Deepak Chopra once said, "All great changes are preceded by chaos." This has never been more accurate than when it’s applied to the current AI and cybersecurity environments—and the regulations that govern them.
New frameworks like the Digital Operational Resilience Act (DORA), the EU AI Act, the Network and Information Systems Directive 2 (NIS2) and the Cybersecurity Maturity Model Certification (CMMC) are reshaping how businesses handle security, risk and compliance. These regulations aren't just about ticking boxes—they carry major financial penalties and demand real operational changes.
For companies in financial services, AI development, critical infrastructure or defense, staying ahead of the changes is vital to avoid penalties, protect data and maintain trust. Let's look at what each entails.
DORA: Protecting Financial Institutions From Cyber Disruptions
Financial institutions face constant cyber threats and operational risks. DORA aims to empower financial organizations to weather system disruptions and continue operating smoothly.
DORA requires penetration testing, vulnerability assessments and disaster recovery planning. It focuses on business continuity to ensure that if a system fails, a plan is in place to keep operations running. Banks, insurance companies and investment firms must validate security controls through rigorous testing.
This regulation is a wake-up call for financial institutions to take cybersecurity resilience seriously. The penalties for non-compliance are severe, making it crucial for businesses to invest in robust security testing and operational risk management.
The EU AI Act: Setting The Global Standard For AI Compliance
AI development currently operates in a regulatory gray area, but the EU AI Act is changing that. One of the first laws to set clear boundaries on AI usage, it focuses on ethical risks, security concerns and prohibited applications.
The most important takeaway is the significant financial penalties for non-compliance: These can be up to 7% of a company's global annual revenue or 35 million euros, whichever is higher. That's more than GDPR, which has already forced businesses worldwide to rethink their approach to data privacy.
This law explicitly bans certain AI applications, particularly those that exploit vulnerabilities. The ban includes AI-powered cyberattacks, social manipulation and unethical facial recognition practices. Article 5 of the act outlines prohibited AI uses, such as systems that exploit people's age, disabilities or socioeconomic circumstances.
This isn't simply a privacy factor; its purpose is to prevent AI from being weaponized.
A common misconception is that this law only affects European companies. That's not the case. Any company developing, deploying or processing AI systems in the EU—or serving EU customers—must comply. For example, if a U.S. company hosts its platform in an EU data center or processes European customer data, this regulation applies.
The EU AI Act is setting the stage for global AI governance. Similar regulations are expected to emerge worldwide, making it smart for businesses to adapt now rather than scrambling to comply later.
NIS2: Strengthening Cybersecurity For Critical Infrastructure
Also in the EU, the NIS2 Directive expands cybersecurity requirements for critical industries like energy, healthcare, transportation and digital services. It builds on the original NIS Directive but goes much further, applying to more organizations, increasing security expectations and enforcing stricter penalties.
The enhanced reporting requirements are one of the biggest challenges. Companies must notify regulators of cyber incidents within 24 hours, provide a complete assessment within 72 hours and demonstrate they are actively managing security risks.
The directive also emphasizes stronger supply chain security, holding companies responsible for ensuring their vendors meet cybersecurity standards. This means businesses can't just secure their own systems—they must also vet suppliers and partners to prevent weak links in the supply chain.
Beyond reporting and supply chain oversight, NIS2 enforces stricter governance requirements. Organizations must appoint security officers, conduct regular risk assessments and develop robust cybersecurity policies. Those that fail to comply face heavy financial penalties and increased regulatory scrutiny.
Compliance isn't optional for companies operating in or serving the EU market. NIS2 is setting a new cybersecurity standard, and businesses that don't act risk fines, operational disruptions and reputational damage.
CMMC: Raising the Bar For U.S. Defense Contractors
The CMMC is a requirement for companies working with the U.S. Department of Defense (DoD). It builds on cybersecurity frameworks like NIST 800-171, ensuring that defense contractors follow strict security protocols to protect sensitive government data.
Recent changes to CMMC include a new self-assessment option for Level 1 compliance, making it easier for smaller contractors to meet requirements without hiring third-party auditors. However, higher certification levels still require independent verification, adding layers of accountability.
With the new compliance requirements going into effect in mid-2025, businesses need to act now. The DoD has made it clear that CMMC certification will be mandatory for contracts, and companies that don't comply risk losing business.
Evolving Security Frameworks: A Smarter Approach To Compliance
For organizations handling sensitive data in healthcare, finance and other regulated industries, new security frameworks present a way to prove compliance with strict privacy and cybersecurity standards. In the past, certification required a lengthy, one-size-fits-all assessment, but newer models offer more flexible options with fewer controls, reducing complexity while maintaining security.
Many businesses don't realize that certification levels vary, and choosing a lower-tier option may not meet regulatory or customer expectations. This is especially important for HIPAA compliance, where recognized certifications can demonstrate that companies meet security standards. As cybersecurity laws evolve, understanding these frameworks ensures that businesses stay compliant, competitive and prepared for future regulations.
Laws like DORA, the EU AI Act and NIS2 are designed to keep technology from becoming a threat. AI development currently lacks clear rules—without oversight, it can be used in dangerous ways. These regulations force businesses to prioritize security and ethics upfront, preventing bigger problems down the road.
To stay ahead, organizations must:
- Identify relevant regulations and update security policies.
- Invest in risk assessments, penetration testing and employee training.
- Stay informed—more regulations are coming.
Compliance isn't just about avoiding penalties but about building a safer, more resilient digital future. Companies that act now will lead, while those that wait will fall behind.
You can read the original article posted in Forbes by Rhymetec CISO, Metin Kortak.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
The advent of the Digital Operational Resilience Act (DORA) has introduced a new set of regulatory expectations that financial entities operating in the European Union need to be aware of. Additionally, organizations such as SaaS startups that provide services to financial entities, or plan to, must begin preparing to meet DORA's requirements.
In a recent webinar hosted by Rhymetec and Vanta, we unpacked DORA requirements and discussed practical steps organizations can take now to align with DORA. Endri Domi, Infosec Manager at Rhymetec, moderated an insightful discussion between Faisal Khan, GRC Solutions Specialist at Vanta, and Metin Kortak, CISO at Rhymetec.
This blog post highlights the key points from their discussion, with a focus on what organizations need to understand and prioritize in the months ahead. You can check out the full webinar here.

What Are DORA Requirements, and Who Must Comply?
DORA requirements come from the EU's Digital Operational Resilience Act, which is now in effect. The regulation applies to financial institutions operating in the EU, as well as certain types of service providers that support them.
