Ask any security professional what the biggest risk to organizations is, and nine times out of ten you'll get the same answer - people.
What security professionals know from experience is further confirmed by security research. Verizon's 2025 Data Breach Investigations Report puts the percentage of breaches that involved human error as high as 60%. Despite the best intentions, even the most diligent employees are susceptible to falling for social engineering tactics like phishing emails.
The onus is on company leadership to not only establish clear security policies for their business but to effectively communicate these policies to employees.
You could have the best, most meticulously documented security policies in the world, but they won't be able to help if they aren't communicated to the people who handle your assets daily. In 2025, small businesses also face added scrutiny from enterprise customers and regulators, making strong policies not just a security measure but a business requirement.
Rhymetec's Senior Cybersecurity Analyst, Kyle Jones, discussed how to effectively communicate security policies with employees in the latest episode of SaaS District:
Rhymetec, a Managed Security Services Provider focused on cybersecurity, compliance, and data privacy, enables SaaS organizations to have in-house security expertise at a fraction of the cost. Security professionals like Kyle have firsthand experience behind the scenes of the information security programs at hundreds of companies.
Based on Kyle's experience, here are 5 tips he encourages businesses to use to communicate security policies with employees effectively:
1. The First Rule of Security Policies for Small Businesses: Know Your Audience
"The first thing I would suggest is know your audience. Know who you're communicating to,” suggested Kyle when asked how to communicate security policies in a startup environment of rapid growth. "If you're a CEO, a CTO, someone that's going to roll out policies - the first thing you want to focus on is knowing your audience. If you're a marketing agency, you don't want to draft heavily technical policies for your employees, because the communication is going to fail."
When tailoring and communicating policies to your organization, you want the policies to become ingrained as practice, not just documents that sit on a shelf (or in a file on your Google Drive that nobody looks at twice!).
The first step to effectively accomplishing this is to know your audience and make sure you remember to tailor your language to everyone in your audience.
If you work in tech, it may seem evident to you what the policy means when it says:
"All corporate devices must utilize full-disk encryption using the AES-XTS data encryption algorithm in compliance with the NIST Advanced Encryption Standard".
But this likely means nothing to your company's lawyer or accountant. Instead, simplify the language and foster clear communication. If the policy is going to apply to a non-technical audience it's far better to create a policy like:
"All corporate laptops and desktops must enable full-disk encryption in their device's settings."
Creating effective policies and procedures requires remembering that many users may not be security or even IT knowledgeable. This is becoming even more important as many small businesses are adopting AI tools and cloud platforms in 2025. Policies must account for a non-technical audience using technologies that carry significant risk if misunderstood.
2. Make Sure Your Small Business Security Policies Are Drafted by a Subject Matter Expert
Kyle emphasized the importance of working with a subject matter expert who understands the regulatory requirements in your industry as well as the voluntary security standards your customers may want you to have.
Having a subject matter expert develop your policies, especially in the early stages, allows you to align your policies with industry standards and with what you want to achieve as your company grows. Businesses that bake security in from the get-go establish a solid foundation, saving money and headaches in the long term.
Many organizations see security policies as "another GRC checklist item". This couldn't be further from the truth. Security policies are a core part of your business, and working towards adherence is critical.
However, even before building buy-in, you need to make sure your security policies are rock solid.
Here are a few questions you should ask in reference to the organization or individual drafting your policies:
- Are they basing their security policies on a risk assessment specific to your organization?
Organizations have dramatically different risk profiles based on industry or sector. For example, a software as a service company has numerous risks related to cloud hosting, data segmentation, and cloud identity and access management. These risks are not shared by a typical accounting firm. Policies should be tailored to your specific organization and can't be written in a vacuum.
- Does the person or organization have a strong working knowledge of how policies are implemented in practice?
Policies are only as useful as their implementation (and you will be audited based on both!). There should be a strong plan for operationalizing any policies that have been drafted on behalf of your business. This is where working with an outside expert like a Managed Security Services Provider, particularly for startups who may not have the resources to build out large in-house security teams, can come into play as a resource.
Ensuring The Companies of the Future Are Secure
To Kyle, one of the most important challenges of his work is making sure companies have solid security practices in place and that they are secure from the ground up:
"At Rhymetec, we're working with startups. A lot of them are early-stage startups…A lot of the companies that I work with and manage the security program for are the future. They have very powerful technologies and very innovative products".
The companies he works with are forward-thinking and looking to grow quickly. Establishing solid security policies for small businesses is critical before they expand into new marketplaces or internationally, before they go public, or before they are acquired.
Subject matter experts like the team at Rhymetec take the job of security entirely off their plate so they can focus on core tasks and grow their business.
3. Emphasize Security Policies Throughout the Year
There's nothing worse than policies that haven't been adopted.
Identify opportunities throughout the year where you can emphasize security policies for your small business in a proactive and exciting way.
"Something else I think that all organizations can do more of is emphasizing the importance of the policies. The policies are not an annual thing we review and send out to employees, and it's done. We want to find different ways to emphasize the policies," Kyle pointed out.
Have a company all hands?
This can be a great opportunity to discuss security policies, their implementation, and overall best practices. Include policy provisions in your security awareness and training courses, and aim to connect policies with outcomes.
When employees ask questions about anything security or IT-related, that can be a great opportunity to reference the policies and see what they say. When Kyle talks to the companies he manages security programs for, he uses their questions as an opportunity to bring up the policies and emphasize their importance.
It can be difficult for employees to conceptualize why security policies are necessary as they can often seem divorced from outcomes.
Walking the company (at a high level) through how a ransomware attack happens, or how threat actors launch business email compromise campaigns can be informative and help solidify the importance of adhering to policy language. The point is not to fearmonger, but to provide information that helps employees mentally link the policies to the reasons behind them.
People are more likely to adhere to something if they understand it.
In other words, don't just tell people what to do - show them why it matters.
4. Have a Training Program Built Around the Policy Language
Staff awareness training is an excellent opportunity to reinforce and build on your policies.
You want to ensure that your training program directly reflects language from your policies. For example, if you have a policy around full disk encryption (to use an earlier example), reinforcing this and providing a how-to guide in your training provides an excellent opportunity for reinforcement.
As another example, if you have a policy of reporting any suspicious emails as phishing for the security team to look at, reinforce this with training! Small businesses now often rely on a myriad of cloud collaboration tools, APIs, and AI assistants. Your training must be updated to reflect this reality and directly reference related policies, such as how to securely handle shared data or what information can be input into AI systems.
It's hard for employees to remember technical minutia and playbooks, so constantly reinforcing and iterating on your organization's security posture and policies is critical.
5. Update and Review Policies Regularly
Risk to your organization changes.
Both the regulatory and threat landscapes are in constant flux. Policies should not only be updated regularly but should be continuously reviewed and adjusted based on new information.
For example, the advent of large language models such as OpenAI's GPT-4 and Google's Gemini should force organizations to reimagine their policies:
- Are employees allowed to use these applications at work?
- What types of data can be shared with them?
- Do our policies reflect current regulatory language about algorithm decision-making?
These are important questions to answer. At Rhymetec we recommend conducting regular policy reviews. Working with a vCISO can dramatically simplify this process as they will be in tune with regulatory and threat landscape changes that could impact your business.
