Regular cybersecurity audits are the best way to ensure your business continuously meets security and compliance requirements while reaping the business benefits of investing in security. This post will go over the different types of audits, their benefits for your organization, how to prepare, and common findings to be aware of.
For many fast-growing startups and SMBs, cybersecurity might not feel like a top priority. But with increasingly complex data regulations, rising threats, and growing client expectations, security can no longer be an afterthought, regardless of company size or industry.
The good news is that organizations that invest in improving their security posture and undergo regular cybersecurity audits start to see a wide range of benefits, especially once they have evidence they've successfully completed their audit through a certification or a report:
Barriers are removed in their deal flows, the time spent on filling out onerous security questionnaires is eliminated, and they can get back to what really matters - moving their business forward.
Why Cybersecurity Audits Matter For Your Organization
A cybersecurity audit is a thorough review of an organization's security posture, assessing the adequacy of protections in place to defend against cyber threats and meet regulatory requirements. You can think of an audit as a health check for your security practices, allowing you to identify potential vulnerabilities before they can lead to an actual security incident.
Audit findings provide valuable insight into how secure your organization is and how well you are meeting any relevant requirements. Knowing how well your security practices measure up against industry standards allows you to pinpoint where improvements need to be made, and make only the changes you actually need.
Cybersecurity audits identify vulnerabilities and show where your security measures align with or diverge from relevant frameworks like ISO 27001, SOC 2, and HIPAA. After an audit, as you enact necessary changes to address the audit's findings, you'll reduce the risk of regulatory penalties, reputational damage, and security incidents. Decision-makers can use the results of an audit to prioritize security improvements and guide their compliance efforts.
When clients, investors, regulators, or other stakeholders expect evidence of your security controls, having third-party verification of the strength of your security posture is important. It shows that you've addressed security requirements upfront, creates confidence in your security approach, and helps meet stakeholder expectations.

Types of Cybersecurity Audits Every Startup Should Be Aware Of
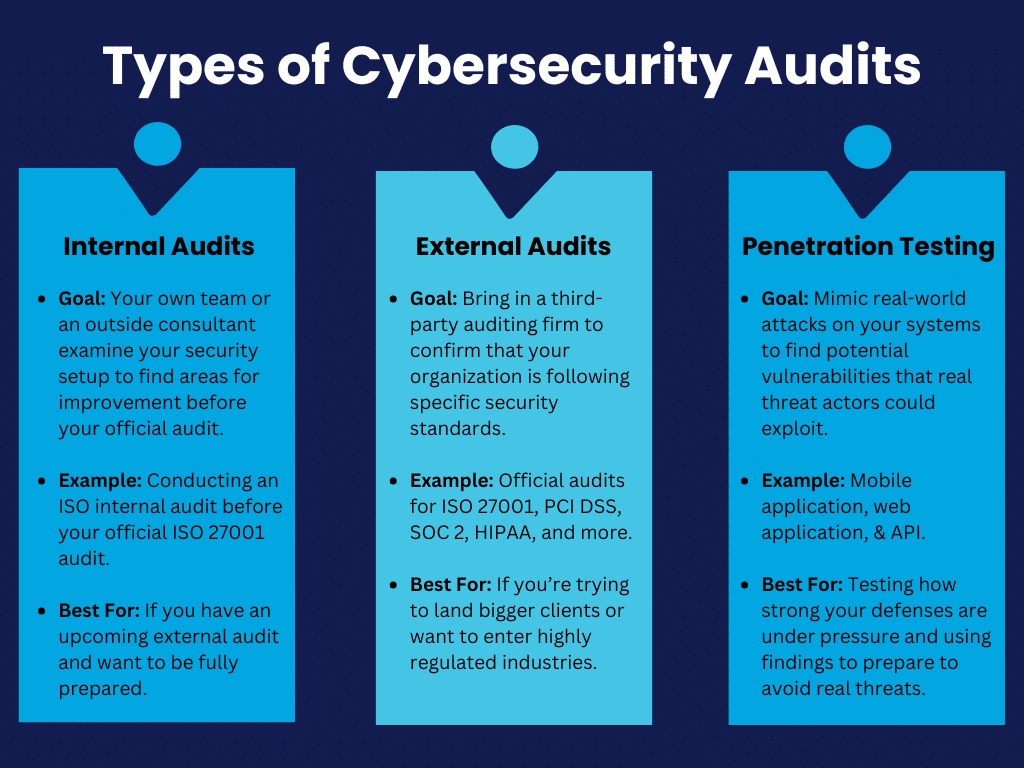
Startups should know about a few different types of cybersecurity audits:
Internal audits are when your own team or an outside consultant examines your security setup. The goal is to conduct a gap assessment and find any areas for improvement to help better prepare you for future external audits. For example, an ISO internal audit provides a way to spot weaknesses early and adjust them before your official audit for frameworks like ISO 27001 and ISO 42001.
External audits bring in a third-party auditing firm to confirm that your organization is following specific security standards such as ISO 27001, PCI DSS, SOC 2, HIPAA, and more. Passing an external audit is vital if you're trying to land bigger clients or want to enter highly regulated industries.
Penetration testing mimics real-world attacks on your systems to find potential vulnerabilities. Penetration tests give you an idea of how strong your defenses really are under pressure, and the findings help prepare you to avoid real threats:
How to Prepare For a Cybersecurity Audit
To prepare for an audit, the first step is to take a close look at your existing policies and procedures: Are they actually being followed?
It's common for companies to write policies that look great on paper but fall short in practice. You'll want to make sure everyone on your team knows their roles, especially around access controls, data handling, and your organization's incident response policies.
Don't neglect the tech side. Run vulnerability scans, review your logging and monitoring, and make sure your backups are up to date. Auditors will likely examine these areas regardless of which type of audit you undergo. Lastly, keep your documentation extremely organized. Auditors appreciate easily accessible and well-organized documentation. Having it ready can be the difference between a smooth audit and a chaotic scramble.
Bonus Tip: A compliance automation tool can come in extremely handy at this stage, as it allows a single place to upload and keep track of all of your documentation. Your auditor will appreciate being able to easily access everything in one place!
Preparing ahead of time as much as possible puts you in control of the process rather than reacting to questions or findings that may come up. Providers like Rhymetec offer internal audits and gap assessment services that are conducted before your audit, leading to fewer surprises during your official audit.
Common Findings in Cybersecurity Audits (And How To Address Them)
Cybersecurity audits often reveal a few common recurring issues that many startups and SMBs face:
One of the most common findings across a variety of different types of audits is weak access controls. Cybersecurity audits frequently find gaps in access control requirements, meaning that too many people have unnecessary access to sensitive data or systems.
The fix here is straightforward:
- Review who has access to what.
- Limit permissions to those who need it.
- Implement multi-factor authentication to add a last additional layer of security to make it harder for unauthorized users to gain access.
Another issue that often comes up is missing or outdated documentation. Auditors will expect to see things like security policies, incident response plans, and training records. If you can't provide these documents or if they're outdated, that's a red flag.
To address this issue, you should:
- Create clear, up-to-date policies that reflect what's actually happening at your organization.
- Make documentation a regular part of your operations, so you're not scrambling to pull everything together before an audit.
- Consider using compliance automation software to organize all of your documentation for auditors in one place.
Another common area where audits also tend to find vulnerabilities is in systems that haven't been patched or updated.
Leaving old software as is is like leaving your door unlocked. You should be regularly updating and patching systems to close off potential entry points for attackers. Simply setting up automated reminders or systems to handle updates can be extremely helpful.
Third-party risk management is another area that is often overlooked by organizations and comes up in audit findings. For PCI DSS audits, for example, this is one of the most common challenges our experts at Rhymetec see that organizations encounter. For many frameworks, you need to make sure your third-party vendors are also compliant.

Finally, many audits reveal a lack of proper employee training. As noted by our experts in Rhymetec's Cybersecurity Awareness Month Tips, your people are often the first line of defense. If they're not aware of basic security practices or don't follow steps to adhere to them on a daily basis, it's a problem.
Ongoing security awareness training and phishing training for employees help everyone in your company recognize and avoid common vectors of attack like phishing attempts.
If possible, address these common issues ahead of time for a smoother audit process.
Cybersecurity Audits and Penetration Testing
Penetration testing is the best way to understand how well your defenses would stand up to real-world attacks.
While not every audit requires a pen test, it's often necessary for audits tied to specific compliance frameworks like PCI DSS and certain SOC 2 reports. These audits don't just ask if you've set up your security controls - they want tangible proof that your system can actually withstand an attack.
Penetration testing is recommended when you need more than a surface-level review of your security and need to go beyond checking boxes to meet compliance requirements; experts simulate actual cyberattacks to try to break through your defenses. Think of it as having someone attempt to lockpick your door, rather than just checking if your door is locked.
Note: If your organization is preparing for a major compliance audit, working with clients that demand high levels of security, or going through rapid growth, a penetration test is highly recommended!
If you incorporate penetration into your regular security checks, you'll get a clear picture of how well you're protected and will be able to tackle weaknesses before they become costly problems down the line. Getting a test done annually or after major changes to your systems helps you stay ahead of emerging threats.
Rhymetec offers a variety of penetration testing services, including:
- Mobile application penetration testing
- API penetration tests
- Web application penetration testing
- External network penetration tests
Choosing The Right Partner for Your Audit
Not all auditors are created equal, so it's important to select a partner who's not only experienced but also a good fit for your company's size, structure, and industry. You need someone who understands both your industry and the specific compliance requirements you're facing.
Audit Partner Factors To Consider
First, check out their track record. Have they worked with startups or SMBs before? It's one thing to know the rules, but another to understand the unique challenges small to midsized companies and startups face regarding security and compliance.
Ask about their previous clients and whether they've helped similar businesses successfully meet their compliance goals. Request to see case studies from their prior engagements with companies with similar profiles as yours.
Another factor to consider is how hands-on you want your audit partner to be. Some partners take a more hands-on approach by choosing to work with select MSSPs to help you improve your security along the way, while others are more focused on just performing the audit and reporting findings.