According to Faisal Khan, GRC Solutions Specialist at Vanta, the purpose of DORA is to improve the resiliency of financial institutions:
"DORA is an EU regulation designed to improve the ability of financial institutions to weather and recover from any information or technology-related disruptions like cyber attacks, data breaches, and system failures. It's really to build that tolerance for themselves so that they're protected in the event some of those things would happen." - Faisal Khan, Vanta
DORA covers both financial entities, such as banks, insurance companies, and investment firms, as well as their ICT third-party service providers. ICT (Information and Communication Technology) third-party service providers include cloud providers and other vendors that manage or support technology for other organizations.
The regulation introduces two types of regulatory documents that support its implementation:
Regulatory Technical Standards (RTS) and Implementing Technical Standards (ITS). RTS specifies what organizations must actually do to meet DORA's requirements, while ITS focuses on how the information should be reported. How each of the 5 pillars of DORA is applied in practice, as shown in the next section, is shaped by the technical standards.
What Are The Five Pillars of DORA Requirements?
DORA requirements are structured around five pillars. Each pillar is designed to reduce ICT-related disruption risk in financial services and strengthen the resilience of the ecosystem. In our webinar, our experts honed in on explaining each pillar in detail, particularly those involving third-party risk and incident reporting:
1. ICT Risk Management
Mitigating ICT-related risks across your organization's digital environment is a core part of DORA. Typically, this entails starting with a live, centralized asset inventory and linking each asset to a business function. This enables you to then align risk prioritization with actual operational impact, and helps keep future reporting manageable.
2. ICT-Related Incident Reporting
As highlighted by our experts, ICT-related incident reporting includes notifying both national competent authorities and any stakeholders who may be affected, such as customers or partners who rely on your platform:
"If you do have ICT-related incidents, those incidents will need to be communicated to the national authorities and other stakeholders who may be impacted by your platform, such as your customers." - Metin Kortak, Rhymetec
If an incident meets the criteria for "major ICT-related incident", you must notify your national competent authority (typically, your financial services or cybersecurity regulator) within 24 hours of detection. Follow-up reports are required as the situation evolves.
Incidents are classified based on metrics such as the number of users affected, duration of the disruption, and impact on data integrity or confidentiality. Your report should explain in detail what your response is and provide guidance for the recipient. The final report submitted to regulators must include a root cause analysis, detailing what happened and why it happened.
Bonus Tip: DORA goes further than GDPR by imposing stricter timelines, requiring a reporting process with multiple updates, and mandating the notification of any major ICT–related incidents (not just those involving personal data). In general, it covers a broader range of disruptions that impact operational continuity.

3. Digital Operational Resilience Testing
Under DORA requirements, operational resilience testing is addressed in Articles 24-27. Organizations must be able to demonstrate that their critical ICT systems can withstand disruption. Testing must be continuous and evidence-based:
"The point of this requirement is to ensure you have testing to verify that the resiliency of your application can be proved. This can be either third-party testing, or it can be internal testing." - Metin Kortak, Rhymetec
This includes a mix of internal exercises (such as tabletop exercises) and, where applicable, advanced testing techniques like threat-led penetration testing (TLPT). The intent is to ensure that your organization is able to 1) recover from disruption and 2) continue delivering critical services under adverse conditions.
For most organizations, the following action items are good options to fulfill the requirements in this pillar:
Tabletop Exercises
Tabletop exercises are scenario-based discussions that mirror real-world scenarios. Undergoing a tabletop exercise allows your organization to test its response capabilities, validate roles and responsibilities, and improve communication without affecting live systems.
Technical Testing
For systems deemed critical, DORA encourages more rigorous validation, which can take the form of failover testing, load testing, and red team exercises. Third-party involvement is encouraged at this stage, particularly for high-risk or business-critical functions.
Testing must occur on a regular basis and must reflect the scale and risk profile of your organization. DORA does not prescribe a one-size-fits-all cadence, but regulators will expect to see a documented rationale for test frequency and scope.
Remediation and Continuous Improvement
Testing is only the first part of the requirement. DORA also expects organizations to conduct lessons learned from testing, remediate weaknesses accordingly, and feed results back into their risk management and ICT governance processes.
The overarching goal of this requirement is to encourage a shift from static, checklist-driven compliance to real-world resilience. Instead of simply having a plan, organizations have to prove it works.
Bonus Tip: Don't forget about your critical third parties! We'll get into that more in the next pillar, but it's also relevant here. In areas where external service providers support your organization's critical functions, you'll need to evaluate their resilience as well. To do this, you can obtain assurance reports, risk assessments, validate their compliance with DORA if applicable, and/or coordinate joint exercises.

4. ICT Third-Party Risk
"If you do not understand your subprocessors, that's probably the first thing you want to do. If you have to comply with GDPR, you probably already understand the subprocessors that you're working with. For DORA, the next step would be to really understand how much data they process and how critical they are to your organization." - Metin Kortak, Rhymetec
One of the foundational steps in meeting DORA requirements is gaining full visibility into your third-party relationships. While organizations that already comply with GDPR are required to maintain records of data subprocessors, DORA introduces an operational resilience component that extends beyond data protection. Under DORA, your organization has to consider not only who you're working with, but how much risk those relationships introduce into your business.
Subprocessors often include cloud providers, SaaS tools, and outsourced IT or security vendors. DORA requires that financial entities mandate ICT third-party service providers that service those entities to map out these relationships and assess their criticality. Article 28 of DORA explicitly mandates risk assessments of ICT third-party service providers, with an emphasis on concentration risk.
"DORA also impacts the other third-party vendors and subprocessors that you are working with, because those vendors ultimately impact also the availability of your platform. For example, if you are hosted by a third-party hosting provider, they also impact the availability of your application. Therefore, you also need to conduct a risk assessment to ensure that the provider can actually support the resiliency of your application." - Metin Kortak, Rhymetec
If you are a financial entity subject to DORA requirements, you must maintain a register of all contractual agreements with ICT third-party providers and identify those considered "critical or important". This represents a broader industry shift from reactive vendor management to proactive operational resilience planning. Organizations that enact these changes will not only be positioned to comply with DORA, but also to build a more resilient overall business.
Other important considerations for the ICT-Third Party Risk Pillar include:
The Volume of Data Processed
How much sensitive or operational data flows through the vendor's systems? The more data processed, the higher the impact of a service disruption or breach.
Criticality to Business Operations
If a subprocessor experiences downtime, how does that affect your ability to deliver services, meet SLAs, and maintain operational continuity?
Dependency Risk
Are there alternative providers or workarounds if a subprocessor fails? If not, that relationship may require additional safeguards in your contract or contingency planning.

Oversight and Exit Strategy
Ongoing monitoring and having the ability to disengage from a vendor if needed (without causing your organization to risk operational issues!) are essential under DORA.