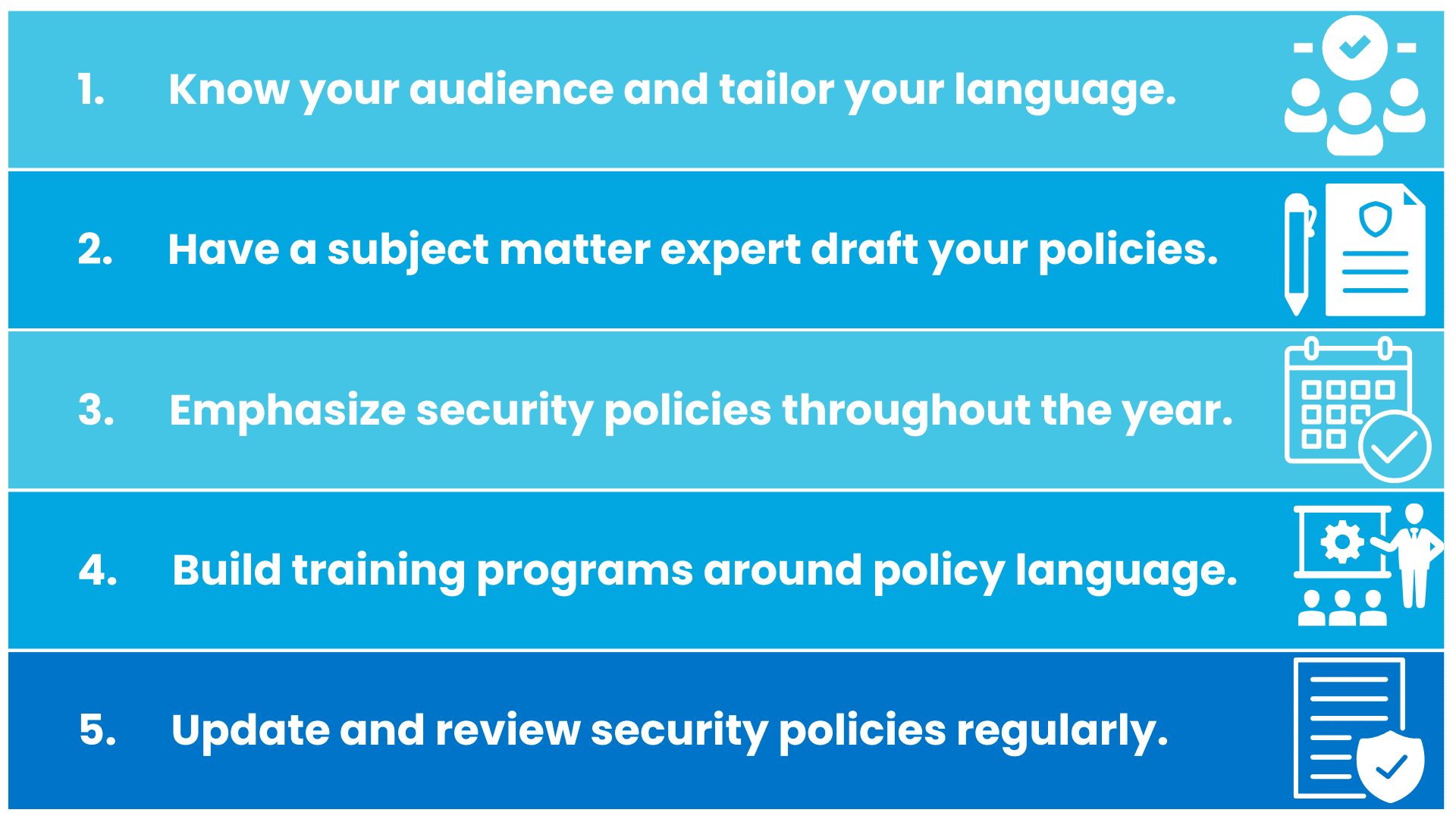
In summary, here are the 5 expert-approved tips discussed in this article to effectively communicate security policies to employees:
Security Policies for Small Businesses: The Bottom Line
Small businesses need security policies that work for them. They need policies that are tailored, based on real risks the business faces, and that meet a range of complex compliance requirements.
When done right, reinforced, and iterated on, policies form the backbone of a security program and enable organizations to do business with confidence and precision.
Hopefully, this article helped solidify how to draft and implement policies effectively. At Rhymetec, we believe that security and compliance are continuous processes that need to evolve and improve over time. We work directly with clients to build policies and security programs that meet regulatory requirements, scale with their growing organization, and enable business outcomes.
If you have more specific questions on crafting security policies for your business, please feel free to contact our team:
FAQs: Security Policies For Small Businesses
Why are security policies so important for small businesses?
Because most breaches stem from human error, strong policies protect against mistakes and provide much-needed guidance to employees. They also demonstrate accountability to customers, auditors, and regulators.
How often should small businesses update their security policies?
At least annually — but ideally every 6 months or whenever major changes occur in technology, staff, or regulations. In 2025, rapid changes in AI and data privacy laws mean reviews are needed more frequently.
Who should write or review a company’s security policies?
A subject matter expert with compliance and technical knowledge. Many SMBs rely on vCISO services or MSSPs like Rhymetec to ensure policies are tailored to industry risks and compliance frameworks.
How can small businesses make policies easier for employees to follow?
Keep language clear and non-technical, integrate policies into training, and connect them to real-world examples like phishing or ransomware incidents. Policies that are simple to understand are more likely to be followed.
Do security policies help with compliance certifications?
Yes. Well-documented policies form the backbone of compliance efforts for frameworks like SOC 2, ISO 27001, HIPAA, GDPR, and CMMC. They are often the first thing auditors request when evaluating a company’s security posture. As part of Rhymetec's Vanta Compliance Services, we can leverage cutting-edge compliance automation technologies like Vanta to accelerate this process for you. We enable our clients to maximize their use of compliance automation platforms like Vanta and Drata.
About Rhymetec
Rhymetec was founded in 2015 as a Penetration Testing company. Since then, we have served hundreds of SaaS businesses globally in all their cybersecurity, compliance, and data privacy needs. We're industry leaders in cloud security, and our custom services align with the specific needs of your business.
About Kyle Jones: Information Security Manager at Rhymetec
Kyle Jones is a Senior Cybersecurity Analyst at Rhymetec. Kyle is an experienced cybersecurity and compliance professional who excels at aligning SaaS cloud architecture with industry standards and regulations. If you have any questions about security, you can get in touch with Kyle on LinkedIn or contact our team at Rhymetec.