Audit Report "Red Flags" To Look Out For
A thorough audit report gives you a roadmap for improving your security with clear steps, while a deficient one can leave you with more questions than answers.
Plus, 69% of organizations report that the quality of compliance reports is extremely important. Your clients and stakeholders will want to see evidence of a thorough, high-quality audit.
So, how do you tell the difference between a thorough audit report and a deficient one?
1. First, look at how the findings are communicated:
A high-quality audit report won't just tell you that there's an issue - it will explain where the problem is, why it matters, and how it could impact your business. Look for specifics, like which systems or processes failed, how attackers could exploit weaknesses, and what steps to take next. If your report is filled with vague statements or broad recommendations without context specific to your organization, that's a sign it's not as thorough as it should be.
2. A high-quality report will also show you how issues across different areas are connected:
If weak access controls, for example, show up in multiple places - whether in your cloud setup, employee accounts, or vendor portals - a good report will explain how these issues are linked. A deficient report might mention them individually without showing the bigger picture.
3. Findings on your documentation is another area where a thorough report stands out from a deficient one:
A high-quality report points out exactly where your policies or training records are lacking and provides actionable steps to fix them. If your report glosses over missing documentation or doesn't dig into whether your policies match actual practices, you're likely looking at a surface-level, boilerplate review rather than a meaningful and tailored audit.
4. Finally, a quality report doesn't simply list issues but will categorize them based on their severity and urgency:
This helps guide you on which areas to focus on first. A deficient report may give you a laundry list of issues but won't help you understand which ones pose the most immediate threat.
In short, a thorough audit report provides clarity, context, and a plan. A deficient one leaves you guessing and unsure of how to proceed and may not hold up under scrutiny from your customers and stakeholders.
How Working With An MSSP Simplifies Cybersecurity Audits
Partnering with a Managed Security Services Provider (MSSP) can take a lot of stress out of cybersecurity audits. An MSSP handles much of the ongoing work for you, so when it's time for your audit, you're not rushing to get everything in order.
With continuous monitoring, regular updates, and fully managed compliance services, an MSSP ensures that your security posture stays audit-ready all year round. For example, if your business needs to meet standards like PCI DSS or ISO 27001, an MSSP can keep your policies and security controls aligned with the latest requirements and make sure you're up-to-date on your recurring audits.
Working with an experienced MSSP is the best way to minimize the risk of non-compliance and saves your internal team from having to devote time to it themselves. When you work with an MSSP, you're essentially outsourcing the complex, technical aspects of security to a team that specializes in it, freeing up your business to focus on growth while staying secure and compliant.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
October isn't just a month of scary movies, sweater weather, and all things pumpkin spice - this month is dedicated to cybersecurity awareness and is a time for the public and private sectors to raise awareness about the importance of cybersecurity.
For the general public and organizations that do not specialize in cybersecurity, this month is a great opportunity to learn their role in protecting their digital assets, avoiding cyber threats, and staying safe online.
Here at Rhymetec, our cybersecurity experts are keenly aware of the risks clients face across many industries. Our experts act both in an advisory capacity and build and manage infosec programs for over 700 organizations.
This October, in honor of Cybersecurity Awareness Month, we've asked them for one piece of advice they would give to a potential client or SaaS business. Here's what they said:
Cybersecurity Awareness Month Tips From Our Experts
The following Cybersecurity Awareness Month tips are directly from Rhymetec's experts, based on their experience working with a variety of clients across different industries:

"The best advice I would give to a potential client is to start with your employees! Humans are the biggest security risk. When planning to become compliant in any framework or just wanting to mature your security posture, start with personnel. You are only as strong as your weakest team member. Recurring security awareness training should be mandatory for all employees. Educating and reminding employees of malicious tactics used by cyber attackers will decrease the likelihood of your organization being victim to a security incident. Awareness is key."
- Memori Hill

“You don’t have to go it alone! Security and Compliance are deep and ever-evolving wells of information. It can be difficult to dedicate effort and resources to building out an effective information security management system while also focusing on the day-to-day activities required to support and expand your business. We have an excellent team of Security experts eager and ready to help out.”
– Dakota Wright

“There are never too many controls in place to prevent a potential breach or a future incident. Depending on your geographical location as well as the type of data you handle, there are different types of compliances that may be required. Here at Rhymetec we offer a wide array of frameworks that we not only implement for you but manage as well, ranging from SOC 2 to FedRAMP. It’s not about if it will happen, but when it will happen.”
– Endri Domi

“Consistency is important. Staying on top of digital tools can help in staying efficient and avoid missing links and flaws. Use tools and software to help simplify compliance.”
– Leena Niazi

“Security for your cloud product should be between 7-15% of your overall monthly cloud budget to ensure you’re adequately protecting your assets. You wouldn’t buy an expensive car and then leave it unlocked with the keys inside in your driveway.”
– Aaron Butler

“Becoming compliant is more than just checking a few boxes on an excel sheet or pressing a button. True compliance requires security hardening measures that are customized to your business and tailored to your environment and customer base. A dedicated compliance team is the most successful way to pursue achieving a compliant status, as well as protecting yourself from internal and external threats.”
– Christian Mouer

“Never underestimate the bad guys.”
– Allan Cavazos

“Cyber security is not a DIY job. There are several domains within cyber security, and you need to have the skills and knowledge to understand these different domains. My one advice would be to hire professionals who understand governance/compliance and technical aspects of cyber security.”
– Metin Kortak

“Compliance may seem like an impossible feat, however, know it is possible, and Rhymetec can help you get there.”
– Pamela Tobón
“Although becoming compliant will improve the overall security posture of your business, no organization is truly infallible. Developing repeatable processes and a workplace culture that prioritizes security education and training will help reduce risk and allow your organization to adapt to the ever-changing threat landscape that SaaS solutions face today.”
– Sam Brokaw

