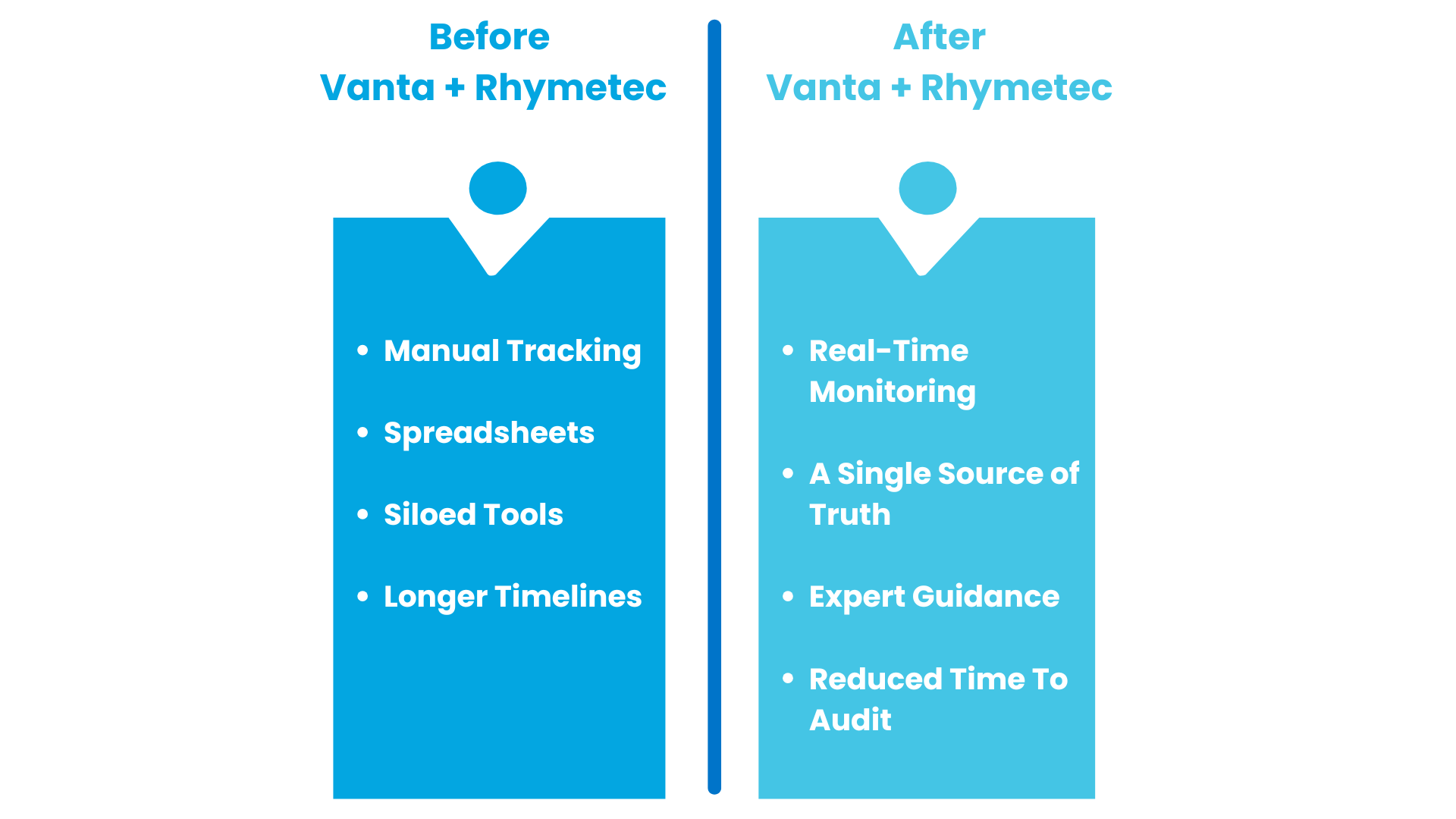
Why Pairing Vanta and Rhymetec Delivers Better Outcomes
Most frameworks require an array of expert judgment, manual implementation of certain controls, and a level of preparation that automation can't complete 100% of on its own.
Rhymetec fills that gap by managing the manual work and aligning Vanta specifically to your environment. We interpret control requirements, resolve flagged issues, write custom policies, manage communication with auditors on your behalf, and more.
By using Vanta for compliance automation - and Rhymetec filling in the gaps for you when needed - clients move faster and meet their compliance goals with less internal burden. Together, we consistently generate strong audit readiness and stronger security programs.
Accessing Vanta Through Rhymetec
Rhymetec is proud to offer Vanta (in conjunction with our Vanta compliance services) directly to clients who haven't yet selected a compliance automation platform.
Particularly in the case of clients early in their compliance journey, this vastly simplifies the buying process by providing both the technology and the services needed to meet requirements in one engagement. We give clients access to a world-class platform without requiring them to manage separate vendor relationships or navigate pricing and setup alone.
Our team at Rhymetec handles everything from the initial deployment and setup in Vanta to ongoing administration of the platform on your behalf. This allows you to adopt automation earlier, which will accelerate your compliance timelines and help you avoid missteps that a self-directed rollout could entail. Contact our team to learn more:
Deepak Chopra once said, "All great changes are preceded by chaos." This has never been more accurate than when it’s applied to the current AI and cybersecurity environments—and the regulations that govern them.
New frameworks like the Digital Operational Resilience Act (DORA), the EU AI Act, the Network and Information Systems Directive 2 (NIS2) and the Cybersecurity Maturity Model Certification (CMMC) are reshaping how businesses handle security, risk and compliance. These regulations aren't just about ticking boxes—they carry major financial penalties and demand real operational changes.
For companies in financial services, AI development, critical infrastructure or defense, staying ahead of the changes is vital to avoid penalties, protect data and maintain trust. Let's look at what each entails.
DORA: Protecting Financial Institutions From Cyber Disruptions
Financial institutions face constant cyber threats and operational risks. DORA aims to empower financial organizations to weather system disruptions and continue operating smoothly.
DORA requires penetration testing, vulnerability assessments and disaster recovery planning. It focuses on business continuity to ensure that if a system fails, a plan is in place to keep operations running. Banks, insurance companies and investment firms must validate security controls through rigorous testing.
This regulation is a wake-up call for financial institutions to take cybersecurity resilience seriously. The penalties for non-compliance are severe, making it crucial for businesses to invest in robust security testing and operational risk management.
The EU AI Act: Setting The Global Standard For AI Compliance
AI development currently operates in a regulatory gray area, but the EU AI Act is changing that. One of the first laws to set clear boundaries on AI usage, it focuses on ethical risks, security concerns and prohibited applications.
The most important takeaway is the significant financial penalties for non-compliance: These can be up to 7% of a company's global annual revenue or 35 million euros, whichever is higher. That's more than GDPR, which has already forced businesses worldwide to rethink their approach to data privacy.
This law explicitly bans certain AI applications, particularly those that exploit vulnerabilities. The ban includes AI-powered cyberattacks, social manipulation and unethical facial recognition practices. Article 5 of the act outlines prohibited AI uses, such as systems that exploit people's age, disabilities or socioeconomic circumstances.
This isn't simply a privacy factor; its purpose is to prevent AI from being weaponized.
A common misconception is that this law only affects European companies. That's not the case. Any company developing, deploying or processing AI systems in the EU—or serving EU customers—must comply. For example, if a U.S. company hosts its platform in an EU data center or processes European customer data, this regulation applies.
The EU AI Act is setting the stage for global AI governance. Similar regulations are expected to emerge worldwide, making it smart for businesses to adapt now rather than scrambling to comply later.
NIS2: Strengthening Cybersecurity For Critical Infrastructure
Also in the EU, the NIS2 Directive expands cybersecurity requirements for critical industries like energy, healthcare, transportation and digital services. It builds on the original NIS Directive but goes much further, applying to more organizations, increasing security expectations and enforcing stricter penalties.
The enhanced reporting requirements are one of the biggest challenges. Companies must notify regulators of cyber incidents within 24 hours, provide a complete assessment within 72 hours and demonstrate they are actively managing security risks.
The directive also emphasizes stronger supply chain security, holding companies responsible for ensuring their vendors meet cybersecurity standards. This means businesses can't just secure their own systems—they must also vet suppliers and partners to prevent weak links in the supply chain.
Beyond reporting and supply chain oversight, NIS2 enforces stricter governance requirements. Organizations must appoint security officers, conduct regular risk assessments and develop robust cybersecurity policies. Those that fail to comply face heavy financial penalties and increased regulatory scrutiny.
Compliance isn't optional for companies operating in or serving the EU market. NIS2 is setting a new cybersecurity standard, and businesses that don't act risk fines, operational disruptions and reputational damage.
CMMC: Raising the Bar For U.S. Defense Contractors
The CMMC is a requirement for companies working with the U.S. Department of Defense (DoD). It builds on cybersecurity frameworks like NIST 800-171, ensuring that defense contractors follow strict security protocols to protect sensitive government data.
Recent changes to CMMC include a new self-assessment option for Level 1 compliance, making it easier for smaller contractors to meet requirements without hiring third-party auditors. However, higher certification levels still require independent verification, adding layers of accountability.
With the new compliance requirements going into effect in mid-2025, businesses need to act now. The DoD has made it clear that CMMC certification will be mandatory for contracts, and companies that don't comply risk losing business.
Evolving Security Frameworks: A Smarter Approach To Compliance
For organizations handling sensitive data in healthcare, finance and other regulated industries, new security frameworks present a way to prove compliance with strict privacy and cybersecurity standards. In the past, certification required a lengthy, one-size-fits-all assessment, but newer models offer more flexible options with fewer controls, reducing complexity while maintaining security.
Many businesses don't realize that certification levels vary, and choosing a lower-tier option may not meet regulatory or customer expectations. This is especially important for HIPAA compliance, where recognized certifications can demonstrate that companies meet security standards. As cybersecurity laws evolve, understanding these frameworks ensures that businesses stay compliant, competitive and prepared for future regulations.