5. Information Sharing
DORA encourages financial entities to participate in trusted information-sharing arrangements around cyber threat intelligence. While not mandatory, participation supports sector-wide resilience.
Bonus Tip: Join regional or sector-specific ISACs (Information Sharing and Analysis Centers) early. This gives your team early visibility into threats targeting similar organizations, often before they've hit public feeds or the news.
What Are Some Considerations When Becoming DORA Compliant, According to The Experts?
As you are working to achieve compliance with DORA requirements, here are several practical considerations to keep in mind, according to our experts at Rhymetec and Vanta:
Trade Reporting Integrity
If your organization is subject to transaction reporting requirements (such as under EMIR or MiFIR), DORA reinforces the need for accuracy and completeness of those reports. Insufficient reporting could raise compliance concerns.
Lack of An Official DORA Certification
This is a common misconception.
Unlike some regulatory frameworks, DORA does not offer a formal certification or audit program. Instead of a formal certification, organizations are expected to demonstrate compliance with DORA requirements through internal audits or third-party assessments.
However, it's important to note that regulators still have the authority to request evidence and conduct inspections, so being "audit-ready" is still critical.
Framework Synergies
DORA is good at outlining what must be done, but often leaves the how to up to each organization and lacks specific implementation guidance. This opens the door to leverage existing security and compliance frameworks, such as ISO/IEC 27001 and 27002, SOC 2, or NIST, to guide implementation.

For example, DORA requires regular risk assessments but doesn't prescribe a methodology. Therefore, ISO 27005 or NIST SP 800-30 can provide details on how to actually carry out risk assessments. Aligning DORA controls with these frameworks, if you already have them, helps avoid duplicating your efforts.
In Conclusion: How Organizations Leverage vCISO Services To Meet DORA Requirements
A virtual CISO (vCISO) can play a critical role in preparing your organization to meet DORA requirements. vCISOs provide technical guidance and control implementation, operational support, and oversight without the cost of a full-time executive hire.
For startups, a vCISO can help build foundational controls, align existing security processes to DORA's requirements, and lead efforts like risk assessments, incident response planning, and third-party due diligence. For more mature organizations, a vCISO can support internal audit functions, map DORA requirements to existing frameworks (such as ISO 27001 or SOC 2), and create alignment between IT, legal, and compliance teams.
Regardless of organization size, a vCISO helps translate complex regulatory language into actionable plans that will hold up under regulatory scrutiny. vCISO services provide access at scale to top-tier cybersecurity and compliance services. vCISOs can also leverage the most cutting-edge tools, such as compliance automation platforms, to get you compliant in the fastest timeframe possible.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.
- DORA Compliance Checklist: What The EU's Digital Operational Resilience Act Means For Your Business
- Meeting EU AI Act Compliance: Core Requirements and Business Benefits
- Penetration Testing FAQ: What You Need To Know | Rhymetec
This Rhymetec DORA Compliance Checklist will help you understand DORA requirements, how to determine if your business falls under DORA's umbrella, the specific measures you'll need to implement, ways to leverage compliance for business growth, and a roadmap to get started.
The European Union's Digital Operational Resilience Act (DORA), which took effect in January 2025, aims to protect financial institutions from risks their dependencies on technology providers may pose to them.
The Act doesn't just cover the financial institutions. If you provide services to EU financial institutions, even if you are a small software company, DORA may apply to you. Many technology providers are classified as "critical ICT third-party service providers" (CTPs) under DORA, and need to adhere to the requirements.

Financial institutions today rely heavily on a variety of services from tech companies.
For example, your average regional bank nowadays may rely on 1) a cloud storage provider for customer data, 2) a payment processing API for transactions, and 3) a third-party authentication service for security, just to name a few.
A disruption in the services of any one of these could threaten the bank's ability to operate. Given how reliant financial institutions have become on these types of services, stricter regulatory oversight is long overdue in this sector. DORA aims to fill this need.
Who Needs To Comply With DORA Requirements?
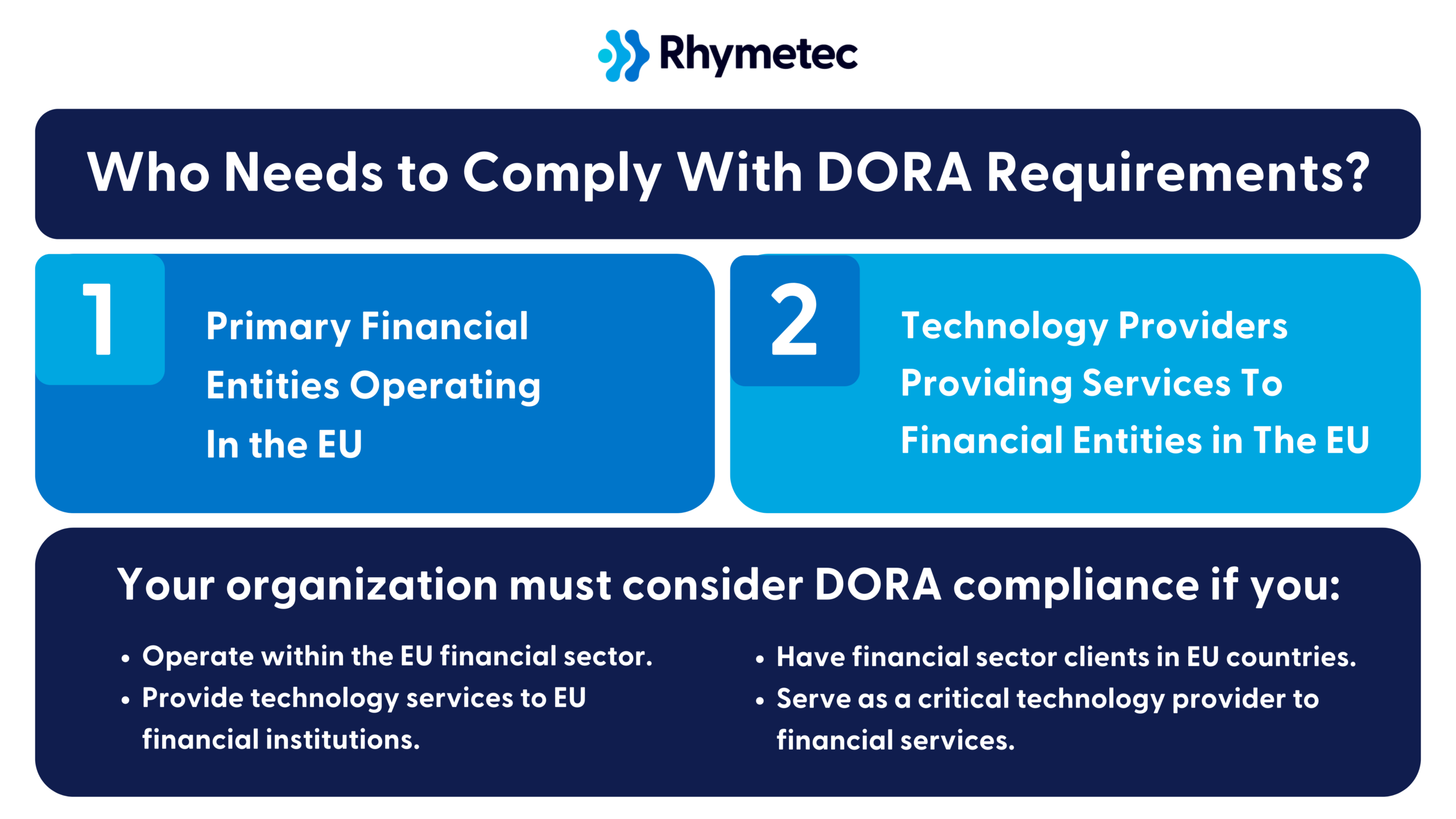
DORA's compliance requirements directly apply to the following categories of organizations:
1. Primary Financial Entities Operating In the EU:
- Banks and credit institutions
- Investment firms
- Insurance and reinsurance companies
- Payment and electronic money institutions
- Cryptocurrency exchanges and providers
- Crowdfunding service providers
2. Technology Providers Providing Services To Financial Entities in The EU:
- Cloud computing services that support financial institutions
- Datacenter providers
- Network information and communication technology services
- Software and hardware providers critical to financial services
- …and more.