Cybersecurity Awareness Month Tips: Common Themes
A common theme that emerged from our experts' Cybersecurity Awareness Month tips was the importance of proactive security measures. The bottom line is that you can never be too prepared.
It's always better to have as many defensive measures in place as possible and avoid a security incident in the first place. Measures like security awareness training for employees to mitigate the human risk factor, putting your security hygiene to the test through regular penetration tests, and allocating sufficient resources to continuously improve your cybersecurity posture are crucial.
Another frequent answer we saw was that cybersecurity is not a DIY job! Hiring an external security team can substantially help organizations, especially in the early stages so that your security program can scale with your business growth. Virtual CISOs at organizations like Rhymetec have extensive experience balancing budgetary needs, usability, and security for start-up cybersecurity programs.
It's not an easy balance, but leveraging an experienced partner can deliver huge amounts of specialized talent without the need to spend millions of dollars on an in-house security team. Managed Security Services Providers like Rhymetec have dozens of professionals across security disciplines like cloud security, compliance, web application security, penetration testing, and others.
They have experience applying these skills to startups and SaaS businesses in a way that drives real security outcomes as you scale while also considering your budget.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- Cybersecurity For Startups: A Rhymetec Guide
- vCISO Pricing Breakdown: Find The Best Fit For Your Needs
- Cybersecurity for SMBs: 10 Key Measures and Statistics
Secure file transfer protocol (SFTP) is a secure and encrypted method of transferring files over a network. It uses secure shell (SSH) connections to keep sensitive data safe during transfer, making it a top choice for businesses and IT professionals. With the average data breach now costing more than $4.45 million, a 15 percent rise over three years, SFTP's role in protecting data is more important than ever.
SFTP Explained
Secure file transfer protocol (SFTP) is an encrypted method of transferring files over a network. It uses SSH connection to encrypt both the commands and the data being transferred, making it a safer option than traditional file transfer methods.
By understanding how to establish and maintain SFTP connections, you can ensure your data is transferred securely and efficiently, safeguarding against potential security threats.
What Is Secure File Transfer Protocol (SFTP)?
Unlike traditional file transfer methods, which can expose your data to potential risks, SFTP uses SSH connections to offer a higher level of security. This function encrypts both the commands and the data being transferred, ensuring that sensitive information remains protected from being intercepted during transit.
In addition to security, SFTP offers reliability and performance efficiency, making it a preferred choice for organizations that require a secure and efficient way to transfer files across networks.
How to Establish an SFTP Session
Establishing an SFTP session requires an SSH client, which is typically pre-installed on most operating systems, including Windows, macOS and Linux. This availability makes it convenient for users across different platforms to initiate secure file transfers without the need for additional software installations.
There are two primary methods of establishing an SFTP connection:
SFTP clients: Tools like Cyberduck, Filezilla and Transmit 5 provide user-friendly interfaces that simplify the process of secure file transfers. These clients require users to input authentication information and relevant file transfer data, streamlining the process for end-users.
Command line: For more advanced users, the command line interface offers a powerful and flexible way to establish SFTP connections. This method is favored by software engineers and system administrators who prefer not to rely on third-party clients. While it may seem more complex, it provides greater control and is considered safer by some users.
Here’s how you can initiate secure file transfers via a command line interface. If you choose to use a third-party SFTP client, you can view their instructions by going to the client's website.
Steps to Initiate Secure File Transfer With SFTP
To initiate a secure file transfer using SFTP through the command line, first set up your connection.
1. Connecting to a Remote Server
Open your terminal or command prompt.
Connect to the remote server or device, which is similar to connecting a remote machine via SSH. Instead of entering SSH username@host_name, enter SFTP username@host_name.
2. Transferring Files
Upon establishing the connection, you can now start transferring files. The following commands will enable you to copy and transfer files to and from both machines.
To download a file from the remote server to your local machine, enter: 'get remote_path local_path'
To upload a file from your local machine to the remote server, use: 'put local_path remote_path'
3. Set Your Security Settings
Always ensure you connect to a remote server via a VPN connection and enable only the necessary network ports. Since SFTP uses port TCP 22, you must ensure this port is open on both machines.
Port 22 should never be open to the public for security purposes. If you must open Port 22, you must do so within a virtual private network (VPN), ensuring that only your own device and the remote machine you're connecting to have access to Port 22.
These steps provide a straightforward method for initiating secure file transfers using SFTP, ensuring your data remains protected during transit.
Basic File Maintenance Using SFTP
Regular file maintenance is crucial for keeping your system organized, ensuring data integrity and optimizing performance. Proper file management helps prevent data loss, reduces clutter and makes locating and managing your files easier. Neglecting file maintenance can lead to inefficient storage use, increased security risks and potential data corruption. You can maintain a clean, efficient and secure file system by routinely performing basic file maintenance tasks.
Once you’re connected to an SFTP server, maintaining and managing files becomes straightforward with a set of basic commands:
put: Copy a file from the local machine to the remote machine.
get: Copy a file from the remote machine to the local machine.
ls: List the contents of a directory on the remote machine.
cd: Change the current working directory on the remote machine.
lls: List the contents of a directory on the local machine.
lcd: Change the current working directory on the local machine.
These commands facilitate efficient file management, making it simple to navigate and organize files on both local and remote systems.
Other Useful SFTP Commands to Know
In addition to basic file transfer commands, SFTP provides several other commands that enhance file management capabilities. These commands are essential for performing more advanced tasks, granting users greater control over their file systems. However, improper use of the commands can lead to unintended changes or security vulnerabilities, so it’s crucial to understand their functions and use them cautiously.
Beyond the basic file transfer and maintenance commands, SFTP offers additional functionalities to enhance your file management capabilities:
chmod: Change file permissions on the remote host.
chown: Change file ownership on the remote host.
mkdir: Create a directory on the remote host.
rm: Delete a file on the remote host.
rmdir: Remove a directory on the remote host.
rename: Rename a file on the remote host.
lpwd: Show the present working directory on the local computer.
pwd: Show the present working directory on the remote host.
These commands offer comprehensive control over file operations, ensuring that you can manage your files securely and efficiently.
Frequently Asked Questions
What is the difference between FTP, FTPS and SFTP?
Understanding the differences between various file transfer protocols is crucial for choosing the right tool for secure file transfers. Here's a brief comparison:
FTP: Traditional file transfer protocol that transmits data without encryption, making it vulnerable to interception.
FTPS: An extension of FTP that adds SSL/TLS encryption for secure transmissions. While more secure than FTP, it doesn't offer the comprehensive security of SFTP.
SFTP: Integrates SSH to encrypt both the commands and data, providing the highest level of security among these protocols.
Is SFTP still relevant today?
SFTP remains highly relevant in today's digital landscape. It is a reliable and cost-effective method for transferring files securely between servers. System administrators and software engineers commonly use SFTP due to its robust security features and ease of integration into existing systems.
Despite the emergence of newer file transfer technologies, SFTP's encryption and secure transmission capabilities make it a preferred choice for maintaining server databases and internal file transfers. Its continued use in various organizations underscores its importance and reliability in ensuring data security.
You can read the original article posted in Built In by Rhymetec CISO, Metin Kortak.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- vCISO Pricing Breakdown: Find The Best Fit For Your Needs
- Cybersecurity for SMBs: 10 Key Measures and Statistics
- A Log Analysis Tutorial
When evaluating vendors to build and audit your information security (infosec) program, there are many important questions to ask: Who exactly will be handling your data? What are the team's credentials and prior experience? Will the vendor be outsourcing services internationally, and if so, how will their control and oversight of the process be impacted?
Is the vendor claiming to be able to both build your infosec program AND conduct your official audit?
Some MSSPs and "compliance as a service" providers are now advertising that they can help organizations meet required controls and conduct their certification audit. In this article, we'll go over the potential issues with this from a legal, reputational, and ethical perspective.
Let's be clear about a few of the potential pitfalls of this approach right off the bat:
Potential Pitfalls Of Engaging "All In One" Vendors
Having the same entity create and assess your infosec controls introduces a blatant conflict of interest. This presents clear ethical issues, as it's essentially like having a restaurant conduct its own health inspection.
They may not provide a fully objective assessment and could be inclined to overlook issues to hand you a more favorable report. Your audit may not hold up under scrutiny from stakeholders in the future, especially if you were to experience a security incident.
Another red flag is if an "all in one" vendor is claiming to be able to implement your security controls and conduct your audit at a suspiciously cheap price tag. Meeting requirements such as SOC 2, HIPAA, GDPR, and dozens of others can be fairly economically efficient and not break the bank. However, compliance isn't incredibly cheap either. As in many cases in life, when something seems too good to be true, it probably is.
Meeting information security compliance requirements isn't always an easy process. It often takes making many complex decisions involving business outcomes, processes, technologies, and acceptable risk. In other cases, it means fundamentally reworking a core business process to meet a requirement.
When done correctly, meeting requirements provides regulators and potential customers the assurance that your organization takes security seriously.
When done poorly, it can result in expensive boondoggles that cost your organization legal fees and valuable customer relationships. Engaging separate entities to develop and audit your infosec program is a safeguard against bias and helps you uphold the integrity of your compliance efforts.

So, what are the actual requirements and guidelines from which the robustness of your compliance can be judged?
Let's take a look at what a few entities and guidelines have to say on audit independence:
Guidelines and Best Practices To Ensure Audit Independence
Sarbanes-Oxley (SOX) is a U.S. federal law aiming to protect investors by improving the reliability of corporate disclosures. Although it primarily applies to publicly traded companies, it can indirectly impact privately held SaaS companies, for example, that may plan to go public in the future or those that provide services to public companies.
For instance, a SaaS company that handles financial data or provides financial reporting services to public companies may need to make sure its controls align with SOX requirements.
Section 404 of Sarbanes-Oxley requires that companies have an independent audit of internal controls over financial reporting.
The Public Company Accounting and Oversight Board (PCAOB) states the following:
A registered public accounting firm and its associated persons must be independent of the firm's audit client throughout the audit and professional engagement period.
Note 1: Under Rule 3520, a registered public accounting firm or associated person's independence obligation with respect to an audit client encompasses not only an obligation to satisfy the independence criteria applicable to the engagement set out in the rules and standards of the PCAOB, but also an obligation to satisfy all other independence criteria applicable to the engagement, including the independence criteria set out in the rules and regulations of the Commission under the federal securities laws.
Note 2: Rule 3520 applies only to those associated persons of a registered public accounting firm required to be independent of the firm's audit client by standards, rules or regulations of the Board or Commission or other applicable independence criteria.
Now that description is a bit heavy on jargon, so we can consult another source. SOC 2 is overseen by the American Institute of Certified Public Accountants (AICPA). AICPA has (fortunately for the non-accountants and lawyers among us) published a "Plain English Guide to Independence," which provides the following guidance:
Independence of mind is the state of mind that permits a member to perform an attest service without being affected by influences that compromise professional judgment, thereby allowing an individual to act with integrity and exercise objectivity and professional skepticism.
Independence in appearance is the avoidance of circumstances that would cause a reasonable and informed third party, who has knowledge of all relevant information, including safeguards applied, to reasonably conclude that the integrity, objectivity or professional skepticism of a firm or member of the attest engagement team is compromised.

Image Source: AICPA
In even plainer English, AICPA is saying that auditors should avoid any conflicts of interest that could impair their objectivity. This includes scenarios where they might audit their own work or the work of close colleagues, which would naturally apply to building and then auditing the same infosec program.
The AICPA's guidance, particularly under the SOC standards, prohibits organizations from auditing their own services, stating that:
"The auditor's responsibility is to provide an independent assessment of the service organization's controls that may affect user entities' financial reporting."
AICPA's emphasis on independence effectively makes it clear that an organization both implementing security controls for compliance and conducting the audit would risk impairing the auditor's independence and objectivity, thus not aligning with best practices. It's clear from their guidance that auditors should avoid any conflicts of interest that could impair their objectivity.
Lastly, many standards and frameworks, such as ISO/IEC 27001 and NIST, emphasize the importance of independence in the auditing process. They recommend that audits be conducted by individuals who are not involved in the day-to-day operations or implementation of the security program.
Assessing Audit Independence and Quality
Now, let's imagine a SOC 2 audit. Say you've hired an accounting firm with a security branch to help implement controls pursuant to SOC 2. Now imagine that the very same firm is going to audit your organization for compliance. Could a reasonable and informed observer conclude that the firm auditing the controls may be biased as a result of the fact that they were the ones who also implemented the controls?
To recall an earlier analogy, it's as if a restaurant were to perform its own health inspection. What are the odds that they are going to find major violations? Probably pretty low. When the same person who designed and implemented the infosec program also audits it, there is a significant risk of bias. They may inadvertently overlook issues or be less critical of their own work.
Even if this "all in one firm" issues a SOC 2 report without findings, your organization could still be at substantial risk. Imagine you have a major cyber event in the future, and customers find out that your SOC 2 report wasn't entirely accurate and that the firm you hired took shortcuts through the process. Information security isn't just a legal risk; it's a business and reputational risk.
A reputable information security compliance provider (whether an accounting firm or a managed security services provider) should do the following:
- Be able to provide reference customers, either publicly or privately, who have worked with the firm in the past to implement controls.
- Work with a reputable outside auditing firm that conducts independent audits of control implementation.
- Ensure that all employees adhere to industry standards, guidelines, and best practices such as those set by the AICPA.

