Meet JT!
My name is JT Carney, and I grew up on Long Island, NY, for the majority of my life, before heading to Penn State University for undergrad. Sports have always been a big part of my life, and I like to stay active outdoors whenever I can. Since my NY Jets always disappoint, one of the highlights throughout college was getting to watch Saquon Barkley play for PSU Football.
After graduating, COVID brought everyone back home for a bit, so I spent a year on Long Island before moving into Manhattan, where I’ve been living for the past four years.

Tell us a surprising fact about yourself…
I’ve traveled to over 22 countries and counting.
If you could have any superpower, what would it be?
Teleportation - I would love the ability to instantly connect with clients and prospects face-to-face anywhere in the world without having to travel.
What are some things you enjoy doing outside of work?
Working out, golfing, fantasy football, and most importantly, traveling around the world and trying new restaurants!
Tell us about your role at Rhymetec…
I’m an Account Executive, coming up on my 1-year Rhymetec anniversary this October. I support our go-to-market efforts by closing deals, building strong partner relationships, and driving growth into new markets.
Why did you pursue a career in the cybersecurity industry?
I previously worked at DTCC (Depository Trust & Clearing Corporation) in financial services, but shifted into the cybersecurity industry due to conversations with friends and family who work in the industry. During COVID, the need for cybersecurity increased significantly after most organizations shifted to WFH and cyber attacks became much more common.
I knew it was an industry that would exponentially grow and wanted to be part of an industry leading organization to protect against such attacks. My shift in career mostly stemmed from my passion for sales and wanting to generate revenue for an organization and be a part of something bigger.

What is your favorite part about working at Rhymetec, or in the cybersecurity industry?
My favorite part is the culture at Rhymetec and how fast cybersecurity is always evolving. I love working with a team that’s constantly growing, collaborating, and pushing each other to stay ahead of the curve. No two days are the same, and you’re always discovering new risks, technologies, and customer challenges.
What is your favorite quote or the best advice you have ever received?
“Seek first to understand, then to be understood.”
From a security or compliance perspective, what advice would you give to a potential client or SaaS business?
Businesses should start viewing compliance as an ongoing program, not a one-time project. It’s not just about passing an audit; it’s about building habits and processes that actually make your business more secure and easier to scale.

If you treat it like a box-checking exercise, you’ll always feel like you’re scrambling. By embedding security and compliance into day-to-day operations, you reduce risk, build customer trust, and avoid the fire drills that come when compliance is treated as a last-minute hurdle.
Connect with JT Carney
If your business works with or plans to work with the U.S. Department of Defense or its contractors, CMMC Level 3 may be a contractual requirement for your organization. Level 3 is the highest level of CMMC, and introduces a higher bar to show that your security program can adequately protect Controlled Unclassified Information (CUI).
At Rhymetec, our vCISOs guide companies through compliance readiness every day. We’ve created this CMMC Level 3 Checklist to help you understand the CMMC Level 3 requirements, identify gaps in your current security program, and how to prioritize remediation efforts prior to engaging a C3PAO for certification and pursuing your official government-led assessment.
With the right planning, CMMC Level 3 can be achieved without derailing business growth or overloading your internal teams. If you are unsure of which level of CMMC you need, check out our CMMC Compliance Checklist for Level 2 and our CMMC Level 1 Checklist, or contact our team today for direct, tailored guidance for your organization.
CMMC Level 3 Compliance Checklist: What Are The Steps?
**The CMMC Level 3 Assessment Guide (v2.13) is released by the DoD’s CIO office and provides specific requirements and processes for assessment. Level 3 applies to a narrow subset of contractors working on high-sensitivity DoD programs involving advanced or unique CUI. Organizations should use our checklist as a reference, but also be sure to review the official rule and guide directly while preparing for assessments by DCMA DIBCAC.
CMMC Level 3, also known as the “Expert” level, applies to organizations supporting DoD programs involving highly sensitive or mission-critical CUI. It combines the full NIST 800-171 control set with even more safeguards, pulled from NIST SP 800-172.
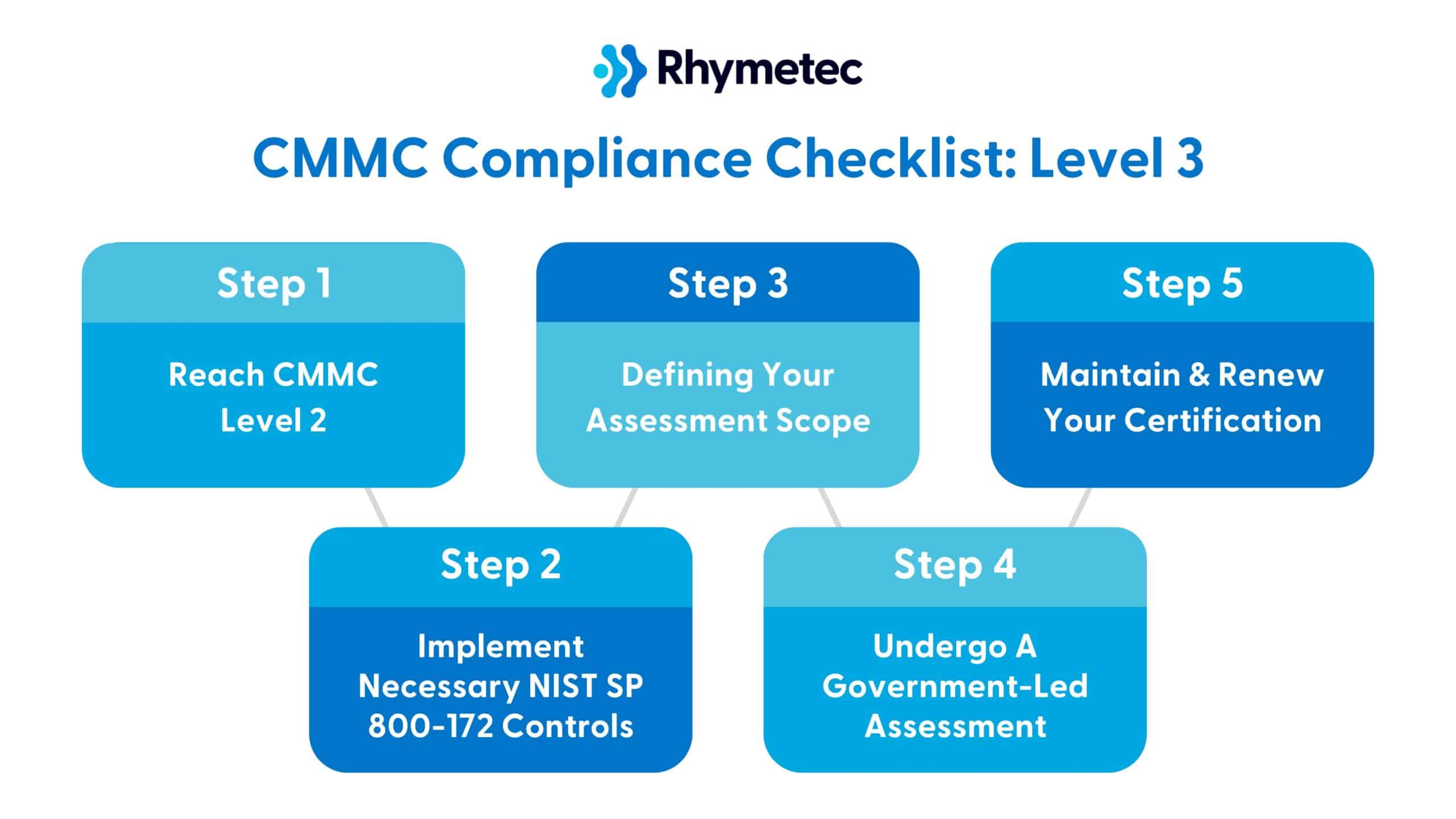
Step 1: Reach CMMC Level 2
Your organization must complete a successful Level 2 CMMC assessment by a C3PAO before beginning Level 3. This ensures all 110 NIST SP 800-171 controls are implemented. Once you have fulfilled the requirements for your CMMC Level 2 checklist, you just need to fill in the remaining requirements for Level 3:
Step 2: Implement Necessary NIST SP 800-172 Controls
The next step is to implement selected NIST SP 800-172 controls. The DoD requires adding 24 additional controls from NIST SP 800-172, which are designed to protect CUI against advanced threats. Additionally, you will need to update your System Security Plan from Level 2 to describe how both the 110 base controls and the 24 additional controls are implemented.
Step 3: Defining Your Assessment Scope
Use the official Level 3 Scoping Guide to categorize which CUI-bearing assets and surrounding systems are in scope. You need to confirm that unrelated systems (such as public WiFI or non-CUI devices) aren’t included.
Step 4: Undergo A Government-Led Assessment
Level 3 requires a government-led assessment by DCMA DIBCAC every three years, plus annual affirmations by the organization’s Affirming Official. The Level 2 (C3PAO) annual affirmation for the same scope must also continue.
The DoD’s Defense Industrial Base Cybersecurity Assessment Center (DIBCAC)’s role in CMMC is to conduct assessments every three years for organizations that need CMMC Level 3. This leads us into Step 5:
Step 5: Maintain and Renew Your Certification
According to official DoD documentation, here are the certification requirements for CMMC Level 3:
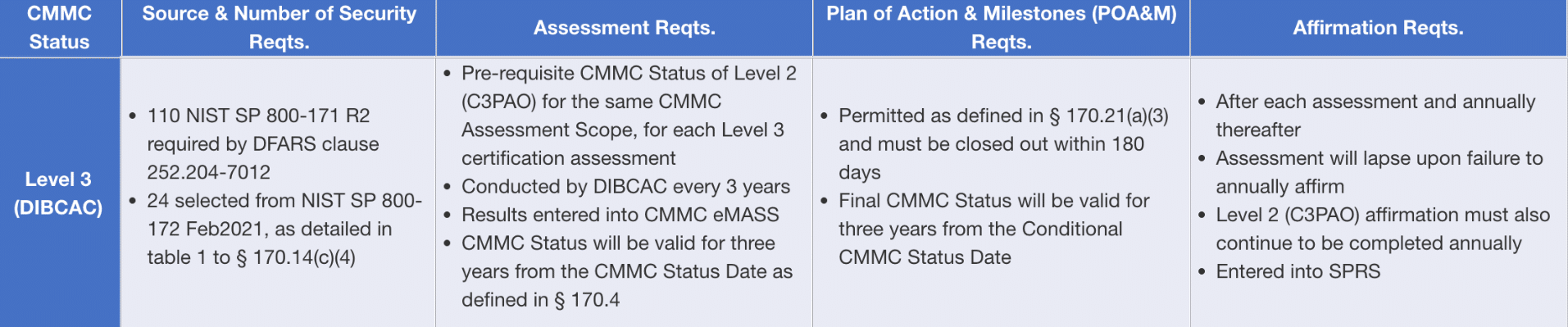
Source: U.S. Department of Defense
Level 3 DIBCAC certifications require renewal every three years, and organizations have to also submit confirmation of compliance every year.
CMMC Level 3 Checklist: Timelines
The time required to meet CMMC requirements varies depending on your organization’s size, industry, and whether or not you already comply with NIST 800-171 or a similar framework. Below are timelines to show what an average organization can expect for Levels 1, 2, and 3.
Working with a vCISO can streamline the process and fast-track you to audit readiness. Rhymetec works closely with trusted auditing partners and can connect you with them for your assessment.
**Note: The following timeline assumes that the organization will start with a gap assessment and follow a typical implementation plan. Organizations that are already aligned with NIST 800-171 can generally proceed faster.
CMMC Level 3 Timeline (9-12 Months)
Gap Assessment and Planning: 1-2 Months
- Gap assessment aligned with NIST 800-171 and advanced controls
- Mapping FCI and CUI
- Initial drafting of documentation
- Create an implementation roadmap
Advanced Technical Controls and Procedural Controls: 6-7 Months
- Network segmentation and access control
- SIEM integration and centralized logging
- Advanced endpoint configuration and hardening
- Security policy creation and approval
- Incident response plan
- …and more.