Your organization must consider DORA compliance if you:
- Operate within the EU financial sector.
- Provide technology services to EU financial institutions.
- Have financial sector clients in EU countries.
- Serve as a critical technology provider to financial services.
If you are unsure if your organization needs to comply with DORA, or if you need help getting started, Rhymetec's DORA Compliance Services can assist you. Our experts are happy to answer any questions you may have - we've helped over 700 organizations fast-forward their security and compliance.
DORA Compliance Checklist: Core Requirements
Let's break down what DORA actually demands from your organization.
You'll need to oversee the implementation of four pillars, each of which carries specific obligations that will impact your operations differently depending on your organization's role in the financial ecosystem:
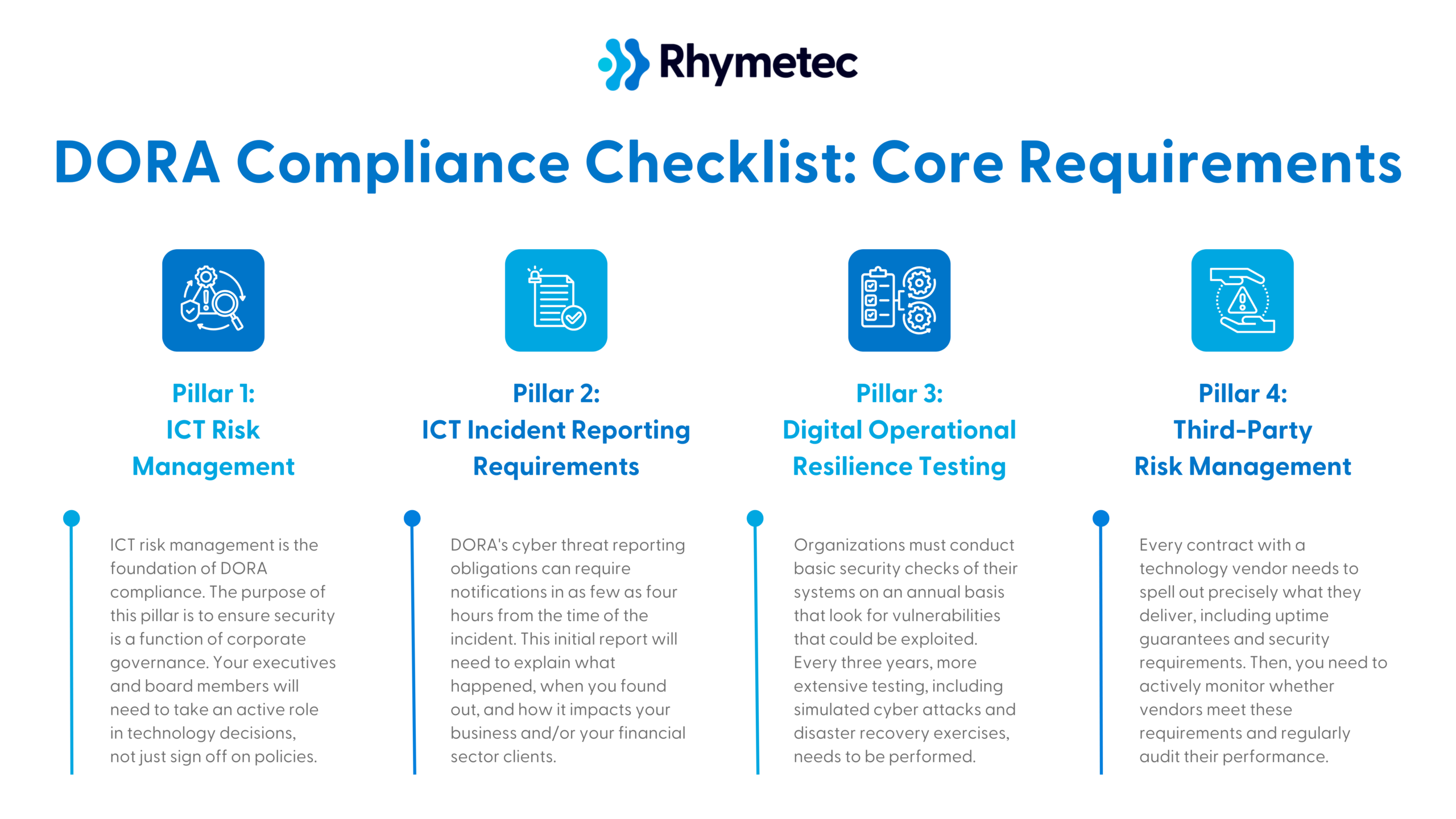
DORA Compliance Checklist Pillar 1: ICT Risk Management
Information and Communication Technology (ICT) risk management is the foundation of DORA compliance.
The purpose of this pillar is to ensure security is a function of corporate governance. Your executives and board members will need to take an active role in technology decisions, not just sign off on policies.
The following action items are requirements under this pillar:
Establish a governance framework for ICT risk management:
- Define who within your organization is responsible for ICT risk management at the executive level, and set policies to formalize accountability and integrate ICT risk into overall risk management.
- For example, you might appoint a security officer responsible for reporting ICT risks to the board.