Some firms, such as Rhymetec, have identified specific high-quality third-party firms that we often recommend to our clients to complete the audit process. But if clients prefer a different audit partner, that is okay too.
Information security compliance requirements shouldn't be considered a burden to businesses. Implementing requirements such as SOC 2, GDPR, HIPAA, and others should help organizations be assured that they are meeting relevant legal and ethical requirements while taking adequate and appropriate measures to safeguard customer data.
When conducted by ethical providers, standards like SOC 2 can substantially enhance a business's confidence and security protocols without disruption and without massive cost. Independent audits provide greater credibility to your stakeholders, including management, customers, and regulatory bodies. You can be confident that the audit findings are impartial and accurate.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business.
Interested in reading more? Check out more content on our blog:
- Maximize Your Use of Compliance Automation Platforms
- Cybersecurity For Startups: A Rhymetec Guide
- Security vs. Compliance? A False Dichotomy
Each year, companies and government institutions suffer data breaches without being able to identify how the breaches occurred or what data was compromised. Enter log analysis. Log analysis involves reviewing and interpreting computer-generated records of events in software applications, operating systems and other digital environments.
Log Analysis Explained
Log analysis is the process of analyzing computer-generated logs tracking activity in a digital environment. It can be used to detect anomalies and diagnose larger security problems, allowing cybersecurity teams to troubleshoot issues, mitigate a breach or protect against a future attack.
Accurate analysis of computer logs can provide the information needed to prevent future attacks. This scenario is typical among organizations lacking proper logging systems. Most establishments don't retain logs for a year unless mandated by laws and compliance regulations. This allows attackers to breach networks without leaving any trace of their actions, complicating efforts to understand and mitigate the damage.
What Is Log Analysis?
Log analysis is the process of analyzing computer-generated records of events in software applications, operating systems, and other digital environments. By capturing data on user activities, system errors and security events, it uncovers helpful information, detects anomalies and diagnoses problems.
Historically, manual log analysis was common, but the vast amount of data available now requires automated systems to identify patterns and troubleshoot issues efficiently. Modern log analysis tools provide filters and query functionalities, allowing users to sift through massive data sets and apply specific criteria to identify relevant logs.
Why Is Log Analysis Important?
Log analysis helps organizations rapidly detect and respond to security incidents and data breaches. By examining logs, security teams identify unauthorized access attempts such as repeated login failures, which may indicate someone trying to breach accounts with incorrect passwords. Using filters and queries, teams focus on specific events or user actions, improving their ability to identify threats swiftly. Logs also reveal unusual activities like accessing sensitive data at odd hours, allowing teams to intervene promptly and reduce the risk of breaches.
How to Do Log Analysis
Log analysis employs various techniques to extract insights and enhance system security and performance:
- Pattern recognition: Identifies recurring sequences within logs, detecting normal and abnormal behavior to spot trends and anomalies over time.
- Anomaly detection: Focuses on identifying irregular activities deviating from established patterns, such as a sudden spike in login attempts indicating a brute-force attack.
- Root cause analysis: Traces issues to their origin, enabling teams to resolve underlying problems rather than just symptoms, preventing future occurrences.
- Classification and tagging: Organizes log data by categorizing events and assigning tags, making filtering and analysis easier and more accurate.
- Automated alerts and proactive analysis: Uses algorithms to monitor logs continuously and alert administrators to real-time potential issues, enhancing security and operational readiness.
Organizations using advanced log analysis techniques increased their ability to detect and mitigate cyber threats by 40 percent, according to a McKinsey survey.
Benefits of Log Analysis
Conducting log analysis is crucial for maintaining a secure, efficient IT environment. Continuous monitoring and proactive analysis enable swift threat detection and response. Robust log analysis tools enhance security, ensure compliance and improve performance. While automated systems handle a significant portion of log analysis, human intervention remains crucial. Systems generate alerts, but human expertise is necessary to interpret these alerts and take appropriate actions. Educating non-engineers about the importance of log analysis helps leaders make informed decisions and allocate resources effectively.
Log Analysis Use Cases
Proactive vs. Reactive Analysis
Effective log analysis involves both proactive automated systems and reactive human intervention. Proactive analysis is managed by computerized systems that continuously monitor and analyze logs, alerting administrators to potential issues in real time. For example, if a user fails multiple times to sign in, the system locks the account or notifies administrators of suspicious activity, ensuring a swift, efficient response.
When a security breach or data anomaly is detected, cybersecurity teams use log analysis tools to identify the problem through filters and queries. These capabilities reduce the volume of data needing manual review, allowing teams to focus on the most relevant logs and trace the root causes of issues. While proactive systems handle most immediate threats, human expertise is crucial for investigating and resolving complex issues.
Compliance and Financial Impact
Compliance with regulations such as General Data Protection Regulation (GDPR) and Health Insurance Portability and Accountability Act (HIPAA) demands careful log analysis. These regulations require organizations to maintain detailed data access and transaction records to protect sensitive information and ensure accountability. Proper log retention settings are essential to meet requirements and avoid legal issues.
A report by IBM states that the average 2023 data breach cost $4.45 million, emphasizing the financial impact of inadequate cybersecurity. Automated log analysis tools enhance security by providing real-time alerts and comprehensive insights, helping organizations stay ahead of potential threats and meet compliance requirements.
Log Analysis in Software Development
Incorporating log analysis in software development is critical for troubleshooting, improving processes, and supporting continuous integration and deployment (CI/CD). When errors occur, logs provide detailed information to identify causes. Filters and queries enable developers to focus on specific logs, such as errors or performance issues, allowing quicker, more accurate problem-solving.
Beyond troubleshooting, log analysis helps developers continuously debug and enhance application performance by identifying issues like slow response times or memory leaks. Software bugs cost the U.S. economy $2.84 trillion annually, emphasizing the financial benefits of effective log analysis, according to a study from the Consortium for IT Software Quality.
In CI/CD environments, log analysis monitors changes and their impacts on software stability. Logs help ensure these changes don’t introduce new errors or vulnerabilities each time new code is integrated. By tracking and analyzing logs throughout deployment, teams maintain high software quality and swiftly address issues, ensuring a smooth development pipeline.
Log Analysis Examples
In 2017, Equifax suffered a massive data breach, exposing the information of 147 million people. Investigations revealed inadequate log analysis contributed to the delay in detecting the breach. The attackers had accessed sensitive data for over two months before discovery.
Conversely, in 2013, Target's security team successfully prevented a breach by using log analysis to detect and respond to unusual network activity. Their proactive approach allowed them to isolate the threat and mitigate potential damage, highlighting that low-log analysis can prevent security breaches and address them when they occur.
Log Analysis Tools to Know
Organizations using advanced log analysis tools reported a 30 percent reduction in downtime and a 25 percent improvement in security incident response times, According to a 2023 Gartner survey. Several powerful log analysis tools are available, each offering unique features and benefits.
Splunk: Widely used for handling large volumes of data, Splunk offers real-time search, monitoring, and analysis for detecting security incidents and performance issues.
Datadog: Integrating seamlessly with cloud services, Datadog excels in visualizing log data and setting up automated alerts for quick response to problems.
SolarWinds: SolarWinds focuses on network and infrastructure monitoring, providing deep insights into performance and security with its log analyzer.
Sumo Logic: Sumo Logic offers scalable log management and analytics, using machine learning to detect anomalies and provide actionable insights.
Graylog: Graylog, an open-source platform known for its flexibility and ease of use, supports various log formats with powerful search and filtering capabilities.
Security information and event management (SIEM) systems are also crucial in log analysis. SIEM systems integrate with an organization's infrastructure to collect and analyze logs in a centralized, human-readable format, identifying security events and suspicious activities. This centralized analysis helps maintain robust security postures and comply with regulatory requirements.
Frequently Asked Questions
What is log analysis used for?
Log analysis is the process of analyzing computer-generated records of events in software applications, operating systems and other digital environments. It’s used to identify suspicious activity that allows cybersecurity teams to mitigate a current breach or prevent a future one by patching up vulnerabilities.
What are the benefits of log analysis?
Log analysis allows companies to maintain a secure IT environment. Conducting continuous monitoring and proactive analysis enable swift threat detection and response, while robust log analysis tools enhance security, ensure compliance and improve performance.
What are the common techniques of log analysis?
Effective log analysis employs a variety of techniques to track suspicious computer activity. These include:
- Pattern recognition
- Anomaly detection
- Root cause analysis
- Classification and tagging
- Automated alerts and proactive analysis
You can read the original article posted in Built In by Rhymetec CISO, Metin Kortak.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- Generative AI Security Risks For Businesses: Practical Advice for the Concerned
- Why Cybersecurity Needs to Be a Priority in SaaS Product Design
- The NIST Governance Function: What Businesses Need To Know
You've just had your morning coffee, your Monday is off to a tiring start, and you log into a 9 am Zoom interview to vet a potential software engineering candidate. The candidate looks and sounds a little bit off but he at least seems to know his stuff, and it is a 9 am interview, after all.
You make the hire. On the new employee's first day your security operation center catches them attempting to download intellectual property off of SharePoint they have no reason to access. Upon investigation, it turns out the "employee" is actually an agent of a hostile foreign government attempting to steal intellectual property.
This may sound like science fiction, but something eerily similar just happened to the security awareness training company KnowBe4. Change "hostile foreign power" to "North Korea" and "attempted to download SharePoint files" to "tried to spread malware through the network," and you've just described the highly sophisticated attack carried out by a North Korean advanced persistent threat.
The advent of generative AI has opened up a dramatic range of new cyber options for malicious actors. Spoofed images, identities, videos, and even live calls with perfectly matching voices, are now within the realm of technical feasibility for sophisticated actors and will likely soon be for even remarkably unsophisticated threat actors.
We are very close to losing the ability to trust what we see and what we hear online. For businesses, the time to implement measures that mitigate generative AI security risks is now.

Security Controls Have To Keep Up: Think Like The Enemy
We must accept a new world where anything digital can be effortlessly faked, and ongoing geopolitical turmoil blends into cyberespionage. The proliferation of generative AI security risks requires a fundamental rethinking of the role of cybersecurity in an organization.
So, what is needed to meet this new reality with confidence?
Security Must Be A Function Of Corporate Governance
Security can no longer be an afterthought or a sub-department of information technology.
Instead, it needs to be a board-level topic and C-level function. Fortunately, many organizations and institutions are rapidly coming to this realization. For example, the NIST CSF V2.0 factors this in with its new governance function.
The NIST governance function stipulates that:
- Executives take on an active role in organizational risk management and collaborate on how potential cybersecurity gaps across the organization may impact broader objectives.
- Regularly hold dialogue among executives about risk management strategies, roles, and policies.
- Establish security goals tailored to the industry and organization at the executive level.
- Document and communicate security policies and expectations down the line to managers and individuals.
- Encourage collaboration at the executive level and across the organization about risk management strategies, including cybersecurity supply chain risk.
- Ensure cybersecurity risk management is explicitly rolled into overall Enterprise Risk Management (ERM).
The bottom line is clear: NIST recommends organizations build a culture of security, starting at the top.
Employee Vetting Is Increasingly Important To Combat Generative AI Security Risks
The rise of remote work since COVID has been enormously beneficial to many companies, individuals, and families, but it brings its own set of information security challenges.
Remote work is fantastic (Rhymetec is a 100% remote company!), but if you handle sensitive data or have sensitive intellectual property, it's likely you need to do more extensive vetting of workers you haven't met before. This includes taking proactive measures such as:
- Requiring all new hires or contractors with access to data to undergo extensive background checks (SOC 2 lists "evaluating individual backgrounds" as a requirement which is typically met with a background check).
- Consider requiring an in-person interview component for senior hires or those who will have access to particularly sensitive data.
- Conduct open-source research on potential hires. Do they have a digital footprint? Do their social media accounts check out? Is their information consistent across employment documentation and other sources?
- Conduct detailed background checks with former employers, including live phone conversations.
- Consider hiring only in known locales where you will have an easy time verifying employment history and background (for example, Rhymetec only hires U.S.-based staff).
While these measures aren't foolproof (unfortunately, nothing is 100%), they dramatically reduce your organization's risk of hiring a potential bad actor or foreign agent.
Train Users On Generative AI Security Risks and Threats
It is now trivially easy to clone an individual's voice, create a highly personalized phishing email, or digitally alter images. However, many employees may not be aware that additional caution is needed when virtually meeting outside parties for the first time or taking phone calls that are allegedly from work colleagues.
Consider conducting specific training for your organization on how generative AI can be used for advanced impersonation techniques. This is a critical measure you can take to secure your remote workforce.