Laws like DORA, the EU AI Act and NIS2 are designed to keep technology from becoming a threat. AI development currently lacks clear rules—without oversight, it can be used in dangerous ways. These regulations force businesses to prioritize security and ethics upfront, preventing bigger problems down the road.
To stay ahead, organizations must:
- Identify relevant regulations and update security policies.
- Invest in risk assessments, penetration testing and employee training.
- Stay informed—more regulations are coming.
Compliance isn't just about avoiding penalties but about building a safer, more resilient digital future. Companies that act now will lead, while those that wait will fall behind.
You can read the original article posted in Forbes by Rhymetec CISO, Metin Kortak.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
The advent of the Digital Operational Resilience Act (DORA) has introduced a new set of regulatory expectations that financial entities operating in the European Union need to be aware of. Additionally, organizations such as SaaS startups that provide services to financial entities, or plan to, must begin preparing to meet DORA's requirements.
In a recent webinar hosted by Rhymetec and Vanta, we unpacked DORA requirements and discussed practical steps organizations can take now to align with DORA. Endri Domi, Infosec Manager at Rhymetec, moderated an insightful discussion between Faisal Khan, GRC Solutions Specialist at Vanta, and Metin Kortak, CISO at Rhymetec.
This blog post highlights the key points from their discussion, with a focus on what organizations need to understand and prioritize in the months ahead. You can check out the full webinar here.

What Are DORA Requirements, and Who Must Comply?
DORA requirements come from the EU's Digital Operational Resilience Act, which is now in effect. The regulation applies to financial institutions operating in the EU, as well as certain types of service providers that support them.
According to Faisal Khan, GRC Solutions Specialist at Vanta, the purpose of DORA is to improve the resiliency of financial institutions:
"DORA is an EU regulation designed to improve the ability of financial institutions to weather and recover from any information or technology-related disruptions like cyber attacks, data breaches, and system failures. It's really to build that tolerance for themselves so that they're protected in the event some of those things would happen." - Faisal Khan, Vanta
DORA covers both financial entities, such as banks, insurance companies, and investment firms, as well as their ICT third-party service providers. ICT (Information and Communication Technology) third-party service providers include cloud providers and other vendors that manage or support technology for other organizations.
The regulation introduces two types of regulatory documents that support its implementation:
Regulatory Technical Standards (RTS) and Implementing Technical Standards (ITS). RTS specifies what organizations must actually do to meet DORA's requirements, while ITS focuses on how the information should be reported. How each of the 5 pillars of DORA is applied in practice, as shown in the next section, is shaped by the technical standards.
What Are The Five Pillars of DORA Requirements?
DORA requirements are structured around five pillars. Each pillar is designed to reduce ICT-related disruption risk in financial services and strengthen the resilience of the ecosystem. In our webinar, our experts honed in on explaining each pillar in detail, particularly those involving third-party risk and incident reporting:
1. ICT Risk Management
Mitigating ICT-related risks across your organization's digital environment is a core part of DORA. Typically, this entails starting with a live, centralized asset inventory and linking each asset to a business function. This enables you to then align risk prioritization with actual operational impact, and helps keep future reporting manageable.
2. ICT-Related Incident Reporting
As highlighted by our experts, ICT-related incident reporting includes notifying both national competent authorities and any stakeholders who may be affected, such as customers or partners who rely on your platform:
"If you do have ICT-related incidents, those incidents will need to be communicated to the national authorities and other stakeholders who may be impacted by your platform, such as your customers." - Metin Kortak, Rhymetec
If an incident meets the criteria for "major ICT-related incident", you must notify your national competent authority (typically, your financial services or cybersecurity regulator) within 24 hours of detection. Follow-up reports are required as the situation evolves.
Incidents are classified based on metrics such as the number of users affected, duration of the disruption, and impact on data integrity or confidentiality. Your report should explain in detail what your response is and provide guidance for the recipient. The final report submitted to regulators must include a root cause analysis, detailing what happened and why it happened.
Bonus Tip: DORA goes further than GDPR by imposing stricter timelines, requiring a reporting process with multiple updates, and mandating the notification of any major ICT–related incidents (not just those involving personal data). In general, it covers a broader range of disruptions that impact operational continuity.

3. Digital Operational Resilience Testing
Under DORA requirements, operational resilience testing is addressed in Articles 24-27. Organizations must be able to demonstrate that their critical ICT systems can withstand disruption. Testing must be continuous and evidence-based:
"The point of this requirement is to ensure you have testing to verify that the resiliency of your application can be proved. This can be either third-party testing, or it can be internal testing." - Metin Kortak, Rhymetec
This includes a mix of internal exercises (such as tabletop exercises) and, where applicable, advanced testing techniques like threat-led penetration testing (TLPT). The intent is to ensure that your organization is able to 1) recover from disruption and 2) continue delivering critical services under adverse conditions.
For most organizations, the following action items are good options to fulfill the requirements in this pillar:
Tabletop Exercises
Tabletop exercises are scenario-based discussions that mirror real-world scenarios. Undergoing a tabletop exercise allows your organization to test its response capabilities, validate roles and responsibilities, and improve communication without affecting live systems.
Technical Testing
For systems deemed critical, DORA encourages more rigorous validation, which can take the form of failover testing, load testing, and red team exercises. Third-party involvement is encouraged at this stage, particularly for high-risk or business-critical functions.
Testing must occur on a regular basis and must reflect the scale and risk profile of your organization. DORA does not prescribe a one-size-fits-all cadence, but regulators will expect to see a documented rationale for test frequency and scope.
Remediation and Continuous Improvement
Testing is only the first part of the requirement. DORA also expects organizations to conduct lessons learned from testing, remediate weaknesses accordingly, and feed results back into their risk management and ICT governance processes.
The overarching goal of this requirement is to encourage a shift from static, checklist-driven compliance to real-world resilience. Instead of simply having a plan, organizations have to prove it works.
Bonus Tip: Don't forget about your critical third parties! We'll get into that more in the next pillar, but it's also relevant here. In areas where external service providers support your organization's critical functions, you'll need to evaluate their resilience as well. To do this, you can obtain assurance reports, risk assessments, validate their compliance with DORA if applicable, and/or coordinate joint exercises.

4. ICT Third-Party Risk
"If you do not understand your subprocessors, that's probably the first thing you want to do. If you have to comply with GDPR, you probably already understand the subprocessors that you're working with. For DORA, the next step would be to really understand how much data they process and how critical they are to your organization." - Metin Kortak, Rhymetec
One of the foundational steps in meeting DORA requirements is gaining full visibility into your third-party relationships. While organizations that already comply with GDPR are required to maintain records of data subprocessors, DORA introduces an operational resilience component that extends beyond data protection. Under DORA, your organization has to consider not only who you're working with, but how much risk those relationships introduce into your business.
Subprocessors often include cloud providers, SaaS tools, and outsourced IT or security vendors. DORA requires that financial entities mandate ICT third-party service providers that service those entities to map out these relationships and assess their criticality. Article 28 of DORA explicitly mandates risk assessments of ICT third-party service providers, with an emphasis on concentration risk.
"DORA also impacts the other third-party vendors and subprocessors that you are working with, because those vendors ultimately impact also the availability of your platform. For example, if you are hosted by a third-party hosting provider, they also impact the availability of your application. Therefore, you also need to conduct a risk assessment to ensure that the provider can actually support the resiliency of your application." - Metin Kortak, Rhymetec
If you are a financial entity subject to DORA requirements, you must maintain a register of all contractual agreements with ICT third-party providers and identify those considered "critical or important". This represents a broader industry shift from reactive vendor management to proactive operational resilience planning. Organizations that enact these changes will not only be positioned to comply with DORA, but also to build a more resilient overall business.
Other important considerations for the ICT-Third Party Risk Pillar include:
The Volume of Data Processed
How much sensitive or operational data flows through the vendor's systems? The more data processed, the higher the impact of a service disruption or breach.
Criticality to Business Operations
If a subprocessor experiences downtime, how does that affect your ability to deliver services, meet SLAs, and maintain operational continuity?
Dependency Risk
Are there alternative providers or workarounds if a subprocessor fails? If not, that relationship may require additional safeguards in your contract or contingency planning.

Oversight and Exit Strategy
Ongoing monitoring and having the ability to disengage from a vendor if needed (without causing your organization to risk operational issues!) are essential under DORA.
5. Information Sharing
DORA encourages financial entities to participate in trusted information-sharing arrangements around cyber threat intelligence. While not mandatory, participation supports sector-wide resilience.
Bonus Tip: Join regional or sector-specific ISACs (Information Sharing and Analysis Centers) early. This gives your team early visibility into threats targeting similar organizations, often before they've hit public feeds or the news.
What Are Some Considerations When Becoming DORA Compliant, According to The Experts?
As you are working to achieve compliance with DORA requirements, here are several practical considerations to keep in mind, according to our experts at Rhymetec and Vanta:
Trade Reporting Integrity
If your organization is subject to transaction reporting requirements (such as under EMIR or MiFIR), DORA reinforces the need for accuracy and completeness of those reports. Insufficient reporting could raise compliance concerns.
Lack of An Official DORA Certification
This is a common misconception.
Unlike some regulatory frameworks, DORA does not offer a formal certification or audit program. Instead of a formal certification, organizations are expected to demonstrate compliance with DORA requirements through internal audits or third-party assessments.
However, it's important to note that regulators still have the authority to request evidence and conduct inspections, so being "audit-ready" is still critical.
Framework Synergies
DORA is good at outlining what must be done, but often leaves the how to up to each organization and lacks specific implementation guidance. This opens the door to leverage existing security and compliance frameworks, such as ISO/IEC 27001 and 27002, SOC 2, or NIST, to guide implementation.

For example, DORA requires regular risk assessments but doesn't prescribe a methodology. Therefore, ISO 27005 or NIST SP 800-30 can provide details on how to actually carry out risk assessments. Aligning DORA controls with these frameworks, if you already have them, helps avoid duplicating your efforts.