Create policies and procedures for ICT risk identification.
- These policies should outline how you will identify threats, protect systems, detect incidents, respond to attacks, and recover.
- Tip: Align these policies with other industry standards like ISO 27001 or NIST. If you already have one of these frameworks, this can make things a lot easier!
Conduct regular risk assessments for ICT-related threats.
- DORA requires that you regularly evaluate risks to your digital systems and data. This includes assessing vulnerabilities, potential attack vectors, and business impact.
- Example: A financial services firm might decide to run quarterly assessments to identify weaknesses in its cloud storage security to meet this requirement.
Implement security measures (if you do not already have them in place).
- Security measures under DORA requirements include encryption, multi-factor authentication, and network segmentation. For a full list of these measures, reference the official DORA text.
- A backup and recovery plan for ICT disruptions is also required, as is monitoring ICT systems for anomalies and potential threats. This often takes the form of using monitoring tools and log analysis.
Lastly, employee training on security measures and ICT risk is required.
- Your staff must receive training in areas such as phishing, password security, and handling sensitive data.
DORA Compliance Checklist Pillar 2: ICT Incident Reporting Requirements
If you experience a system outage, data breach, or security incident, DORA sets strict rules about reporting the incident. DORA's cyber threat reporting obligations, for example, can require notifications in as few as four hours from the time of the incident. This initial report will need to explain what happened, when you found out, and how it impacts your business and/or your financial sector clients.
Requirements in this step include:
Develop an internal reporting mechanism for incidents, and figure out how you will identify and classify ICT-related incidents.
- ICT incidents under DORA are classified based on severity, and your response should be designed to match the severity of the incident. For example, a trading platform might classify a Distributed Denial-of-Service (DDoS) Attack as a high-severity incident requiring an immediate response.
- Establish policies for reporting major ICT-related incidents to the appropriate authorities within the required timeframe. Regulatory bodies need to be notified in the case of significant disruptions or cyberattacks.
Document and analyze incidents to improve processes and prevent recurrence.
- Every incident has to be logged, reviewed, and analyzed to improve security measures.
- After an incident, you should have policies in place to dictate how you will communicate incident impacts and remediation efforts to stakeholders.
DORA Compliance Checklist Pillar 3: Digital Operational Resilience Testing
DORA requires regularly testing your technology systems to ensure they can withstand problems and cyber attacks.
Organizations must conduct basic security checks of their systems on an annual basis that look for vulnerabilities that could be exploited. Every three years, more extensive testing, including simulated cyber attacks and disaster recovery exercises, needs to be performed.
Some organizations that fall under even more stringent DORA requirements (due to how pivotal they are to the financial sector) may need to go a step further and hire external security experts to conduct a penetration test. A penetration test is a good idea for all organizations, however, as it is the gold standard way to test your defenses in real-world situations.
In general, the requirements under this pillar are:
Conduct periodic testing of ICT systems, and perform penetration testing.
- Testing your security defenses against common threats like phishing and malware is required under DORA.
- Penetration testing is the industry-standard way to test your defenses!
Based on the results of your testing, develop remediation plans.
- For example, a company may find they need to update their firewall rules and disable unused ports after a penetration tester exposes vulnerabilities in their network.
Document testing outcomes and improvement measures.
- Under DORA requirements, organizations must maintain records of all testing activities, findings, and corrective actions.
DORA Compliance Checklist Pillar 4: Third-Party Risk Management
Lastly, your responsibility under DORA requirements extends to any vendors you rely on to serve your financial sector clients.
Every contract with a technology vendor needs to spell out precisely what they deliver, including uptime guarantees and security requirements. Then, you need to actively monitor whether vendors meet these requirements and regularly audit their performance.
DORA also requires that you plan for vendor failures, and demonstrate how you would switch to a different vendor if needed. One of the goals of this pillar is to help manage vendor concentration risk - organizations shouldn't rely too heavily on any single vendor.
Requirements include:
Create an inventory of ICT third-party providers.
- You'll need to document all of your vendors that provide ICT-related services. This can include the SaaS platforms you use, for example.
- Assign each vendor a risk level.
Carry out risk assessments for third-party ICT services.
- DORA requires you to evaluate the security posture of your vendors before and during the relationship.
- For instance, require your vendors to complete a security questionnaire or share their SOC 2 report.
Establish contractual agreements that define security and resilience expectations.
- Contracts should include cybersecurity requirements, incident response obligations, and compliance expectations relevant to your industry. For example, a payment processor might require its vendors to meet PCI DSS requirements.
Monitor third-party compliance with ICT risk requirements.
- Ongoing oversight of vendors' security practices is required. For example, you could conduct annual reviews of your cloud provider's security controls.
Develop exit strategies for critical third-party dependencies.
- Businesses must plan ahead for vendor disruptions, by having alternative providers or internal solutions ready.