Practice The Principle of Least Privilege
It's likely that in the relatively near future, individuals and companies will be regularly targeted by generative AI-enabled attacks.
From spear-phishing emails to voice cloning, it is a natural technology not only for nation-states but also for ordinary cybercriminals to leverage to carry out more effective attacks and thefts. To be realistic, some percentage of organizations (even those practicing good security!) will be compromised as a result.
The principle of least privilege and data segmentation is a critical facet of an effective defense. Data breaches can never be 100% prevented, but you can minimize the risk and mitigate the damage. NIST defines the principle of least privilege as:
A security principle that a system should restrict the access privileges of users (or processes acting on behalf of users) to the minimum necessary to accomplish assigned tasks.
Implementing the principle of least privilege dramatically reduces the risk of a major breach or other successful cyberattack against your organization due to generative AI security risks and other threats.
Follow A Framework or Standard
We've talked a lot about reducing the risk of generative AI threats to your business, and that is important. But in reality, many organizations today aren't doing the bare minimum to protect accounts. GenAI deepfake voice phishing attacks are scary, but so are threat actors leveraging leaked credentials to simply log in to vulnerable accounts.
Rhymetec has extensive experience helping organizations meet a diverse range of cybersecurity standards and frameworks that are designed to maximally reduce the risk of major cyber events affecting your organization while minimizing disruption to core business practices.
Generative AI security risks include AI-enabled phishing attacks, deepfakes, voice spoofing, data poisoning, and automated cyberattacks. You can vastly reduce the risk of these threats by implementing an information security standard with gold-standard measures like employee training, patch management, data encryption, multi-factor authentication, and thorough vendor and employee vetting.
We recommend choosing an information security standard, requirement, or framework to meet, such as:
- SOC 2
- NIST 800-53
- ISO 27001
- NIST CSF V2.0
Frameworks and standards can help guide your organization in building an effective cybersecurity posture that reduces the risks of data breaches, ransomware attacks, insider threats, and, yes - deepfakes.
Approach Vendor Selection Strategically
It's just as important to vet your potential vendors as it is to vet potential employees.
Many businesses nowadays opt to outsource their cybersecurity by working with a Managed Security Services Provider (MSSP) instead of hiring an in-house security team. Additionally, outsourcing complex services like penetration testing is the norm.
The following questions can help guide your decision when evaluating potential vendors:
1. Where is the vendor's team based?
Location can influence their expertise on regional or industry-specific regulations.
2. Who exactly will be carrying out the work for you?
Are they permanent staff or contractors? Permanent staff may provide greater consistency and accountability compared to contractors. Be aware that some MSSPs do outsource a large portion of their services, so it's critical to ask this question.
3. What are the team's credentials and prior experience?
Ask for specific information, examples, and case studies that showcase their past projects and qualifications.
4. How much time will be allocated to this project?
Asking about the time commitment, particularly for services like penetration testing, helps form a complete picture of how comprehensive the project will be.
5. How will the final report work, if applicable?
For services like penetration testing, internal audits, and phishing testing & training, ask how the findings will be presented to you. This could give you a better understanding of where potentially sensitive information would be stored and who may have access to it.
Do they have a dashboard with an easy-to-navigate UI for you? Will you be provided with a detailed report conveying the findings and corresponding recommendations? Will you be given regular updates throughout the project or only a final report? Regular updates can be important for offerings like phishing testing services.
6. Do they outsource any services internationally?
If so, to where? A vendor's control and oversight of the process may be impacted if they are outsourcing a large portion of the work, and different regions may have different regulations and standards. How does the vendor ensure quality and security despite outsourcing?
These are important questions to ask, especially when thinking about generative AI security risks.