In Conclusion: How Organizations Leverage vCISO Services To Meet DORA Requirements
A virtual CISO (vCISO) can play a critical role in preparing your organization to meet DORA requirements. vCISOs provide technical guidance and control implementation, operational support, and oversight without the cost of a full-time executive hire.
For startups, a vCISO can help build foundational controls, align existing security processes to DORA's requirements, and lead efforts like risk assessments, incident response planning, and third-party due diligence. For more mature organizations, a vCISO can support internal audit functions, map DORA requirements to existing frameworks (such as ISO 27001 or SOC 2), and create alignment between IT, legal, and compliance teams.
Regardless of organization size, a vCISO helps translate complex regulatory language into actionable plans that will hold up under regulatory scrutiny. vCISO services provide access at scale to top-tier cybersecurity and compliance services. vCISOs can also leverage the most cutting-edge tools, such as compliance automation platforms, to get you compliant in the fastest timeframe possible.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.
- DORA Compliance Checklist: What The EU's Digital Operational Resilience Act Means For Your Business
- Meeting EU AI Act Compliance: Core Requirements and Business Benefits
- Penetration Testing FAQ: What You Need To Know | Rhymetec
Working with a CMMC consultant is an attractive option for many organizations seeking to meet the updated CMMC requirements nowadays.
The Department of Defense (DoD) released CMMC 2.0 on October 15th, 2024, a requirement for defense contractors and subcontractors with the goal of improving cybersecurity standards. The updated version refines the original framework, aiming to simplify the path to compliance while maintaining the highest security standards for organizations that handle Controlled Unclassified Information (CUI) and other sensitive contract data.
One way in which the updated version simplifies compliance is by aligning requirements even more closely with existing cybersecurity standards like NIST SP 800—171. Many organizations may already comply with NIST 800-171 or another framework very closely aligned with it. Either way, the shift in compliance expectations has led many organizations to assess whether they have the in-house resources to manage security or if they need external support through a CMMC consultant.
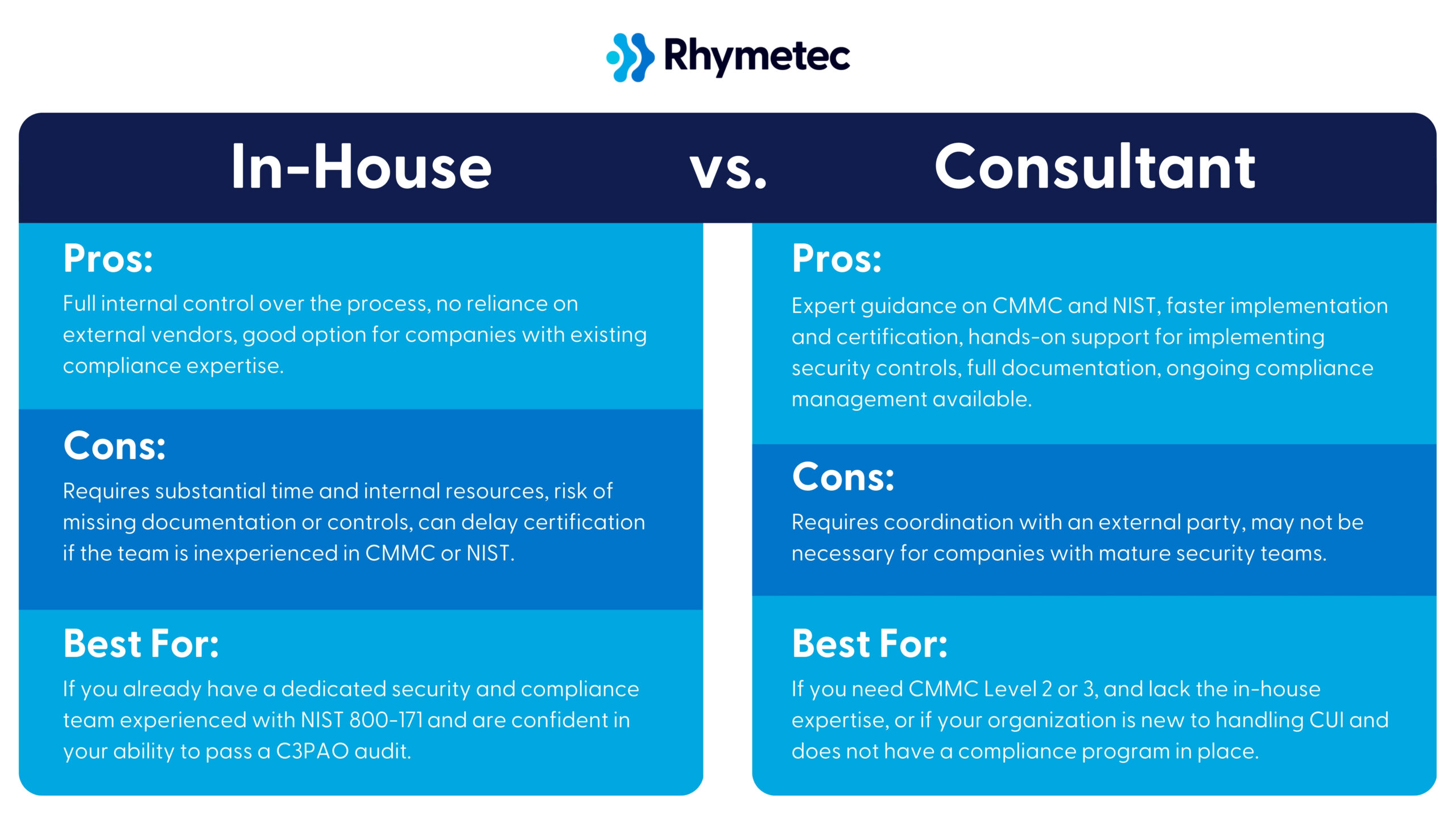
Working with a Managed Security Services Provider that offers CMMC consulting services (like Rhymetec!) can help contractors meet CMMC 2.0 requirements efficiently. MSSPs take the work off your plate and help you meet your goals in the fastest time frame possible. We've helped over 1,000 organizations meet their compliance and security requirements in the fastest time frame possible.
In this article, we go over how CMMC 2.0 works, the options available for achieving compliance, and the potential advantages of working with a CMMC consultant.
What Is A CMMC Consultant, and What Do They Do?
Unless you have a fully built-out in-house cybersecurity and compliance team, CMMC can be a massive project to take on internally—taking a year or longer to meet requirements. This is where a CMMC consultant comes in.
A CMMC consultant is a cybersecurity and compliance expert who helps defense contractors meet the requirements of the Cybersecurity Maturity Model Certification (CMMC) 2.0. Consultants do everything from conducting a gap assessment to see where you are versus where you need to be, developing practical strategies to achieve compliance that will fit seamlessly (and as non-disruptively as possible!) into your operations, and guiding you through the certification process in partnership with an external auditor.
For many businesses, especially small and mid-sized contractors, understanding and implementing CMMC controls can be challenging. A CMMC consultant provides tailored, specialized knowledge to streamline the entire process, reduce your risk of non-compliance, and make big improvements to your overall security if you do not already have certain measures in place.
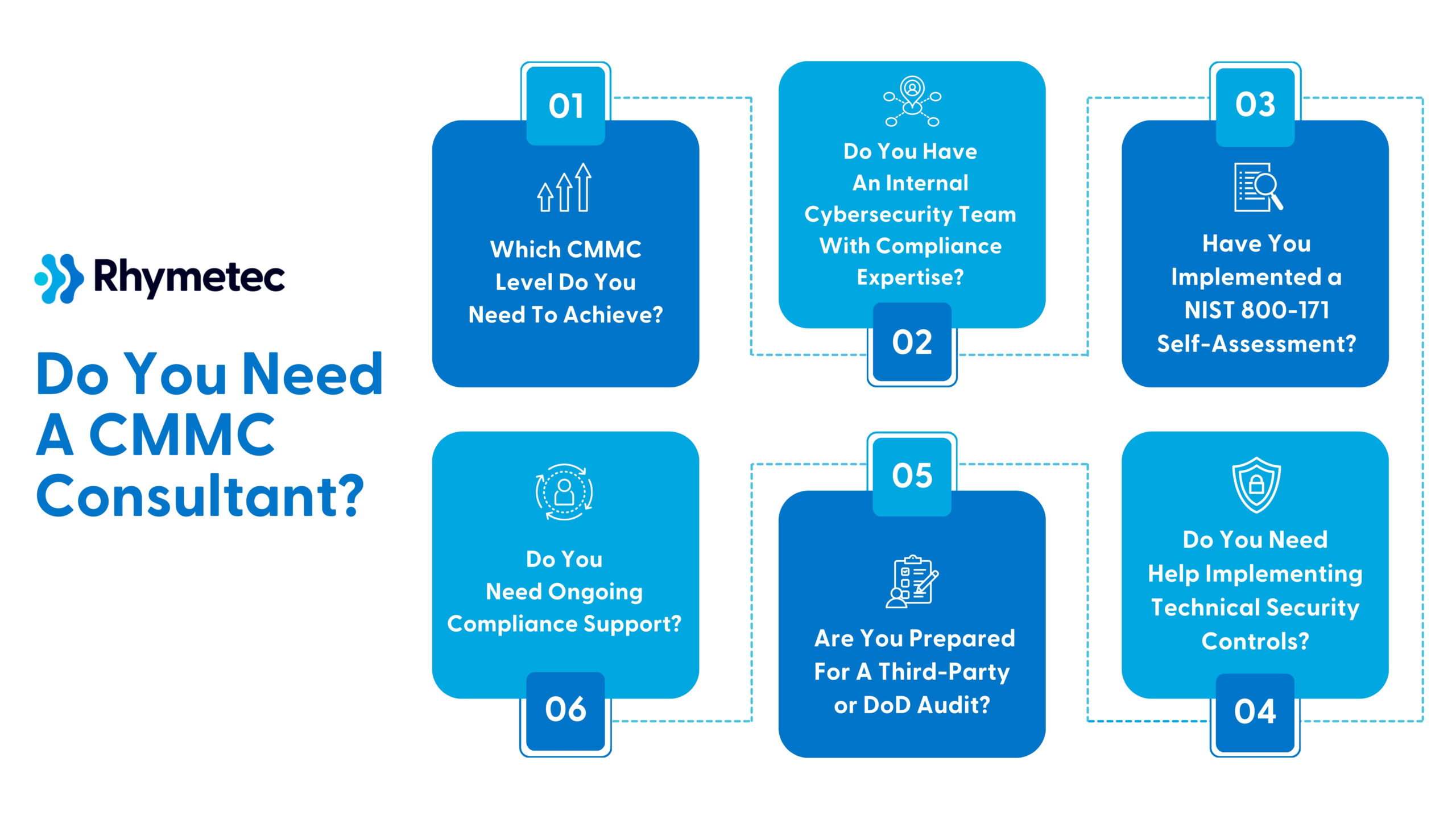
Do You Need A CMMC Consultant?
The best way to determine if you need a CMMC consultant is to look through the responsibilities and deliverables in the next section and assess whether or not you have the in-house capacity to fulfill all of these items.
If you are a larger organization and already have a security team with personnel that can accomplish the necessary tasks for CMMC (A Chief Information Security Officer, Penetration Tester, Cloud Security Specialist, Vulnerability Management Analyst, etc.), you can probably do most of this on your own or with guidance from a CMMC consultant rather than full support.
However, for smaller organizations or those without a fully developed in-house security program, engaging a CMMC consultant entails multiple benefits.
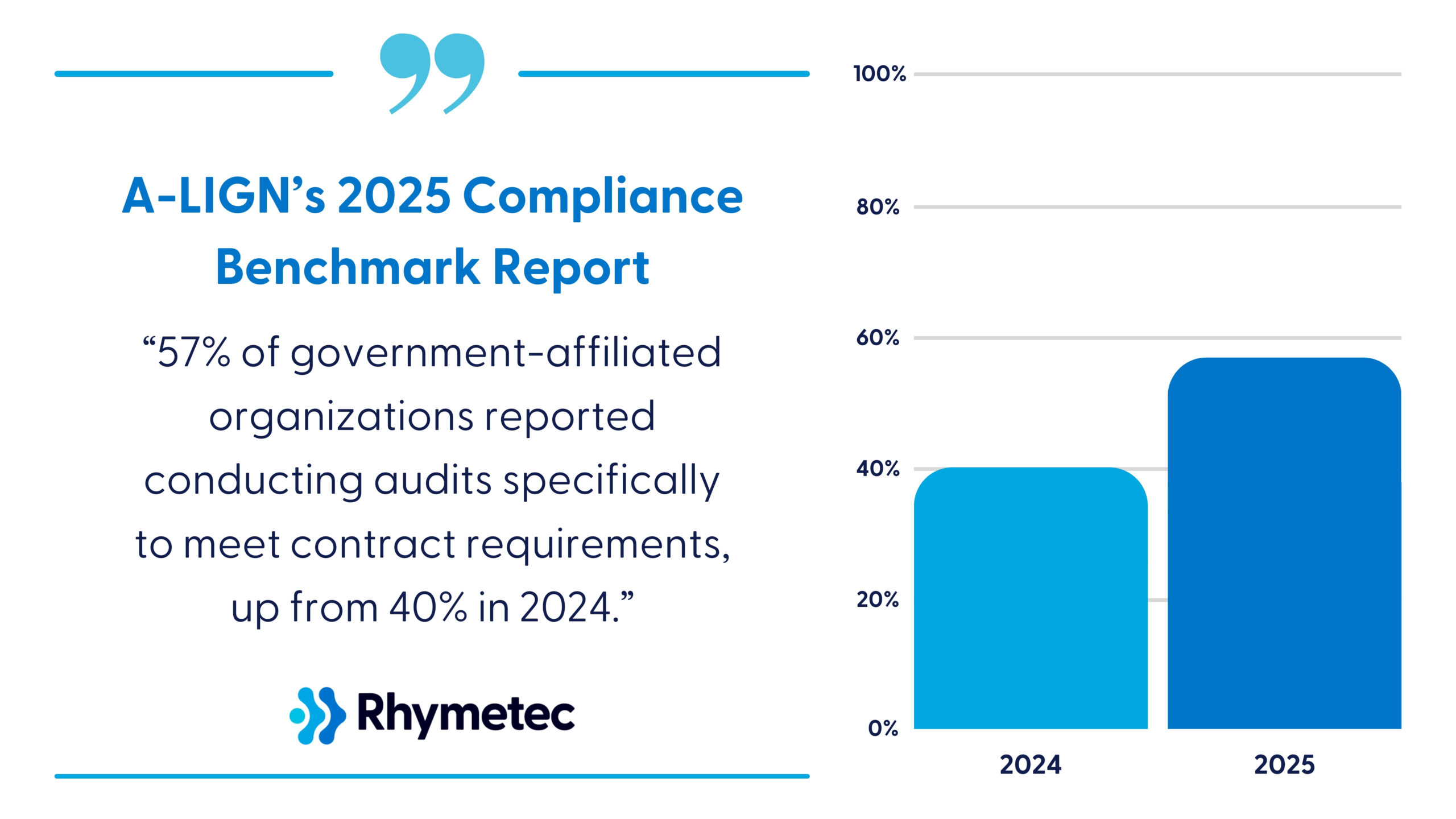
According to A-LIGN’s 2025 Compliance Benchmark Report, 57% of government-affiliated organizations reported conducting audits specifically to meet contract requirements, up from 40% in 2024. DoD contractors and subcontractors will need to obtain certification under one of three trust levels to demonstrate that they have adequately implemented cybersecurity measures.
Below are some questions to help you assess whether working with a consultant is the right choice. After you answer these questions and review the responsibilities and deliverables listed below in the next section, you should have a clear picture of whether or not you need a CMMC consultant:
1. Which CMMC Level Do You Need To Achieve?
The CMMC level you need depends on the type of contracts you handle:
CMMC Level 1 (Basic Cyber Hygiene) is required for contractors who only handle Federal Contract Information (FCI). Compliance is self-assessed, but security controls must still be implemented.
CMMC Level 2 (Advanced Cyber Hygiene) is required for contractors who handle Controlled Unclassified Information (CUI). Compliance requires a third-party assessment (C3PAO) every year.
CMMC Level 3 (Expert) is required for contractors who are working on high-security DoD projects. Compliance entails DoD-led audits and adherence to NIST SP 800-171 and portions of NIST SP 800-172.
If you need CMMC Level 2 or Level 3, working with a CMMC consultant can be extremely helpful, given the amount of work involved in the third-party assessment process, implementing missing security controls, and maintaining ongoing compliance.
2. Do You Have An Internal Cybersecurity Team With Compliance Expertise?
If you have a dedicated cybersecurity and compliance team, you may be able to handle CMMC requirements internally. Even if you do have an internal team, however, a CMMC consultant can still be beneficial if:
- Your internal team is unfamiliar with NIST 800-171 and CMMC requirements.
- You need help preparing evidence for a third-party assessment.
- Your security team does not specialize in compliance or lacks the expertise to develop CMMC procedures and policies.
3. Have You Implemented a NIST 800-171 Self-Assessment?
If you need CMMC Level 2 or Level 3, you should already have a NIST 800-171 self-assessment and an SPRS score recorded. If you haven't completed this step, a CMMC consultant can guide you through the process. Additionally, if your SPRS score is low, or if you have many missing security controls, you may need a consultant to develop a remediation strategy before moving forward.
4. Do You Need Help Implementing Technical Security Controls?
There are a range of technical security controls required by CMMC that many organizations may not have adopted yet. If your company lacks the bandwidth to deploy these measures, a CMMC consultant can provide guidance and support (or do it for you, depending on the level of support outlined in the engagement). These types of technical controls include configuring multi-factor authentication, implementing network segmentation, SIEM logging and monitoring, and vulnerability management.
5. Are You Prepared For A Third-Party or DoD Audit?
For Levels 2 and 3, organizations have to pass an official assessment conducted by a Certified Third-Party Assessor Organization (C3PAO) or the DoD. The most common issues contractors face with these assessments are due to insufficient documentation, improperly implemented controls, or lack of audit preparation. A CMMC consultant can remediate these issues and more in advance of your assessment.
6. Do You Need Ongoing Compliance Support?
Lastly, it's important to know that CMMC compliance requires ongoing monitoring and maintenance. You'll need to keep your certification in good standing year-round. If your organization does not have a dedicated team to handle continuous compliance, a CMMC consultant can provide long-term security and compliance management. Ongoing support can include:
- Review of your security controls
- Vulnerability scanning (and remediation as needed)
- Incident response drills
- Log reviews and SIEM tuning.
If the answer is "yes" to multiple questions, partnering with a CMMC consultant may be a good option for your organization.
Next, let's go over what a CMMC consultant typically accomplishes for organizations throughout the engagement. This should help give you a good idea of what to expect:
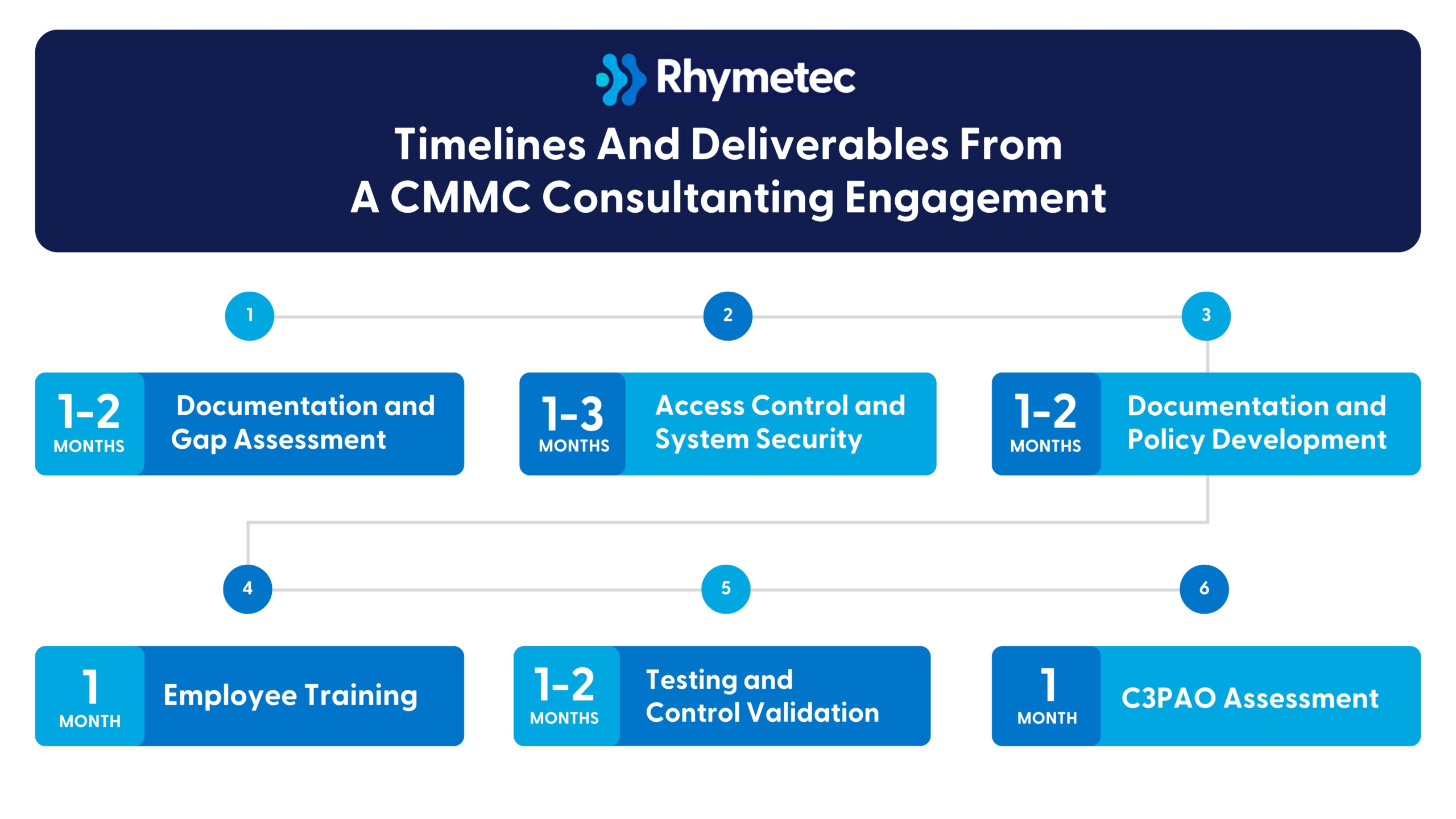
Timelines And Deliverables From A CMMC Consultanting Engagement
A CMMC consultant provides end-to-end support to help defense contractors achieve CMMC compliance. At a high level, this process entails assessing your organization's current security posture, implementing the required controls you don't already have, developing documentation, training personnel, and preparing for the official assessment.
Here is what this process and the deliverables will look like, in general, for an organization starting from a more basic security posture:
1. CMMC Initial Assessment - Documentation and Gap Assessment:
- Conduct a gap assessment to assess your current CMMC maturity level.
- Review existing security documentation to determine alignment with CMMC 2.0. requirements and identify any gaps in your documentation to be addressed before certification.
- Review CUI/FCI data flows to assess how sensitive information is handled.
- Map current security controls to NIST SP 800-171 and CMMC requirements.
- Document your organization's Supplier Performance Risk System (SPRS) score.
- Develop a preliminary Plan of Action & Milestones (POA&M) to address deficiencies.
- Estimate resource requirements for remediation.
Timeline With A CMMC Consultant: 1-2 Months
2. Implementation of Access Control and System Security
- Configure multi-factor authentication (MFA) for all required systems.
- Implement least privilege access principles to restrict user permissions.
- Set up remote access controls and document access control procedures.
- Deploy a Privileged Access Management (PAM) solution for sensitive accounts.
- Implement network segmentation and develop network diagrams.
- Deploy endpoint protection solutions.
- Configure logging and monitoring systems, including SIEM solutions.
- Set up backup solutions and document backup and recovery procedures.
Timeline With A CMMC Consultant: 1-3 Months
3. Documentation and Policy Development
- Develop a System Security Plan (SSP) documenting security controls.
- Create an Incident Response Plan for handling security incidents.
- Establish a Disaster Recovery Plan.
- Create training documentation for security awareness and compliance.
Timeline With A CMMC Consultant: 1-2 Months
4. Training
- Conduct security awareness training for employees.
- Develop role-specific training for personnel handling CUI/FCI.
- Run incident response drills to prepare teams for cyber threats.
- Train employees on documentation procedures.
- Hold policy review sessions.
Timeline With A CMMC Consultant: 1 Month
5. Testing and Control Validation
- Perform internal control testing to verify compliance.
- Conduct vulnerability assessments and penetration testing to evaluate system defenses.
- Review security documentation for accuracy/completion.
- Validate processes and security controls through real-world testing.
Timeline With A CMMC Consultant: 1-2 Months
6. C3PAO Assessment
- Conduct a final documentation review to make sure all requirements have been met.
- Validate security controls against CMMC 2.0 standards.
- Prepare teams for staff interviews conducted during the official assessment.
- Perform technical testing to confirm systems meet all requirements.
Timeline With A CMMC Consultant: 1 Month
Ongoing Maintenance
To maintain compliance and readiness for recertification, a CMMC consultant provides ongoing support through the following:
- Monthly security control reviews to assess compliance status on an ongoing basis.
- Vulnerability scanning to identify and remediate emerging threats.
- Access reviews to ensure permissions remain properly restricted.
- Incident response testing to evaluate security team preparedness.
- Log review to monitor system activity and detect anomalies.
Why Work With A CMMC Consultant?
Achieving compliance is not simple. There is an array of technical and procedural controls and extensive required documentation. A CMMC consultant helps businesses navigate these requirements by providing specialized expertise (at a much lower price point than building out an in-house team would cost) and reducing administrative burdens.
Many defense contractors lack the in-house resources to manage requirements, especially as the DoD increases enforcement of cybersecurity standards. Often, for example, small defense contractors with no formal cybersecurity programs need to achieve CMMC Level 1 to continue bidding on DoD contracts. Having limited IT staff and a lack of security policies and policies can be a significant roadblock.
In this scenario, a CMMC consultant would help by starting with an initial assessment to determine the company's current security posture and documentation and, from there, develop all missing policies, procedures, and documents. Often, this includes a System Security Plan (SSP), access control policies, and an incident response plan.
Many contractors also underestimate the complexity of CMMC and wait too long to start the process. The risk of failing an assessment can lead to contract loss and reputational damage. Working with a CMMC consultant reduces risk, streamlines implementation, strengthens your cybersecurity, and ensures you stay audit-ready year-round.
If your business relies on DoD contracts, CMMC certification isn't optional. Engaging a CMMC consultant early on in the process saves significant time and headaches down the road.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.

Meet Matt!
I'm an analyst based in GA who graduated from Kennesaw State University with my Bachelor's in Cybersecurity in May of 2023. I also dabble in some other technical work too! I consider myself a handyman as I can work with a lot of various tools and know that I have the capacity to do more in the future.
Outside of technical work, I like to make digital art and do landscaping. I took a lot after my grandpa, who was a multi-talented man and who knew how to get stuff done!
Tell us a surprising fact about yourself…
I'm not quite ambidextrous, but I've taught myself how to do a lot of things with my left hand! All things outside of writing, that is. Maybe I'll get there someday!
If you could have any superpower, what would it be?
Teleportation. We lose a lot of time due to travel and being in-between places… It'd be a convenient power, however, I'd probably become super out of shape and chunky because I'd get lazy and never move anywhere normally as a result…
What are some things you enjoy doing outside of work?
I jog in the mornings and like to go on a trail during the weekends. I also like to tinker with electronics and fiddle with gadgets whenever I have the opportunity to do so!
Tell us about your role at Rhymetec…
It's currently my one-year anniversary at Rhymetec! My role is to help aid my project manager in his work by better understanding our clientele's environments and programs so I can assist with inquiries and even offer suggestions or analysis on how they can better improve their security standing.
I really like working here because it's exposing me to a wide variety of tools and environments that I probably wouldn't have encountered so soon. The experience that I'm receiving here will be invaluable for the rest of my career! I can also kind of brag to my buddies that I can conduct ISO/IEC audits too.
Why did you pursue a career in the cybersecurity industry?
I originally majored in Engineering before finding that a lot of the theory wasn't sticking to me. I'm more of a hands-on person who works better with several manuals in front of me and enough time to make things happen. I was pursuing interests in IT/CS after the fact before finding that Cybersecurity had the right level of "hands-on” that interested me.
As to how I ended up with Cybersecurity, funnily enough, there was a representative who came into one of my lectures while I was in university who tipped me off to considering a degree change with Cyber!

What is your favorite part about working at Rhymetec, or in the cybersecurity industry?
Lots to learn everywhere. Cybersecurity is as much of a theory as it is a concept. It concerns itself with information technology and similarly connected devices. In the end, it's risk management, contingency planning, and fortifying defenses! It's an ever-evolving race towards what guards our assets in the best possible way, with more creative and unique ways continuing to be found for people to defend (or even attack) with!
What is the best advice you have ever received?
I read this from an art book and have it pinned on my wall since it applies to many areas outside of art:
"TALENT: Don't bother about whether or not you have it. Just assume that you do, and then forget about it. Talent is a word we use after someone has become accomplished. There is no way to detect it before the fact, or when someone is still grappling with the learning process. It is impossible to predict when or if mastery will click into place. Besides, the thing we label as talent is not a single ability. It is a complex mixture of motive, curiosity, receptivity, intelligence, sensitivity, good teaching, perseverance, timing, sheer luck, and countless other things. If any part of it is genetic, God-given, the result of astrological fiddle-faddle, fate, or destiny, that part is not the sole determining factor. All the other ingredients must be present in the right combination–and no one knows the exact recipe. Therefore Dear Reader, don't waste time worrying if you are talented—and don't blame any failures on the lack of it–that is really a cop-out."
- Richard Schmid, "Alla Prima II – Everything I Know About Painting - and More"
From a security or compliance perspective, what advice would you give to a potential client or SaaS business?
This one's a tough one, as I'm still relatively fresh out of university! I feel like more of a senior role or more experienced member could give better insight here… that, or I'd be parroting them, which isn't a bad thing! I think the best advice I could give is:
"Which would you prefer: the pain of diligence or the pain of regret?"
This could apply to a lot with regards to ensuring that appropriate preventive measures are in-place against threats and threat actors.
Connect with Matt Jenkins
Leading cloud security company celebrates 10 years of success attributing sustainable growth to its highly skilled team, strategic partnerships and expanding globally.
(NEW YORK — March 28, 2025) –
Rhymetec, the industry leader in cloud security that provides innovative cybersecurity, compliance and data privacy services to modern-day SaaS businesses, today announces multiple significant accomplishments in honor of its 10-year anniversary. These include continued company growth, both in the U.S. and internationally, service expansion, and strengthened strategic partnerships.
"I could not be more proud of the accomplishments of our team at Rhymetec. For the past 10 years, we have continued to evolve to meet our client's needs, while navigating constant changes in the industry," said Justin Rende, founder and chief executive officer of Rhymetec. "We've built a network of trusted partners to better serve our customers and looking to the future, we remain committed to the same mission we started with — to deliver sustainable compliance strategies with the highest security standards."
Since its founding in 2015, Rhymetec has experienced notable milestones and accomplishments, including:
Company Growth:
- Rhymetec has more than 35 full-time employees today. Rhymetec is proud to state that they do not outsource their services.
- Has served more than 1,000 clients spanning companies of all sizes from startups to enterprises
- Helped clients manage more than 1,200 Audits
- Completed more than 900 Penetration Tests
New Frameworks and Compliance Offerings for 2025:
These offerings are alongside Rhymetec's Virtual CISO (vCISO) service:
- CMMC
- DORA
- NIS-2
- EU AI Act
- Data Privacy Framework
Rhymetec's strategic partnerships and active participation in key industry events have been essential to the company's success and growth. Over the years, collaborations with industry leaders like Vanta, Drata, A-LIGN, and others have not only solidified Rhymetec's role as a trusted partner but also fueled momentum for shared growth. Joining together on events such as Vanta's company kick-off and Drata and A-LIGN's sales kick-off serve as opportunities to strengthen relationships, exchange insights, and drive collective innovation in the cybersecurity and compliance space.
These partnerships, along with sponsorships at major conferences in Q1 like ViVE, reinforce Rhymetec's commitment to elevating industry standards, supporting clients through their growth phases, and driving forward the shared mission of delivering top-tier security and compliance solutions.
Further notable in Rhymetec's success is in its strategic approach to employee development. The company recently announced the promotion of Endri Domi, one of Rhymetec's first employees, from security program manager to information security manager. In his new role, Domi will help lead Rhymetec's team of highly skilled security professionals.
"I am grateful for the trust and support from my colleagues and leadership at Rhymetec," Domi said. "I am excited to tackle new challenges and continue delivering excellence in information security for our clients."
To learn more about Rhymetec and its suite of cybersecurity services, visit www.rhymetec.com.
About Rhymetec
Rhymetec is an industry leader in cloud security, providing innovative cybersecurity and data privacy services to the modern-day SaaS business. The company builds, deploys and manages compliant information security and data privacy programs directly within their customers' unique environments, allowing them to focus on their core competencies within their business. Over the years, Rhymetec's services have grown to include a vCISO (virtual CISO) program, ISO internal audits and a variety of penetration testing services. For more information, visit www.rhymetec.com and follow on Twitter or LinkedIn.
You can read the original press release on PR Newswire.
To Learn More About Rhymetec's Services
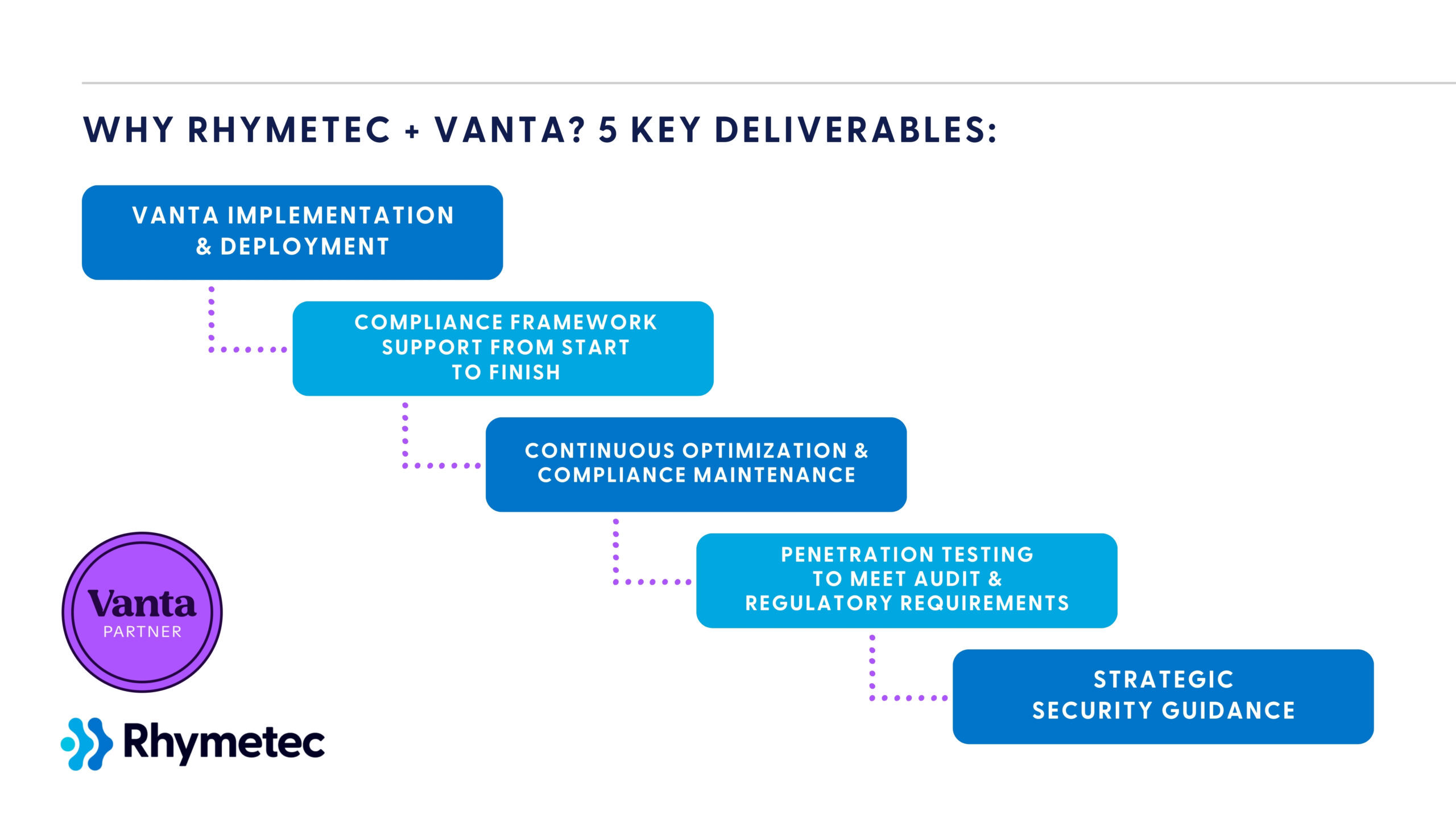
As an industry leader in cybersecurity and compliance, Rhymetec is proud to partner with Vanta to deliver a complete solution for modern businesses. As Vanta's 1st MSP partner, together, we fast-track compliance, strengthen your security posture, and reduce the time and effort needed to meet regulatory requirements.
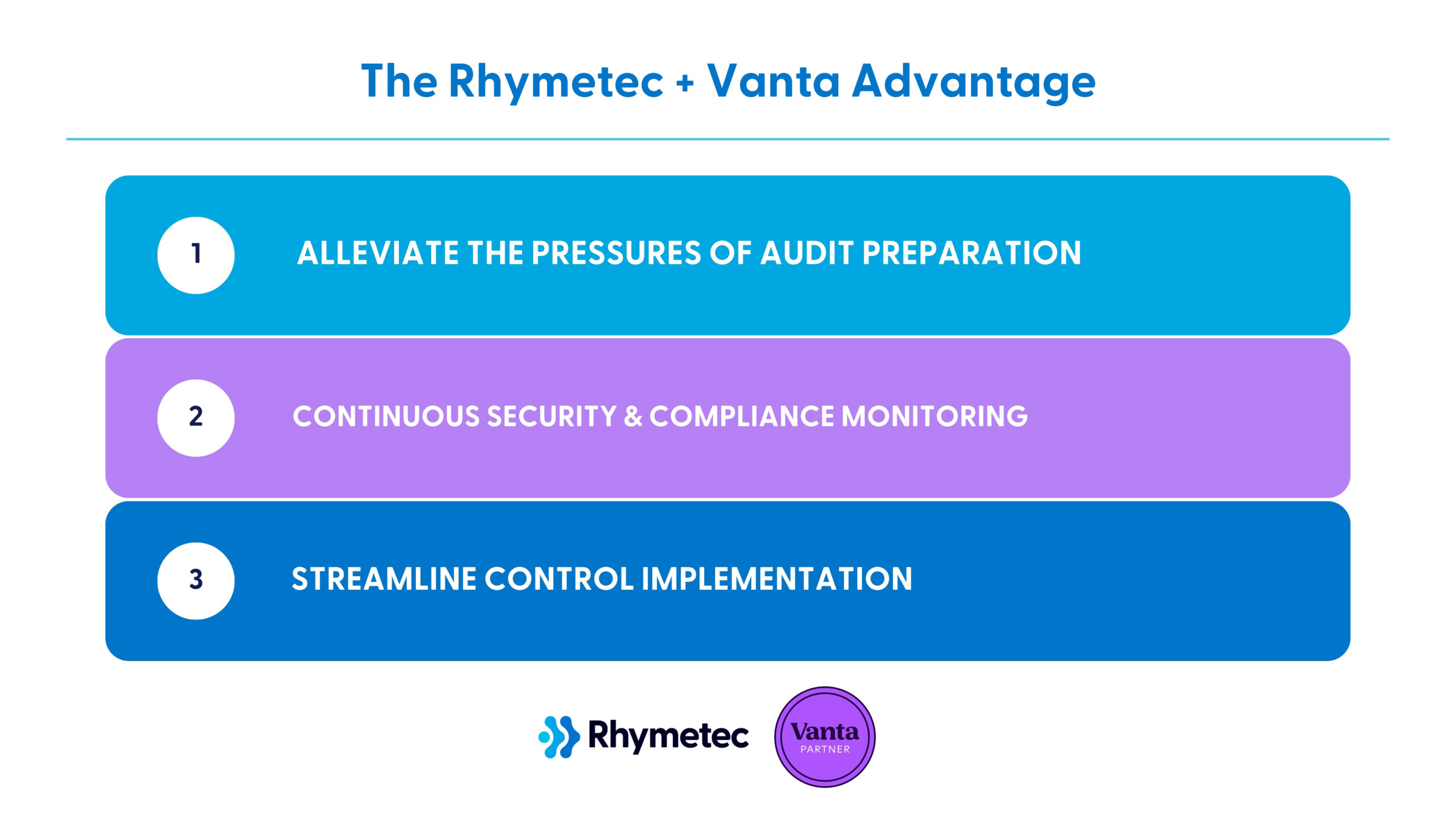
The Rhymetec + Vanta Advantage
Our team at Rhymetec leverages Vanta to transform compliance from a complex challenge into a strategic advantage for your business. Over the last decade, we've helped over 1,000 companies around the world meet their security and compliance goals.
With our joint services, you can:
1. Alleviate The Pressures of Audit Preparation
Vanta was built with auditors and the audit process top-of-mind. Rhymetec will ensure you have all the documents and evidence necessary for the audit itself, and manage the audit process using Vanta as a source of truth.
2. Access Continuous Security and Compliance Monitoring and Support
Vanta's automation capabilities help achieve ongoing compliance maintenance and management, while Rhymetec's vCISO services address ongoing security efforts and questionnaires, aiding new phases of growth.
3. Streamline Control Implementation With Vanta Compliance Services
Rhymetec implements controls required by the compliance framework selected by the client. Vanta plays a key role in this process for each control through system integrations and identification of areas for improvement.
Together, we provide a simplified approach to security and the compliance automation process. We work together to provide an automated and comprehensive solution, saving significant time and resources for you.
Our Vanta Compliance Services
Vanta Implementation and Deployment
Vanta automates 90% of compliance tasks through integrations with 300+ systems, real-time control monitoring, and automated evidence collection.
The Rhymetec team configures and deploys the platform on your behalf, integrating it with your infrastructure to maximize automation capabilities. We connect relevant systems, set up automated workflows, and customize policies to fit your organization and the selected compliance framework.
With Vanta deployment carried out by our experts, your team avoids the complexity of configuring integrations. From day one, we ensure accurate and reliable compliance monitoring and allow you to dramatically reduce the burden on your internal resources.
Compliance Framework Support From Start To Finish
Vanta provides pre-built controls for 20+ frameworks, including SOC 2, ISO 27001, HIPAA, and GDPR. It automates scoping and document management and provides a foundation for policy creation. The Rhymetec team aligns these automated capabilities with your business needs and your selected compliance framework, performing the tasks required for full compliance such as internal audits, tabletop exercises, and evidence preparation.
Managing compliance without a dedicated team can lead to missed controls or even doing too much and implementing unnecessary requirements. By handling the full compliance process, we eliminate uncertainty, accelerate your audit readiness, and ensure your documentation fully meets auditor expectations.
Continuous Optimization and Compliance Maintenace
Vanta's continuous monitoring identifies failing controls, missing security measures, and real-time compliance risks. Automated notifications provide alerts to potential issues, and remediation workflows drive fast resolution.
Our team at Rhymetec oversees these alerts, interprets risk impacts, and executes the manual corrections on your behalf so you can maintain compliance.
Ongoing compliance management is resource-intensive. Without expert oversight, organizations risk falling out of compliance between audits. With our team handling continuous monitoring and remediation, your organization stays audit-ready, reduces compliance drift, and proactively addresses any security gaps.
Penetration Testing To Meet Audit and Regulatory Requirements
Many voluntary frameworks as well as legal requirements require penetration testing.
SOC 2, PCI DSS, ISO 27001, CMMC, and HIPAA all include requirements to regularly test network and application security. Regulations such as GDPR and CCPA also encourage proactive security measures to identify vulnerabilities before a security incident can occur, and penetration testing can be used to fulfill these requirements.
Rhymetec started as a penetration testing company in 2015, and we offer the highest quality penetration tests to meet your organization's compliance obligations while enhancing its security posture. We provide detailed reports of the findings, along with remediation recommendations, helping your organization address security gaps before an audit.
We offer a range of penetration testing services to fit your security and compliance needs, including mobile application penetration testing and web application penetration testing.
Strategic Security Guidance
Vanta's AI-driven features streamline core compliance areas to include risk management, access reviews, vendor security assessments, and security questionnaires. The platform accelerates compliance workflows, while expert guidance from Rhymetec's team enables you to interpret findings, implement security best practices, and customize controls based on your unique risk profile and risk appetite.
Security and compliance strategies must be tailored to business needs. Without in-house expertise, it can be difficult to implement effective controls. With Rhymetec's team providing ongoing guidance, while leveraging Vanta's cutting-edge integrations and capabilities, you gain a compliance program that meets regulatory requirements while reducing risk to your organization and maintaining operational efficiency.
Why Rhymetec?
Transparency:
We believe our clients deserve complete clarity about what they're getting, how we work, and the results they can expect. Whether it's our methodologies, testing scope, or the tools we use, we provide detailed insights at every step.
Autonomous:
As a self-funded company, we have the freedom to make client-focused decisions quickly and flexibly. This independence allows us to adapt our services to meet your unique needs and help our partners win in competitive scenarios. Our autonomy ensures every decision prioritizes your success.
Team Credentials:
Our team boasts a broad range of industry-recognized certifications, including Burp Suite Certified Practitioner, ISC2 CISSP, EC-Council CHFI, CPENT, Offensive Security: OSE3 OSED OSEP OSWA OSWE OSCP, and CompTIA Security+, PECB Internal Auditor Certifications, and more.
Market Maturity:
Rhymetec was founded in 2015. Our specialized expertise ensures a deeper understanding of your business's unique challenges, providing the most impactful security insights. Don't settle for less experienced competitors when it comes to protecting your business or meeting the needs for compliance requirements.
Frameworks Supported by Rhymetec's Vanta Compliance Services
Achieve compliance faster and with greater confidence with Vanta's automation and Rhymetec's hands-on security expertise. Together, we streamline control implementation and tackle every step of the compliance process for you. We fully manage the following frameworks (and more) on your behalf, from start to finish, getting you over the finish line with your audit in the fastest time frame possible:
SOC 2 With Vanta & Rhymetec
Vanta automates control monitoring, policy management, and evidence collection for SOC 2, reducing the time required to prepare for an audit. As SOC 2 allows flexibility in control implementation (which requires interpretation to align with your business operations), the Rhymetec team ensures that automated controls are properly scoped, fills in gaps with manual tasks like risk assessments and penetration testing, and guides your team through audit readiness.
ISO 27001 With Vanta & Rhymetec
Vanta accelerates ISO 27001 certification by automating risk assessments, system inventory, and document management, including the Statement of Applicability. ISO 27001 also requires internal audits and ongoing security improvements. Our team at Rhymetec handles these manual components and others, develops custom policies, and aligns your Information Security Management System (ISMS) to your business risks.
GDPR
Vanta supports GDPR compliance through automated access reviews, vendor risk assessments, and security monitoring. GDPR compliance also entails implementing legal and operational processes, such as data mapping, incident response planning, Data Protection Impact Assessments, and more. At Rhymetec, our vCISOs carry out these actions and ensure that all of your privacy policies, manual risk assessments, and data processing agreements are in full alignment with GDPR requirements.
HIPAA
Vanta automates HIPAA compliance by monitoring technical safeguards, conducting access control reviews, and managing security policies. For the aspects of HIPAA compliance that require administrative safeguards, such as employee training, documented risk management procedures, and business associate agreements, the Rhymetec team bridges the gap by filling in or fine-tuning these items. For example, we implement customized employee training and advise you on regulatory expectations. Leveraging Vanta and our services provides a complete approach to HIPAA compliance.
PCI DSS
Vanta identifies security gaps related to PCI DSS controls, while the Rhymetec team fills pieces such as penetration testing, network segmentation, and quarterly scanning. Our experts ensure that all PCI DSS requirements are met, manages security assessments, and handles auditor interactions for you. By combining Vanta's automation with our technical security expertise, you meet the requirements in the fastest timeframe possible and maintain continuous compliance over time.
CMMC
Vanta helps streamline CMMC compliance by automating areas such as security control monitoring and access review. While working to meet the extensive CMMC requirements under risk management, ongoing assessments, and security controls, a dedicated team of security and compliance experts can greatly reduce the complexity for your organization. While leveraging Vanta, Rhymetec’s team ensures that all necessary security measures (including incident response planning tailored to your organization, system security plans, and third-party risk management) are correctly implemented.
Additional Frameworks Supported By Rhymetec and Vanta
Beyond the frameworks listed above, Vanta and Rhymetec support a range of other compliance frameworks. These include ISO/IEC 42001 for AI risk management, DORA for financial sector resilience, HITRUST CSF for healthcare security, NIST AI RMF for AI governance, The California Consumer Privacy Act (CCPA), and various other global and industry-specific standards.
For any framework(s) you select, using Vanta in conjunction with Rhymetec's guidance streamlines certification, strengthens your security operations, and sets you up for successful long-term compliance.
Ready to Simplify Your Vanta Compliance Journey?
Don't let compliance barriers slow down your growth.
Our experts are ready to transform security from a roadblock to a competitive advantage. We leverage the most cutting-edge tools like Vanta on your behalf and remove the work entirely off your plate so you can get back to what really matters - running your business. Contact us today to learn more.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.
Meet Kelsey!
Hello! My name is Kelsey. I grew up in Groton, Massachusetts - think cows, farms, and a lot of trails for biking, walking, and exploring nature. Growing up, I spent every summer at my Nana's beach house in North Hampton, NH, with my brothers. During the school year, my studies, field hockey, and exploring the huge woodlands behind my house was all that mattered! Post high school, I got my Bachelor's Degree in Communications and a minor in Psychology at Emmanuel College in Boston, MA. I stayed in Boston for a couple of years, living with my best friend and the city life. It was amazing, and ultimately started my HR career as an Administrative Assistant as I slowly took on more HR responsibilities. I couldn't imagine a different career path!

Tell us a surprising fact about yourself…
I've always loved to write, especially poetry. I'm slowly working towards a huge personal goal of creating and publishing my first poetry book under a pseudonym.
If you could have any superpower, what would it be?
I would want the superpower to communicate with all animals - mammals, birds, insects, fish, etc. I'm extremely passionate about all animals and believe it's our obligation as humans to treat all wildlife with respect and compassion. To have the ability to communicate with them directly would allow us as humans to better serve the Earth and live in a symbiotic world with them.
What are some things you enjoy doing outside of work?
Outside of work, I love to immerse myself in nature and new activities. I try to get my outside-of-work creative juices flowing, and that looks like:
1. LOTS of nature walks, camping, and hikes!
There are so many beautiful places near me, and I try to do at least 3 new hikes a month on the weekends.
2. *Trying* to play the ukulele - I'm self-taught, but it's fun learning new chords and painfully trying to sing along.
3. Writing poetry and short stories, often inspired by my surroundings. I'll take my writing notebook to the beach and listen to some music or take in the scenery for inspiration.
4. Exploring new restaurants and different cuisines. I love food and don’t shy away from trying unique dishes. I have a running Excel spreadsheet with every restaurant I've eaten at in Santa Barbara since moving here, and the list grows almost every week (my wallet doesn't like this hobby of mine).
5. Working out has been a huge part of my life most recently, and I've focused on moving my body every day and lifting weights. It's the best stress reliever, and has helped me get stronger with trying to surf the California waves!

Tell us about your role at Rhymetec…
I've been at Rhymetec for almost a full year, and lead our people initiatives as our People Operations Specialist.
For Rhymetec and our employees, I manage:
- Talent Acquisition processes from curating job descriptions, building candidate pipelines, and conducting the recruiting process from initial phone screen to onboarding new hires
- Internal HR compliance
- Implementation of HR technologies and manage existing HR technologies
- Performance Management
- Training, Learning, & Development
Why did you pursue a career in the cybersecurity industry?
I'd been in the technology industry for the last 4 years, working at a Financial Technology company (in HR) before pursuing Rhymetec. I love working in tech - it's fast-paced and challenging, and you're constantly learning! The work is rewarding as well - helping companies (internal and external) achieve their goals in the cybersecurity space is vital for their success. When I saw the opportunity to work with and for Rhymetec, it felt like a natural next step for me to get into the cybersecurity world from FinTech.
What is your favorite part about working at Rhymetec, or in the cybersecurity industry?
First and foremost, our leadership team and employees are incredible. They have taught me so much about cybersecurity in the last year working with them, and never shy away from a learning moment or giving insights into what is happening in the industry to support me in recruiting or internal efforts.
Working within cybersecurity has taught me how important it is to stay digitally vigilant. I'm able to share this knowledge with my friends, family, and others to stay protected against scams and hackers, and keeping their data safe.
What is the best advice you have ever received?
"Life is a succession of lessons which must be lived to be understood." - Ralph Waldo Emerson
This is a quote I keep in my back pocket. I used to be afraid to put myself out there professionally and personally. Whether it's speaking my mind, disagreeing with an internal process, or having a solution in mind to enhance something that isn't working. This quote is the best life rule to me. If you don't put yourself in new, uncomfortable experiences, your life will stay stagnant. Growth and challenging myself, as I believe with others, is extremely important to creating a meaningful life. To have the confidence in yourself to simply experience new things is hard. But trusting yourself and your decisions will catapult you into beautiful things. We should never be afraid to "do the hard thing", and show up as our most authentic selves while doing it.

From a security or compliance perspective, what advice would you give to a potential client or SaaS business?
Security and compliance are not just checkboxes — they're the foundation of trust in any SaaS business. My biggest piece of advice is to prioritize security from day one. Don't wait for an audit or a client request to start thinking about compliance; build a proactive security culture that evolves with your business and ensure you have the right MSSP support in place.
Regular risk assessments, employee security training, and a strong incident response plan can make all the difference. At Rhymetec, we help SaaS companies navigate complex frameworks like SOC 2, ISO 27001, and PCI, ensuring they stay secure, compliant, and ahead of emerging threats. Our passion for supporting compliance and cybersecurity comes from a deep place of understanding SaaS business models and how to stay congruent with emerging trends within cybersecurity & compliance.
Connect with Kelsey Hannemann
Businesses often rely on a network of vendors to support their operations, yet many don’t realize this reliance comes with significant cybersecurity risks. Because of this, strengthening vendor risk management isn't just a necessity; it's a critical component of maintaining customer trust and safeguarding sensitive information. Here's how businesses can strengthen their vendor risk management practices and stay ahead of potential threats:
Start With Due Diligence
Before onboarding a vendor, conduct a thorough evaluation of their security practices. This means more than simply reviewing their policies or taking their word for it. Begin by requesting detailed information about their cybersecurity measures, including network security, data protection protocols, and any certifications or attestation reports they hold (e.g., ISO 27001 or SOC 2 compliance).
Next, conduct interviews with their team, ask for case studies and request references from other clients. A vendor's security posture should be robust and transparent, and any hesitance or vagueness in providing this information should be considered a red flag.
Implement Ongoing Monitoring And Review Processes
Onboarding a vendor with strong security practices is just the beginning. Cybersecurity isn’t static, and your approach to vendor management shouldn't be either. Define a process for ongoing monitoring of your vendors' security postures. This could involve quarterly reviews, where you reassess vendors' network security, business continuity plans, and any incidents of data breaches.
Regular reviews help verify that vendors maintain the standards agreed upon at the start of your partnership. After all, a vendor's security measures might lapse or become outdated over time, posing a risk to your business. You can identify and address potential issues by staying proactive and conducting regular assessments before they escalate.
Strengthen Communication And Transparency
Transparency is key in vendor relationships, especially when it comes to cybersecurity. Establish clear communication channels and expectations from the start. Your vendors should be aware that you expect to be informed of any security incidents or changes in their operations that could impact their ability to safeguard your data.
You may also want to consider asking your vendors if they have a trust center or public page that outlines their controls and practices, reporting on their security status in real time. This kind of transparency builds trust and allows you to address potential risks swiftly.
Leverage Technology For Continuous Monitoring
As the number of vendors you work with increases, so does the complexity of managing them. To stay ahead, you can invest in technology solutions that help automate the monitoring process. Tools that continuously track vendor performance, security updates, and compliance status can provide real-time insights, enabling you to act quickly if a risk is identified.
These tools can also help you maintain an up-to-date inventory of your vendors, track the flow of data between your company and its vendors, and identify any potential vulnerabilities. In the cybersecurity landscape, where threats evolve rapidly, leveraging technology can provide a significant advantage in staying ahead of potential risks.
Tailor Your Approach Based On Vendor Risk Levels
Not all vendors pose the same level of risk to your organization, so a one-size-fits-all approach to vendor management can be inefficient and ineffective. Instead, classify your vendors based on their access to your sensitive data and the potential impact on your business if their security were to be compromised.
More stringent monitoring and controls should be in place for high-risk vendors, such as those with access to critical systems or sensitive customer information. This might include more frequent reviews, higher standards for cybersecurity measures, and more detailed contractual obligations. A less intensive approach may be sufficient for lower-risk vendors, but they should still be subject to regular reviews to ensure they meet your security expectations.
Cultivate A Culture Of Security Within Your Organization
Strengthening vendor risk management starts with a culture of security within your own organization. Your team should understand the importance of cybersecurity and be trained to identify potential risks when interacting with vendors. Encourage your employees to follow best practices, like verifying the legitimacy of vendor claims and reporting any suspicious behavior.
Develop A Vendor Incident Response Plan
Incidents can still occur no matter how robust your vendor management process is. As such, it’s crucial to have a vendor incident response plan outlining the steps your company will take if a vendor's security is compromised. This plan should include clear communication protocols, roles and responsibilities, and a process for mitigating the impact of a security breach.
By planning for the worst, you can respond quickly and effectively to minimize the damage to your business and your clients. A well-prepared incident response plan can also help to reassure your clients that you are committed to protecting their data, even in the face of unexpected challenges.
In Closing
Strengthening vendor risk management is not a one-time task, but an ongoing commitment. By implementing comprehensive due diligence, ongoing monitoring, clear communication, and leveraging technology, businesses can significantly reduce their exposure to cybersecurity risks. Prioritizing cybersecurity and ethics in vendor management protects your business and builds the trust essential for long-term success in the digital era.
You can read the original article posted in Fast Company by Rhymetec CEO, Justin Rende.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.