DORA Compliance Checklist Timelines: 6-9 Months Total On Average; 4-6 Months Total With Rhymetec
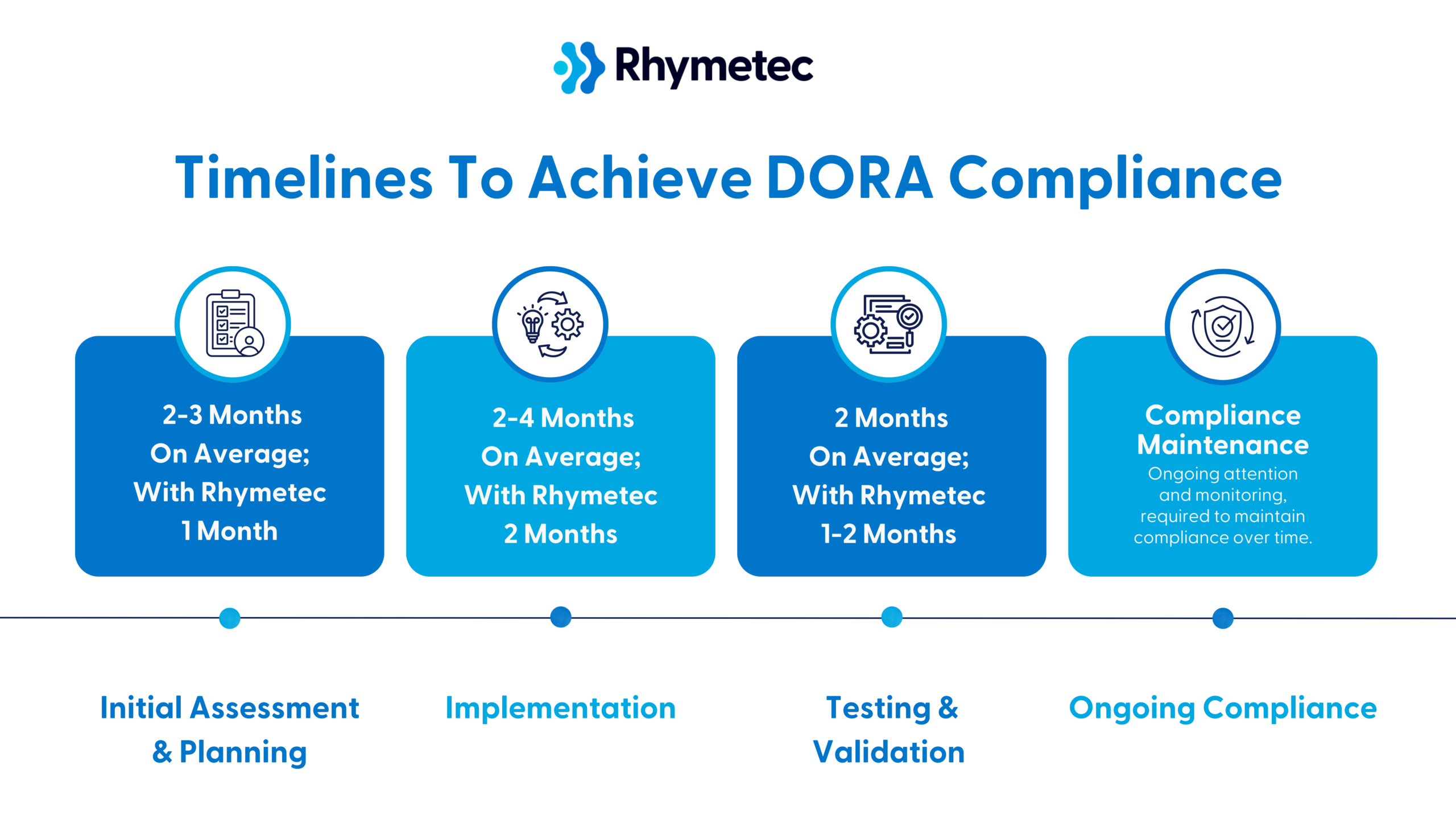
Below is a roadmap with timelines to give you an idea of what you can expect. Although these steps may vary depending on your organization's individual factors and needs, this should give you a general idea of what to plan for:
Initial Assessment and Planning (2-3 Months On Average; With Rhymetec 1 Month)
The first step is to understand where your organization stands in relation to DORA requirements. To do this:
- Bring in personnel from IT, security, legal, and business operations in order to understand the roles and impact across your entire organization. If you're a SaaS provider, include project managers who understand your technology stack and business leaders who manage financial sector relationships.
- Conduct a gap analysis, assessing where you currently are versus where you need to be to meet DORA requirements.
- Create an inventory of technology assets that support financial sector services (also known as mapping your ICT assets). You'll need to document every server, database, API, and third-party system you use.
After you have a clear understanding of your gaps, the next step is to develop a detailed implementation plan and allocate resources accordingly. Calculate costs for new tools, additional staff, training programs, and possible consulting help. Include both one-time costs (such as new monitoring systems) and ongoing expenses (such as additional security staff or regular testing).
Implementation (2-4 Months On Average; With Rhymetec 2 Months)
Now comes the actual work of building your compliance program:
- Update your documentation. Create or revise policies and procedures to meet DORA requirements, including incident response plans, business continuity procedures, and vendor management policies.
- Make your policies practical: Your incident response plan, for example, should include actual contact information and clear steps.
- Implement new controls. Deploy new security measures, as outlined by DORA requirements, and any monitoring tools or testing procedures you need.
- Update vendor management. You'll likely need to review and update contracts with critical service providers and add requirements for things like incident reporting and service levels.
Testing and Validation (2 Months On Average; With Rhymetec 1-2 Months)
Before finally achieving compliance, testing and validating your new controls is important. To do this:
- Conduct trial runs that allow you to practice your incident response procedures with realistic scenarios. The industry standard way to accomplish this is with a tabletop exercise, where your team works through a fictional but realistic scenario, such as what you would do in the event of a ransomware attack.
- Verify you can meet your recovery time objectives. Test scenarios where you'd need to switch between backup systems or alternative providers, document any gaps you find, and adjust your procedures accordingly based on what you find.
- Have legal and compliance experts review your documentation to make sure it will hold up under regulatory scrutiny.
Ongoing Compliance (Continuous)
Compliance requires ongoing attention and monitoring.
Organizations that are serious about maintaining compliance should schedule regular reviews of their compliance program, such as on a quarterly basis. This is important because changes in your business or technology impact your DORA obligations.
Monitor metrics about system performance, incident response times, and vendor service levels to spot potential issues before they impact your compliance.
Lastly, use lessons learned from any incidents that occur to continually improve your procedures, and stay informed about any changes in regulatory best practices and guidance.