In Conclusion: The Importance of Employee and Vendor Vetting In the Age of Generative AI Security Risks
Extremely thorough vetting of potential vendors and employees is absolutely essential as a proactive security measure, particularly with the advent of generative AI security risks.
No security program can ever be 100% foolproof, but fortunately, there are many measures you can take to substantially reduce risk. Hopefully, this guide provided actionable recommendations and strategic questions to ask as you are considering vendors and vetting employees.
As a fully remote company for nearly a decade, our team at Rhymetec has ample experience implementing these strategies and can provide further guidance. We act as a part of your team to provide fully managed services in areas including risk management, employee vetting and training, continuous monitoring, compliance automation, cloud storage security, and more.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
About the Author: Justin Rende, CEO
Justin Rende has been providing comprehensive and customizable technology solutions around the globe since 2001. In 2015 he founded Rhymetec with the mission to reduce the complexities of cloud security and make cutting-edge cybersecurity services available to SaaS-based startups. Under Justin's leadership, Rhymetec has redesigned infosec and data privacy compliance programs for the modern SaaS-based company and established itself as a leader in cloud security services.
Interested in reading more? Check out more content on our blog.
Businesses of all sizes handle sensitive data, including customer information, employee records, and proprietary information. In today's world, there are millions of options for protecting that data from cyber attacks—firewalls for protecting corporate networks, anti-malware tools for identifying and blocking malware, penetration tests for exploiting vulnerabilities before attackers do, intrusion detection and prevention systems for monitoring and preventing security incidents.
There is only one risk that cannot be prevented by security systems, regardless of how sophisticated they are: people.
The Need For Cybersecurity Awareness
Errors made by uninformed staff pose one of the biggest risks to organizational cybersecurity. Employees who lack proper training often unwittingly open the door to cybercriminals through seemingly innocent actions, such as clicking on phishing emails or mismanaging sensitive information.
The consequences of such vulnerabilities can be devastating. A 2023 report by IBM shows the average data breach cost has soared to $4.45 million per incident, the highest in the 17-year history of IBM's report. These breaches can result in substantial financial losses, erode customer trust, and lead to legal ramifications and long-term reputational damage.
Providing Effective Cybersecurity Awareness Training
Successful cybersecurity awareness training prepares employees to defend their organizations against evolving threats. Here are a few proactive strategies leaders can implement into their employees' cybersecurity training:
1. Deliver Comprehensive Phishing Training
Phishing remains one of the most prevalent methods cybercriminals use to get unauthorized access to sensitive information. Deceptive emails mimic legitimate communications to entice users to click on malicious links or attachments.
For instance, the 2023 Microsoft Azure data breach used a phishing attack to target mid-level and senior Microsoft executives for financial fraud and data theft. Train your employees to recognize and avoid these tactics, and to report them whenever possible.
2. Perform Regular Security Assessments And Testing
Your organization's security infrastructure requires regular security assessments to maintain integrity. Penetration tests and vulnerability scans help identify and address security weaknesses before attackers can exploit them.
For example, routine testing at a financial institution could reveal previously unknown entry points in its network, allowing the company to fortify its defenses and prevent intrusions such as the breach experienced by Equifax in 2017.
3. Adapt Training To Technological Advancements
Keep your organization's cybersecurity training up to date with the latest threats and technological advancements. Use artificial intelligence (AI) and machine learning tools to simulate real-time cyber-attacks. Give employees practical, hands-on experience in responding to threats, to ensure they understand theoretical concepts and can apply practical skills in real-world scenarios.
Facing Challenges In Implementing Training
Implementing effective cybersecurity awareness training is fraught with challenges ranging from financial constraints to employee resistance. These issues can hinder the development of a security-conscious culture within an organization.
Budget Constraints
Many companies struggle with budget limitations, making it difficult to allocate sufficient funds for comprehensive cybersecurity training programs. Although global cybersecurity spending is expected to reach US $273.60bn by 2028, businesses often allocate only a minimal portion of this budget to employee training. This underfunding results in inadequate knowledge, leaving employees ill-equipped to handle new cyber threats.
Educating upper management on the risks facing your organization may encourage them to allocate more funds to cybersecurity. Highlighting past cybersecurity incidents and their financial implications on businesses similar to yours in size or industry can underscore the value of proactive investment.
Employee Resistance
Resistance to cybersecurity awareness training is another significant hurdle, often due to a lack of understanding of its importance. Employees may view these sessions as disruptions rather than as crucial investments in digital safety. This issue is compounded by many workers not fully engaging with the training material, and companies frequently failing to verify learning retention.
To combat employee resistance, make your training programs engaging and relevant to employees' daily tasks. Simulating real-life scenarios and incorporating gamification techniques can increase engagement and make learning more impactful.
Threat Complexity
Continuously evolving cybersecurity risks mean companies must regularly update training content and methods. Organizations must remain vigilant and proactive, allocating significant resources to keep training programs aligned with the latest threats. Invest in advanced training tools that use AI and machine learning to simulate real-time attacks and provide your employees with practical, relevant experience.
Fostering a culture of continuous learning helps maintain high levels of awareness and preparedness among staff. Sound strategies include regularly scheduled updates, security drills, and the integration of real-world scenarios into training sessions.
Reducing Vulnerability Through Education
As the risks of becoming a cybersecurity attack victim increase, the need for training and awareness also rises. Effective education equips employees with the tools to recognize and respond to threats. It also fosters a culture of cybersecurity awareness that infuses all levels of the organization. By proactively safeguarding sensitive information, your organization will maintain the trust of clients and stakeholders.
Invest in continuous and effective cybersecurity training programs to ensure your workforce can deal with current cyber threats and adapt to future challenges. Emphasize the necessity of targeted training, realistic simulations, and ongoing education that can reduce vulnerabilities and enhance your organization's security posture, boost resilience, and support future success.
You can read the original article posted in Fast Company by Rhymetec CISO, Metin Kortak.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering.
Under Metin’s leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business.
Interested in reading more? Check out additional content on our blog:
- Maximize Your Use of Compliance Automation Platforms
- Cybersecurity For Startups: A Rhymetec Guide for 2024
- Security vs. Compliance? A False Dichotomy
New business registrations are booming, according to the U.S. Chamber of Commerce. Starting a business is a mainstay of the American dream, and at least five million new small businesses have been established each year since 2021.
This is great news for our economy but, sadly, startups are a prime target for cybercriminals. According to Verizon, 92% of tactics used by threat actors against small businesses are either social engineering tactics, such as phishing emails, or basic web application attacks. Employees at companies with fewer than 100 workers experience 350% more social engineering attempts than those at large companies. For many, it takes just one incident to put them out of business within six months, making robust cybersecurity critical for survival.
Unique Challenges Face Startups
Startups face unique cybersecurity challenges, primarily because of their limited resources and expertise. They often prioritize rapid growth and innovation over security measures, making them attractive marks for cyberattackers. Most startups have less robust infrastructure than established corporations. They may also lack dedicated security personnel, leaving them vulnerable to data breaches, ransomware and phishing attacks.
Additionally, startups might struggle to comply with cybersecurity regulations due to their evolving nature and the complexity of technology. These factors combine to create a precarious security environment. Although startups can address the challenges by investing in cybersecurity from the outset, the following 7 cybersecurity tips can help you secure your company in the short term.
Seven Practical Cybersecurity Tips for Startups To Implement Immediately
Fortify your startup against cyber threats with these seven practical strategies you can immediately implement to enhance your defenses.
1. Insist on multifactor authentication (MFA). Implementing this protocol helps secure all access points—from the cloud to your network and SaaS. MFA reduces breach risks by ensuring more than a password is needed for access. This measure is crucial to protect against advanced threats such as session replay and SIM swapping attacks.
2. Manage system updates and patch installation. Update your software regularly to keep your startup secure. Automate updates to fix security gaps quickly and reduce the risk of hacks. Focus on patching systems that are exposed to the internet and those with known weaknesses. This helps protect against severe threats and minimizes disruptions to your IT infrastructure.