Validation and Final Preparation For Your Assessment (2-3 Months)
- Vulnerability scan and pen test
- Finalize documentation
- Undergo an official government-led audit
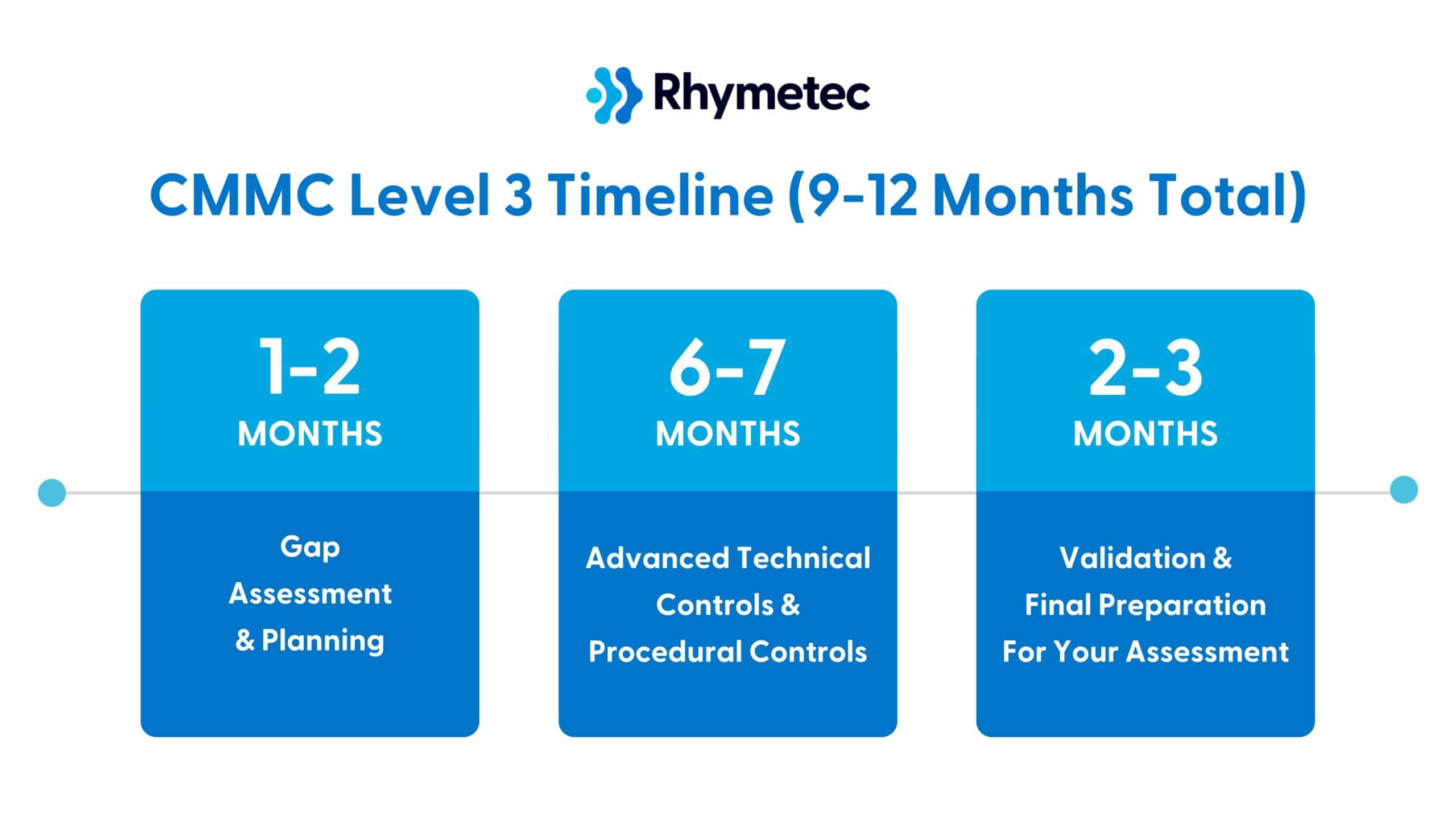
**Note: Level 3 readiness can be accelerated if your organization has already implemented FedRAMP or other NIST-based frameworks. Organizations with complex cloud environments can require more time for controls such as segmentation and advanced logging. The support of a vCISO from the beginning can vastly speed things up!
What About Other Federal Regulations? FedRAMP and CMMC
Many organizations are unsure whether they need to meet CMMC, FedRAMP, or both:
"Being in a marketplace where we're working with a lot of cloud service providers and a lot of software application services, that's one of the most common questions we get. There are significant differences between the two frameworks, but there are also a lot of overlapping controls." - Metin Kortak, CISO at Rhymetec
CMMC applies to DoD contractors and subcontractors working with CUI or FCI, and maps directly onto the NIST SP 800-171 security controls.
FedRAMP is designed for cloud service providers that offer IaaS, PaaS, or SaaS to civilian federal agencies. It is based on NIST SP 800-53, and uses impact-level baselines (Low, Moderate, and High).
"If you are a cloud service provider and you are working with the Department of Defense, there is a likely chance you need to comply with both CMMC and FedRAMP. A lot of organizations in this position will choose to pursue FedRAMP first. If you comply with FedRAMP and you implement all of the controls, you're already implementing the majority of the controls you’ll need for CMMC. The remaining work for CMMC will be working with auditors and gathering documentation.” - Metin Kortak, CISO at Rhymetec
Both frameworks require foundational security measures, including access controls, incident response, and continuous monitoring. However, FedRAMP imposes a broader and deeper set of both technical and documentation requirements, especially around cloud-hosted services.
The good news is there’s substantial overlap—especially at FedRAMP Moderate—but the organization is still responsible for meeting all NIST SP 800-171 Rev. 2 objectives across the CMMC scope. FedRAMP-authorized CSPs help, but you must still map, evidence, and assess controls for your environment.
Organizations that need both will often opt to do FedRAMP first, as they can then leverage that foundation to streamline CMMC compliance. For a deeper dive on the differences between these two federal frameworks (and how to determine which you need), check out our blog on CMMC vs. FedRAMP.
Advantages of Engaging A CMMC Consultant To Help Meet CMMC Level 3 Requirements (The Earlier, The Better!)
The higher levels of CMMC are complex.
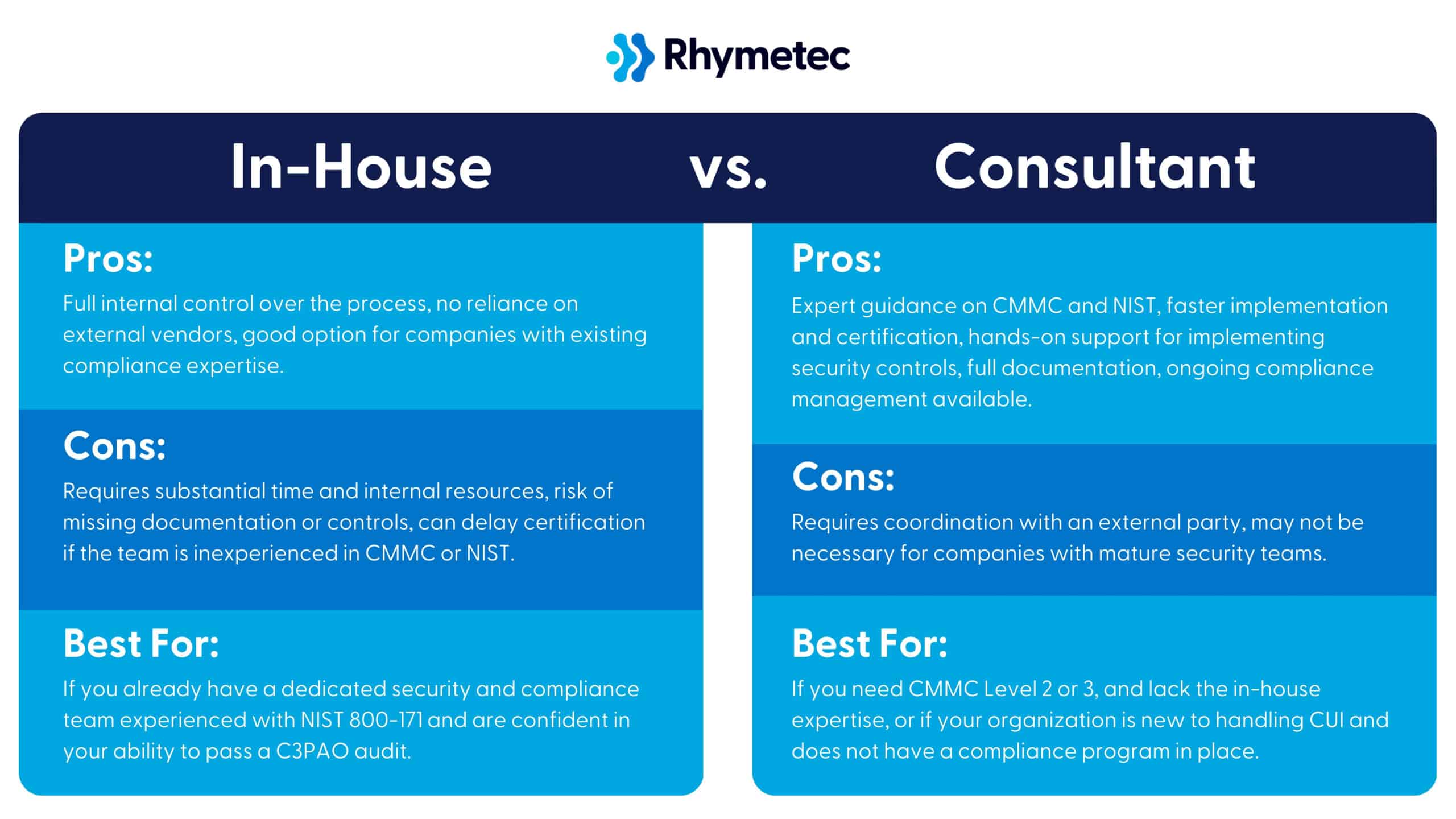
If you aren’t already compliant with the relevant NIST frameworks, compliance for Levels 2 and 3 will require implementing a massive amount of technical controls and corresponding documentation. For many companies, it simply isn’t feasible to manage all of this internally.
This is where a virtual CISO (vCISO) comes in. A vCISO acts as a CMMC Consultant, working closely with your team to understand your environment and translating technical requirements into what you actually need to accomplish.
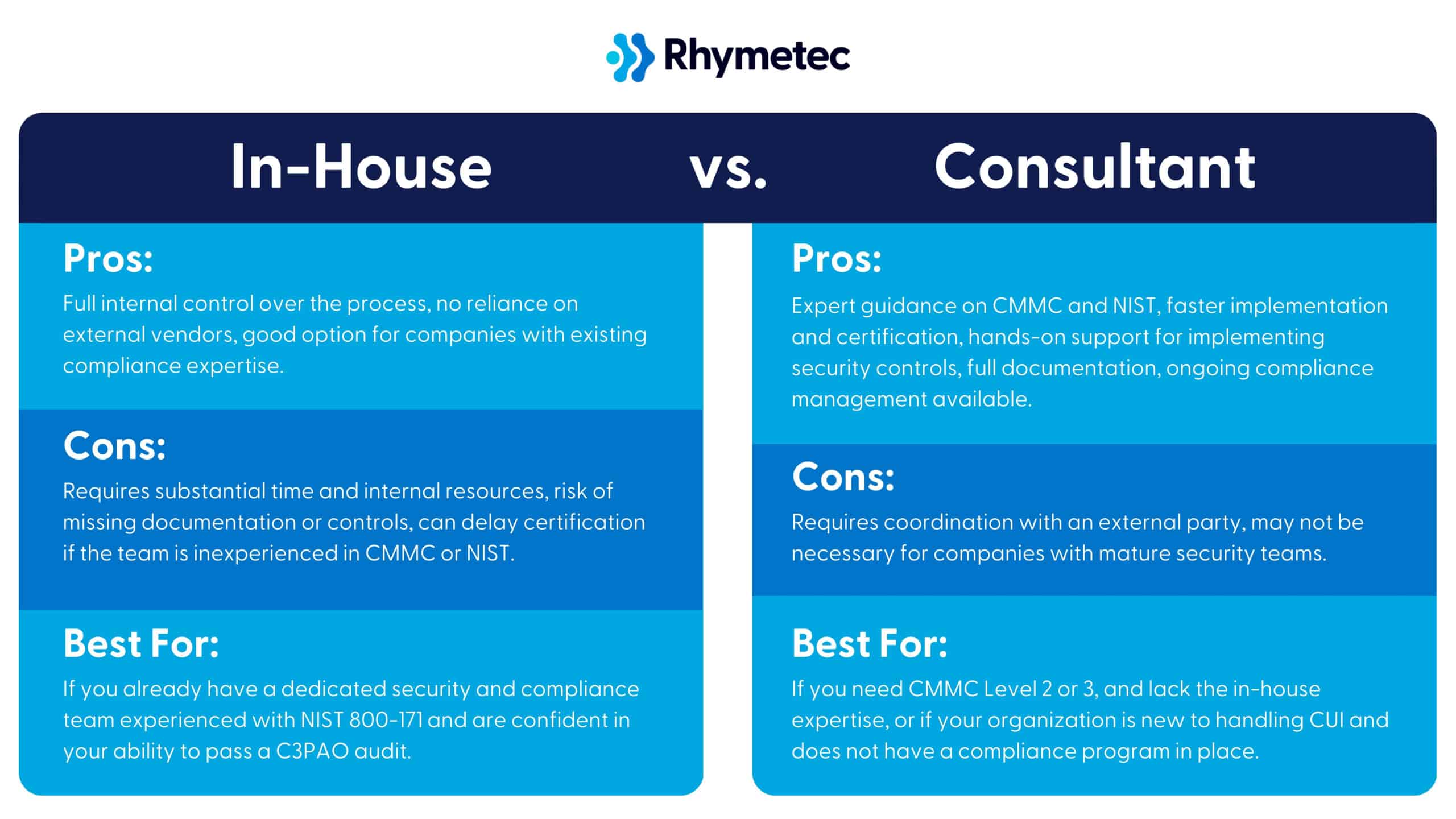
Our vCISOs at Rhymetec support you throughout the entire CMMC preparation process. We conduct your gap assessment, carry out control implementation for the controls you need, finalize documentation, and serve as the main contact point for auditors on your behalf.