Business Benefits of DORA Compliance
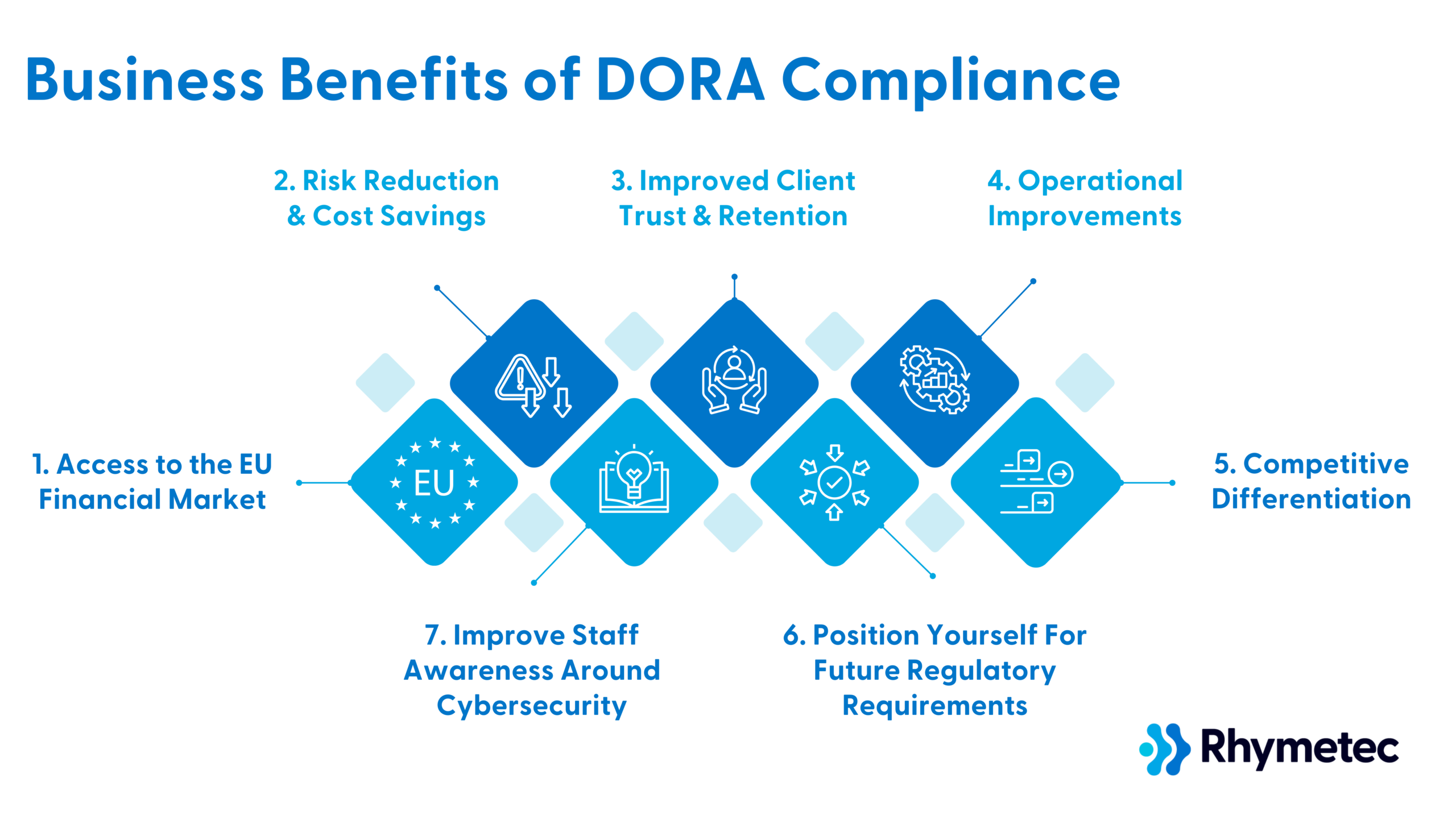
While DORA requirements may seem daunting, organizations that embrace these changes stand to gain significant competitive advantages in the European market. Complying with DORA offers substantial business advantages that extend far beyond regulatory adherence.
Here's how meeting DORA requirements strengthens your market position and creates new opportunities for your business:
1. Access to the EU Financial Market
By meeting DORA requirements, you gain the ability to serve financial institutions across the European Union.
Banks, insurance companies, and investment firms must work with DORA-compliant technology providers. Your non-compliant competitors get excluded from EU financial sector opportunities, while you can expand your market reach. This creates a clear competitive advantage.
For example, a small cloud storage provider that achieves DORA compliance can compete for contracts with major EU banks, opening up revenue streams that were previously inaccessible. Without compliance, they'd be limited to serving non-financial clients or risking their potential EU financial clients selecting compliant competitors.
2. Risk Reduction and Cost Savings
The approach to risk management under DORA is intended to help prevent costly incidents before they occur. While it may seem like a costly upfront investment to implement security controls, it costs far less than recovering from major technology failures or cyber-attacks.
For example, DORA-style monitoring enables companies to discover and fix potential system failure points before they can lead to massive revenue loss and reputational damage.
The time and money spent on monitoring and backup systems is an extremely wise investment compared to the potential losses and reputational damage a system failure could incur on many business's daily operations.
3. Improved Client Trust and Retention
Financial institutions face intense scrutiny over their technology providers. DORA compliance sends a strong signal to them that your company is committed to security and operational excellence, and will be less likely to cause them issues.
Compliance enables you to provide detailed evidence of your resilience measures, making it easier for financial clients to trust you with their operations.
It also serves to shorten sales cycles, as your team can readily demonstrate their security and reliability measures to prospective financial sector clients.
4. Operational Improvements
The rigorous testing that DORA requires can reveal opportunities to improve your operations.
Let's take a specific example to explain how:
A trading software provider implementing DORA's system mapping requirements could discover they're running redundant data validation checks across multiple different services.
By figuring this out, they can reduce their infrastructure costs while improving system performance. Without undergoing the compliance process, whether it be DORA or other regulations, issues like these may have never been discovered.
5. Competitive Differentiation
Achieving compliance with DORA sets you apart even in markets beyond the EU financial sector.
Take, for instance, a cloud database provider trying to compete for contracts with healthcare providers or government agencies. While DORA compliance isn't required for these sectors, the provider could leverage their DORA-compliant controls and processes to demonstrate their commitment to operational resilience, potentially helping win contracts over less rigorously controlled competitors.
Meeting DORA requirements provides an overall boost to your marketing and sales efforts as well. Your team can use compliance as a differentiator in marketing materials and sales meetings.
6. Position Yourself For Future Regulatory Requirements
Digital operational resilience only stands to become more important across all sectors. DORA-compliant organizations can get ahead of the curve and position themselves for future regulatory requirements.
Experts anticipate similar regulations to emerge in other regions and industries. DORA-compliant organizations may find themselves already 80% compliant with future regulations, saving significant time and resources compared to competitors who need to start from scratch.
By implementing DORA requirements now, you're preparing your business for future compliance needs while gaining all of the immediate security and operational benefits.
7. Improve Staff Awareness Around Cybersecurity
Implementing DORA requirements builds valuable expertise within your organization, at every level. Your team develops skills and know-how in risk management, incident response, and operational resilience that benefit all aspects of your business.
The value of DORA compliance lies not just in meeting regulatory requirements, but also in building a more resilient and competitive business. While the implementation process requires substantial effort and investment on your part, the resulting business benefits far outweigh the costs.