3. Develop a comprehensive cybersecurity program. This program should include real-time threat detection, structured incident response and robust backup and recovery plans. Prioritize regular risk assessments, use endpoint protection and continuously monitor systems to spot and handle threats quickly.
4. Ensure all employees use strong passwords. Even if you have multifactor authentication in place, encourage the creation of complex passwords combining length, characters and numbers. Use tools like password managers for better security. Regularly monitor and update passwords, especially after data breaches, to prevent unauthorized access.
5. Create clear, written security policies. Establish a cybersecurity foundation for your startup that contains simple, audience-focused language. Regularly update policies to reflect current trends, and clearly explain the reasons behind policies to enhance compliance. Ensure policies include new technologies and regulatory changes to remain effective.
6. Implement backup and recovery strategies. Schedule automatic backups to maintain data integrity and prepare for emergencies. Store your backups in various locations and routinely test recovery procedures to ensure they work effectively when needed. Regularly test your backup and recovery process to ensure effectiveness against natural disasters, ransomware and data breaches.
7. Monitor vendor security diligently. Before you start working with third-party vendors, conduct detailed security assessments to check and manage risks. Set clear security responsibilities in contracts and monitor their compliance to ensure their services don’t weaken your startup’s cybersecurity.
By adopting these practical cybersecurity tips, you can bolster your startup against various cyber threats and help ensure your data and systems remain secure.
No Better Time Than Now
As the number of startups balloons and the shift to remote work continues to climb, there’s no better time than now to integrate these cybersecurity tips into your business model. Establishing good cybersecurity habits helps protect your business against common vulnerabilities. It empowers you to build a strong foundation that can support future growth and technological advancements.
Avoid the scramble to implement cybersecurity measures under pressure. Review your security posture now and take steps to ensure a smoother, more secure expansion as your business evolves.
You can read the original article posted in Forbes by Rhymetec CEO, Justin Rende.
About Rhymetec
Rhymetec was founded in 2015 as a Penetration Testing company. Since then, we have served hundreds of SaaS businesses globally in all their cybersecurity, compliance, and data privacy needs. We’re industry leaders in cloud security, and our custom services align with the specific needs of your business. If you want to learn more about how our team can help your business with your security needs, contact our team for more information.
Interested in reading more? Check out our blog and other articles:
- Maximize Your Use of Compliance Automation Platforms
- Security Questionnaire From A Customer? What To Expect and How To Answer
- Cybersecurity for Startups: A Rhymetec Guide for 2024
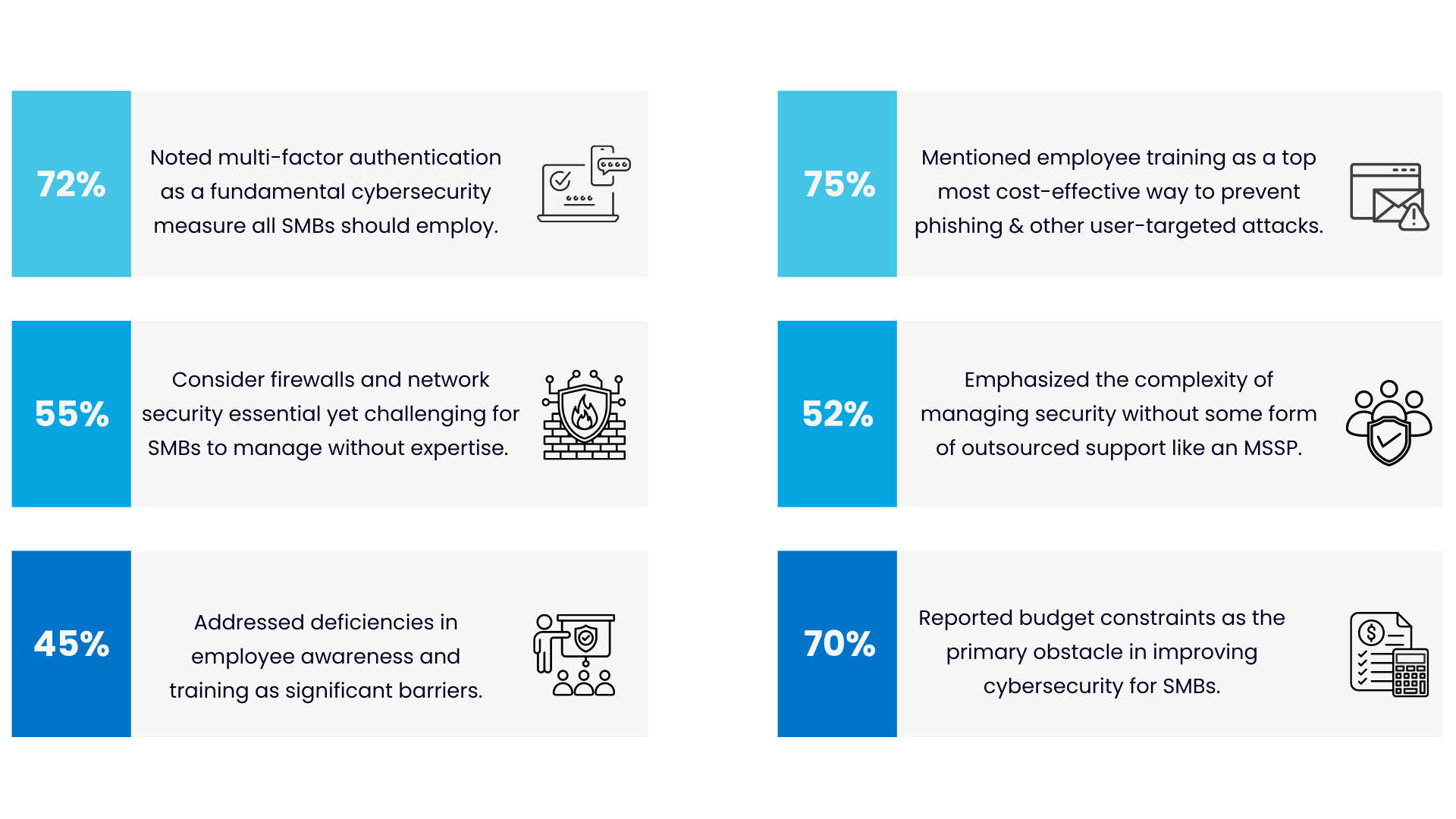
What are the most critical cybersecurity measures for small and medium-sized businesses (SMBs)?
We analyzed over 300 responses from security professionals to find out.
We identified the top 10 most important cybersecurity measures for SMBs, as well as the 5 most common obstacles SMBs face when building out or improving their security program. Using the information from our findings, SMBs can be better prepared to tailor their security program to expert-approved measures and stay ahead of the most common obstacles.
This research brief discusses the importance of cybersecurity for small and medium-sized businesses, our research methodology, results, and evidence-based recommendations. The findings address the following research questions:
- According to security professionals, what are the most critical cybersecurity measures and services for SMBs?
- Which obstacles do SMBs most frequently encounter when building out or improving upon their security program?
We answer these questions (and more), discuss practical implications, and provide 6 ways to balance security with obstacles like budgetary constraints that SMBs often face.
Before jumping in, here are a few of the most interesting findings to highlight:
SMB Cybersecurity Statistics
Data were collected through a systematic search of online cybersecurity forums. Using real-world discussions from online forums in research has several key advantages: The discussions provide a rich source of practical insights based on people's firsthand experiences that are directly applicable to SMBs facing similar issues. Solutions and advice shared in forums are often scrutinized, debated, and validated by the community.
Data analysis leveraged both quantitative and qualitative methodologies to understand the significance of SMB cybersecurity measures and challenges discussed across threads (For more details on data collection and analysis, see the method section).
A thematic analysis identified recurring topics across the discussions, which were categorized into themes to reflect the main ideas and insights. A descriptive statistical analysis quantified the frequency and prevalence of certain terms, concepts, and themes within the dataset.
Results: SMB Cybersecurity Statistics From Over 300 Expert Responses
Here are the top 10 expert-approved cybersecurity measures for SMBs based on our analysis. The following cybersecurity measures emerged as the most frequently mentioned suggestions for small and medium businesses to improve their cybersecurity:
Cybersecurity Measure: % of answers mentioning it as critical for SMBs
- Multi-Factor Authentication (MFA): 72%
- Regular Patching and Software Updates: 68%
- Endpoint Protection (Antivirus, EDR): 65%
- Firewalls and Network Security: 60%
- Security Awareness Training: 58%
- Data Backup and Recovery Solutions: 55%
- Email Security: 50%
- Vulnerability Management: 45%
- Managed Security Services (MSSP, MDR): 40%
- Security Policies and Procedures: 35%
Practical implications and advice for SMBs based on these findings are discussed in the conclusion section.
Top 10 SMB Cybersecurity Measures
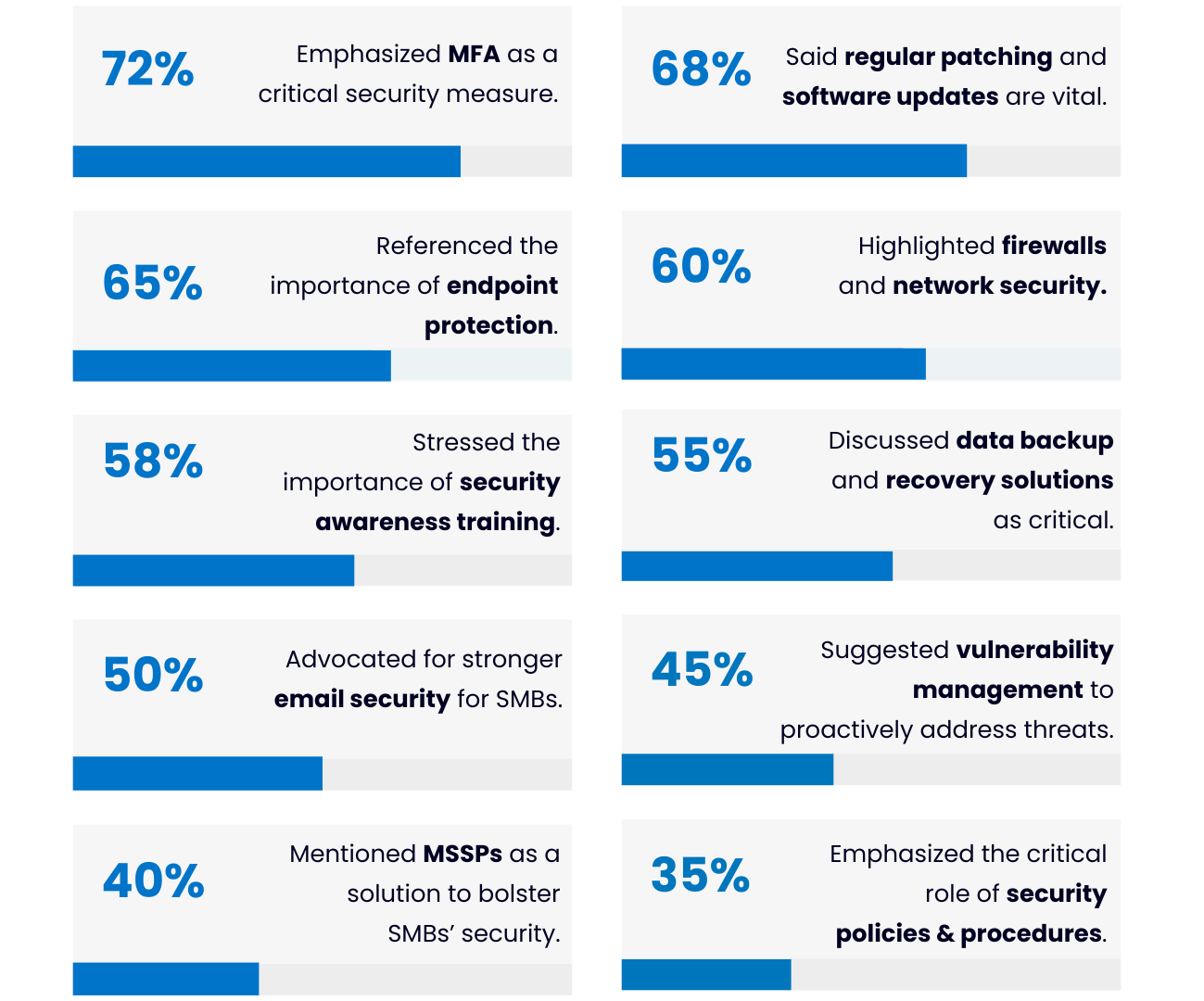
Common Obstacles With SMB Cybersecurity
Many security experts work with a variety of organizations and obtain insights into the specific problems they face based on factors like organization size. The following obstacles that SMBs encounter most frequently when trying to improve security should be kept in mind when implementing and improving security:
Obstacle Faced by SMBs: % of responses mentioning it
- Limited Budget: 70%
- Lack of In-House IT Expertise: 65%
- Complexity of Managing Security Solutions: 50%
- Awareness and Training Deficiencies: 45%
- Scaling Security with Business Growth: 30%
When building out your security program, it's critical to keep these considerations in mind. For example, when drafting security policies for small businesses, there's often a balancing act between security and budget that requires security measures to be tailored to the organization's capacities. Unsurprisingly, budget was the most frequently discussed obstacle:
Top 5 Obstacles For SMBs With Cybersecurity
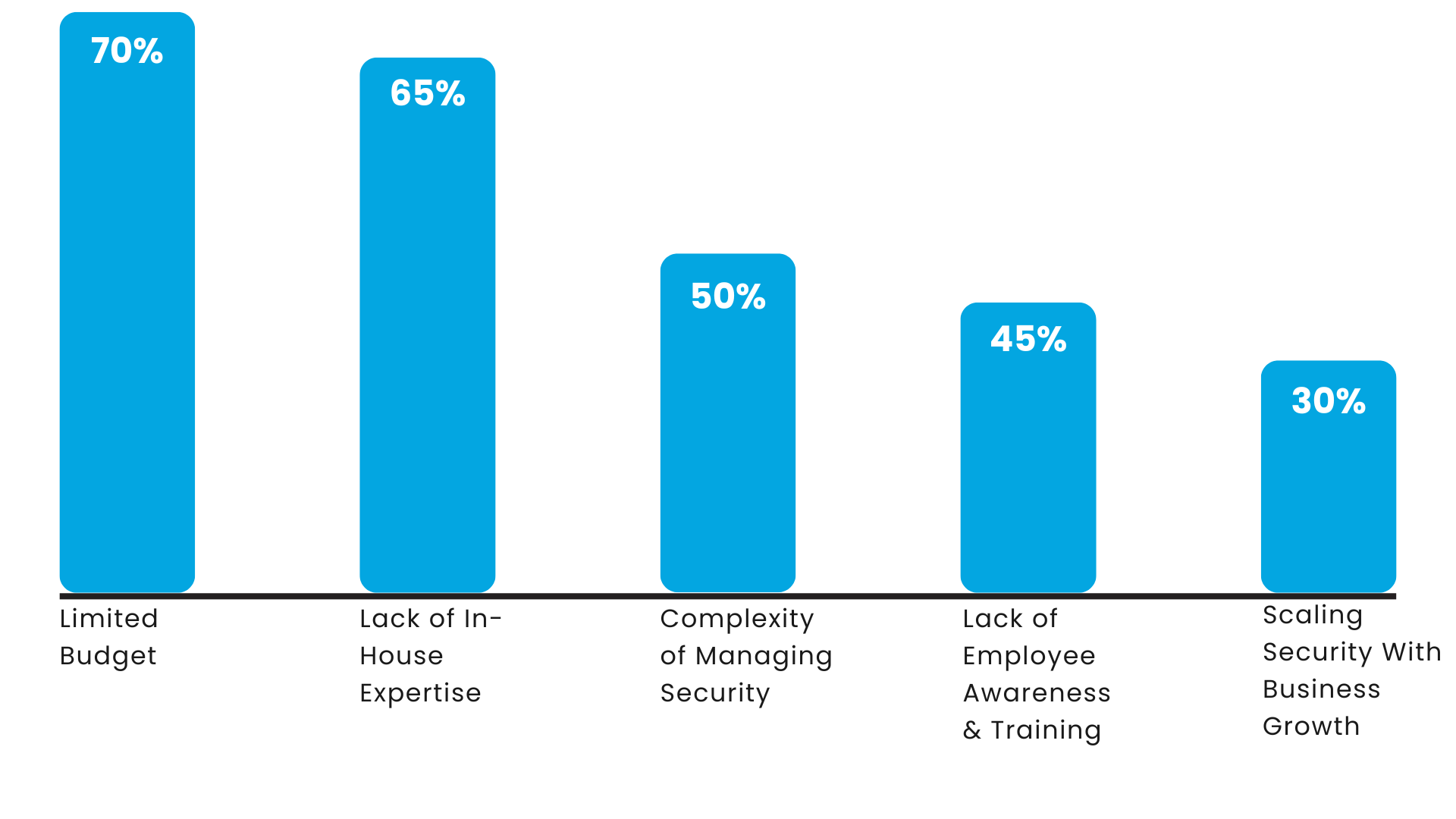
Thematic Analysis: Categorizing Obstacles & Practical Implications
Thematic analysis is used to find common themes and ideas by analyzing how people are discussing a particular topic. The analysis groups similar themes and patterns together to understand what people think and to provide a clear picture of the main points.
The thematic analysis for our research revealed several consistent patterns and recurring topics of discussion across the forum:
Resource Constraints
Limited financial and human resources hinder many SMBs. This impacts their ability to employ security measures, especially more advanced measures that companies handling specific types of data may need.
Rhymetec's Take: There are a range of security measures SMBs can adopt that are both low-cost and effective. For example, enforcing strong password policies for all employees and using MFA are great ways to enhance security without breaking the bank.
Dependence on External Support
The analysis revealed a substantial reliance on external vendors (such as MSSPs) due to gaps in in-house capacity. Outsourcing security was often discussed as a necessary strategy to make up for limited internal resources, especially for more complex security measures.
Rhymetec's Take: Given that many SMBs choose to outsource their security, they should be sure to have a rigorous process for carefully evaluating vendors according to their specific needs. Not all MSSPs are created equally. Many provide surface-level security measures or serve in a purely advisory capacity.
Depending on the type of data organizations handle, as well as security regulations in their industry, more support may or may not be needed. MSSPs that offer solutions like a vCISO service are equipped to provide substantially more hands-on support.
Awareness and Education
There was a continuous emphasis on the importance of security training to help mitigate human error and increase awareness of security risks. The importance of measures like phishing training for employees emerged as a recurring theme.
Rhymetec's Take: Security awareness training plays a critical role for small and medium businesses in preventing phishing and social engineering attacks. Training programs should include simulated phishing attacks, educating staff on the latest and most relevant security threats, and teaching safe online practices.
Regulatory Compliance
Many SMBs are driven by compliance requirements to improve their security. This fact emerged as a common theme throughout analyzed forums. Compliance with industry regulations such as GDPR, HIPAA, or PCI DSS was mentioned many times as the motivating factor to implement security measures. The language and controls under their selected framework(s), therefore, end up guiding their security policies.
Rhymetec's Take: It is clear from the analysis that for many SMBs, the need to meet compliance ends up driving security instead of the other way around. This is understandable, as SMBs often lack the same in-house resources as larger companies.
Traditionally, compliance is thought of as a "pass or fail" measurement of controls against a standard, whereas security is the management of risk through implementing controls and is measured through control maturity and effective risk mitigation. However, depending on how you choose to approach compliance (for example, the criteria you select under SOC 2), it can lean more toward security.