**For information on our vCISO pricing options, check out our blog on vCISO pricing.
Outsourcing the bulk of the work required for CMMC is helpful at any point in the compliance process, but is especially transformative during the initial stages. In our experience, especially partnering with startups to meet their compliance goals, working with a vCISO from the beginning allows you to turn an onerous process into a business enabler.
An experienced vCISO will build a security program for your organization that not only meets CMMC and requirements but scales as your business grows. They understand exactly how to structure your compliance program to enable you to more easily meet additional or future requirements in your industry, and can connect you to the best auditing partners in your space. Contact us today to learn more.
Partner For Success: Work With Rhymetec + An Accredited C3PAO
Meeting CMMC requirements is a complex process.
The good news is that you don’t have to do it alone. Our partnership with industry leader A-LIGN, an accredited C3PAO, gives you access to both the security legwork needed to meet requirements as well as certified assessment services.
Together, we help organizations prepare for CMMC with confidence. Whether you are just getting started or finalizing your readiness for an assessment, we’re here to support your compliance journey with security expertise and a trusted C3PAO partner.
C3PAOs are the only organizations authorized by the CyberAB to perform official CMMC assessments. Their involvement is essentially a must-have for any contractor aiming for certification. Meanwhile, as a Registered Provider Organization (RPO), Rhymetec works hand-in-hand with A-LIGN to help you prepare for that assessment.
RPOs are approved to offer consulting and readiness support, and help you implement required controls, remediate gaps, and make sure your security practices and documentation align with CMMC standards. Together with A-LIGN, we are proud to offer this streamlined option for our clients.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with over 1,000 companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – growing their business. Contact us today to get started.
In our recent CMMC webinar, we joined forces with Vanta and A-LIGN to discuss the updated CMMC 2.0 and what organizations should be doing now to meet the requirements. Morgan Kaplan, Director of USG Strategy & Affairs at Vanta, moderated a lively discussion between Metin Kortak, Rhymetec CISO, and Matt Bruggeman, Director of Federal Sales at A-LIGN.
This Rhymetec CMMC Compliance Checklist for CMMC Level 2 is directly based on their discussion and pulls in expert insights from the webinar. Check out the recording of the full webinar here.

First, What Is CMMC?
CMMC, or the Cybersecurity Maturity Model Certification, is the Department of Defense's approach to standardizing cybersecurity requirements across its supply chain. It protects Controlled Unclassified Information (CUI) by requiring contractors (and many subcontractors as well) to meet security practices based on the type of work and data they handle.
As Rhymetec CISO Metin Kortak explained in our webinar:
"CMMC is a framework that's been developed by the US Department of Defense, and it really applies to anyone who's working with the Department of Defense and also processes, transmits, or stores controlled unclassified information. If you're processing that information and you're also working on direct contracts with the Department of Defense, or if you're one of their subcontractors, that means CMMC might apply to you." - Metin Kortak, CISO at Rhymetec
That scope includes contractors, manufacturers, software vendors, and cloud service providers that deal with DoD contracts even indirectly. This Rhymetec CMMC Compliance Checklist breaks down what's required and how to build a roadmap that aligns with contract timelines for CMMC Level 2. (If you need CMMC Level 1, check out our CMMC Level 1 Checklist).
You can also contact our team today and we'd be happy to walk you through everything you need to know.
Contact
How Does The Updated CMMC Version 2.0 Differ From The Original Version 1.0?
CMMC 2.0 simplifies the framework while reinforcing its core goal to protect sensitive data within the Defense Industrial Base (DIB). The shift from Version 1.0 to 2.0 reflects feedback from industry stakeholders who found the original model extremely onerous to implement:
"CMMC 1.0 was quite strict and required organizations to go through many additional requirements outside of NIST 800-171. This made the process extremely difficult, especially for organizations that need to comply with other government compliance frameworks such as FedRAMP. Based on the feedback received, 2.0 is a less strict version of CMMC, while still maintaining the core security requirements.” - Metin Kortak, CISO at Rhymetec
CMMC 1.0 introduced five maturity levels and included additional practices and documentation beyond NIST 800-171. This generated a lot of confusion for subcontractors and SaaS providers, especially those also working toward FedRAMP.
CMMC 2.0 successfully restructured the model around three levels and removed the unique CMMC-only requirements. The new version falls under basic safeguarding practices and are derived from the Federal Acquisition Regulation (FAR) 52.204-21, which directly references and relates to NIST SP 800-171 as part of its requirements.
This change reduces redundancy and increases compatibility with other federal frameworks. With the updated version, CMMC consultants have seen renewed customer interest:
"In the past, in terms of the requirements themselves, it's been more around NIST 800-171, plus a couple of other CMMC requirements. Recently, there have been updates to the CMMC framework. They've updated from Version 1.0 to 2.0. We've seen a lot of interest from our customers about this new version of CMMC." - Metin Kortak, CISO at Rhymetec
This renewed interest is likely since the assessment requirements have evolved. The new version maintains some elements of the previous requirements, but refines the role of C3PAOs (Certified Third Party Assessor Organizations):
"C3PAOs come in and assess you against the requirements, depending on the level that you're at. Our goal is to validate that the sensitive data is actually being protected, because looking historically at just relying on self-attestations to 800-171 for anybody within the supply chain has not been sufficient." - Matt Bruggeman, A-LIGN
In short, CMMC 2.0 is:
- Better aligned with existing industry standards.
- Highly adaptable to real-world constraints.
- More accessible for businesses supporting DoD missions.
Getting Started: Determining Which Level You Need and A Gap Assessment
Before you get started on working through your CMMC compliance checklist (for whichever level you need), it’s important to understand what type of data your organization handles.
This will determine which certification level of CMMC applies to your business:
"The first thing is understanding what type of data you process. If you don't know that, working with a partner to help you determine that can be helpful, because that's going to help you figure out which level of compliance you're going to need to do for CMMC." - Metin Kortak, CISO at Rhymetec
Determining Which Type of Organization Your Organization Handles
Two main types of information matter when it comes to CMMC:
- Federal Contract Information (FCI): Any information provided by or generated for the government under a contract that’s not intended for public release. Include project timelines, internal communications, and organizational charts related to a DoD contract.
- Controlled Unclassified Information (CUI): More sensitive than FCI. This is information that the government has decided needs to be protected, but doesn’t meet classification levels such as “Secret” or “Top Secret”:
“CUI is sensitive information that does not meet the criteria for classification but must still be protected. It is Government-created or owned UNCLASSIFIED information that allows for, or requires, safeguarding and dissemination controls in accordance with laws, regulations, or Government-wide policies.” - Department of Defense
Examples of CUI include software code related to defense programs, incident response reports, training content, documentation for DoD systems, and API guides that define how systems interoperate with DoD environments.
So, which CMMC Level Do You Need?
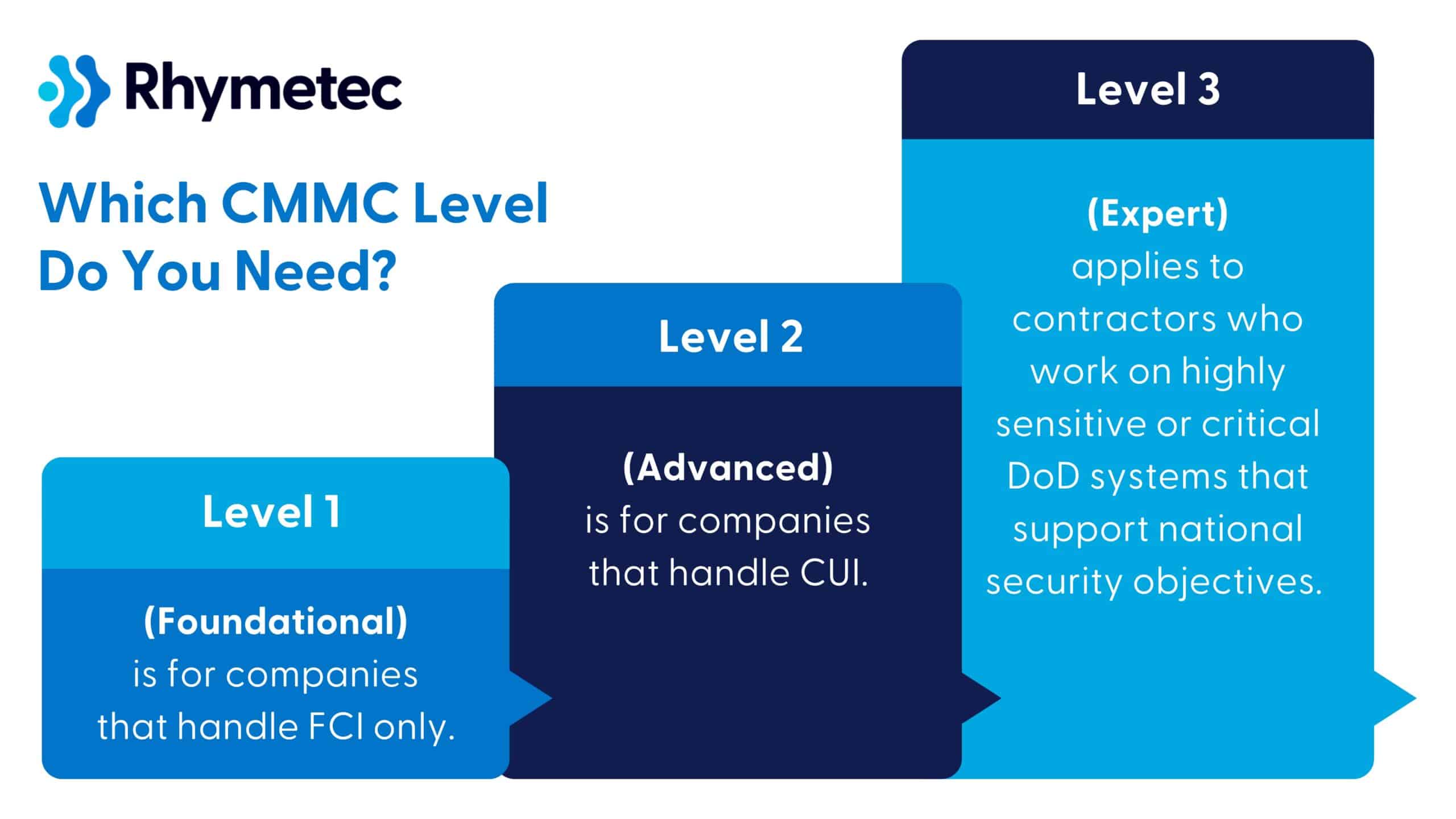
Based on the type of data your organization handles, there are three levels of CMMC:
- Level 1 (Foundational) applies to companies that handle FCI only and do not store or process any CUI. This could be an IT helpdesk vendor managing onboarding for non-sensitive systems, construction companies that work on DoD facilities, or a staffing agency that places civilian contractors on DoD projects, just to give a few examples. The new version of Level 1 falls under basic safeguarding practices and is derived from the Federal Acquisition Regulation (FAR) 52.204-21, which directly references and relates to NIST SP 800-171 as part of its requirements.
- Level 2 (Advanced) is for companies that handle CUI. Examples include a SaaS provider offering workflow tools to a DoD agency that handles technical mission data, manufacturing companies that produce parts for defense blueprints, and subcontractors who write embedded software for military systems. Requirements entail full implementation of NIST SP 800-171 (110 controls). Some contractors allow self-attestation, but many require a C3PAO to perform an audit and issue your certification.
- Level 3 (Expert) applies to contractors who work on highly sensitive or critical DoD systems that support national security objectives. Defense contractors managing secure communications infrastructure, and aerospace or defense firms involved in weapons systems development, are examples of organizations that will need Level 3. Requirements include more advanced security controls based on NIST SP 800-172, and a government-led assessment must be conducted.
Getting Started: Conducting A Gap Assessment
Once you’ve identified which level applies to your organization, the next step is a gap assessment.
"For the next step, at Rhymetec, we always start with a gap assessment. A gap assessment against the NIST 800-171 controls is a must-have…It helps you determine if you have any missing controls or if you have any gaps in your compliance, so you can start putting together a roadmap for completing the remaining controls." - Metin Kortak, CISO at Rhymetec
The aim is to compare your current environment against the required controls. This process tells you what needs to be done before you’re ready to self-attest or move into the certification phase.
CMMC 2.0 also allows you to use a Plan of Action and Milestones (POA&M) to formally track missing controls and your plan for implementing them:
“In 2.0, CMMC came out with a final action and milestones plan. This document essentially allows you to create implementation plans for controls that are missing in your gap assessment, so that you can remediate these controls within a certain amount of time. This is also something you can work with third parties on or conduct your own self-assessment.” - Metin Kortak, CISO at Rhymetec
Next, we'll break down what you need to do for each level of CMMC:
CMMC Compliance Checklist: What Are The Level 2 Requirements?
CMMC Level 2 applies to organizations that process, store, or transmit CUI as part of their work with the Department of Defense. This includes software vendors, MSPs, and subcontractors that handle technical data, system specifications, or any other sensitive project-related information:
"If you process CUI as part of your work in the supply chain of the DoD, that's where the Level 2 requirements come in. A majority of organizations that handle CUI will require a third-party audit and CMMC certification." - Matt Bruggeman, A-LIGN
Level 2 is based on the controls in NIST SP 800-171.
These controls are grouped into areas to include access control, configuration management, incident response, and audit and accountability. For a more comprehensive list of the 110 controls (with more technical detail), see the NIST SP 800-171 official documentation here.
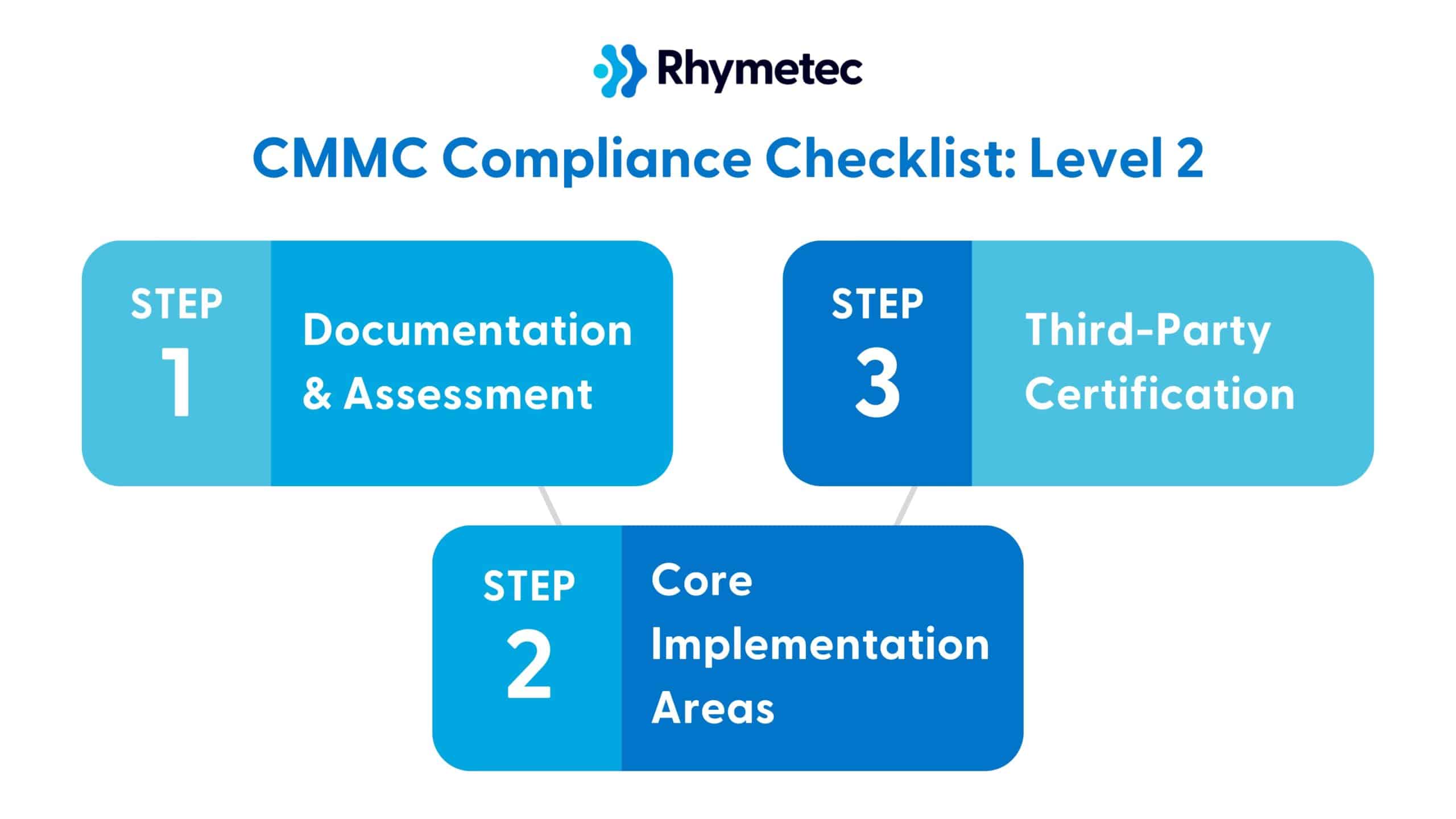
Below is a checklist with the main items broken down into three categories to give you an idea of what to expect:
1. Documentation and Assessment
Complete a full NIST 800- 171A self-assessment (or third-party assessment).
This will show which controls your organization is missing or needs to improve, and form the foundation for remediation work needed for CMMC.
Develop a System Security Plan (SSP).
The SSP documents how your organization has implemented each NIST control and serves as the core evidence package when it comes time for your external assessment by a C3PAO.
Create a Plan of Action and Milestones (POA&M) for any discovered gaps.
The purpose of a POA&M is to outline the timelines and resources needed to remediate security control deficiencies you discovered during the self-assessment.
Submit or update your SPRS score.
The Supplier Performance Risk System (SPRS) score is an indication of how many of the 110 controls you've implemented, and is required by DoD contracting officers when evaluating vendor eligibility.
Document CUI data flows.
Mapping how CUI moves through your systems (and your vendors) is a core part of scoping your security boundary and making sure this is documented in your compliance program.
2. Core Implementation Areas
Access Control.
Enforce measures to include least privilege and MFA, and manage privileged accounts.
Asset Management.
Inventory CUI systems, segment networks, and label systems appropriately.
Audit and Accountability.
Retain records and review logs for anomalies.
Configuration Management.
Establish secure baseline configurations and change control procedures.
Identification and Authentication.
Make sure your organization is using strong authentication mechanisms and unique IDs for users.
Incident Response.
Create an incident response plan if your organization doesn't already have one, and test it.
Maintenance.
Track system maintenance activities.
Media Protection.
Create policies to limit and monitor removable media and sanitize storage before reuse.
Personnel Security.
Screen employees, terminate access promptly, and deliver regular security training.
Physical Protection.
Restrict physical access to systems and facilities handling CUI.
Risk Assessments.
Perform risk assessments and remediate vulnerabilities.
Security Assessment.
Conduct internal control testing and prepare for external audits.
System and Communications Protection.
Implement boundary defenses and encryption for CUI in transit.
System and Information Integrity.
Deploy measures to include endpoint protection, monitoring for malware, and regular patching.
3. Third-Party Certification
Most organizations at Level 2 will be required to undergo an audit by a CMMC Third Party Assessment Organization (C3PAO).
Some contractors (specifically, those working on lower-risk programs) might be permitted to self-attest for Level 2, but this is an exception.
C3PAOs validate the implementation of the 110 controls. Generally, you can expect them to conduct technical testing, interview your staff, and verify documentation.
Preparing for Level 2 requires an enormous amount of coordinated effort across technical and operational domains. Working with a CMMC Consultant can vastly streamline the process for you.
CMMC Compliance Checklist: Level 2 Timelines
The time required to meet CMMC Level 2 requirements varies depending on your organization’s size, industry, and whether or not you already comply with NIST 800-171 or a similar framework.
Below are timelines to show what an average organization can expect for CMMC Level 2.
**The following timeline assumes that the organization will start with a gap assessment and follow a typical implementation plan. Organizations that are already aligned with NIST 800-171 can proceed faster.
CMMC Level 2 Timeline (6-8 Months)
Gap Assessment and Planning (1-2 Months)
- Determine the type of CUI your organization handles
- Map data flows for CUI and list out the systems involved in processing it
- Conduct a gap assessment against the 110 controls
- Draft your POA&M and create an implementation roadmap
Control Implementation (3-4 Months)
- Implementation of 110 controls, including access control, endpoint protection, backup and disaster recovery, incident response, and change management policies.
Documentation and Internal Validation Prior to Audit (1 Month)
- Internal testing of controls
- Vulnerability scan and patching
- Finalize documentation of evidence
C3PAO Audit (1 Month)
- Pre-assessment (optional, but strongly recommended)
- Official audit with interviews, control verification, and documentation review
- Validation of compliance (ongoing)
**Note: A vCISO can streamline the process and fast-track you to audit readiness. Rhymetec works closely with trusted auditing partners and can connect you with them for your assessment.

Advantages of Engaging A CMMC Consultant (The Earlier, The Better!)
The higher levels of CMMC are complex.
If you aren’t already compliant with the relevant NIST frameworks, compliance for Level 2 will require implementing a massive amount of technical controls and corresponding documentation. For many companies, it simply doesn’t make sense to try to manage all of this internally.
This is where a virtual CISO (vCISO) comes in.
A vCISO works closely with your team to understand your environment and translates CMMC requirements into what you actually need to accomplish.
Our vCISOs at Rhymetec support you throughout the entire CMMC preparation process. We conduct your gap assessment, carry out control implementation for the controls you need, finalize documentation, and serve as the main contact point for auditors on your behalf.
**For information on our vCISO pricing options, check out our blog on vCISO pricing.
Outsourcing the bulk of the work required for CMMC is helpful at any point in the compliance process, but is especially transformative during the initial stages. In our experience, especially partnering with startups to meet their compliance goals, working with a vCISO from the beginning allows you to turn an onerous process into a business enabler.
An experienced vCISO will build a security program for your organization that not only meets CMMC and requirements but scales as your business grows. They understand exactly how to structure your compliance program to enable you to more easily meet additional or future requirements in your industry, and can connect you to the best auditing partners in your space.
Partner For Success: Work With Rhymetec + An Accredited C3PAO
Meeting CMMC requirements is a complex process.
The good news is that you don’t have to do it alone. Our partnership with industry leader A-LIGN, an accredited C3PAO, gives you access to both the security legwork needed to meet requirements as well as certified assessment services.
Together, we help organizations prepare for CMMC with confidence. Whether you are just getting started or finalizing your readiness for an assessment, we’re here to support your compliance journey with security expertise and a trusted C3PAO partner.
C3PAOs are the only organizations authorized by the CyberAB to perform official CMMC assessments. Their involvement is essentially a must-have for any contractor aiming for certification. Meanwhile, as a Registered Provider Organization (RPO), Rhymetec works hand-in-hand with A-LIGN to help you prepare for that assessment.
RPOs are approved to offer consulting and readiness support, and help you implement required controls, remediate gaps, and make sure your security practices and documentation align with CMMC standards. Together with A-LIGN, we are proud to offer this streamlined option for our clients. Contact us todayto learn more.
Over 80% of breaches involve weak or misused credentials, according to Verizon’s Data Breach Investigations Report. This is a clear example of just one risk that represents both a security and a compliance risk for organizations, as it impacts everything from the efficacy of your cybersecurity program to compliance audits, contracts, and revenue.
For federal contractors handling Federal Contract Information (FCI), CMMC Level 1 directly addresses this risk and other pressing ones. Level 1 is designed to encourage basic cyber hygiene, and outlines 15 controls that help safeguard sensitive data and maintain eligibility for federal contracts.
In this blog post, we will go over a CMMC Level 1 checklist and requirements, starting with which types of organizations Level 1 applies to:
Government contractors, subcontractors, and suppliers in the federal supply chain that handle FCI (Federal Contract Information) likely fall into CMMC Level 1. This tier is designed for contractors and subcontractors working with the Department of Defense who don't store or process sensitive technical data but still have access to basic contract details, for example.
CMMC Level 1 has 15 requirements. Your organization must meet these 15 requirements and self-attest against them each year. The requirements fall under basic safeguarding practices and are derived from the Federal Acquisition Regulation (FAR) 52.204-21.
Below is our CMMC Level 1 Checklist, starting with the gap assessment process and then walking you through the 15 requirements that need to be addressed:
Getting Started - CMMC Level 1 Checklist: Gap Assessment
"At Rhymetec, we always start with a gap assessment. A gap assessment against the NIST 800-171 controls is a must-have…It helps you determine if you have any missing controls or if you have any gaps in your compliance, so you can start putting together a roadmap for completing the remaining controls." - Metin Kortak, Rhymetec
The aim is to compare your current environment against the required controls. This process tells you what needs to be done before you’re ready to self-attest or move into the certification phase.
CMMC 2.0 also allows you to use a Plan of Action and Milestones (POA&M) to formally track missing controls and your plan for implementing them:
“In 2.0, CMMC came out with a final action and milestones plan. This document essentially allows you to create implementation plans for controls that are missing in your gap assessment, so that you can remediate these controls within a certain amount of time. This is also something you can work with third parties on or conduct your own self-assessment.” - Metin Kortak, Rhymetec
Next, we'll break down what you need to do to meet the requirements of CMMC Level 1.
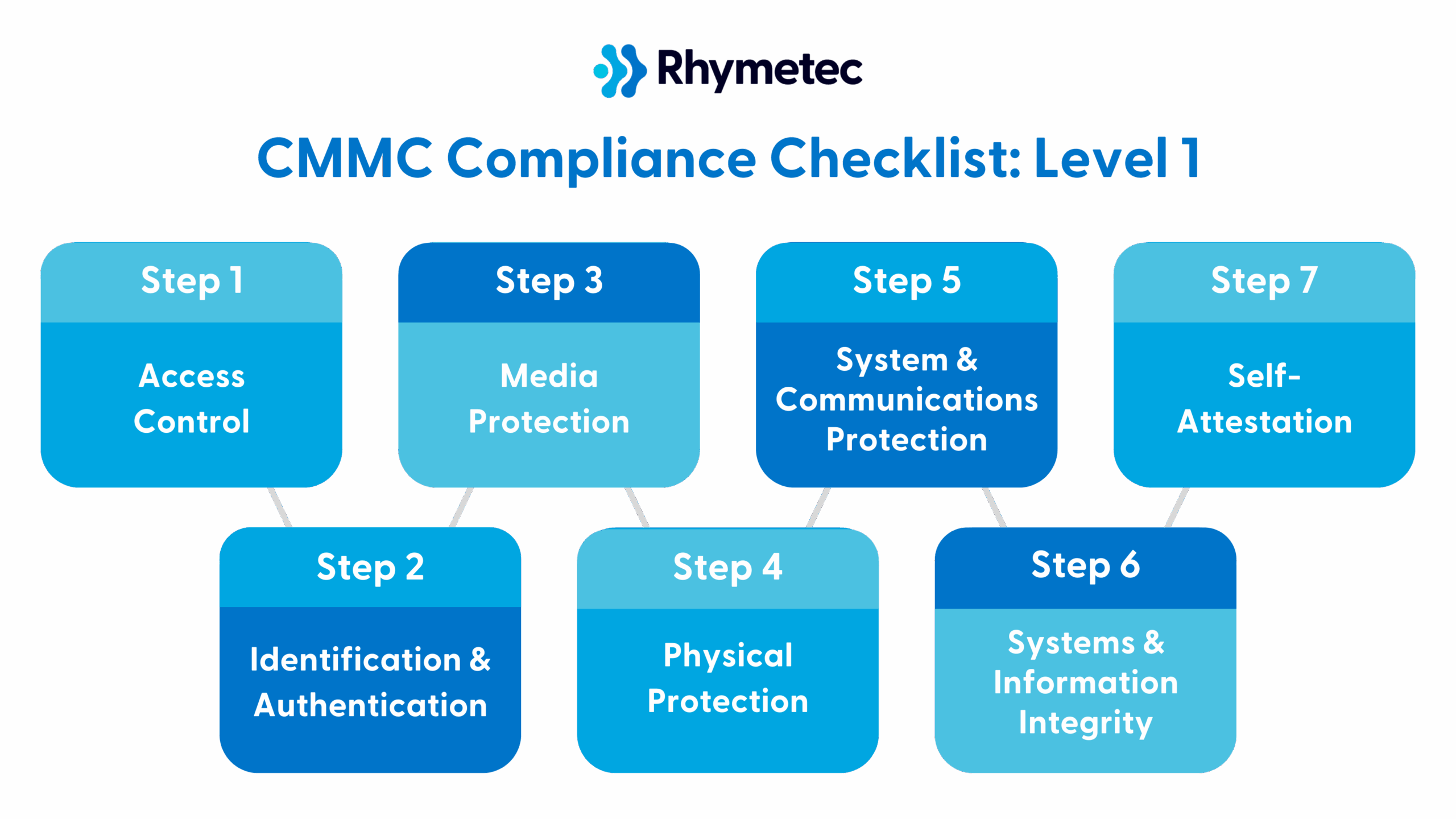
CMMC Level 1 Checklist
If your organization handles only FCI and not CUI, then CMMC Level 1 likely applies to you.
"If you're only handling FCI and not CUI, you fall into Level 1. Level 1 is an order of magnitude less involved than Level 2. It actually only has 15 requirements that are heavily aligned with a subset of the NIST 800-171 framework. You must meet these 15 requirements, and then you just need to self-attest against them each year." - Matt Bruggeman, A-LIGN
This tier is designed for contractors and subcontractors working with the Department of Defense who don't store or process sensitive technical data but still have access to basic contract details, for example. The 15 requirements fall under basic safeguarding practices and map to NIST 800-171, Rev. 2, specifically from Federal Acquisition Regulation (FAR) 52.204-21.
Below are the 15 action items you need to address for CMMC Level 1, divided into clear sections based on our expert advice.
*For a full list of these items with a greater level of technical detail, see the official FAR 52.204-21 documentation.
Access Control
1. Limit system access to authorized users.
To reduce the risk of unauthorized exposure of data, only users with a business need should be able to log in to systems that store or process FCI.
In practice, what you’ll need to do is action items such as setting up role-based access controls, implementing IAM (identity and access management) tools, and regularly auditing user access to remove accounts if they are no longer needed.
These types of security measures entail broader business benefits, as they reduce the risk of insider threats and limit the extent of potential damage in case of compromised credentials.
2. Limit system access to authorized devices.
Even if a user is not authorized, their device might be without the proper controls.
All laptops and mobile devices connected to your systems should be managed to prevent untrusted endpoints from introducing threats. Implementing Mobile Device Management or endpoint detection and response solutions are industry-standard methods to accomplish this and prevent threats from entering through untrusted endpoints.
3. Control access to system functions (e.g., user roles).
Users should only be able to perform actions appropriate for their job (such as admin tasks being restricted to IT staff). It is critical to define roles and assign permissions accordingly, and restrict admin rights to select personnel.
These measures vastly minimize the risk of unauthorized changes or even accidental misconfigurations being made.
4. Verify control connections to external systems.
Any systems that link with a third party (such as a cloud storage provider or file-sharing services) can become gateways for data leaks. As such, they must be reviewed and approved to prevent unauthorized data transfers.
Organizations can accomplish this by maintaining an inventory of all third-party connections, reviewing and approving integrations before use, and monitoring data flow between internal systems and external services. This serves to protect against data loss via insecure APIs or file-sharing platforms.
Identification and Authentication
5. Require user identification before granting system access.
Every action should be traceable to an individual.
Action items to accomplish this objective include assigning unique user IDs to all personnel, eliminating any shared accounts, and enabling logging to tie activity back to specific users.
The business value of this step is crucial, as it creates accountability and aids in forensic investigation in case of incidents.
Media Protection
6. Sanitize or destroy media containing FCI before disposal.
Leaving data on discarded devices is a common but extremely preventable risk.
Simply establishing a process to wipe drives using certified tools, physically destroy storage devices when decommissioned, and document sanitization or destruction (for audit purposes) accomplishes this and prevents data leakage from improperly discarded hardware.
7. Protect FCI stored on removable media and external drives.
Portable storage can create unique risks when used off-site, and it’s critical to protect data in the event devices are lost or stolen.
Avoiding the use of removable media altogether is the best way to circumvent this risk entirely, but if your organization has to use removable media, you should be encrypting USB drives and external hard drives and locking physical storage devices when not in use.
Physical Protection
8. Limit physical access to systems storing or processing FCI.
Unauthorized individuals shouldn’t be able to walk up to a server or terminal.
Acceptable measures to fulfill this requirement under CMMC Level 1 include using keycards, biometric access, or badge systems, monitoring entry points with surveillance, and keeping visitor logs. All of these measures greatly reduce the risk of physical tampering and/or data theft.
System and Communications Protection
9. Monitor and control communications at system boundaries.
Network traffic needs to be inspected and controlled to catch threats early.
Firewalls and intrusion detection tools are used to monitor traffic entering or leaving your network and block suspicious activity, and setting up logging and alerting for traffic anomalies cues you into threats early on.
10. Implement boundary protections such as firewalls and filters.
Network segmentation can both contain threats and reduce their impact.
Actions such as applying email filters and web proxies, enforcing traffic rule zones between zones, and creating VLANs to isolate sensitive systems will limit the radius of a breach and keep attackers from causing further harm.
11. Use cryptographic methods when transmitting FCI.
Sensitive data in transit needs to be protected from being intercepted. The recommended controls around this are enforcing TLS for all network communications, using secure transfer protocols, and encryption.

Systems and Information Integrity
12. Identify system flaws (e.g., patches) and manage them.
Outdated systems are prime targets for attackers. This is why it is crucially important to keep systems up to date by applying security patches regularly.
For CMMC Level 1, organizations need to be accomplishing this by prioritizing critical updates, applying patches on a schedule with a documented process, and regularly checking for software updates.
13. Take steps to protect against malicious code, such as antivirus.
Malware can compromise systems and exfiltrate data. To combat this risk, deploying anti-malware tools to block viruses and other threats that could compromise FCI are industry standard steps.
14. Monitor system activity for security events.
Without visibility, threats can go undetected for months. It’s crucial to set up a way to track system logs in order to detect unusual behavior that could indicate a breach or misuse. To accomplish this, organizations often implement a SIEM platform, or other tools to monitor for suspicious behavior.
15. Perform periodic system scans and take corrective action.
Running regular vulnerability scans to detect weaknesses and applying fixes or updates as needed to keep systems secure is something every organization should be doing. The business value of this last control is keeping your security posture strong and supporting audit readiness.
CMMC Level 1 Checklist: Self-Attestation For CMMC Level 1
Unlike Level 2 and Level 3, Level 1 does not require a third-party assessment.
Instead, your organization must annually self-attest to meet all 15 practices. That attestation must come from a senior company official and be submitted through the Supplier Performance Risk System (SPRS).
Most organizations will need to document the following for Level 1:
- How are these 15 controls above are implemented
- Which systems process or store FCI
- Who is responsible for each requirement
- Dates of the last review and updates
Although Level 1 is a massive degree less resource-intensive than Level 2 or 3, that doesn’t mean that accountability is any less important! Contractors who don’t meet these requirements can face contract risks.
Here is how long you can anticipate CMMC Level 1 to take:
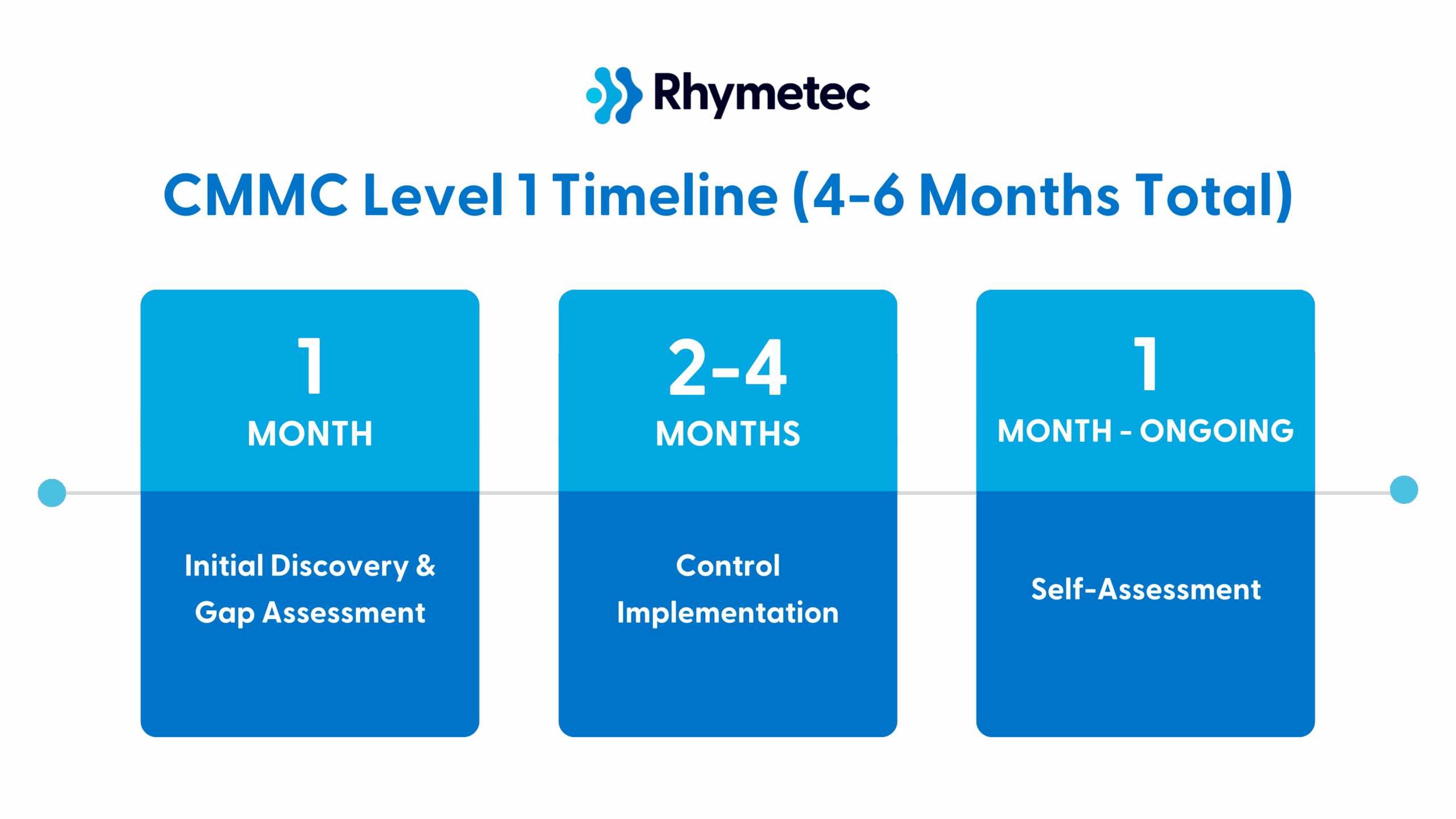
Partner For Success: Work With An Accredited C3PAO
Meeting CMMC requirements is a complex process, even for Level 1.
The good news is that you don’t have to do it alone. Our partnership with industry leader A-LIGN, an accredited C3PAO, gives you access to both the security legwork needed to meet requirements as well as certified assessment services. Working with trusted partners speeds up the timeline for CMMC.
Together, we help organizations prepare for CMMC with confidence. Whether you are just getting started or finalizing your readiness for an assessment, we’re here to support your compliance journey with security expertise and a trusted C3PAO partner.
C3PAOs are the only organizations authorized by the CyberAB to perform official CMMC assessments, if you need to go beyond self-assessments. Their involvement is essentially a must-have for any contractor aiming for certification. Meanwhile, as a Registered Provider Organization (RPO), Rhymetec works hand-in-hand with A-LIGN to help you prepare for that assessment.
RPOs are approved to offer consulting and readiness support, and help you implement required controls, remediate gaps, and make sure your security practices and documentation align with CMMC standards.
Together with A-LIGN, we are proud to offer this streamlined option for our clients. Contact us today to get started.
Meet Hunter!
Hi! My name is Hunter Moreno, and I'm a cybersecurity analyst at Rhymetec. My path to where I am today wasn't traditional. I wanted to delay taking out student loans until I reached university, so I worked in IT full-time while in community college, taking just a class or two each semester as I could afford them.
After receiving my associate's degree, I transferred to university for my bachelor's in cybersecurity. During this time, I got my first cybersecurity role with an oil and energy company where I handled security for their locations across the USA, Colombia, and Mexico. This experience gave me hands-on experience with endpoint security, threat intelligence, and cyberattack response. Most importantly, it taught me to adjust my communication to align with a non-technical audience, as many breaches result from human error, too many tools, or not enough tools.
I recently finished my master's degree in Information Technology with a focus in Information Security. However, my education journey is not over just yet! I plan to start studying pen testing and obtaining certifications.
Tell us a surprising fact about yourself…
I grew up on a ranch in a small town with just one stoplight! I even had a computer with dial-up internet in our barn!
If you could have any superpower, what would it be?
I'd love the power to instantly teach cybersecurity awareness to elderly people everywhere. Elderly people are often targeted by scammers and cybercriminals, and being able to help them recognize and avoid these threats would prevent tremendous financial and emotional damage.
What are some things you enjoy doing outside of work?
I love rock 'n' roll music and going to concerts! I actually got to combine this passion with my studies - my master's capstone project involved creating a database related to music.
Tell us about your role at Rhymetec…
I'm a cybersecurity analyst at Rhymetec, where I've been working since September 2024. I help our customers achieve compliance with standards like SOC 2, ISO 27001, and HIPAA. My daily responsibilities vary quite a bit, which keeps the work interesting, but typically include setting up monitoring alarms in AWS and Azure environments, creating security policies, and running compliance tests. I also conduct vendor reviews and risk assessments, manage device compliance configurations like encryption and MFA setup, oversee mobile device management security, and perform internal audits. A significant part of my work involves gathering evidence for compliance audits and conducting employee security reviews.
Why did you pursue a career in the cybersecurity industry?
My grandfather let me play games on a computer starting around age 5 because he knew computers were the future, and I've been hooked on technology ever since. Growing up, I had to run a 25-foot dial-up cord to the barn just to get more computer time!
As I got deeper into technology during my studies, I was trying to figure out which direction to take my career. I learned that cybersecurity was a rapidly growing field with great opportunities, and that practical aspect really appealed to me. Combined with my fascination with how technology works and the challenge of protecting digital systems, cybersecurity felt like the perfect fit.
What is your favorite part about working at Rhymetec, or in the cybersecurity industry?
I love that cybersecurity is like being a digital protector. Our job is to see threats you don't until it's too late. Every day brings different challenges and puzzles to solve, whether it's helping a client set up better security controls or investigating a potential threat. Plus, the field changes so quickly that I'm always learning something new, which keeps the work exciting.
What is your favorite quote or the best advice you have ever received?
The best advice I’ve ever received came from my mother and grandmother: “Education is the one thing no one can ever take from you.” That belief shaped my approach to life. It taught me that knowledge builds independence, creates opportunity, and empowers you to navigate challenges on your own terms. I carried that mindset through working my way through school and earning my master’s degree, and it continues to guide me today. Whether it’s formal education or self-taught skills, I believe continuous learning is one of the most powerful tools anyone can have.

From a security or compliance perspective, what advice would you give to a potential client or SaaS business?
My biggest piece of advice is to never assume your security controls are working just because someone says they are. I've seen too many cases in my career where servers and systems were thought to be secure, but when we actually verified the controls, we found significant gaps. Often this happens because security measures weren't properly documented or the implementation was never completed as planned.
Compliance frameworks like SOC 2 and ISO 27001 aren't just regulatory requirements - they provide crucial verification that your security controls are actually in place and functioning as intended. Beyond the technical benefits, achieving compliance also demonstrates to your customers and stakeholders that you take security seriously. In today's business environment, that visible commitment to protecting data can be a real competitive advantage.
Connect with Hunter Moreno
In 2025, more companies than ever before are budgeting for ISO 27001 certification costs. In a recent ISO survey, the global number of ISO 27001 certificates reached over 70,000 certificates and were reported in 150 countries and across a range of economic sectors.
Many of these certifications are driven by customer demand and procurement requirements, in particular in fields such as B2B SaaS.
Understandably, cost is often one of the most important questions companies exploring their compliance options have. ISO 27001 is a bit more involved than other frameworks in this space, such as SOC 2, as it requires a broader set of security controls and third-party requirements.
External audit costs, internal resource time, implementing technology changes at your organization, and ongoing maintenance all factor into ISO 27001 certification costs. Without a clear breakdown, it can be easy to underestimate both the initial investment and the ongoing effort.
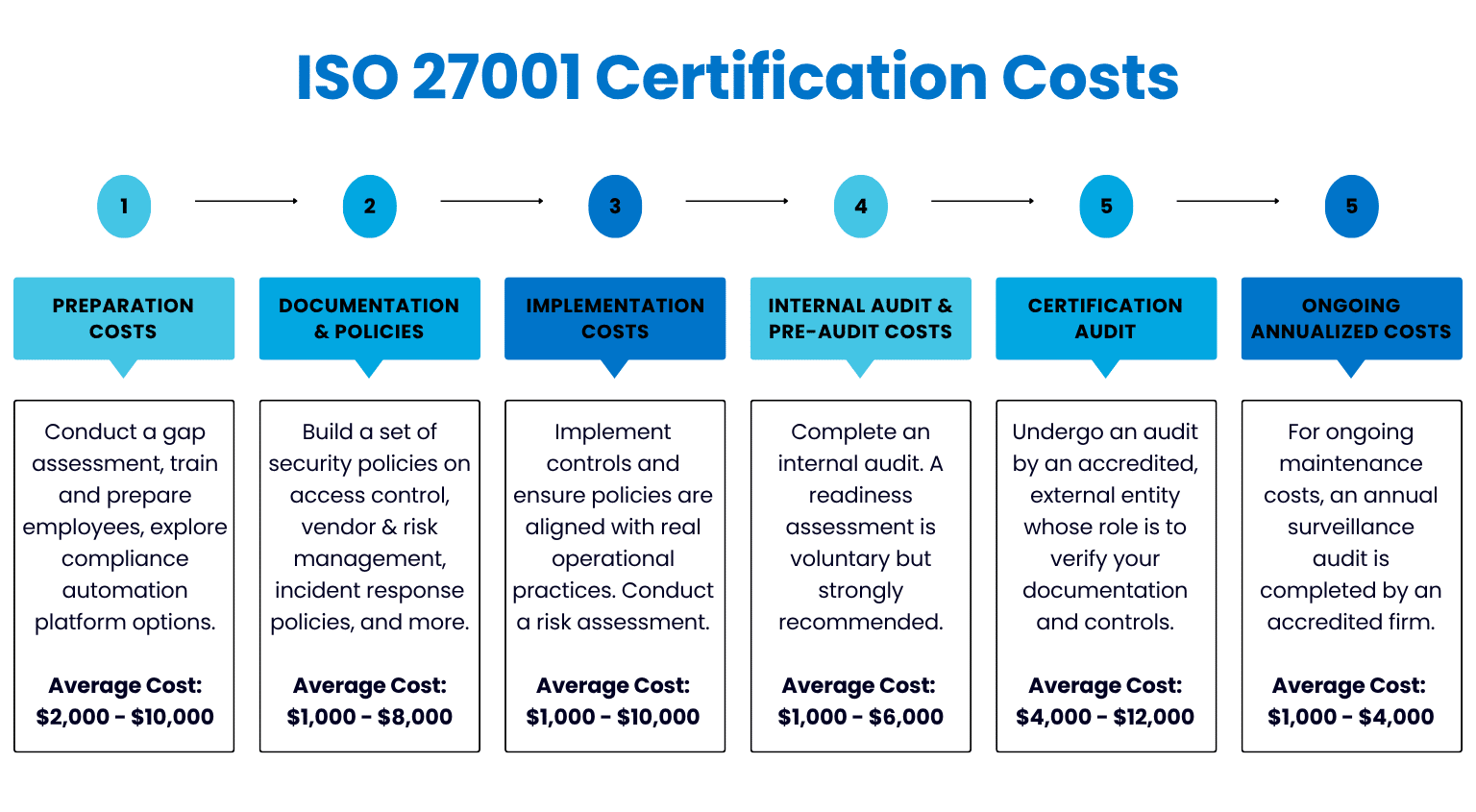
This blog outlines what to expect for ISO 27001 certification costs, based on current market data, our team’s firsthand experience working with SaaS startups, and input from certified auditors we work closely with.
Preparation Costs
Preparation costs for ISO 27001 represent a substantial part of the overall investment. Before engaging a registrar (an accredited certification body), your organization must complete a range of activities that require time, resources, investing in new technologies, and, in many cases, external support.
Typically, the first step of an ISO 27001 engagement is a gap assessment. A gap assessment shows where you are versus where you need to be by identifying missing controls and policy gaps in comparison to the ISO 27001 standard. Companies may complete this assessment internally or work with a third-party consultant for greater objectivity and expertise (if you don’t have in-house personnel with compliance experience).
Following the gap assessment, staff training and security awareness are typically the next steps.
Every employee needs to understand their role in protecting both company and customer data. Your organization will likely need to develop new onboarding materials, invest in employee training sessions, and plan targeted training sessions for engineers and leadership.
The adoption of new software for compliance is often included in the preparation phase. Startups in rapid phases of growth typically select to use tools like Drata or Vanta to automate the pieces of compliance that can be automated, and keep track of their progress in one central place.
These tools support policy management, control tracking, evidence collection, audit preparation, and more. These platforms can vastly simplify the compliance process, but they do entail an investment. Check out our blog post on compliance automation platforms for more information on how these tools work and how they accelerate compliance.
Each one of these preparation activities helps to create a foundation for a successful certification process. Companies that invest early on in assessments, training, and new technologies tend to move through the audit with greater efficiency and fewer surprises. While the cost ranges vary, the effort spent up front directly impacts how much time and work will be needed later on.
Estimated Total Cost of Preparation: $2,000 - $10,000
ISO 27001 Certification Cost: Documentation and Policy Development
ISO 27001 requires formal documentation of the Information Security Management System (ISMS), including your policies and procedures. Documents are reviewed during the audit and must align with how your organization operates in practice.
For this step, most companies begin by building out a core set of policies around access control, vendor management, risk management, acceptable use policies, incident response policies, and asset management. Policies must reflect actual practices and responsibilities that are implemented.
While templates can be used to accelerate this step, customization specific to your organization is important. This is a good example of where using a compliance automation tool (such as Vanta or Drata) in combination with working with an expert security and compliance professional (such as our vCISOs at Rhymetec) can be extremely helpful:
The compliance automation tool provides an excellent baseline, while a dedicated team can customize documentation and policy development to your organization in a way that will pass scrutiny during your audit.
Some companies choose to adopt a full ISMS documentation toolkit or policy automation platform. Although optional, these tools simplify everything from version control to auditor access and stakeholder review, but they do come with additional software costs.
Your documentation will be one of the most scrutinized aspects of your ISO 27001 audit. It’s critical to adequately plan out enough time and resources to draft, review, and align policies with actual practices. Building out your policies with day-to-day operations in mind can help streamline the audit process while supporting long-term security and compliance.
Estimated Cost of Documentation and Policy Development: $1,000 - $8,000
Implementation Costs: Building The Framework
Once documentation is drafted, the next step is to begin actually implementing the controls required by ISO 27001.
The most critical piece of this phase is making sure your policies are aligned with real operational practices. Additionally, at this stage, you will assign responsibilities and validate that controls work as they are meant to. Costs can also add up during the implementation phase from technology upgrades you may need.
Conducting a risk assessment and documenting a plan to mitigate any identified risks is also a key part of this stage. Many companies choose to circumvent the need to acquire new technologies and dedicate internal resources by engaging a vCISO (Virtual CISO). At Rhymetec, our vCISOs take the implementation work off your plate and accomplish these items for you.
Estimated Implementation Costs: $1,000 - $10,000

Internal Audit and Pre-Audit Expenses
Before undergoing your certification audit, you’ll need to complete an internal audit.
In many cases, organizations will outsource this step to a firm specializing in pre-audit assessments (or, if you are already working with a vCISO, they will do this work for you!). Organizations with internal teams can manage this on their own, but many choose to work with outside consultants to speed things up and ensure objectivity. It’s important to note that it’s encouraged to find internal auditors who are PECB-accredited.
The pre-audit, or readiness assessment, is a voluntary but highly recommended assessment typically carried out by a consultant (such as a vCISO) or the certification entity. This serves to mimic your official audit, identifying areas of weakness and reducing the risk of non-conformity during your real audit. Costs during this stage also reflect the need to revise any discovered gaps, finalize your evidence collection, and coordinate between teams.
Estimated Internal Audit & Pre-Audit Costs: $1,000 - $6,000
Certification Audit Costs
After you’ve completed your ISO 27001 readiness work, the ISO 27001 certification audit is conducted by an accredited, external entity. The process is divided into two phases:
Phase 1 - Verifies your documentation.
Phase 2 - Verifies that controls are working as intended.
Costs depend primarily on organizational size, which region you are in, how complex your infrastructure is, and the level of risk associated with your operations. The total cost of the audit covers both of these phases. For startups or for SMBs with less than 100 employees, the audit typically takes anywhere from a few days to two weeks.
If areas of non-conformity are discovered during the audit, it may be necessary to undergo a follow-up audit after making changes. This can cost extra as well. Some auditing firms also tack on administrative costs, in addition to the baseline cost of the audit.
Estimated Cost For Accredited ISO 27001 Audit: $4,000 - $12,000
Ongoing Costs: Maintaining Your Certification
Once certification has been obtained, your organization must maintain the ISMS and undergo annual surveillance audits. This requirement generates a recurring set of compliance activities to be completed every year:
The annual surveillance audit is completed by an accredited firm. While less demanding compared to the original audit, it’s still an obligatory step. Your internal team or vCISO will manage updating documentation, risk remediation where needed, technical control updates, and more.
Additionally, every three years your organization will need to undergo a recertification audit, with costs similar to the initial audit. This is built into the overall ISO 27001 certification costs for ongoing maintenance.
Estimated Ongoing Costs (Annualized): $1,000 - $4,000
Additional Factors That May Influence Your ISO 27001 Certification Cost
While most organizations follow a similar certification process, a number of variables can influence total cost. The following factors will affect the duration of your audit, internal preparation effort, and the level of external support needed:
Company Size and Structure
Larger teams, companies with multiple office locations, or hybrid work environments tend to increase both the number of controls and the audit scope. Costs due to these factors add up in terms of time spent on audit activities, documentation, and coordinating with internal teams.
Level of Technical Complexity
Companies with custom infrastructure, multi-cloud environments, or proprietary platforms often require additional effort in terms of documentation and control verification. Auditors also need to spend more time reviewing technical evidence in these cases.
Systems and Vendors That Are In-Scope
The number of systems and third-party services included in the ISMS directly affects the depth and length of your audit. Most companies include at least a dozen vendors in their initial ISO 27001 scope.
Internal Experience Level
Companies without prior compliance experience will require a greater level of external guidance. Meanwhile, teams that are already familiar with SOC 2 or similar frameworks tend to move faster and are able to reduce external costs.
The controls required for ISO 27001 overlap with several other popular frameworks in this space. If you already have SOC 2, for example, your organization can leverage some of those requirements to meet some of the ISO 27001 requirements.
Auditing Body Selection
Certification bodies charge different rates and employ slightly different methodologies. Regional pricing differences, travel costs, and preferred audit partners can influence the final quote.
Total ISO 27001 Certification Cost
For most startups and SMBs, the full cost of ISO 27001 certification falls between $10,000 - $50,000. This covers everything from preparation, implementation, internal and external readiness assessments, the official audit, and the first year of ongoing expenses.
Companies building from scratch and managing the process on their own will fall toward the higher range, while companies that opt to engage external support (such as a vCISO) will see lower overall bundled costs, even if they are starting from scratch.
This cost is front-loaded in year one, with most of the budget being allocated before and during the initial audit. After certification, annual maintenance costs are typically much lower.
In Conclusion: Planning For ISO 27001 Certification Cost
ISO 27001 certification is a multi-phase effort that touches nearly every part of a company’s operations. The audit itself is just one part of the full cost. Preparation work, implementation of the ISMS, internal (and external) testing, and ongoing maintenance all contribute to the total budget.
Companies that plan early on and understand their internal capacity are better positioned to keep costs under control. For early-stage teams, the main drivers of cost are scope, control maturity, and whether you’re handling the work internally or bringing in outside help.
Most startups and small to mid-sized companies spend between $10,000 - $50,000, depending on how much needs to be built from scratch. Large corporations may spend over $100,000, depending on their industry and the complexity of their operations. At Rhymetec, our vCISO pricing depends on which tier of support you select:

Properly budgeting for ISO 27001 certification costs enables organizations to get certified while building sustainable security practices that scale as the business grows. Whether you are in the early stages of building your compliance program or if you have already started the work and feel stuck, our experts can assist. Contact us today to get started.
Meet Sam!
I grew up in Charlotte, North Carolina, and later moved to Charleston, South Carolina for college, where I earned my Master of Science in Information and Computer Sciences. My career began in IT support, where I worked in both the banking and healthcare industries.
Over time, I transitioned into cybersecurity, and for several years I’ve worked as an Information Security Analyst with a strong focus in the healthcare sector. About a year ago, I joined Rhymetec, where I continue to build on my cybersecurity expertise. Outside of work, I enjoy reading, gaming (both video and board games), working out, and relaxing at the beach.

Tell us a surprising fact about yourself…
Despite growing up biking, skateboarding, and playing sports like basketball and soccer, I’ve never broken a bone or been admitted to a hospital. Knock on wood.
If you could have any superpower, what would it be?
If I could have any superpower, it would be time travel. I’ve always had an interest in history, and the idea of being able to witness significant events or explore different eras firsthand really fascinates me.
What are some things you enjoy doing outside of work?
Spending time at the beach with my fiance, traveling any chance I can, staying active, and enjoying get togethers with my close friends, and family.
Tell us about your role at Rhymetec…
I’ve been with Rhymetec for a year, working as a Cyber Security Analyst. In my role, I support our clients in achieving and maintaining compliance with various frameworks such as SOC 2, ISO 27001, HIPAA, GDPR, and others. My day-to-day responsibilities involve managing project tasks related to audit preparedness, conducting audits for both internal and external clients, and responding to a wide
range of cybersecurity-related client needs.
Why did you pursue a career in the cybersecurity industry?
Ironically, my academic path began with a Bachelor’s in Psychology, but I’ve always had a strong interest in computers and technology. That interest led me to take computer science courses and eventually pursue a graduate degree in Information and Computer Sciences. I started my career in IT support, working in both the banking and healthcare sectors, where I gained hands-on technical experience and a solid foundation in the IT field.
From the beginning, my goal was to transition into cybersecurity. I saw it as a field that was rapidly evolving, full of complex challenges, and deeply connected to real-world outcomes. What fascinates me most about cybersecurity is the pace of change, the constant need to adapt and learn, and the critical role it plays in protecting people, organizations, and data. It’s a career that keeps me engaged, challenged, and continuously growing.
What is your favorite part about working at Rhymetec, or in the cybersecurity industry?
What I love most about working at Rhymetec is the culture and the team. I’m surrounded by dedicated and talented professionals who not only support one another and our clients but also create an environment where growth and development are encouraged. The company has given me the tools and opportunities to grow in this role and continue maturing as a cybersecurity analyst.
What is your favorite quote or the best advice you have ever received?
One of the best pieces of advice I’ve ever received was: “You don’t have to know everything, just be willing to learn.” It came from a mentor early in my career, and it resonates, especially in a field like cybersecurity, where things are constantly evolving. It’s easy to feel like you’re always trying to catch up, but curiosity, adaptability, and a willingness to grow are often more valuable than having all the answers upfront. It’s shaped how I approach challenges, new roles, and even how I support others on my team.
From a security or compliance perspective, what advice would you give to a potential client or SaaS business?
The best advice I would give to a potential client is to build security and compliance into your processes early, not as an afterthought. It’s far more efficient and cost effective to design your systems, policies, and workflows with frameworks like SOC 2 or ISO 27001, in mind from the start, rather than retrofitting them later.
Also, don’t treat compliance as a checkbox exercise. The goal should be to create a security-first culture where protecting data and earning user trust are prioritized. This means investing in monitoring, documentation, employee training, and proactive risk management—not just preparing for the next audit.
Rhymetec can help clients achieve these goals by providing guidance tailored to your specific compliance needs, whether it's SOC 2, ISO 27001, HIPAA, or others. We work closely with clients to build sustainable security programs, prepare for audits, and implement best practices that align with both regulatory requirements and business objectives.
Connect with Sam Brokaw
The federal government spends more than $100 billion annually on IT services, much of it through contracts with private companies. That level of investment brings strict cybersecurity expectations, especially for contractors that handle government data.
Two frameworks frequently encountered in this space are the Cybersecurity Maturity Model Certification (CMMC) and the Federal Risk and Authorization Management Program (FedRAMP). Both programs share the same goal of protecting sensitive information. However, they serve slightly different purposes and apply to different types of vendors.
CMMC is designed for companies working with the Department of Defense, in particular for those that handle Controlled Unclassified Information (CUI). Over 100,000 companies are part of the Defense Industrial Base. Any of them that handle CUI will eventually need to meet CMMC Level 2 or 3.
Meanwhile, FedRAMP applies to cloud service providers working with civilian federal agencies. If you are a defense contractor, a SaaS provider, or if your organization supports both civilian and DoD programs, it's important to understand how CMMC and FedRAMP compare.
This article outlines the main differences between CMMC and FedRAMP, including which types of organizations they apply to, the requirements of each framework, and how to handle certification.

Who Needs CMMC and Who Needs FedRAMP?
CMMC and FedRAMP apply to different groups of contractors and vendors based on two factors:
- The agencies they serve, and
- The type of data they handle.
In short, if you're in the DoD supply chain, you may need to meet CMMC. If you're a cloud provider for civilian agencies, you may need FedRAMP authorization. Some organizations may need to pursue both if they serve both sides of the government in these capacities.
Below is a non-exhaustive list of a few common types of companies to which CMMC would apply. Remember that CMMC applies to companies that do business with the Department of Defense (DoD) and process, store, or transmit Controlled Unclassified Information (CUI) or Federal Contract Information (FCI):
- Defense manufacturers that produce components for aircrafts, vehicles, or weapons systems.
- Managed IT providers that support DoD facilities or systems.
- Staffing firms placing personnel in DoD programs (that involve access to CUI).
- R&D firms involved in any military-related developments or prototypes under DoD contracts.
- SaaS companies providing support to DoD missions.
- …and more.
Basically, if a company touches DoD contract information in any way (and in particular if it involves CUI), it will most likely fall under CMMC.
FedRAMP, on the other hand, applies to cloud service providers that want to sell their platforms or applications to civilian federal agencies (non-DoD). The types of companies this would include are:
- SaaS, IaaS, and PaaS vendors offering cloud-based products to agencies like the Department of Energy, the Department of the Treasury, or the Environmental Protection Agency.
- Data analytics platforms with cloud infrastructure that hosts government data.
- Project management or HR platforms that are seeking to be used across multiple federal departments.
- File storage, communications, or productivity tools that may process or store government records.
- Software vendors selling through government marketplaces like FedRAMP.gov or GSA Advantage.
For more information on what you will need to plan for to meet CMMC requirements specifically - and depending on which level of CMMC you need - check out our CMMC Level 1 Checklist and our CMMC Level 2 Checklist.
Security Requirements Compared
While CMMC and FedRAMP indeed share some overlap given their common goal to protect sensitive government data, they are built on different baseline requirements, and their approaches to security controls differ.
CMMC is based on the NIST SP 800-171 framework. It requires organizations to implement 110 security controls across 14 control families if they handle CUI and need to meet Level 2 certification. For organizations handling only FCI (Federal Contract Information), Level 1 requires 15 controls focused on basic security hygiene. CMMC's overall requirements are structured around the following security considerations:
- Access control
- Incident response
- Configuration management
- Personnel and physical security
- System and communications protection (measures such as encryption and traffic monitoring).
Additionally, organizations must also produce documentation, including System Security Plans (SSPs) and Plans of Action and Milestones (POA&Ms), and be ready for assessment by a third-party assessment organization (C3PAO) at Level 2 or 3. Lastly, it's important to note that CMMC 2.0 is not a point-in-time audit. Contractors are required to maintain compliance continuously. For Levels 2 and 3, assessment will lapse upon failure to annually affirm, according to the DoD's CMMC Guidance.
FedRAMP, by contrast, is based largely on NIST SP 800-53 controls, which are a bit more complex in scope. A Moderate FedRAMP authorization requires over 300 controls across a wide range of domains, including:
- Continuous monitoring of systems and data.
- Incident response procedures and breach notification timelines.
- Risk assessment processes and security authorization packages.
- Documentation of how systems are interconnected/dependent on each other.
- Penetration testing and vulnerability scanning.
- Independent third-party assessments.
FedRAMP places more emphasis on supply chain risk management, cloud architecture documentation, and the remediation of vulnerabilities. Cloud service providers must show that they have a set of documents to pass the Joint Authorization Board or agency review.
Documentation and Assessment Differences To Be Aware Of: CMMC vs. FedRAMP
The goal of documentation for CMMC (at Level 2) is to show that your organization meets the 110 controls from NIST SP 800-171. This includes documentation of:
- How controls are being implemented, and the plan for how they will be maintained. This documentation is your System Security Plan (SSP).
- A Plan of Action and Milestones (POA&M) - A list of gaps and a plan for remediation, with specific steps.
- A list of policies and procedures, showing how your organization covers access control, incident response, configuration management, and other security controls.
- Evidence of implementation (such as user logs, training records, configuration screenshots, etc) also must be included in your documentation.
Finally, assessment is conducted by a C3PAO (Certified Third-Party Assessment Organization) for Level 2. Self-assessment is allowed at Level 1 (and in some cases, for Level 2), but must still be documented in SPRS (Supplier Performance Risk System) and affirmed by a senior official.
*It's important to note that if you need CMMC Level 3, you will still need C3PAO affirmation completed on an annual basis, according to the DoD's updated overview of CMMC. For CMMC Level 3, the ongoing C3PAO assessments are in addition to undergoing an assessment every 3 years by the Defense Contract Management Agency's Defense Industrial Base Cybersecurity Assessment Center (DIBCAC).
FedRAMP documentation, meanwhile, is part of a full authorization package submitted to either a sponsoring agency or the Joint Authorization Board. Required documents include:
- System Security Plan (SSP) - this can often reach over 600 pages for Moderate-level systems!
- A Privacy Impact Assessment that identifies how personal data is being collected, used, and protected.
- A Continuous Monitoring Plan detailing how your organization will monitor system changes, incidents, and vulnerabilities.
- An Incident Response Plan, showing how incidents will be reported and handled.
- Documentation showing how system changes are approved and tracked (also known as a Configuration Management Plan).
Assessment is carried out by a third-party assessment organization that has been recognized by the FedRAMP PMO (Program Management Office). FedRAMP requires ongoing authorization maintenance, which takes the form of monthly vulnerability scans, incident reporting, and annual reassessments.
How Certification Works: CMMC vs. FedRAMP
CMMC 2.0 certification is tied to a company's eligibility for Department of Defense contracts. Depending on the sensitivity of the data involved, contractors must meet either Level 1 (self-assessed) Level 2 (typically third-party assessed) requirements, or Level 3 (third-party assessed). As discussed in greater detail in the previous sections, the process entails the following steps:
The first step is to conduct an internal NIST 800-171 gap assessment to compare where you are versus where you need to be. The next step is to document your System Security Plan and Plan of Action and Milestones, followed by finally engaging a certified third-party assessment organization (for Level 2 and 3).
There is no central approval body, and certification is granted per contract, with the assessment scope being based on the environment that contains CUI.
FedRAMP follows a centralized authorization process managed by the FedRAMP Program Management Office. There are two paths:
- Agency Authorization. For this option, a single agency sponsors the cloud service provider and reviews the authorization package.
- Joint Authorization Board. Authorization via a Joint Authorization Board (which comprises the DHS, GSA, and the DoD) involves a higher bar of scrutiny.
For the FedRAMP process, your organization will work with a Third-Party Assessment Organization to complete your Security Assessment Plan and Security Assessment Report. You'll then need to submit a full authorization package through FedRAMP's secure repository, and finally, undergo ongoing monitoring after approval.
Can You Be Compliant With Both?
The short answer is yes.
If your organization provides cloud-based services to civilian agencies and works with the Department of Defense, you likely need to comply with both FedRAMP and CMMC. For example, a SaaS company that supports DoD contracts involving CUI will need CMMC Level 2, and if the same product is then sold to a civilian agency (like the Department of Energy), they will also need FedRAMP authorization.
CMMC and FedRAMP share foundational requirements from NIST standards. But it's not a direct map on - meeting FedRAMP Moderate, for instance, doesn't automatically mean you meet CMMC Level 2. The good news is it absolutely does reduce duplication in areas such as access control, system monitoring, and incident response.
If you do need both CMMC and FedRAMP, figuring out early on how to align both compliance efforts can reduce cost and headaches down the road. This is a common use case for working with a consultant to manage both tracks. A consultant has the experience implementing these requirements across a large spectrum of different types of organizations, and can help ensure efficient implementation.
When To Bring In A Consultant Or MSSP
A recent report by the U.S. Government Accountability Office shows that many small businesses in the defense industry lack the internal resources to implement NIST 800-171 without outside help. This illustrates a growing need for CMMC consultants and MSSPs.
In the report, many smaller businesses in particular expressed concerns about the costs and resources required for CMMC implementation. This is where outsourcing the process can be transformative. Outsourcing is a fraction of the investment that building out an in-house team to carry out the implementation process would be.
The fact is that organizations often wait too long to bring in help, and this can lead to missed deadlines and unnecessary rework. If you're pursuing CMMC, FedRAMP, or both, bringing in a consultant early can reduce risk and cost.
It can be a good idea to bring in a consultant or MSSP if you don't have internal staff with experience in NIST 800-171 or 800-53 implementation, if you're unsure how to scope your CUI, if you're being asked to respond to a security questionnaire and aren't confident in your answers, or if you need to align your environment for both frameworks.
A consultant will perform a gap analysis, build a compliance roadmap, draft documentation for you, implement technical controls, and fully prepare your team for assessment. For small and mid-sized organizations, especially those with aggressive go-to-market timelines, outsourcing to a qualified team helps avoid delays and prevents compliance from blocking growth.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
With a Registered Practitioner on Staff and a Proven Track Record, the Company Solidifies Its Role as a Leading Partner for Defense Contractors Navigating New CMMC Requirements.
NEW YORK, May 28, 2025 –
Rhymetec, the industry leader in cloud security that provides innovative cybersecurity, compliance, and data privacy services to modern-day SaaS businesses, today announces it has achieved the status of Cybersecurity Maturity Model Certification (CMMC) Registered Provider Organization (RPO) through CyberAB. Developed by the U.S. Department of Defense (DoD), the CMMC Program is a set of rules designed to strengthen cybersecurity and protect sensitive government information shared with defense contractors.
As a CMMC RPO, Rhymetec is equipped to provide expert advisory and compliance readiness and maintenance services to help organizations understand CMMC requirements, implement necessary controls, and prepare for audits and assessments. This milestone is especially timely, as the final CMMC requirements take effect this month, making compliance essential for contractors looking to win or retain DoD contracts. Rhymetec's commitment to advancing CMMC readiness is further demonstrated by its active participation in industry events such as CEIC West and recent collaborations with leading compliance partners like Vanta and A-LIGN.
"With the final CMMC requirements now in effect, defense contractors and subcontractors are under real pressure to get compliance right," said Justin Rende, founder and chief executive officer of Rhymetec. "Achieving RPO status reinforces our commitment to guiding clients through this critical process with clarity, confidence, and deep expertise."
In addition to being a designated CMMC Registered Provider Organization (RPO), Rhymetec's chief information security officer (CISO), Metin Kortak, has earned the credential of CMMC Registered Practitioner (RP). This distinction underscores the company's dedication to cybersecurity excellence and hands-on expertise. Having a certified RP on staff is not only a requirement for RPOs but also enhances the value of Rhymetec's advisory and managed services, enabling more strategic guidance and tailored preparation for organizations seeking certification under the latest CMMC standards.
"CMMC isn't just about checking boxes; it's about building a resilient security posture that can stand up to real-world threats," said Metin Kortak, CISO of Rhymetec. "As a Registered Practitioner, I'm proud to help organizations cut through the complexity and take actionable steps toward long-term compliance and protection."
If your organization needs guidance navigating the complexities of CMMC compliance, including conducting gap assessments or self-assessments, developing System Security Plans (SSPs), drafting a Plan of Action and Milestones (POA&M), implementing required security controls, and supporting remediation efforts, Rhymetec can help.
You can read the original press release on PR Newswire.
About Rhymetec
Rhymetec is an industry leader in cloud security, providing innovative cybersecurity and data privacy services to the modern-day SaaS business. The company builds, deploys and manages compliant information security and data privacy programs directly within their customers' unique environments, allowing them to focus on their core competencies within their business. Over the years, Rhymetec's services have grown to include a vCISO (Virtual CISO) program, ISO Internal Audits, and a variety of Penetration Testing services. For more information, please visit www.rhymetec.com and follow us on LinkedIn.

Meet Vic!
My name is Vic DeBenedetto, and I grew up in the Philly suburbs (Go Birds!).
Growing up for me consisted of lots of sports practices during the school year and spending summers down at Long Beach Island, NJ. Although, like most kids, I tried every sport there was, the two that stuck were football and lacrosse. In the summer, I hung up the cleats and was a stand up paddleboard instructor at my local marina.
After college at Penn State, I moved back to Philly. After a 4-year stint in the city, I recently settled in the suburbs.
Tell us a surprising fact about yourself…
When I was 18, I explored every career path that didn't involve going to college. My top two options that I can remember were enlisting in the military or becoming a barber. I'm not sure what drove that, but I'm glad I ended up where I am!
If you could have any superpower, what would it be?
If I could have any superpower, it would be the ability to completely block out distractions and focus at will. In a world that's constantly buzzing with notifications (Slack especially) and competing priorities, having consistent focus would be a game-changer - not just for productivity, but for being fully present in everything I do.
What are some things you enjoy doing outside of work?
My favorite thing to do outside of work is golf. While my handicap is still in the double-digits, I have the bug and try to get out as much as possible! In the winter, I'm an avid skier and try to book at least one trip a year. Outside of that, I do CrossFit every morning before work to start the day, which never fails to humble me. On the weekends, if I'm not on the golf course or in the gym, I'm usually either trying new restaurants out or hanging out with friends and family.

Tell us about your role at Rhymetec…
I have been working at Rhymetec for over a year—but it feels like so much longer (in the best way)! As an Account Executive, I'm responsible for bringing new business into Rhymetec and expanding our reach. I work closely with our incredible partners to identify prospects who are a strong fit for our services and guide them through their compliance and cybersecurity journeys, from initial discovery to onboarding. My role is a mix of consulting, partner relationship-building, and sales, which keeps every day interesting.
What I love most about working at Rhymetec is the combination of people and purpose. I truly believe we have the best team and culture; everyone is driven, supportive, and fun to work with. I feel inspired every time I open my laptop and genuinely look forward to the conversations and challenges each day brings. It's rewarding to know that the work we do makes a real difference for our clients, helping them feel confident and secure as they grow.
Why did you pursue a career in the cybersecurity industry?
I came from a marketing technology background, and while I enjoyed that space, I was looking for something that felt more like a need rather than a nice-to-have. That's what drew me to cybersecurity. It's an industry that's not just growing rapidly—it's essential. Every company, no matter the size or industry, needs to take security seriously, and I found that really compelling.
I didn't always plan on working in cybersecurity, but once I learned more about the space, I was completely bought in. The constant evolution of threats and the high stakes involved make it both fascinating and meaningful. I love that the work we do helps companies protect what matters most and gives them the confidence to keep moving forward.
What is your favorite part about working at Rhymetec, or in the cybersecurity industry?
One of my favorite parts is getting to collaborate with such great partners. We work with some of the best in the industry, and it's rewarding to be part of a network that's all working toward the same goal: helping companies strengthen their security and achieve compliance. The relationships we've built with our partners make the work not only effective but also enjoyable—I'm constantly learning and growing through them.

What is your favorite quote or the best advice you have ever received?
The best advice I've ever received came from my dad, who always reminded me: "God gave you two ears and one mouth, so listen twice as much as you speak." It's simple but powerful, and it's stuck with me throughout my personal and professional life. Whether I'm in a meeting, on a sales call, or just having a conversation, I've found that really listening—rather than thinking about what to say next—makes all the difference. It helps build trust, uncover real needs, and create stronger connections.
From a security or compliance perspective, what advice would you give to a potential client or SaaS business?
When advising a potential client or SaaS business from a security or compliance perspective, I would emphasize the importance of adopting both a proactive and holistic approach to data protection and regulatory adherence. A reactive and narrow will always lead to a large-scale data breach and loss of customer trust.
At Rhymetec, we understand that a proactive and holistic security program involves implementing various controls across multiple security domains including, but not limited to, risk management, incident management, cryptography and access management. Additionally, staying informed about relevant regulations—such as GDPR, HIPAA, or DORA—and regularly ensuring that your practices align with these standards is essential for maintaining compliance and building trust with your clients.