DORA Compliance Checklist: Cost Considerations
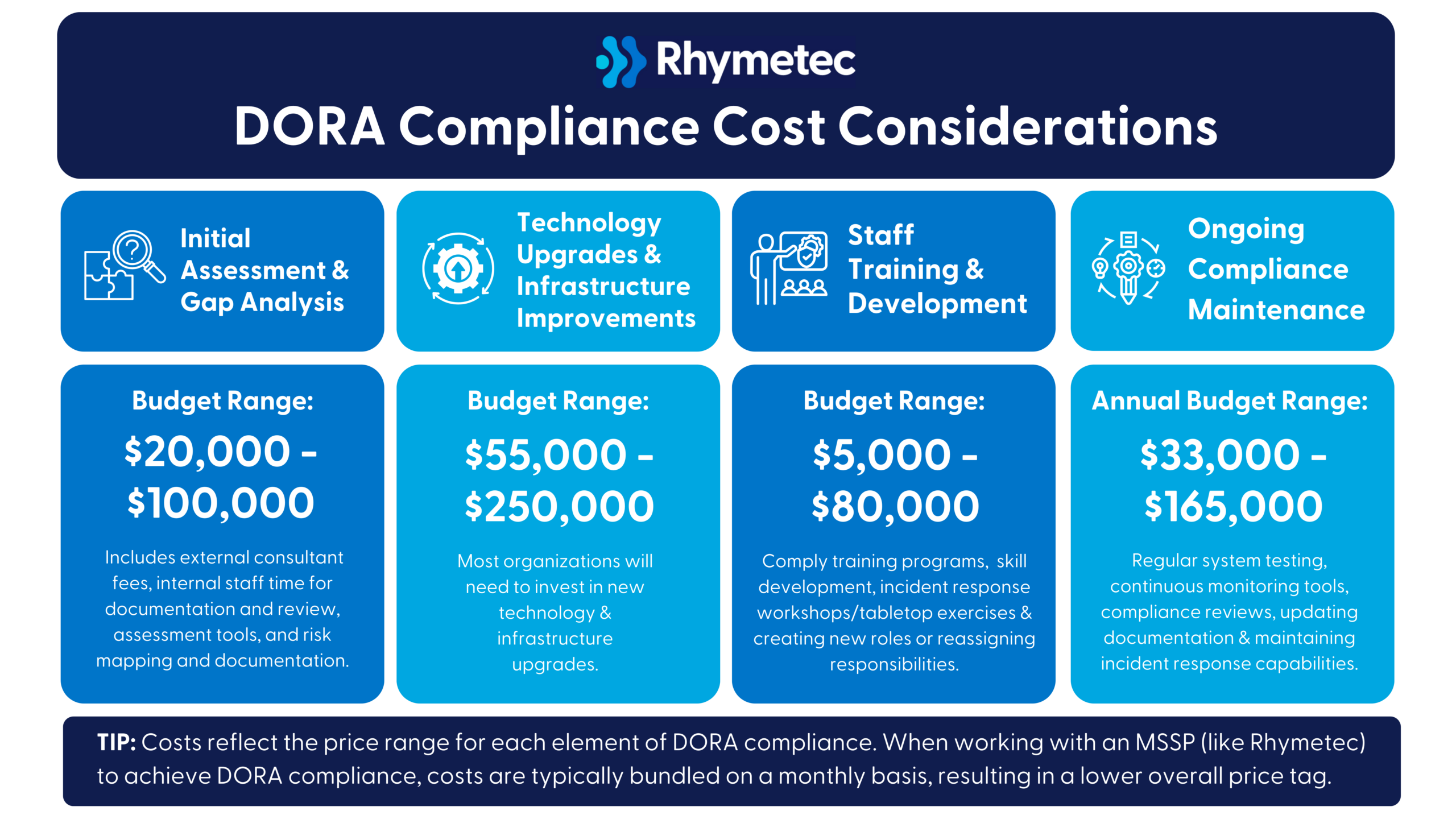
Costs to achieve DORA compliance will vary depending on your organization's size, complexity, and technology infrastructure. Here is an estimation of what you can anticipate:
Initial Assessment and Gap Analysis
Budget Range: $20,000 - $100,000
This includes external consultant fees, internal staff time for documentation and review, assessment tools, and risk mapping and documentation.
Technology Upgrades and Infrastructure Improvements
Budget Range: $55,000 - $250,000
Most organizations will need to invest in improved monitoring systems, incident response capabilities and technologies, security information and event management (SIEM) upgrades, additional backup and recovery infrastructure, and compliance tracking and reporting tools.
Staff Training and Development
Budget Range: $5,000 - $80,000
Investments include compliance training programs, cybersecurity skill development, incident response workshops/tabletop exercises, and creating new internal roles or reassigning responsibilities.
Ongoing Compliance Maintenance
Annual Budget Range: $33,000 - $165,000
Recurring annual costs include regular system testing, continuous monitoring tools, compliance reviews, updating documentation, and maintaining incident response capabilities.
Potential Hidden Costs of Fulfilling Your DORA Compliance Checklist
Potential hidden costs can include additional administrative overhead, needing to redesign existing processes, productivity loss during implementation, vendor management, and a possible temporary reduction in service delivery.
Cost Mitigation Strategies
Fortunately, there are a few things you can do it mitigate the impact of the cost associated with achieving DORA compliance:
- Start early to spread out implementation costs.
- Use a phased implementation approach and spread costs over multiple budget cycles.
- Use a compliance automation tool.
- Leverage a vCISO service to take the work off your plate entirely while receiving the highest level of service and expertise (to see costs associated with this option, check out our vCISO pricing blog).
DORA compliance is an investment in your organization's resilience and future competitiveness. While the upfront costs may seem hefty, they pale in comparison to potential losses from a major technology failure, cybersecurity incident, or regulatory non-compliance risks.
Practical Implementation Tips
Fortunately, you don't have to build everything from scratch to implement DORA requirements.
A compliance automation platform can significantly streamline the process by essentially enabling you to compile and document everything you already have. These tools enable you to automatically track your compliance progress, generate documentation, and alert you to potential gaps.
(For more information on exactly how the compliance automation process works, check out our blog post on this topic.)
Working with a virtual Chief Information Security Officer (vCISO) can also dramatically simplify your DORA compliance journey. A vCISO brings a wealth of experience in regulatory compliance and helps you avoid common pitfalls while accelerating your implementation timeline, all at a fraction of the cost of a full-time CISO.
By combining compliance automation tools with vCISO support, you can keep costs under control while meeting your DORA requirements in the fastest timeframe possible.
Additional Resources: Official EU Documentation
- Official Text of DORA - The full regulation text and requirements. This is the ultimate source of authority for any questions on specific requirements and should be referenced when there are questions about the interpretation of requirements or obligations.
- European Banking Authority (EBA) Guidelines - Technical standards and implementation guidance, as well as the latest updates on DORA implementation. The EBA's Q&A tool is an incredibly useful resource and can be used to answer common implementation questions.
- European Securities and Markets Authority (ESMA) - ESMA is one of the regulators responsible for overseeing DORA compliance. They provide updates and interpretations of DORA requirements.
In Conclusion: Get Started Today On Fulfilling Your DORA Compliance Checklist
DORA represents an opportunity to gain access to a lucrative segment of the EU marketplace, improve client trust, and strengthen your organization's operational resilience.
The most efficient way to begin your compliance journey is by engaging a virtual CISO (vCISO) who can conduct a gap assessment for you, leverage a compliance automation platform on your behalf, and guide your implementation while keeping costs manageable.
Our team at Rhymetec is happy to answer any questions you may have, and to walk you through how to tailor this DORA compliance checklist to your organization. Contact us today for more information.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with over 700 companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog: