Needing to meet EU AI Act compliance has further complicated regulatory requirements around AI for many companies - even those that are located outside of Europe. The stakes are substantial, with fines of up to €35 million or 7% of global annual revenue for serious violations. For context, that exceeds even GDPR penalties.
The Act imposes significant obligations on companies developing or deploying AI systems. If you're a U.S.-based SaaS company offering AI-powered services in the EU, for example, the law may apply to you. If your product touches high-risk areas like healthcare, recruitment, or finance, you'll have stricter protocols to follow.
Our team at Rhymetec helps organizations understand their compliance requirements, automate the parts of compliance that can be automated, and fast-track your compliance. This article will help you understand whether your AI systems fall within scope and their risk categories, the measures you need to implement, and how to turn compliance into a competitive advantage.

Which Types of Organizations Need EU AI Act Compliance?
The EU AI Act applies to organizations that develop or use AI systems within the European Union (EU), regardless of where they are based. Even companies outside of the EU must comply if their AI systems affect individuals in the EU.
The Act categories AI systems based on risk, with corresponding requirements for each category:
- Prohibited AI Systems: These are AI systems that pose unacceptable risks. An example of this under the EU AI Act would be an AI system being used to predict the risk of an individual committing a crime based solely on personality or profiling traits.
- High-Risk AI Systems: AI used in critical areas such as law enforcement, hiring, credit scoring, infrastructure, and medical devices must meet strict requirements. Both providers and deployers of high-risk AI have to comply with these obligations.
- Limited-Risk AI Systems: AI systems with transparency obligations, such as chatbots or AI-generated content, must disclose that users are interacting with AI.
- Minimal-Risk AI Systems: These are AI applications with low regulatory impact, such as spam filters or recommendation algorithms. These tend to be largely unaffected by the EU AI Act.
Organizations impacted by the AI Act include:
- AI Developers and Providers: Companies building AI models or integrating AI into their products must meet compliance requirements if their systems fall under high-risk or transparency rules.
- Deployers of High-Risk AI: Businesses using AI systems classified as high-risk in hiring, credit decisions, or critical services must comply with risk management and oversight obligations.
- Distributors and Importers: Organizations that place AI systems on the EU market must verify compliance before distribution.
- Non-EU Companies Serving EU Users: Organizations are subject is the Act if they offer AI-driven services or products affecting EU individuals. For example, a software company outside of the EU selling AI-based medical diagnostics to European healthcare providers would need to comply.
Companies must determine which of their AI systems fall under the AI Act's scope and what compliance obligations apply, based on how the technology is being used.
What Are The Requirements, and How Can EU AI Act Compliance Be Achieved?
Compliance with the EU AI Act entails several core requirements (all of which Rhymetec can fulfill on your behalf!). Below are the main requirements and how to meet them. Keep in mind that your organization's requirements will vary based on the risk level of your AI systems, as discussed above.
1. Risk Management
High-risk AI providers are required to extensively document their risk management process. Risk management under the EU AI Act means having a clear process on how you will assess and mitigate AI-related risks, through measures including continuous monitoring and periodic evaluations to address any emerging risks.

2. Incident Response and Business Continuity
Organizations must have mechanisms in place to not only identify AI risks but also to actually respond to incidents.
Your team should know exactly how they would respond and recover from AI-related failures or security incidents. This can be documented in an incident response plan, which is a good idea for every organization to have regardless of their compliance obligations. For your business continuity plans, the goal should be to ensure that AI systems remain operational and safe during disruptions.
3. Data Protection and Recovery
AI systems must use training data that is as high-quality and unbiased as possible. They must also implement corresponding controls to protect data from unauthorized access, corruption, or loss. This set of requirements under the EU AI Act shares heavy overlap with privacy regulations in the EU, such as GDPR.
4. Ongoing Security Controls
AI systems need to include safeguards against cybersecurity threats and vulnerabilities. This can be accomplished by applying security measures, including access controls, logging, and anomaly detection.
5. Compliance Documentation and Reporting
Lastly, AI providers need to keep detailed records of system design, functionality, and decision-making processes. High-risk AI systems require additional technical documentation that can be reviewed by regulators.
How Does The EU AI Act Compare To Voluntary AI Frameworks?
Understanding the differences and overlap between the EU AI Act and voluntary frameworks (like ISO 42001 and the NIST AI Risk Management Framework) can help streamline your compliance efforts. The good news is that these frameworks do overlap quite a bit, and you can leverage existing work you may have already completed and/or use EU AI Act compliance to fill in requirements for future regulations.
The EU AI Act vs. ISO/IEC 42001
ISO 42001 provides an excellent framework for AI governance but does not carry legal obligations. Companies that adopt ISO 42001 must still meet the EU AI Act's legal obligations if their AI system(s) fall under the Act. Fortunately, there is some overlap between the EU AI Act and ISO 42001 controls:
If your organization already has an ISO 42001-compliant risk management framework, it can fairly easily be adapted to fulfill the EU AI Act's risk assessment obligations. Both the EU AI Act and ISO 42001 also include controls for bias mitigation and improving data quality. If you have already documented data governance policies under ISO 42001, they can contribute to meeting these requirements.
Finally, ISO 42001 requires documenting your AI system risks and objectives. The AI Act mandates similar documentation for high-risk AI systems, so an organization that is already ISO 42001 compliant can leverage existing documentation to fulfill the AI Act's record-keeping obligations.
The EU AI Act vs. The NIST AI Risk Management Framework
The NIST AI RMF is a voluntary guideline that provides a framework organizations can use to manage AI risks, but it does not entail enforcement measures or assign risk categories.
However, both heavily emphasize risk management and governance. Companies that have already adopted the NIST AI RMF already have elements in place that align with the AI Act requirements. For example, the NIST AI RMF defines oversight roles that can be mapped onto the AI Act's requirements to designate responsible individuals for compliance and monitoring.
Another area in which the requirements overlap is transparency and documentation. Under the NIST AI RMF, organizations are encouraged to document AI risks and decision-making processes. Likewise, the AI Act requires technical documentation for high-risk AI systems, including explanations of system functionality.
In general, businesses with existing voluntary AI frameworks can accelerate EU AI Act compliance by mapping existing controls to the Act's requirements. Organizations that use the NIST AI RMF or ISO 42001 have a head start in EU AI Act compliance, but must still determine whether their AI system(s) fall under the Act and what additional legal obligations apply.

5 Business Benefits of EU AI Act Compliance
For many organizations, complying with the EU AI Act is a regulatory requirement. However, it can also provide other advantages. Companies that integrate AI Act compliance into their operations reduce their legal risks while strengthening their market position and improving trust. The 5 main benefits are:
1. Broader Access To The EU Market
Compliance allows businesses to sell and deploy AI systems in the EU without facing legal barriers or enforcement actions. Companies that fail to comply, meanwhile, risk facing fines and restrictions on their AI products.
2. Substantial Reduction in Risk To Your Organization
By implementing AI governance, risk management, and transparency measures, you can reduce the likelihood of legal disputes, regulatory penalties, and reputational damage to your organization.
3. An Advantage Over Non-Compliant Competitors
By meeting the requirements under the EU AI Act, your organization can demonstrate a commitment to responsible AI use, which helps differentiate you in the market. Customers, investors, and business partners may prioritize vendors with compliant AI solutions.
4. Stronger AI Governance
A natural byproduct of meeting requirements under the EU AI Act is having clearer AI-related policies and oversight processes. This improves internal decision-making and AI systems' reliability. Companies that comply with the EU AI Act will also find it easier to adapt to other current and/or future AI regulations.
5. Customer and Public Trust
The general public and businesses are increasingly concerned about AI-related risks. Seeing that you are compliant with the EU AI Act creates reassurance that you take the risks seriously, and builds confidence in your AI products and services.
In Conclusion: EU AI Act Compliance Key Takeaways
The EU AI Act introduces an array of requirements impacting AI providers, deployers, and businesses operating in the EU or serving EU users. Compliance includes risk management, incident response plans, documentation, and ongoing security controls. EU AI Act compliance is an entry point to many business advantages, such as expanding your market access in the EU.
Many organizations choose to outsource the work of EU AI Act compliance to a virtual CISO (Chief Information Security Officer). Our virtual CISOs at Rhymetec have helped over 1,000 organizations meet their security and compliance needs in the fastest timeframe possible. Contact us today or check out our information on vCISO pricing to learn more.
Interested in reading more? Check out more content on our blog:
- DORA Compliance Checklist: What The EU's Digital Operational Resilience Act Means For Your Business
- NIS2 Requirements: What You Need To Know For Your Business
- Compliance For Startups: The Definitive Guide to Picking the Right Consultant
This Rhymetec DORA Compliance Checklist will help you understand DORA requirements, how to determine if your business falls under DORA's umbrella, the specific measures you'll need to implement, ways to leverage compliance for business growth, and a roadmap to get started.
The European Union's Digital Operational Resilience Act (DORA), which took effect in January 2025, aims to protect financial institutions from risks their dependencies on technology providers may pose to them.
The Act doesn't just cover the financial institutions. If you provide services to EU financial institutions, even if you are a small software company, DORA may apply to you. Many technology providers are classified as "critical ICT third-party service providers" (CTPs) under DORA, and need to adhere to the requirements.

Financial institutions today rely heavily on a variety of services from tech companies.
For example, your average regional bank nowadays may rely on 1) a cloud storage provider for customer data, 2) a payment processing API for transactions, and 3) a third-party authentication service for security, just to name a few.
A disruption in the services of any one of these could threaten the bank's ability to operate. Given how reliant financial institutions have become on these types of services, stricter regulatory oversight is long overdue in this sector. DORA aims to fill this need.
Who Needs To Comply With DORA Requirements?
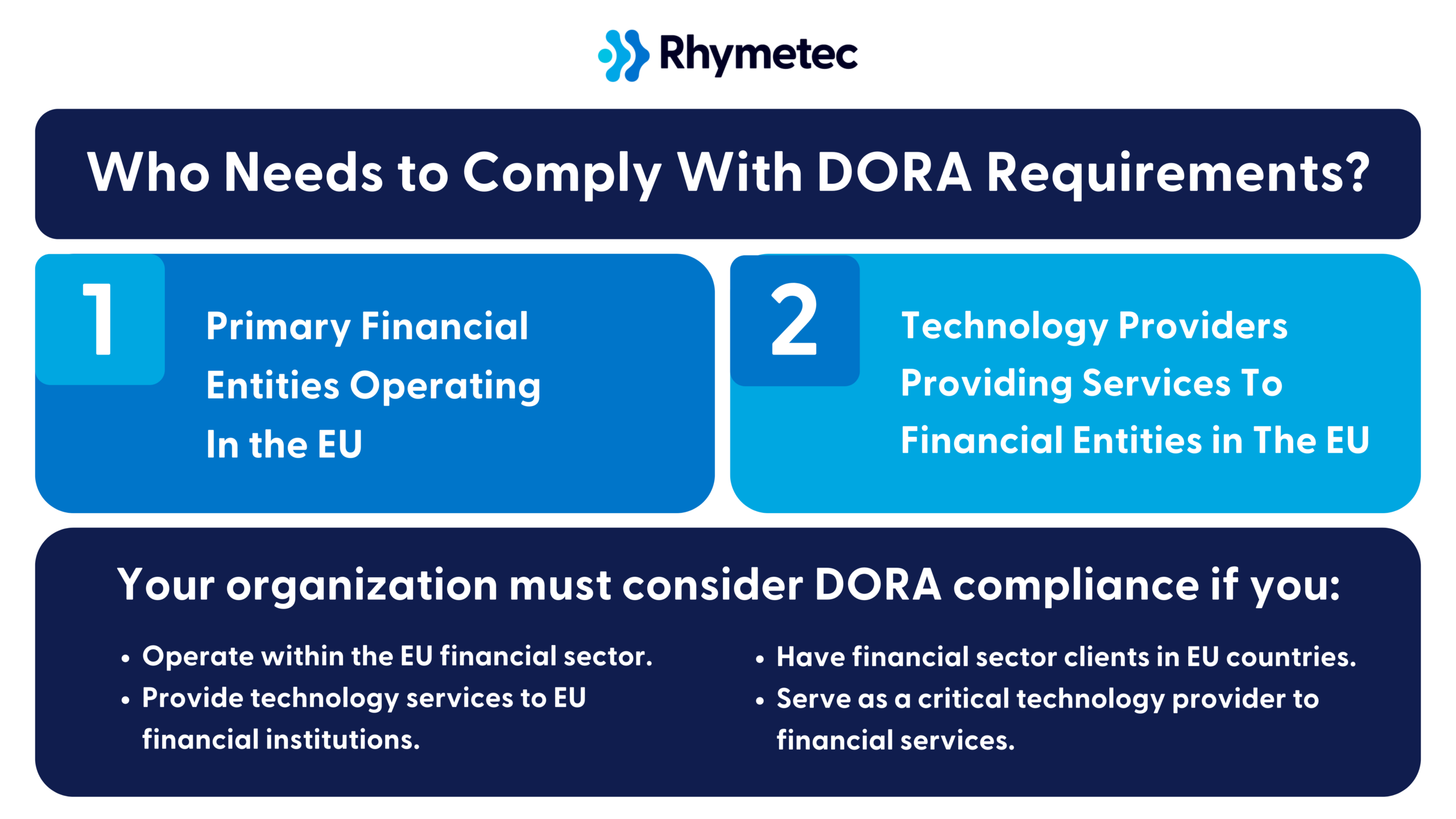
DORA's compliance requirements directly apply to the following categories of organizations:
1. Primary Financial Entities Operating In the EU:
- Banks and credit institutions
- Investment firms
- Insurance and reinsurance companies
- Payment and electronic money institutions
- Cryptocurrency exchanges and providers
- Crowdfunding service providers
2. Technology Providers Providing Services To Financial Entities in The EU:
- Cloud computing services that support financial institutions
- Datacenter providers
- Network information and communication technology services
- Software and hardware providers critical to financial services
- …and more.
Your organization must consider DORA compliance if you:
- Operate within the EU financial sector.
- Provide technology services to EU financial institutions.
- Have financial sector clients in EU countries.
- Serve as a critical technology provider to financial services.
If you are unsure if your organization needs to comply with DORA, or if you need help getting started, Rhymetec's DORA Compliance Services can assist you. Our experts are happy to answer any questions you may have - we've helped over 700 organizations fast-forward their security and compliance.
DORA Compliance Checklist: Core Requirements
Let's break down what DORA actually demands from your organization.
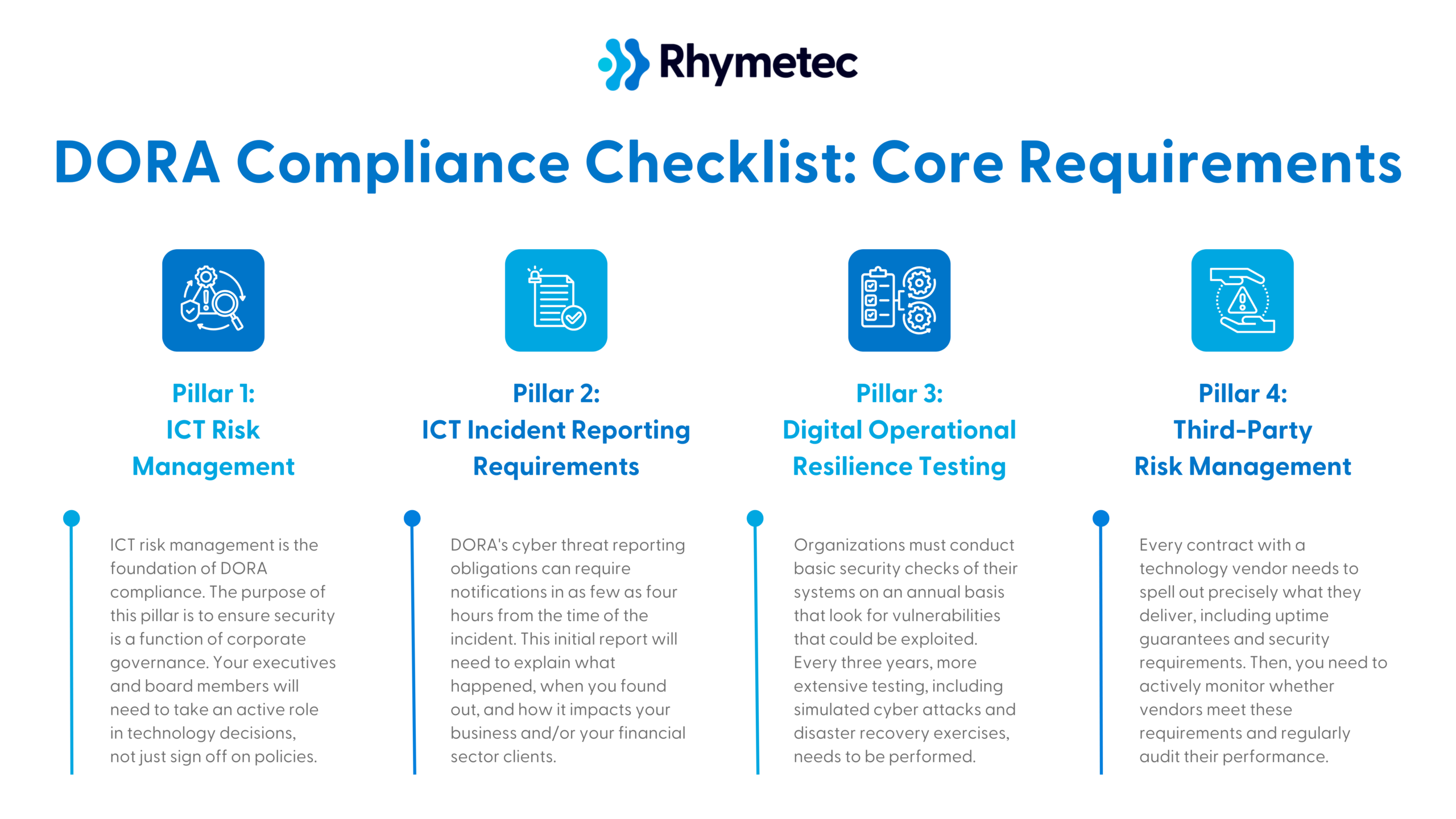
You'll need to oversee the implementation of four pillars, each of which carries specific obligations that will impact your operations differently depending on your organization's role in the financial ecosystem:
DORA Compliance Checklist Pillar 1: ICT Risk Management
Information and Communication Technology (ICT) risk management is the foundation of DORA compliance.
The purpose of this pillar is to ensure security is a function of corporate governance. Your executives and board members will need to take an active role in technology decisions, not just sign off on policies.
The following action items are requirements under this pillar:
Establish a governance framework for ICT risk management:
- Define who within your organization is responsible for ICT risk management at the executive level, and set policies to formalize accountability and integrate ICT risk into overall risk management.
- For example, you might appoint a security officer responsible for reporting ICT risks to the board.
Create policies and procedures for ICT risk identification.
- These policies should outline how you will identify threats, protect systems, detect incidents, respond to attacks, and recover.
- Tip: Align these policies with other industry standards like ISO 27001 or NIST. If you already have one of these frameworks, this can make things a lot easier!
Conduct regular risk assessments for ICT-related threats.
- DORA requires that you regularly evaluate risks to your digital systems and data. This includes assessing vulnerabilities, potential attack vectors, and business impact.
- Example: A financial services firm might decide to run quarterly assessments to identify weaknesses in its cloud storage security to meet this requirement.
Implement security measures (if you do not already have them in place).
- Security measures under DORA requirements include encryption, multi-factor authentication, and network segmentation. For a full list of these measures, reference the official DORA text.
- A backup and recovery plan for ICT disruptions is also required, as is monitoring ICT systems for anomalies and potential threats. This often takes the form of using monitoring tools and log analysis.
Lastly, employee training on security measures and ICT risk is required.
- Your staff must receive training in areas such as phishing, password security, and handling sensitive data.
DORA Compliance Checklist Pillar 2: ICT Incident Reporting Requirements
If you experience a system outage, data breach, or security incident, DORA sets strict rules about reporting the incident. DORA's cyber threat reporting obligations, for example, can require notifications in as few as four hours from the time of the incident. This initial report will need to explain what happened, when you found out, and how it impacts your business and/or your financial sector clients.
Requirements in this step include:
Develop an internal reporting mechanism for incidents, and figure out how you will identify and classify ICT-related incidents.
- ICT incidents under DORA are classified based on severity, and your response should be designed to match the severity of the incident. For example, a trading platform might classify a Distributed Denial-of-Service (DDoS) Attack as a high-severity incident requiring an immediate response.
- Establish policies for reporting major ICT-related incidents to the appropriate authorities within the required timeframe. Regulatory bodies need to be notified in the case of significant disruptions or cyberattacks.
Document and analyze incidents to improve processes and prevent recurrence.
- Every incident has to be logged, reviewed, and analyzed to improve security measures.
- After an incident, you should have policies in place to dictate how you will communicate incident impacts and remediation efforts to stakeholders.
DORA Compliance Checklist Pillar 3: Digital Operational Resilience Testing
DORA requires regularly testing your technology systems to ensure they can withstand problems and cyber attacks.
Organizations must conduct basic security checks of their systems on an annual basis that look for vulnerabilities that could be exploited. Every three years, more extensive testing, including simulated cyber attacks and disaster recovery exercises, needs to be performed.
Some organizations that fall under even more stringent DORA requirements (due to how pivotal they are to the financial sector) may need to go a step further and hire external security experts to conduct a penetration test. A penetration test is a good idea for all organizations, however, as it is the gold standard way to test your defenses in real-world situations.
In general, the requirements under this pillar are:
Conduct periodic testing of ICT systems, and perform penetration testing.
- Testing your security defenses against common threats like phishing and malware is required under DORA.
- Penetration testing is the industry-standard way to test your defenses!
Based on the results of your testing, develop remediation plans.
- For example, a company may find they need to update their firewall rules and disable unused ports after a penetration tester exposes vulnerabilities in their network.
Document testing outcomes and improvement measures.
- Under DORA requirements, organizations must maintain records of all testing activities, findings, and corrective actions.
DORA Compliance Checklist Pillar 4: Third-Party Risk Management
Lastly, your responsibility under DORA requirements extends to any vendors you rely on to serve your financial sector clients.
Every contract with a technology vendor needs to spell out precisely what they deliver, including uptime guarantees and security requirements. Then, you need to actively monitor whether vendors meet these requirements and regularly audit their performance.
DORA also requires that you plan for vendor failures, and demonstrate how you would switch to a different vendor if needed. One of the goals of this pillar is to help manage vendor concentration risk - organizations shouldn't rely too heavily on any single vendor.
Requirements include:
Create an inventory of ICT third-party providers.
- You'll need to document all of your vendors that provide ICT-related services. This can include the SaaS platforms you use, for example.
- Assign each vendor a risk level.
Carry out risk assessments for third-party ICT services.
- DORA requires you to evaluate the security posture of your vendors before and during the relationship.
- For instance, require your vendors to complete a security questionnaire or share their SOC 2 report.
Establish contractual agreements that define security and resilience expectations.
- Contracts should include cybersecurity requirements, incident response obligations, and compliance expectations relevant to your industry. For example, a payment processor might require its vendors to meet PCI DSS requirements.
Monitor third-party compliance with ICT risk requirements.
- Ongoing oversight of vendors' security practices is required. For example, you could conduct annual reviews of your cloud provider's security controls.
Develop exit strategies for critical third-party dependencies.
- Businesses must plan ahead for vendor disruptions, by having alternative providers or internal solutions ready.
DORA Compliance Checklist Timelines: 6-9 Months Total On Average; 4-6 Months Total With Rhymetec
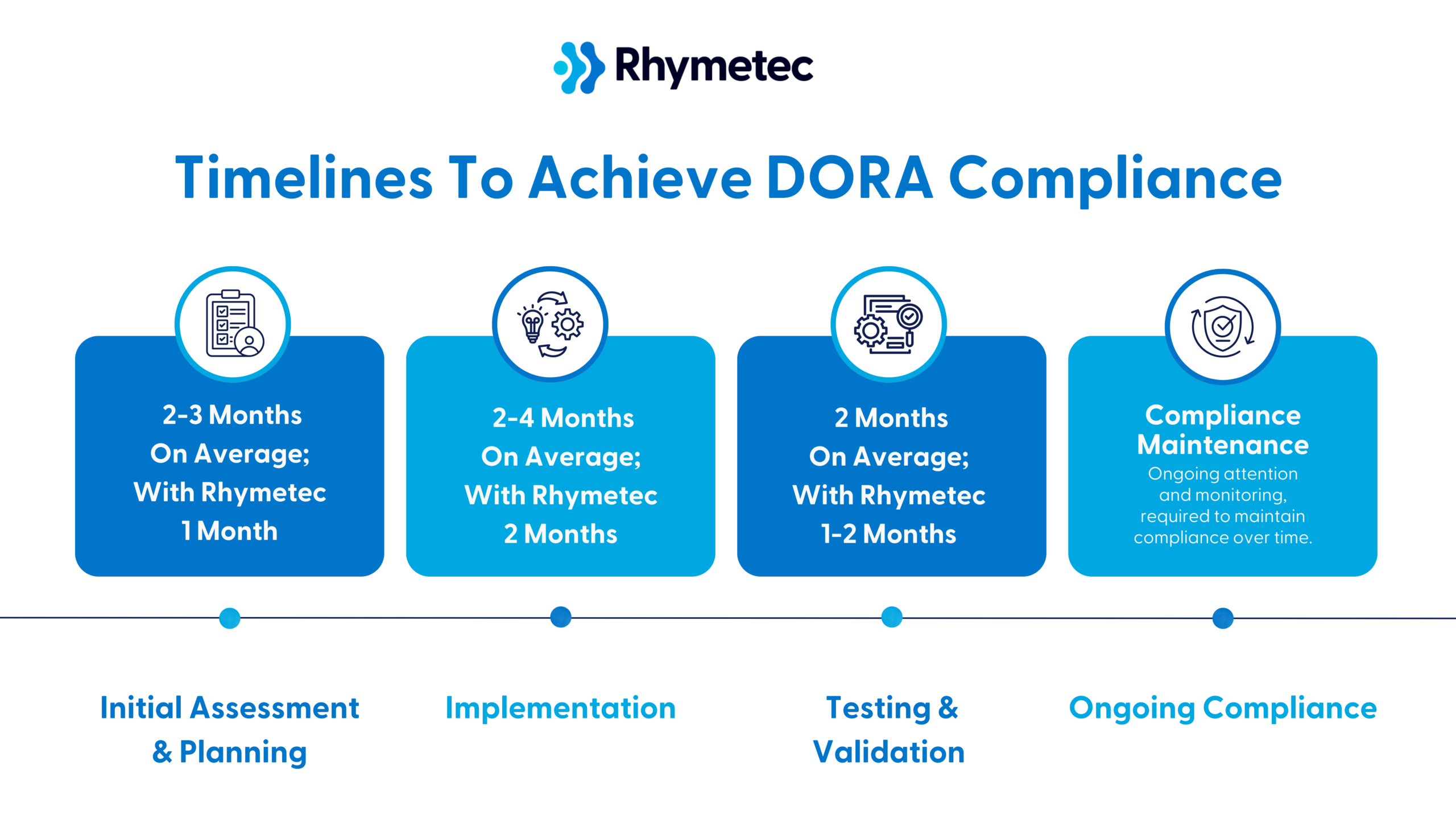
Below is a roadmap with timelines to give you an idea of what you can expect. Although these steps may vary depending on your organization's individual factors and needs, this should give you a general idea of what to plan for:
Initial Assessment and Planning (2-3 Months On Average; With Rhymetec 1 Month)
The first step is to understand where your organization stands in relation to DORA requirements. To do this:
- Bring in personnel from IT, security, legal, and business operations in order to understand the roles and impact across your entire organization. If you're a SaaS provider, include project managers who understand your technology stack and business leaders who manage financial sector relationships.
- Conduct a gap analysis, assessing where you currently are versus where you need to be to meet DORA requirements.
- Create an inventory of technology assets that support financial sector services (also known as mapping your ICT assets). You'll need to document every server, database, API, and third-party system you use.
After you have a clear understanding of your gaps, the next step is to develop a detailed implementation plan and allocate resources accordingly. Calculate costs for new tools, additional staff, training programs, and possible consulting help. Include both one-time costs (such as new monitoring systems) and ongoing expenses (such as additional security staff or regular testing).
Implementation (2-4 Months On Average; With Rhymetec 2 Months)
Now comes the actual work of building your compliance program:
- Update your documentation. Create or revise policies and procedures to meet DORA requirements, including incident response plans, business continuity procedures, and vendor management policies.
- Make your policies practical: Your incident response plan, for example, should include actual contact information and clear steps.
- Implement new controls. Deploy new security measures, as outlined by DORA requirements, and any monitoring tools or testing procedures you need.
- Update vendor management. You'll likely need to review and update contracts with critical service providers and add requirements for things like incident reporting and service levels.
Testing and Validation (2 Months On Average; With Rhymetec 1-2 Months)
Before finally achieving compliance, testing and validating your new controls is important. To do this:
- Conduct trial runs that allow you to practice your incident response procedures with realistic scenarios. The industry standard way to accomplish this is with a tabletop exercise, where your team works through a fictional but realistic scenario, such as what you would do in the event of a ransomware attack.
- Verify you can meet your recovery time objectives. Test scenarios where you'd need to switch between backup systems or alternative providers, document any gaps you find, and adjust your procedures accordingly based on what you find.
- Have legal and compliance experts review your documentation to make sure it will hold up under regulatory scrutiny.
Ongoing Compliance (Continuous)
Compliance requires ongoing attention and monitoring.
Organizations that are serious about maintaining compliance should schedule regular reviews of their compliance program, such as on a quarterly basis. This is important because changes in your business or technology impact your DORA obligations.
Monitor metrics about system performance, incident response times, and vendor service levels to spot potential issues before they impact your compliance.
Lastly, use lessons learned from any incidents that occur to continually improve your procedures, and stay informed about any changes in regulatory best practices and guidance.
Business Benefits of DORA Compliance
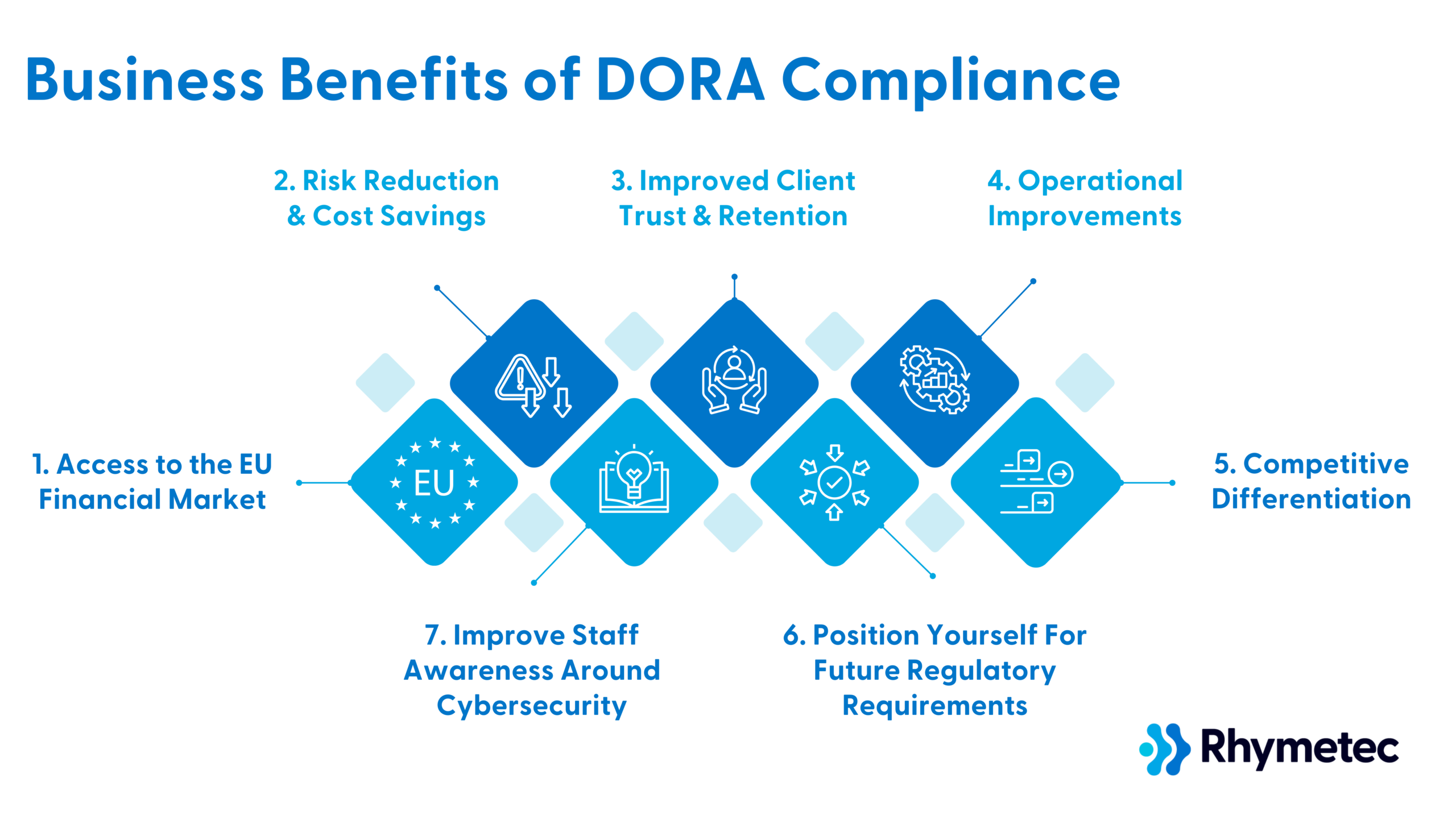
While DORA requirements may seem daunting, organizations that embrace these changes stand to gain significant competitive advantages in the European market. Complying with DORA offers substantial business advantages that extend far beyond regulatory adherence.
Here's how meeting DORA requirements strengthens your market position and creates new opportunities for your business:
1. Access to the EU Financial Market
By meeting DORA requirements, you gain the ability to serve financial institutions across the European Union.
Banks, insurance companies, and investment firms must work with DORA-compliant technology providers. Your non-compliant competitors get excluded from EU financial sector opportunities, while you can expand your market reach. This creates a clear competitive advantage.
For example, a small cloud storage provider that achieves DORA compliance can compete for contracts with major EU banks, opening up revenue streams that were previously inaccessible. Without compliance, they'd be limited to serving non-financial clients or risking their potential EU financial clients selecting compliant competitors.
2. Risk Reduction and Cost Savings
The approach to risk management under DORA is intended to help prevent costly incidents before they occur. While it may seem like a costly upfront investment to implement security controls, it costs far less than recovering from major technology failures or cyber-attacks.
For example, DORA-style monitoring enables companies to discover and fix potential system failure points before they can lead to massive revenue loss and reputational damage.
The time and money spent on monitoring and backup systems is an extremely wise investment compared to the potential losses and reputational damage a system failure could incur on many business's daily operations.
3. Improved Client Trust and Retention
Financial institutions face intense scrutiny over their technology providers. DORA compliance sends a strong signal to them that your company is committed to security and operational excellence, and will be less likely to cause them issues.
Compliance enables you to provide detailed evidence of your resilience measures, making it easier for financial clients to trust you with their operations.
It also serves to shorten sales cycles, as your team can readily demonstrate their security and reliability measures to prospective financial sector clients.
4. Operational Improvements
The rigorous testing that DORA requires can reveal opportunities to improve your operations.
Let's take a specific example to explain how:
A trading software provider implementing DORA's system mapping requirements could discover they're running redundant data validation checks across multiple different services.
By figuring this out, they can reduce their infrastructure costs while improving system performance. Without undergoing the compliance process, whether it be DORA or other regulations, issues like these may have never been discovered.
5. Competitive Differentiation
Achieving compliance with DORA sets you apart even in markets beyond the EU financial sector.
Take, for instance, a cloud database provider trying to compete for contracts with healthcare providers or government agencies. While DORA compliance isn't required for these sectors, the provider could leverage their DORA-compliant controls and processes to demonstrate their commitment to operational resilience, potentially helping win contracts over less rigorously controlled competitors.
Meeting DORA requirements provides an overall boost to your marketing and sales efforts as well. Your team can use compliance as a differentiator in marketing materials and sales meetings.
6. Position Yourself For Future Regulatory Requirements
Digital operational resilience only stands to become more important across all sectors. DORA-compliant organizations can get ahead of the curve and position themselves for future regulatory requirements.
Experts anticipate similar regulations to emerge in other regions and industries. DORA-compliant organizations may find themselves already 80% compliant with future regulations, saving significant time and resources compared to competitors who need to start from scratch.
By implementing DORA requirements now, you're preparing your business for future compliance needs while gaining all of the immediate security and operational benefits.
7. Improve Staff Awareness Around Cybersecurity
Implementing DORA requirements builds valuable expertise within your organization, at every level. Your team develops skills and know-how in risk management, incident response, and operational resilience that benefit all aspects of your business.
The value of DORA compliance lies not just in meeting regulatory requirements, but also in building a more resilient and competitive business. While the implementation process requires substantial effort and investment on your part, the resulting business benefits far outweigh the costs.
DORA Compliance Checklist: Cost Considerations
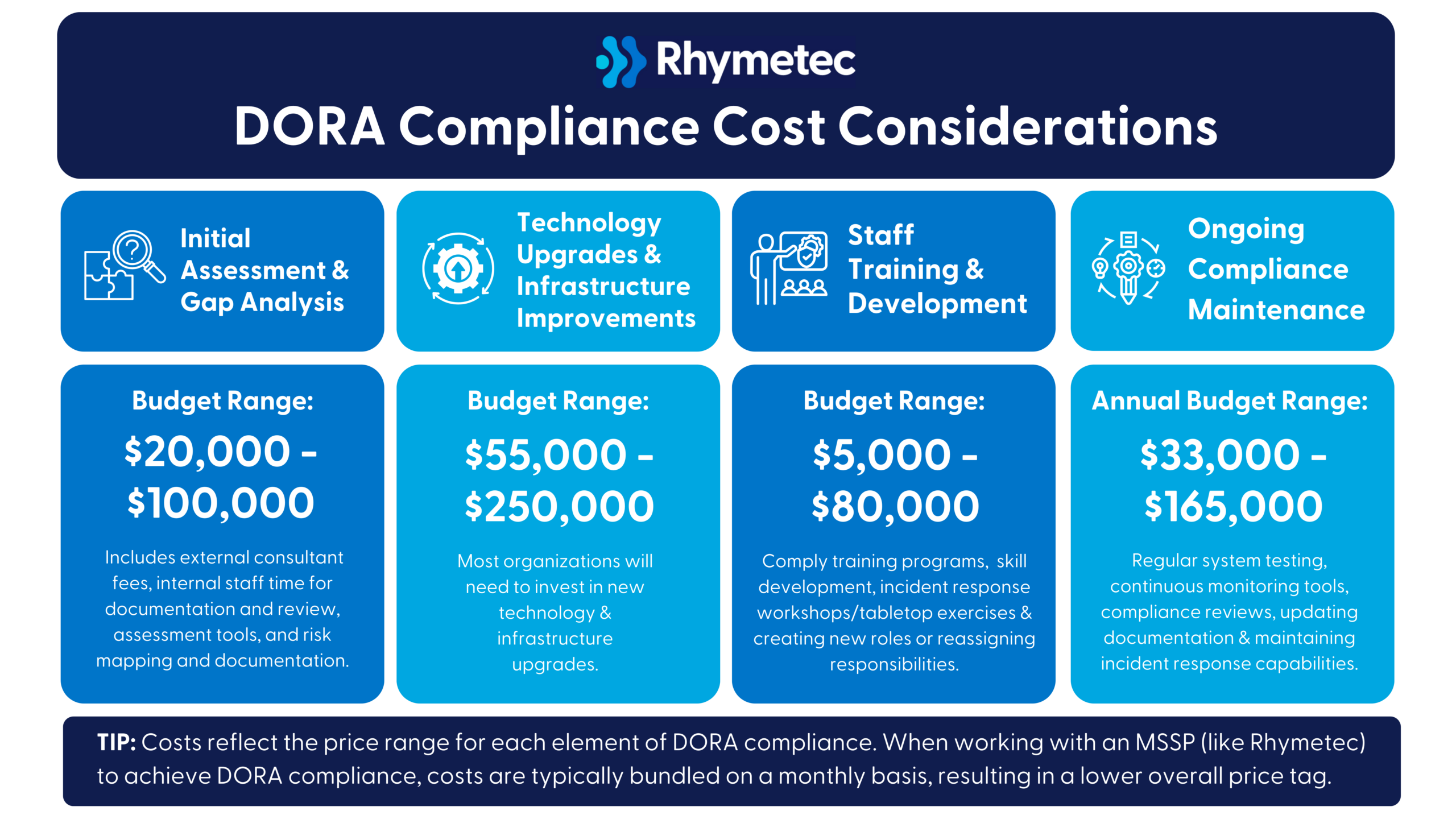
Costs to achieve DORA compliance will vary depending on your organization's size, complexity, and technology infrastructure. Here is an estimation of what you can anticipate:
Initial Assessment and Gap Analysis
Budget Range: $20,000 - $100,000
This includes external consultant fees, internal staff time for documentation and review, assessment tools, and risk mapping and documentation.
Technology Upgrades and Infrastructure Improvements
Budget Range: $55,000 - $250,000
Most organizations will need to invest in improved monitoring systems, incident response capabilities and technologies, security information and event management (SIEM) upgrades, additional backup and recovery infrastructure, and compliance tracking and reporting tools.
Staff Training and Development
Budget Range: $5,000 - $80,000
Investments include compliance training programs, cybersecurity skill development, incident response workshops/tabletop exercises, and creating new internal roles or reassigning responsibilities.
Ongoing Compliance Maintenance
Annual Budget Range: $33,000 - $165,000
Recurring annual costs include regular system testing, continuous monitoring tools, compliance reviews, updating documentation, and maintaining incident response capabilities.
Potential Hidden Costs of Fulfilling Your DORA Compliance Checklist
Potential hidden costs can include additional administrative overhead, needing to redesign existing processes, productivity loss during implementation, vendor management, and a possible temporary reduction in service delivery.
Cost Mitigation Strategies
Fortunately, there are a few things you can do it mitigate the impact of the cost associated with achieving DORA compliance:
- Start early to spread out implementation costs.
- Use a phased implementation approach and spread costs over multiple budget cycles.
- Use a compliance automation tool.
- Leverage a vCISO service to take the work off your plate entirely while receiving the highest level of service and expertise (to see costs associated with this option, check out our vCISO pricing blog).
DORA compliance is an investment in your organization's resilience and future competitiveness. While the upfront costs may seem hefty, they pale in comparison to potential losses from a major technology failure, cybersecurity incident, or regulatory non-compliance risks.
Practical Implementation Tips
Fortunately, you don't have to build everything from scratch to implement DORA requirements.
A compliance automation platform can significantly streamline the process by essentially enabling you to compile and document everything you already have. These tools enable you to automatically track your compliance progress, generate documentation, and alert you to potential gaps.
(For more information on exactly how the compliance automation process works, check out our blog post on this topic.)
Working with a virtual Chief Information Security Officer (vCISO) can also dramatically simplify your DORA compliance journey. A vCISO brings a wealth of experience in regulatory compliance and helps you avoid common pitfalls while accelerating your implementation timeline, all at a fraction of the cost of a full-time CISO.
By combining compliance automation tools with vCISO support, you can keep costs under control while meeting your DORA requirements in the fastest timeframe possible.
Additional Resources: Official EU Documentation
- Official Text of DORA - The full regulation text and requirements. This is the ultimate source of authority for any questions on specific requirements and should be referenced when there are questions about the interpretation of requirements or obligations.
- European Banking Authority (EBA) Guidelines - Technical standards and implementation guidance, as well as the latest updates on DORA implementation. The EBA's Q&A tool is an incredibly useful resource and can be used to answer common implementation questions.
- European Securities and Markets Authority (ESMA) - ESMA is one of the regulators responsible for overseeing DORA compliance. They provide updates and interpretations of DORA requirements.
In Conclusion: Get Started Today On Fulfilling Your DORA Compliance Checklist
DORA represents an opportunity to gain access to a lucrative segment of the EU marketplace, improve client trust, and strengthen your organization's operational resilience.
The most efficient way to begin your compliance journey is by engaging a virtual CISO (vCISO) who can conduct a gap assessment for you, leverage a compliance automation platform on your behalf, and guide your implementation while keeping costs manageable.
Our team at Rhymetec is happy to answer any questions you may have, and to walk you through how to tailor this DORA compliance checklist to your organization. Contact us today for more information.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with over 700 companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- CISO As a Service: A Scalable Security Solution
- Penetration Testing vs. Vulnerability Scanning: Key Differences
- NIS2 Requirements: What You Need To Know For Your Business
Meet Kyle!
Hi, I'm Kyle! I grew up in Dacula, Georgia which is about 45 minutes outside of Atlanta. My childhood mostly consisted of playing sports year-round while maintaining good study habits. After high school, I went to Kennesaw State University, where I majored in Psychology with a keen interest in human consciousness. During my freshman summer, I was fortunate enough to land a job as a systems administrator, and that’s where my tech career began.

Tell us a surprising fact about yourself…
I have over 1,000 books in my home library and some of them date back to the mid-1800s.
If you could have any superpower, what would it be?
If I could have a superpower, it would be the ability to manipulate time. This superpower is important to me because time is one of the fundamental substances of life. Being able to rewind, pause, and fast forward time would allow so many key benefits such as:
- Changing the things I regret (haha)
- Extra time for learning and personal development
- Preventing accidents or dangerous situations
- Experiencing more life
What are some things you enjoy doing outside of work?
Outside of work, I enjoy a variety of activities that help me unwind and explore my passions. Here are a few of my favorites:
- Outdoor Activities: I love spending time in nature, whether it’s hiking on local trails or running around the area. The fresh air and beautiful scenery are always refreshing!
- Writing: Writing is a significant passion of mine. I enjoy crafting stories, articles, or even journaling my thoughts and experiences. It allows me to express my creativity and communicate ideas effectively.
- Reading: I’m an avid reader and enjoy diving into different genres, especially psychology and personal development books. It’s a great way to escape and gain new perspectives.
- Fitness: Staying active is important to me, so I regularly go to the gym and do High-intensity interval training (HIIT) workouts. It helps me maintain a healthy lifestyle and boosts my mood.
- Technical Analysis: I have a keen interest in technical analysis, particularly in financial markets. I spend time analyzing charts and trends, which not only sharpens my analytical skills but also keeps me informed about global market dynamics.
Tell us about your role at Rhymetec…
I have been working at Rhymetec for a little more than 2 years and started as a Cloud Compliance Analyst.
Currently, as the Information Security Manager at Rhymetec, my role consists of the following responsibilities:
- Service, Quality Efficiency Improvements
- Internal and External Procedure Maintenance
- Security Team Management Support
- Security Team Training
I love working for Rhymetec because as someone who is addicted to growth, I am confident there’s not a better environment to reach your full potential as a cloud security professional. Also, I have always had a strong passion for the startup space and even invested in companies prior to starting at Rhymetec. Being involved with the companies that will become household names in the near future is extremely exciting.
Why did you pursue a career in the cybersecurity industry?
As a psychology major, cybersecurity was the last thing I imagined making a career. Though I worked in tech throughout college, I was confident that I would spend my working years as a relationship therapist and launch attachment nurseries around the globe. Then, I started to learn about cybersecurity in 2018, considering its upside potential and overall business value. It seemed more innovative to focus on securing the development of technology rather than focus on the insecurities that have developed within people.
I also have some natural attractions to cybersecurity as well such as:
- My passion for problem-solving
- The dynamic and ever-changing nature of the field
- The opportunity to protect people and organizations from threats
What is your favorite part about working at Rhymetec, or in the cybersecurity industry?
There's nothing more exciting than staying one step ahead of cybercriminals, protecting people's digital lives, and maintaining a strong reputation for the companies we protect.
The constant learning, the chance to use the technology of the future, and knowing that my work directly prevents cyber attacks make my career at Rhymetec incredibly rewarding.
What is your favorite quote or the best advice you have ever received?
I spent a lot of time reading Albert Einstein, who provides great insights and perspectives on all parts of life. One of the most impactful pieces of advice I encountered is his quote: “Strive not to be a man of success, but rather to be a man of value.”
This statement resonates deeply with me as it emphasizes the importance of contributing positively to the world rather than merely chasing accolades or material. In a society that often measures success by material, this perspective serves as a reminder that true fulfillment comes from making meaningful contributions.
From a security or compliance perspective, what advice would you give to a potential client or SaaS business?
When advising a potential client or SaaS business from a security or compliance perspective, I would emphasize the importance of adopting both a proactive and holistic approach to data protection and regulatory adherence. A reactive and narrow will always lead to a large-scale data breach and loss of customer trust.
At Rhymetec, we understand that a proactive and holistic security program involves implementing various controls across multiple security domains including, but not limited to, risk management, incident management, cryptography and access management. Additionally, staying informed about relevant regulations—such as GDPR, HIPAA, or DORA—and regularly ensuring that your practices align with these standards is essential for maintaining compliance and building trust with your clients.
Connect with Kyle Jones
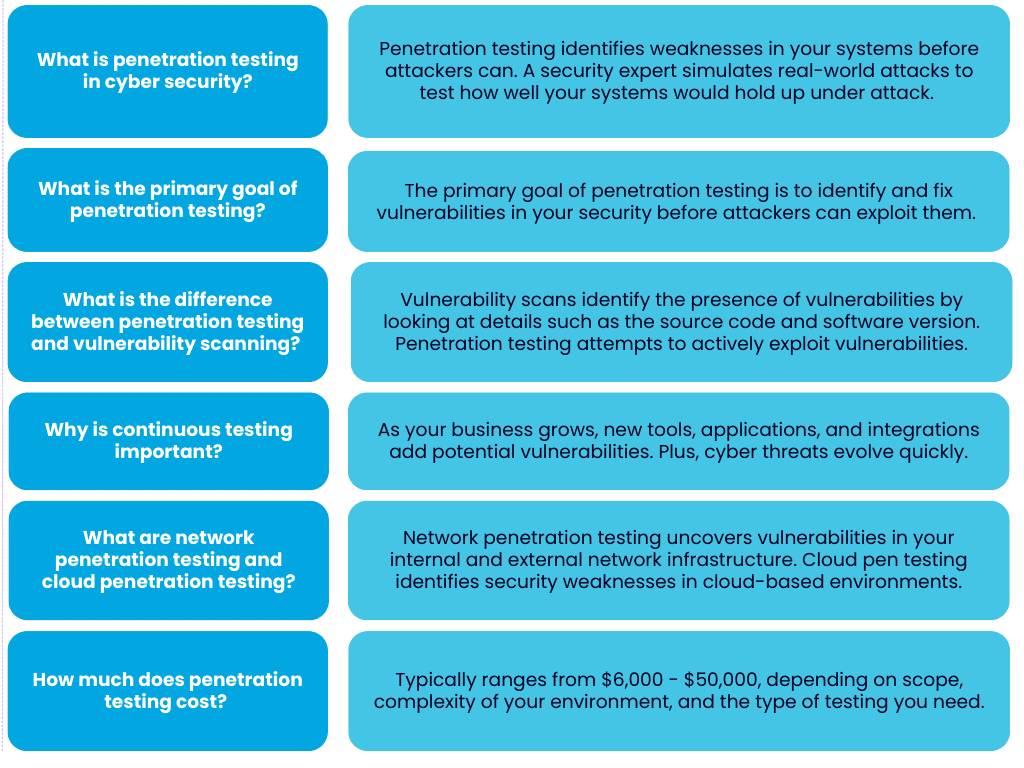
In this penetration testing FAQ, we go over the most common questions around penetration testing and its role in a modern security program.
According to IBM's annual report, in 2024, the average cost of a data breach reached $4.88 million globally, reflecting a 10% increase from 2023. This is the highest total ever and is projected to continue to increase.
The best way to protect yourself from financial, reputational, and other damages that can result from a data breach is to prevent attacks from happening in the first place.
This is the main goal of penetration testing. Penetration testing is one of the single most effective ways to reduce risk, as it is preventative rather than reactive. A penetration test finds weaknesses in your security before attackers do, thus taking the advantage away from bad actors.
This Rhymetec penetration testing FAQ explores key questions, including what penetration testing is, how it works, why it matters for organizations, how it compares to a vulnerability scan, and how much it can cost.

What is penetration testing in cyber security?
Penetration testing is a way to identify weaknesses in your systems before an attacker does:
During a penetration test, a security expert will simulate real-world attacks to test how well your systems would hold up if they were actually under attack. This allows them to pinpoint vulnerabilities that could allow a real attacker to gain unauthorized access and/or expose your sensitive data.
At the end of your penetration test, you'll have a clear picture of the gaps in your defenses.
You can think of a penetration test like hiring a professional to test the locks on your building's doors and windows, but the locks are your firewalls, applications, and networks. After uncovering your potential vulnerabilities, a good pen testing firm will also advise you on where to go from there and provide you with a roadmap to remediate gaps.
What is the primary goal of penetration testing?
The primary goal of penetration testing is to identify and fix vulnerabilities in your security before attackers can exploit them.
The process simulates how a real attacker may attempt to breach your defenses, providing you with insights to act on that are vastly more informative than results from automated scans or theoretical security risks.
After a penetration test, you'll have a clear list of vulnerabilities that need to be addressed, as well as an understanding of the risks these issues pose to your business.
Understanding the tangible impact these risks could have enables you to prioritize which vulnerabilities need to be remediated first. Being able to effectively prioritize risks and allocate resources accordingly (and within the constraints of budgets and resources) is another goal of penetration testing.

Example of Security and Compliance Risks Addressed by Penetration Testing
Let's take an example of a vulnerability that is frequently uncovered during a penetration test and its potential impact:
An overlooked patch could lead to financial loss, downtime, or even damage customer trust. By conducting a penetration test, you bring issues like this to light and can then prioritize actions that have the most significant impact.
In terms of risks of non-compliance, it's important to know that penetration testing is often a compliance requirement and is an industry-standard way to fulfill a range of controls. For SOC 2 compliance, for example, penetration testing can address the risk of unauthorized access to systems that process or store customer data.
Including a penetration test in your SOC 2 readiness assessment prepares you to show auditors that you've covered a range of requirements.
However, compliance alone shouldn't be the end goal! A good pen test helps you align security measures with the unique threats and challenges your business faces, creating a more resilient system overall as your business continues to grow.
Bonus Tip For Startups: Penetration testing can strengthen your position with investors. Demonstrating a commitment to cybersecurity via gold standard measures like penetration testing signals that your business is ready to handle risks that could impact revenue or reputation.
Additionally, as previously mentioned, penetration testing fulfills requirements under a vast range of both voluntary standards and legal requirements that investors may want to see, particularly if you're targeting enterprise clients.

What is the difference between penetration testing and vulnerability scanning?
Both penetration testing and vulnerability scanning should be cornerstones in your cybersecurity strategy.
However, it's important to understand the key differences between these two measures:
The key difference between penetration testing and vulnerability scanning is that vulnerability scans identify the presence of vulnerabilities by looking at details such as the source code and software version but do not attempt to exploit the vulnerabilities.
Penetration testing goes further. Ethical hackers attempt to exploit vulnerabilities to see if they could lead to a security incident. Penetration testing is significantly more robust than vulnerability scanning and allows you to identify the most critical real-world risks and focus your remediation efforts on them.
A vulnerability scan is a great first step for identifying surface-level issues and known vulnerabilities, while penetration testing gives you an understanding of how these issues could be exploited in practice, finds additional potential issues beyond what a vulnerability scan would uncover, and enables you to strategically prioritize remediation of your most pressing risks.
Bonus Tip: If your organization is looking for a firm to run vulnerability scans or conduct a penetration test for you, it's extremely important to understand the differences between penetration testing and vulnerability scanning.
Buyers of security services may encounter issues differentiating between these two measures as a result of technical jargon and a lack of transparency from vendors. Unfortunately, some vendors will claim to offer "penetration testing" that is really just vulnerability scanning and may not be suited to meet your security or compliance goals.
What are the differences between a manual and automated penetration test?
The main difference between manual and automated penetration testing is how vulnerabilities are discovered. What firms may refer to as "automated penetration testing" identifies potential vulnerabilities by scanning for known issues.
Although this is an effective way to discover vulnerabilities quickly, it limits the test to what is already documented in the vulnerability database and does not provide an idea of how these vulnerabilities could be exploited in a real-world scenario by a bad actor.
Zero-Day Attacks and Automated Penetration Testing
A major limitation of automated penetration testing is it cannot detect issues that could lead to zero-day attacks, a type of attack that exploits a vulnerability that is entirely unknown to the security community. Because these vulnerabilities have not been documented, they are some of the most dangerous threats organizations face.
Automated penetration testing relies on databases of known vulnerabilities, leaving a major gap in your security assessment if you rely solely on automated methods. Manual penetration testing is much more involved and remediates this issue by leveraging human expertise and creativity.
The Stuxnet attack is a notorious example of a sophisticated zero-day attack. This malware targeted Iran's nuclear facilities in 2010 and exploited multiple zero-day vulnerabilities in Windows systems and industrial control software. The attack was able to bypass traditional security measures because it exploited flaws that no one knew existed at the time.
While no test can accurately predict every possible zero-day vulnerability, manual penetration testing greatly reduces the risk by finding security gaps that automated tools miss.
Attackers Leverage Both Automated and Manual Tools
Attackers don't rely solely on automated tools, so neither should your penetration testing!
While automated tools can provide a baseline of security by revealing common issues, without manual testing, you risk overlooking a range of serious issues that could lead to a breach.
Manual testing is also more specific. The tester considers your specific business context, such as the value of your data, the risk associated with your technology stack, your risk appetite, and the tactics an attacker would be most likely to use against your organization.
Red Flags Indicating An Overly Automated Penetration Test
If your penetration test feels rushed, provides generic results, or lacks detailed explanations specific to your business, it may rely on heavily automated tools.
Additionally, if the timeline seems unusually short for the scope of work, or if the report lists vulnerabilities without contexts or recommendations, your provider may be running scans without performing the deeper analysis that manual testing entails.
You should always ask your provider about their process and request a scope of work. A reputable firm will explain how they combine automated tools with manual techniques, provide examples of past testing scenarios, and describe the skills and experience of their pen testers.
Why is it important to continuously conduct penetration testing for a strong security system?
Your systems and environments are not static.
As your business grows, new tools, applications, and integrations are introduced - each adding potential vulnerabilities. Cyber threats evolve just as quickly, with attackers developing new techniques to bypass existing defenses.
Continuous penetration testing helps you keep up with these changes and minimizes the likelihood of an unknown vulnerability turning into an incident.
Compliance requirements also often call for regular penetration testing, but compliance isn't the only reason you should be conducting pen testing. Regular penetration testing creates a process where risks are identified and addressed, rather than waiting and having to react to what could have been avoidable incidents.
For organizations like startups where change is constant, ongoing penetration testing helps you stay informed and ahead of threats as the threat landscape evolves.
Continuously conducting penetration testing protects sensitive data and reduces the overall cost of addressing vulnerabilities by catching them early while reassuring stakeholders and customers that security is a consistent priority for your business.
What is network penetration testing?
Network penetration testing uncovers vulnerabilities in your internal and external network infrastructure:
Internal networks include devices and systems within your organization, such as local file shares, servers, and employee workstations. External networks are the points where your systems interact with the internet, such as public-facing websites or VPN gateways.
A network penetration test mimics the actions of a hacker attempting to exploit weak points specifically in your network. For example, this could take the shape of testing firewalls to see if they're properly configured, identifying open ports that could allow unauthorized access, or determining if you have any outdated protocols leaving your systems exposed.
Bonus Tip: Network penetration testing is particularly relevant as remote work and cloud adoption expand! These trends increase the complexity of network environments and expand your attack surface. Regular network testing helps you maintain visibility and control over your infrastructure and minimizes the risk of unauthorized access or disruption.

What is cloud penetration testing?
Cloud penetration testing identifies security weaknesses in cloud-based environments by testing the security of APIs, the configuration of your cloud infrastructure, how access controls are managed, and more.
An example of a common issue in cloud environments that cloud penetration testing often reveals the presence of is misconfigured storage. Sensitive data can be easily left exposed to the internet if storage is misconfigured.
Another example is overly permissive access controls that allow unauthorized users to interact with resources they should not have access to. Cloud penetration testing simulates attacks to help you find and remediate these risks, among others.
Bonus Tip: Cloud security is often a shared responsibility with your cloud provider. While providers like AWS or Azure manage the security of the underlying infrastructure, you are responsible for securing how you use their services. A penetration test helps you verify that your configurations align with both security best practices and your business needs.
How much does penetration testing cost?
The cost of a penetration test depends on the scope of the test, the size and complexity of your environment, and the type of testing you need.
For smaller organizations with a relatively straightforward network or a single application, a test may range from a few thousand to several thousand dollars. Larger organizations with more complex systems can anticipate higher costs due to the amount of time and resources required.
Specialized tests, such as those targeting cloud environments, APIs, or compliance requirements, may also carry a heavier price tag. A basic external test that focuses on your public-facing systems will generally cost less than a more comprehensive internal test that examines your entire network.
While penetration testing is an investment, it helps reduce the potential costs of a breach, which can include lost revenue, damaged reputation, and non-compliance issues. Understanding and remediating your risks early on can save your business substantially in the long run. Hopefully this penetration testing FAQ provided a solid idea of the cost-benefit analysis of investing in pen testing for your organization.
Penetration Testing FAQ:
In Conclusion: Penetration Testing FAQ
We hope this penetration testing FAQ provided helpful information and gave you a deeper understanding of penetration testing and what to look for when assessing vendors.
If you have further questions, our experts at Rhymetec are happy to help. We offer a range of penetration testing services, including:
- API Penetration Testing
- External Network Penetration Testing
- Mobile Application Penetration Testing
- Web Application Penetration Testing
Contact us today to learn more.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.
The future of cybersecurity remains a constant concern for security professionals and organizational leaders. Even if the organization is protected now, what new threats and events could derail the organization in a few days, weeks, or months? After all, the rapid advancement of technology also means a rapid advancement of vulnerabilities.
There is no crystal ball to forecast the future; however, organizations can make informed predictions about cybersecurity in the coming year. There are several trends that will likely shape the cyberlandscape in 2025, and organizations looking to stay ahead of the curve should prepare accordingly.
More Sophisticated Ransomware
Since up to 20% of all breaches are ransomware attacks, this security challenge has been a prevalent risk for over a decade, and its threat potential stands to become even greater in the near future. There are now more than 150 ransomware families, showing that this attack vector is proliferating and increasing in sophistication.
Moreover, artificial intelligence (AI) is fueling this growth, making ransomware increasingly complex and more difficult to detect—which also means it is more dangerous. Previously, malware scanners had proven quite effective in detecting ransomware, but their effectiveness is decreasing as technology evolves.
What can organizations do about this? First, they must rethink how they detect ransomware. Organizations may need to augment their existing tools and bring in newer, AI-fueled systems to identify and thwart more sophisticated threats. Second, invest in employee training, specifically around phishing attacks, as these are still the primary vehicle for ransomware deployment.
To this end, the most effective training involves providing phishing simulations and phishing material to educate employees on how to spot the phish in the future. The next step is to wait for an employee to fall for a phishing email and/or input their credentials into a phishing website (and they will). At that point, they should be given immediate security awareness guidance on what phishing is and how to avoid phishing attempts in the future. Responding at the moment they fell prey to the attempt is key to raising awareness and preventing similar scenarios in the future.
More Security Needed for the Cloud
According to G2, 85% of organizations will be “cloud first” by 2025. While this is exciting news for our digital-centric society, the downside is that cloud adoption has moved faster than cloud security measures have.
With many organizations moving to remote or hybrid environments, employees have gone from using IT-configured devices on the office premises to using remote devices nearly anywhere and everywhere. This, naturally, makes the organizations with a remote and/or hybrid workforce must focus on implementing robust cloud security frameworks. Two examples include Zero Trust Architecture, which assumes no user or device is trusted by default, and Cloud Security Posture Management (CSPM), which consists of continuously monitoring cloud infrastructure to identify and remediate security risk and misconfigurations. Employee education and clear policies about cloud usage are as crucial as ever, along with implementing tools meant for cloud environments.
AI Continues to Change Cybersecurity
Cybercriminals use AI technology to create more elaborate hacking tools, while cybersecurity professionals rely on it to develop better threat detection systems and predict future attacks. The debate over whether AI has helped or hurt cybersecurity efforts continues, but its impact is undeniable. In truth, it has become even more of a complex issue because both sides of the equation are embracing it. As 2025 approaches, both protectors and attackers will continue to turn to AI to outsmart one another.
Outside of the threat and defense landscape, AI governance also plays a critical role. While the International Organization for Standardization (ISO) and International Electrotechnical Commission (IEC), ISO/IEC 42001:2023 Information technology — Artificial intelligence — Management system standard represents progress in establishing governance and responsible management of AI systems, it alone is insufficient. Organizations must implement additional safeguards and strategies to protect their AI operations fully.
The organizations that will fare the best will implement AI-enhanced security tools, such as AI-powered threat detection, automated compliance monitoring, and/or behavioral analytics. Staying on top of regulatory developments and compliance is also of critical importance.
Cyberwarfare in Upcoming Elections
In the digital environment, cyberwarfare has become the new norm in elections, with hackers attempting to manipulate outcomes and spread misinformation. Given the high-profile elections regularly occurring around the world, cybercriminals are expected to target political campaigns and critical infrastructure.
As is usually the case, an ounce of prevention is worth a pound of cure. Organizations and governments alike should plan for a spike in attacks leading up to important elections, taking the time now to proactively secure crucial systems and implement plans to combat misinformation campaigns.
Retain and Attract Cybersecurity Experts
Half of cybersecurity professionals expect that they will burnout in the next 12 months due to the stress and pressures of their jobs. Professionals in the field suffer from burnout after facing unprecedented pressure and being held accountable for breaches. Given the already existing talent gap, this is nothing short of a crisis.
To retain their seasoned cybersecurity specialists, organizations must avoid personally blaming chief information security officers (CISOs) for cyberattacks. Even though the individuals in this role oversee the organization's security measures, and are the most visible in this department, they should not be personally held responsible for breaches. This often happens due to a lack of understanding of cybersecurity, and the natural human desire to find someone or something to blame for a problem. But these situations are usually highly complex and the only outcome from pinning an attack on a CISO is that they will be more likely to burn out and/or leave the organization.
Along the same lines, an organization's security team is the backbone of the enterprise and should be supported well, especially those in high-stress roles. As such, organizations should provide mechanisms to support and appreciate security teams, ensuring scheduled breaks, and distributing employee workload. This should be done while also recognizing their achievements. Organizations can enhance their security teams' effectiveness by investing in robust security measures, even when the return on investment is not immediately apparent. This commitment demonstrates a dedication to setting everyone up for success by equipping both the organization and its security department with the best tools available.
Last, reconsider how to educate and certify cybersecurity experts. For example, the Certified Information Systems Security Professional (CISSP) certification is still often used but is based on technology from the early 2000s. Instead, certifications should be relevant to today’s cybersecurity landscape, and the industry needs to reflect this. For instance, certifications from CompTIA, the Criminal Justice Information Services (CJIS) certification from the United States Federal Bureau of Investigation (FBI), and the Certified Ethical Hacker (CEH) are all highly respected and applicable today.
Looking Ahead
In 2025, organizations can look forward to many technological advancements. But these advancements will come with more ransomware, AI on both the attacker and defender sides of security, cyberwarfare, employee shortages, and more. As such, organizations must be vigilant and more proactive than ever in investing in security measures and putting safeguards first.
About The Author: Justin Rende, CEO
Justin Rende is the founder and CEO of Rhymetec, a cybersecurity firm providing cybersecurity, compliance, and data privacy needs to SaaS companies. With more than 20 years of experience in cybersecurity, Rende has focused exclusively on developing the most innovative and customizable cybersecurity solutions for modern SaaS-based companies.
You can read the original article posted in ISACA by Rhymetec CEO, Justin Rende.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.
Artificial intelligence (AI) is increasingly shaping cybersecurity. While it brings opportunities, it also raises concerns. For chief information security officers (CISOs), understanding AI can mean the difference between turning it into a valuable asset or fearing it as a threat.
Here's how you can make AI a trusted ally in your operations by implementing actionable strategies for safe and effective use.
AI in Cybersecurity—Friend or Foe?
AI can be both a friend and a foe in cybersecurity. One primary concern for CISOs is privacy. When employees use AI without proper training, sensitive information might be exposed. According to IBM's 2024 Cost of a Data Breach report, 57% of IT professionals surveyed cited data privacy as a leading barrier to implementing generative AI models.
Another risk is that attackers will use AI to create sophisticated threats, making it a double-edged sword. There are also fears about AI replacing jobs, but this is not necessarily true. When effectively managed, AI helps automate repetitive tasks and enhances security efficiency. The key lies in using AI ethically, and proactively managing its risks.
Prerequisites for Embracing AI Safely
Before embracing AI, CISOs must ensure foundational protections are in place. Preventative measures like data privacy controls and intrusion detection systems are essential for preventing worst-case scenarios.
Training is another essential piece. Employees need to be well-informed about how to use AI tools correctly—particularly generative AI tools such as chatbots, which could be used carelessly to expose sensitive data. Training should focus on what information can and cannot be shared with AI systems.
In addition, aligning with established frameworks like ISO 42001 or the NIST AI Standards provides CISOs with clear guidelines. Aligning with these standards helps reduce incidents by 30%, according to the NIST 2023 AI Security Report, enabling a safe environment for integrating AI and setting up controls that reduce risks and foster trust.
AI as a "Force Multiplier" for CiSOS
AI can be a powerful "force multiplier" for security teams. AI-based threat detection reduces incident response times by up to 50%, allowing CISOs to detect threats early on and respond more quickly. When used correctly, it significantly increases efficiency. One of the key advantages of AI is its ability to perform log analysis and threat detection. It can sort through massive amounts of data that would be impossible for human teams to analyze manually.
AI also assists employees directly. AI-driven tools answer policy questions, saving time and boosting internal training effectiveness. This doesn't reduce jobs, but instead shifts the focus to strategic activities that add value.
How to Deploy AI with Human Oversight and Accountability
Human oversight is essential when integrating AI into cybersecurity. Teams must conduct random checks on AI's outputs to identify biases and inaccuracies, ensuring AI aligns with organizational goals. Accountability also needs to be well-defined. Even though AI plays a role in decision-making, humans are still ultimately responsible. CISOs should assign accountability to specific teams or individuals who oversee AI deployments to ensure that the organization has a clear plan for dealing with any mistakes or misuse of AI systems.
Continuous AI Improvement in Cybersecurity
Continuous improvement is necessary to keep AI effective. Training exercises like phishing simulations help employees stay vigilant. Developers should receive specialized training on building ethical AI systems, including AI System Impact Assessments to gauge the societal impact of technologies. AI tools also need regular evaluation for biases and effectiveness to ensure they meet evolving organizational needs.
AI Limitations in Cybersecurity
Despite all the benefits, AI has its limitations in cybersecurity. AI depends heavily on the quality of its training data, so its decisions will reflect those weaknesses if the data it is trained on is incomplete or biased. It's also not yet capable of handling every kind of security scenario; many tasks still require human intuition and understanding.
AI is simply a tool that does what it's trained to do. It lacks the ability to think critically or understand nuance. Because of this, CISOs must be realistic about what AI can achieve and ensure that it is always paired with human oversight to fill in the gaps where AI falls short.
Actionable Tips to Integrate AI without Fear
For CISOs looking to integrate AI into their security operations without the fear of unintended consequences, it's best to start small. Begin with low-risk processes like automated log analysis and build from there. Collaboration is also key; work with AI experts to choose and implement the best tools suited to the organization's needs.
Before scaling up AI usage, conduct internal audits and gap analysis to understand any weak spots. This helps prepare the organization for full AI integration while ensuring all necessary security controls are already in place.
Making AI your Best Friend
When adopted thoughtfully and carefully, AI can transform cybersecurity operations, making them more efficient and effective. CISOs should start with small steps, focusing on robust training, human oversight, and incremental adoption. AI doesn't need to be feared—it needs to be understood and managed. With proper safeguards, AI can be a powerful ally in keeping organizations safe from cyber threats.
You can read the original article posted in Fast Company by Rhymetec CISO, Metin Kortak.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.
Did you know that most data leaks and vulnerabilities don't stem from highly sophisticated hackers exploiting zero-day vulnerabilities, but rather from simple misconfigurations and poor access controls?
It's no secret that cloud environments are complex - actually, "incredibly complex" might be a better description. It's also well known that people are prone to errors. Sometimes these are as simple as misplacing keys; other times, they involve your cloud admin making their password "admin" and leading to a major breach.
You might be thinking, "My team is experienced and highly competent; there's no way we'd make such basic mistakes."
Well, cloud penetration testing lets you put that belief to the test.
A cloud penetration test is conceptually similar to a traditional network penetration test: A white hat hacker attempts to breach your cloud environment while documenting the vulnerabilities and misconfigurations they exploit to gain access. Cloud penetration testing applies this same framework to cloud environments.

What Exactly Is Cloud Penetration Testing?
Cloud penetration testing involves an outside party (usually a specialized security provider like Rhymetec) taking on the role of a threat actor attempting to gain access to your cloud environment. How the firm or individual gains access can include many forms, such as:
- Configuration analysis - Examining network access controls and service configurations for vulnerabilities.
- Identity federation testing - Examining cross-account access, third-party integrations, and federation configurations.
- Storage assessment - Checking for improperly secured storage buckets, publicly accessible data, and inadequate encryption.
- Identity and Access Management (IAM) exploitation - Testing for overly permissive roles, misconfigured policies, and compromised credentials.
- API security testing - Probing API endpoints for vulnerabilities, authentication bypasses, and authorization flaws.
- Container security evaluation - Analyzing container configurations, image vulnerabilities, and orchestration misconfigurations.
- Serverless function testing - Examining function permissions, runtime vulnerabilities, and dependency issues.
- Network security assessment - Testing VPC configurations, firewall rules, and network segmentation.
- Service-specific testing - Evaluating the security of managed services like databases, load balancers, and compute instances.
- Compliance validation - Ensuring cloud resources meet regulatory requirements and security standards.
A good cloud penetration testing company will spend the time to scope out the work with you prior to the engagement.
Working with a pen testing firm that takes the time to understand your organization's context and needs is critical. This is because penetration testing shouldn't be done in a vacuum - it's a small piece of a larger puzzle that creates effective risk mitigation for an organization.
Ideally, a cloud penetration test is aligned with an organization's risk assessment and broader security architecture to maximize the value that the pen test brings.
The Stages of a Cloud Penetration Testing Engagement
A cloud penetration testing firm begins with reconnaissance and planning, the foundation of any successful security assessment.
A pen testing team or individual takes the time to thoroughly map out your cloud infrastructure landscape. This entails listing assets, understanding how your cloud services interact, establishing clear boundaries for testing, and ensuring that the firm and client agree to a fixed set of rules of engagement.
Ideally, this should be closely aligned with your organization's risk assessment. If you don't have a formal risk assessment documented, ask questions like:
- What cloud infrastructure holds the most sensitive data?
- What would be the legal, reputation, and compliance risks if a certain system was breached?
- Which parts of cloud infrastructure contain the most essential elements required for business continuity?
- Has the cloud admin actually set his password as admin (ok we're slightly kidding with this one, but ensuring good password hygiene is a critical step!).
- What dependencies do core business functions have on various elements of the cloud infrastructure?
Next comes the discovery and enumeration phase.
This is where a pen testing firm actively probes your cloud environment, looking for exploitable vulnerabilities or other flaws in your cloud security. For example, a team will scan for public-facing assets, identifying potential entry points, and mapping the web of relationships between different cloud services.
The vulnerability assessment phase is where a security team actively begins attempting to gain access. This is where theory meets practice - the pen testing team is not just identifying potential vulnerabilities. At this stage, they're determining if they're actually exploitable.
A competent security team will dig deep into IAM roles and permissions, probe API endpoints, and examine storage configurations. It's like pressure testing every door and window in your digital house.
Then comes active exploitation. The pen testing firm will attempt to chain vulnerabilities together, gain access, move laterally, and escalate privileges. Think of it as stress-testing your security controls under real-world conditions. The team will document every successful path to build a map of potential vulnerabilities, misconfigurations, and weaknesses in your cloud security approach.
Post-exploitation explores the potential impact of any successful breaches. What sensitive data could the team access? How far could they move through the environment? What business-critical systems were within reach?
This phase often reveals the true business impact of technical vulnerabilities - turning technical findings into business risks that leadership can understand and act on.
Finally, we reach the documentation and reporting phase, where all these findings transform into actionable intelligence. This shouldn't be just a dry technical report, but rather, a roadmap for improving your security posture.
At Rhymetec, our team provides detailed vulnerability reports, clear exploitation paths, and prioritized remediation steps. Most importantly, we translate technical findings into business impact, helping everyone understand not just what we found, but why it matters.
Going Beyond MFA
Many organizations mistakenly believe that just because they have implemented multi-factor authentication (MFA) means that pen tests and deeper security measures aren't necessary. Unfortunately, this couldn't be further from the truth.
Security only works when organizations take a defense-in-depth approach - they layer security controls one on top of the other to mitigate as much as possible the risk of a breach of confidentiality, integrity, or availability of core IT systems. If a threat actor finds a stolen credential that works, you're back down to single-factor authentication.
2FA is also bypassable. Threat actors use stolen session cookies that result from malware infections and MFA fatigue attacks to bypass authenticator codes directly (or if the MFA is via SMS, they can use SIM swapping).
MFA is a fantastic first step and is a baseline cybersecurity measure for startups and other organizations. It should be an initial strong layer of security but not your be-all-end-all approach to ensuring the confidentiality, availability, and integrity of your cloud environment.
Choose Rhymetec For Your Cloud Penetration Test
Unfortunately, with today's highly commoditized cybercrime landscape, the question isn't whether your cloud environment will face attempted breaches - it's when. Whether you're running a startup with a simple cloud setup or managing a complex enterprise environment, the stakes have never been higher. Your customers trust you with their data, your employees rely on your systems, and your business depends on the integrity of your cloud infrastructure.
A Rhymetec pen test entails an intentional launching of simulated cyberattacks by our own penetration testers to access or exploit computer systems, networks, websites, and applications. Our pen testers will identify exploitable issues so that effective security controls can be implemented or will test the robustness of your current infosec program.
Our cloud penetration testing experts will work with you to develop and execute on a comprehensive penetration testing plan that puts your business in a position to defeat attackers and ensure the confidentiality, availability, and integrity of your cloud environment.
About Rhymetec
At Rhymetec, our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- 25 Cybersecurity Memes For 2025: The Ultimate List of Security and Compliance Memes
- Penetration Testing vs. Vulnerability Scanning: What Are The Differences?
- Compliance For Startups: The Definitive Guide to Picking The Right Consultant
Rhymetec Wraps Up 2024 with Major Milestones and a Continued Commitment to Cybersecurity Excellence
(NEW YORK — Dec. 10, 2024) –
/PRNewswire/ — Rhymetec, the industry leader in cloud security that provides innovative cybersecurity, compliance, and data privacy services to modern-day SaaS businesses, today announces significant milestones as it closes out a transformative year. Following 61% employee growth and the launch of an internship program in 2024, Rhymetec has further solidified its position as an industry leader through ongoing efforts to drive continuous improvement in services, build strategic partnerships, and maintain the highest standards of security and compliance for its clients.
“We’ve always believed that security and compliance are not ‘one-and-done’ efforts—they need to be integrated into the foundation of an organization’s operations,” said Justin Rende, founder and chief executive officer of Rhymetec. “In a market where many competitors offer solutions so companies can check the box of security, we remain true to our mission of delivering ongoing, sustainable compliance strategies and the highest security standards. As we look ahead to 2025, we’re dedicated to further progress, transparency, and partnerships that help our clients achieve long-term success and meet the evolving challenges of global regulations.”
This year, Rhymetec launched an internship program to cultivate cybersecurity’s next generation of talent. The company enjoyed celebrating its success throughout the year and strengthening its partnerships with key industry players during a company retreat in Cabo San Lucas. Representatives from Vanta and A-LIGN joined the retreat, where the teams discussed plans for further collaboration. In 2024 alone, Rhymetec solidified its partnerships with organizations like Johanson Group and Drata—becoming a Drata gold partner—and further developed partnerships with Picnic, A-LIGN, and BARR, to name a few.
“Johanson Group has been working with Rhymetec for five years,” said Ryan Johanson, partner at Johanson Group. “They have always done a fantastic job helping clients implement a GRC platform and getting them ready for audit. They are responsive to clients’ needs and insightful about the technology and compliance roadmaps. When we see a client working with Rhymetec, we know the client will be well prepared for the audit.”
In 2025, Rhymetec is preparing to introduce new frameworks and compliance offerings to address emerging global regulations, including DORA, NIS 2, and the EU AI Act. Additionally, the company plans to enhance its application security offerings, focusing on more proactive, offensive solutions.
To learn more about Rhymetec and its suite of cybersecurity services, please visit www.rhymetec.com.
About Rhymetec
Rhymetec is an industry leader in cloud security, providing innovative cybersecurity and data privacy services to the modern-day SaaS business. The company builds, deploys and manages compliant information security and data privacy programs directly within their customers’ unique environments, allowing them to focus on their core competencies within their business. Over the years, Rhymetec’s services have grown to include a vCISO (Virtual CISO) program, ISO Internal Audits, and a variety of Penetration Testing services. For more information, please visit www.rhymetec.com and follow us on Twitter or LinkedIn.
Read the original press release on PRNewswire.
To Learn More About Rhymetec's Services
To kick off the New Year, we've compiled 25 cybersecurity memes for 2025! Sharing these memes can help lighten the mood in the often stressful world of cybersecurity and reinforce important security concepts.
Check out our ultimate list of the best cybersecurity and compliance memes:
1. Cybersecurity Memes: The Small Business Dilemma

The hard truth is that cybersecurity is important regardless of organization size! In fact, small businesses are actually more likely to be targeted, precisely because they are small. Small businesses also need security policies, incident response plans, and much, much more.
2. The Regular Updating Scroll of Truth
We've all been there. It never feels like the right time to update, does it? It's so tempting to click "Remind me tomorrow" every day. But regular updates are one of the most basic and important things to do for security. However tempting it may be to keep putting it off:
3. Software Updates Cannot Be Ignored!
Regular updating enables known vulnerabilities to be patched. If vulnerabilities are not addressed, threat actors can exploit them. Plus, besides the obvious security benefits, updates also improve the performance and functionality of the applications you use every day. And that leads us to…
4. Don't Be This Surprised Pikachu
Failing to update software is like leaving the door wide open for cybercriminals. Known exploits can target unpatched systems, making you an easy target. Don't be this Pikachu - get proactive with your cybersecurity!
5. The Neverending Questionnaire
What better topic for cybersecurity memes than the infamous security questionnaire? We (or our GRC teams) have all been here:
6. The Friday Afternoon Security Questionnaire
Friday afternoons are for winding down, not being bombarded with a security questionnaire. Pro tip: Keep your documentation organized, and future-you will thank you!
7. When You Realize You Can Stop Filling Out So Many Security Questionnaires

That's right - the actual reason to get a SOC 2 report is to avoid filling out security questionnaires! (Just kidding, though, security also matters…)
8. Password Cybersecurity Memes

If you think this is an exaggeration, think again! Here are the top 10 passwords used in the United States:
- 123456
- 123456789
- 12345678
- password
- qwerty123
- qwerty1
- 111111
- 12345
- secret
- 123123
The top 200 feature a wide range of other variations of the word "password."
9. Hacker, or Bob From Accounting?
When logs show unusual activity, at first glance, it can seem like a toss-up: malicious actor or user error? Whether it's Bob from accounting or something more sinister, analyzing these events is critical.
10. And Definitely Don't Do This:
You could have the strongest password in the world, but if you use it across multiple accounts, it doesn't matter!
If just one site is compromised, attackers can easily gain access to your other accounts. Unique passwords create additional layers of security and make it harder for cybercriminals to exploit a single point of entry.
11. When You Put Your Cat's Name In Your Password
When your password is "Fluffy123"...Remember that your pet's name isn't as secure as you think. Use strong, unique passwords and leave Fluffy out of it.
12. Cybersecurity Memes: Penetration Testing
Penetration testing isn't just a checkbox for compliance. It should be conducted on a regular basis to identify vulnerabilities before attackers can exploit them. Don't wait for a breach to find out what's exposed! When shopping for pen testing vendors, look for teams that employ local talent and don't outsource their services.
13. Penetration Testing or Just a Vulnerability Scan?
Some vendors claim to offer "penetration testing" when, in reality, what they are really doing is vulnerability scanning. Make sure to know the differences between penetration testing vs. vulnerability scanning, so you know your pen testing vendor is doing what they say they are!
14. The Layers of Security: Defense in Depth
Good security means implementing many layers of defense. An example of defense-in-depth is access control on top of things like your firewall and intrusion detection to keep your assets safe. This is a standard security philosophy and strategy.
15. Rickrolling: The OG Phishing Simulation
If you learned how to not trust any links by being chronically online during your childhood, you're not alone. Rickrolling really did teach an entire generation to stop blindly clicking links. It didn't come with a training manual, but it worked. Can your phishing training say the same?
16. When Your Team Passes The Phishing Test Like Pros
Okay, maybe it was all the rickrolling they've encountered.
Or maybe it was your training program! Either way, it's a big win for security awareness. Phishing attacks are one of the most common threats, and getting your team to spot them is incredibly important.
As phishing attacks become even more sophisticated with the advent of AI, investing in phishing training for employees is something every single organization should be doing as a basic security measure nowadays.
17. A False Dichotomy? Compliance vs. Cybersecurity

Compliance: checking the boxes to get compliant ASAP.
Cybersecurity: so, so much more.
Ahh, the security vs. compliance debate. The challenge is balancing both. Compliance might make auditors happy, but it doesn't always mean your systems are actually secure. True security goes beyond frameworks.
But why not do both?
18. Compliance Cybersecurity Memes

Startups - we get it. There's a lot on your plate. However, not prioritizing compliance for startups is a risky move. Compliance builds trust with customers and sets your business up for long-term success. Bluey gets it.
19. Regulations…Just When You Think You're Safe

Just when you think you've finally caught up with the latest compliance regulations….new changes are announced. It's a never-ending cycle. Stay ready, because the compliance game never stops.
20. SOC 2: When They Say Everything's Fine
When the team says they have everything under control for SOC 2, but you know nothing is ever as simple as it seems.
SOC 2 is no joke and is quite a process. Don't assume it's going to be easy, and don't wait until the last minute to find out if you're missing key pieces. Make sure everything really is under control before your audit by conducting a gap assessment or working with a seasoned MSSP (Managed Security Services Provider) to help you be prepared.
21. What Do You Mean It's Quarterly?
Like many other legal and voluntary standards, there are ongoing action items to stay compliant with PCI DSS. Don't ever assume compliance is over once you have all the boxes checked off one time. Most frameworks involve ongoing items.
And that leads us to:
22. When Your Compliance Approach Is "Check The Box"
Don't let this be your compliance program!
SOC 2, ISO 27001, PCI DSS, GDPR, HIPAA, and more all require organizations to monitor vendor compliance on an ongoing basis to remain compliant. This is a critical part of risk management, especially as organizations increasingly rely on third-party services.
23. Imagine: This Could Be You
When that moment hits, and you realize you're officially certified - all the hard work and investments finally paid off. Time to celebrate, but don't forget - security is a journey, not a destination.
24. It's Been 84 Years….

When you try to get compliant without using a compliance automation tool, it can feel like it takes decades…Compliance automation tools seriously speed things up.
25. Lastly…Maybe All You Need Is a vCISO (Even If She Doesn't Even Go Here)

Many startups and SMBs outsource cybersecurity and compliance to a vCISO. The CISO as a service option can be a much more sustainable, scalable, and cost-effective option than building out an entire security team in-house.
At Rhymetec, our vCISOs integrate with your team and act as a part of your organization to help you meet your goals and turn security and compliance into business enablers.
Beyond Cybersecurity Memes - About Rhymetec
We hope these cybersecurity memes for 2025 brightened your day!
At Rhymetec, our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.
Meet Eden!
Hi! I'm Eden - yes, like the Garden of. I was born and raised in Connecticut and don't plan on leaving as it's been home for 34 years!
I attended Marist College for both undergraduate and graduate school. I have a BA in TV/Radio/Film and an MA in Marketing! While working in experiential events, I found a love for marketing and wanted to broaden my knowledge, so I returned to school.
I am very family-oriented and pride myself on being the “cool" aunt to my nieces, who are more like my best friends. I also have a cat named Luna (named after Luna Lovegood from Harry Potter) who likes to make her appearance on calls frequently.

Tell us a surprising fact about yourself…
I was on MTV TRL in the early 2000s! I was deemed the Jonas Brothers' biggest fan but lost out in the trivia competition to another fan. Don't ask me to find the footage of it… it's buried with my past love for the JoBros.
If you could have any superpower, what would it be?
I'd want to be able to fly. It would be great to get anywhere faster, especially when there's traffic!
What are some things you enjoy doing outside of work?
One of my favorite things is going to concerts—especially K-pop ones! There’s something different about the performances; I'm in awe of the talent.
I am also a shopaholic and love going shopping. In good weather, I also enjoy going to amusement parks as I consider myself a rollercoaster junkie. If time and money were no object, I would also travel a ton more. I love sightseeing and exploring new places!
Lastly, I love to bake. The more challenging the recipe, the more likely I will try it! It's relaxing to me, and then I get excited when others get to try it and admit that it came out good!

Tell us about your role at Rhymetec…
I'm a marketing associate at Rhymetec. I focus on lead generation, email campaigns, events/webinars, and partnerships. I have also been crowned the meme queen on social media!
Why did you pursue a career in the cybersecurity industry?
I come from a background in haircare/beauty, CPG, and, more recently, SaaS, so cybersecurity was a brand new venture for me when I pursued my position at Rhymetec.
After being here for 7 months, I’ve learned how fascinating it is and being able to pursue a career in the cybersecurity industry now has been extremely rewarding for me.
Like I tell everyone, I grew up on the computer rather than playing outside with friends. I’ve always been interested in anything and everything related to technology, so learning about cybersecurity has piqued my interest further and, I feel, comes naturally to me. So naturally that I am currently studying for my Security+ certification!
What is your favorite part about working at Rhymetec, or in the cybersecurity industry?
My favorite part about working at Rhymetec is I am constantly learning new things. I am also surrounded by some of the most intelligent, kind, and knowledgeable people who make every day here feel like home. I am grateful for this opportunity and so lucky to work with such amazing people daily!
What is the best advice you have ever received?
My mom has always taught me to love myself first. Whether in my work or self-esteem, you need to love and believe in yourself before you can expect anyone else to return the love and confidence. When you feel confident, everything else will come naturally to you.

From a security or compliance perspective, what advice would you give to a potential client or SaaS business?
I would tell a potential client or SaaS business to TRUST Rhymetec! Not because I work here or anything - but because we have some of the most robust services, and our team is smart, quick, and ready to work. We have some of the best cybersecurity analysts and penetration testers in the game. Always trust your gut with the best in the business—it'll be worth it when you gain your certifications and become compliant!