Needing to achieve compliance can serve as a gateway to truly robust security for many organizations. At the very least, it provides a solid baseline of security to build on.
It's also important to note that implementing even baseline security measures under many regulations (such as MFA, backups, and asset monitoring) vastly improves security if these measures were not previously implemented!
Practical and Cost-Effective Solutions
Discussions often revolved around seeking practical, easy-to-implement solutions that offer substantial security benefits without overly excessive costs. There was a focus on basic yet effective measures such as MFA, firewalls, regular patching, and data backups.
Rhymetec's Take: Resoundingly, MFA was the most frequently mentioned critical cybersecurity measure for SMBs. This aligns with prior security research from Verizon emphasizing the role of the human element in cybersecurity: MFA is the number one way organizations can protect themselves from cyber-attacks. If an organization does not enforce clear MFA policies for all employees, all it takes for a breach to occur is one employee having a weak password that gets identified through password spraying or traditional leaks.
Overall, these results highlight the importance of strategic investments in security measures that are effective and feasible within the constraints that smaller businesses often have.
SMB cybersecurity programs should prioritize foundational solutions that offer the highest ROI, scale with business growth, and strike a balance between effective security and realistic constraints.

Method: Analysis of Online Forums In Cybersecurity
Data were collected through a systematic search of online cybersecurity forums, using search terms including: "cybersecurity for SMBs" and "small business cybersecurity". The following selection criteria were used to choose discussions for analysis:
- Posted in the last 5 years
- Contain at least 3 comments
- Relevant to the research questions
We identified 20 discussions in alignment with the selection criteria, totaling 327 data points (the posts and replies). Discussions included posts asking the following questions to obtain advice from cybersecurity professionals: "Cybersecurity for small-medium businesses?", "Advice for a small business looking to tighten security?" and "Improving security posture as a small business." Each post had an average of 15 comments responding to the question.
Thematic Analysis & Descriptive Statistics
A thematic analysis was conducted following a structured coding process to extract and interpret the data systematically. The raw data were organized into meaningful categories to enable identification of themes and patterns. Initial codes were generated by assigning codes to sections of threads that summarize what was being discussed in the body of the post and subsequent comments.
Codes were refined and merged to better match emerging themes. For example, codes such as "budget constraints" and "financial limitations" were merged into a single code based on their similarity. The textual data were broken down into meaningful parts, each tagged with a code encapsulating the key idea of that part of the text. For example:
- "Phishing risks": Assigned to mentions of phishing as a significant threat and discussions on measures to counter it.
- "Dependence on MSSPs": Tagged when reliance on managed security service providers for the cybersecurity needs of SMBs was expressed.
- "Compliance driven": Used for discussions where regulatory compliance (like GDPR or HIPAA) was a primary motivator for adopting cybersecurity measures.
Next, a descriptive statistical analysis was conducted to quantify the frequency and prevalence of certain terms, concepts, and themes within the dataset.
In Conclusion: Balancing Cost, Complexity, and Effectiveness of SMB Cybersecurity
SMB cybersecurity needs to be manageable and sustainable. It's important to craft a strategy from the beginning that balances realistic constraints with the need for security.
Again, here are the most common obstacles small and midsized businesses encounter with cybersecurity, as revealed by our research:
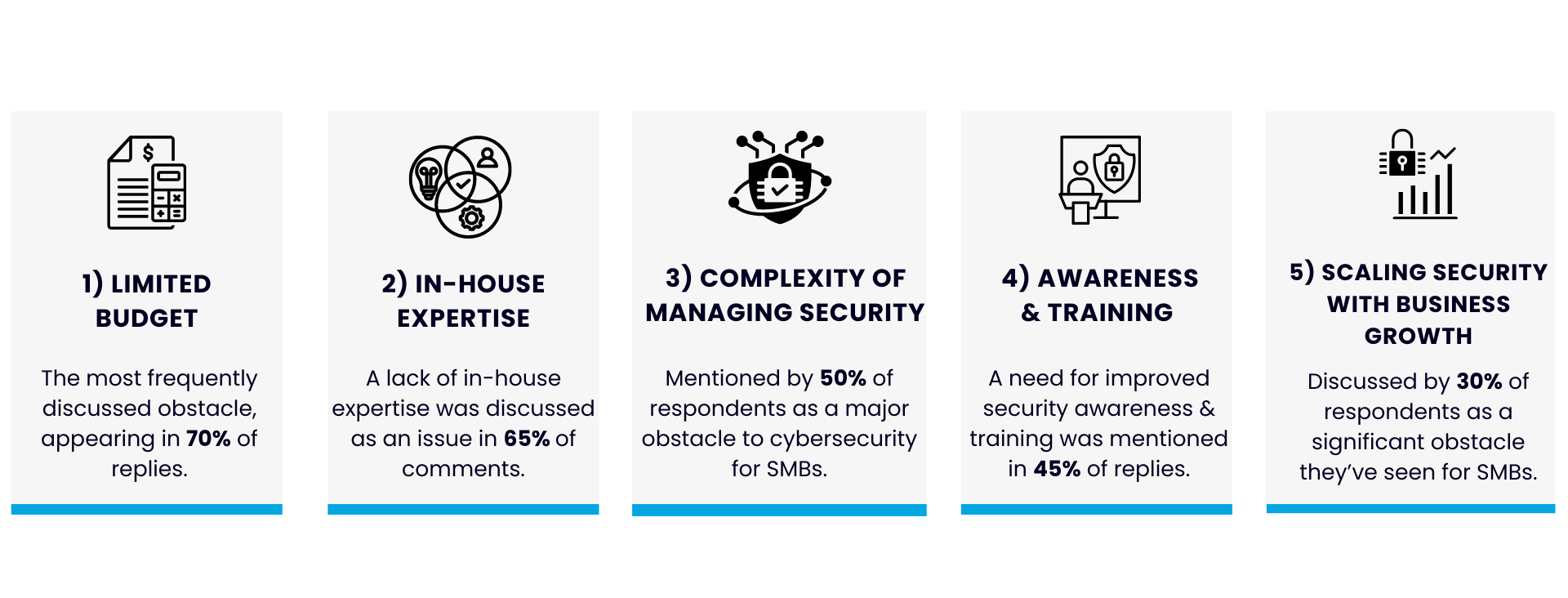
The 6 pieces of advice below strike a balance between these realistic constraints while prioritizing security measures that are effective and yield the highest ROI.
The major takeaways from this research include the following advice for SMBs:
1. Prioritize Cost-Effective Security Measures
Focus on controls such as MFA, enabling backups, and regular patching that are relatively low-cost and high-reward in terms of security benefits.
2. If Possible, Get The Basics Right From The Beginning
Have a subject matter expert draft your security policies. It's important to bake security in from the very beginning (or as soon as possible) so your security program can grow seamlessly with your business.
It's much harder to go back later and expand upon your security program and policies when your business has grown substantially and has more assets.
3. Conduct A Cost-Benefit Analysis
Evaluate the financial implications of cybersecurity investments against the potential costs of data breaches, considering both direct and indirect costs like reputational damage and legal fees.
4. Invest In Employee Training And Awareness
Foster a culture where security is everyone's responsibility. Encourage employees to report suspicious activities without fear of repercussions and conduct ongoing security awareness training.
5. Plan For Compliance And Regular Audits
Understand your regulatory requirements and stay informed about any regulations that may impact your industry (such as GDPR and HIPAA). The legal and regulatory compliance requirements relevant to your organization change.
Managed compliance services can help you stay ahead of this and continuously ensure you are meeting all relevant requirements. Conducting regular security assessments can also help identify gaps in security and improve weak areas before they can be exploited.
6. Embed Cybersecurity Into Business Strategy
This last piece of advice is critical for company leadership.
Leadership should ensure that cybersecurity is a top priority from the highest levels of the organization. Additionally, it's good practice to align business goals with cybersecurity. If security considerations are baked into overall business goals and strategies, it helps foster an environment that continuously seeks to prioritize and improve security as risks to your organization change.
Hopefully, this research report helped provide evidence-based recommendations that are both practical and effective for SMBs. In summary, here are the 6 expert-approved ways for SMBs to balance effective security with budgetary and personnel constraints:
6 Evidence-Based Tips For Effective SMB Cybersecurity
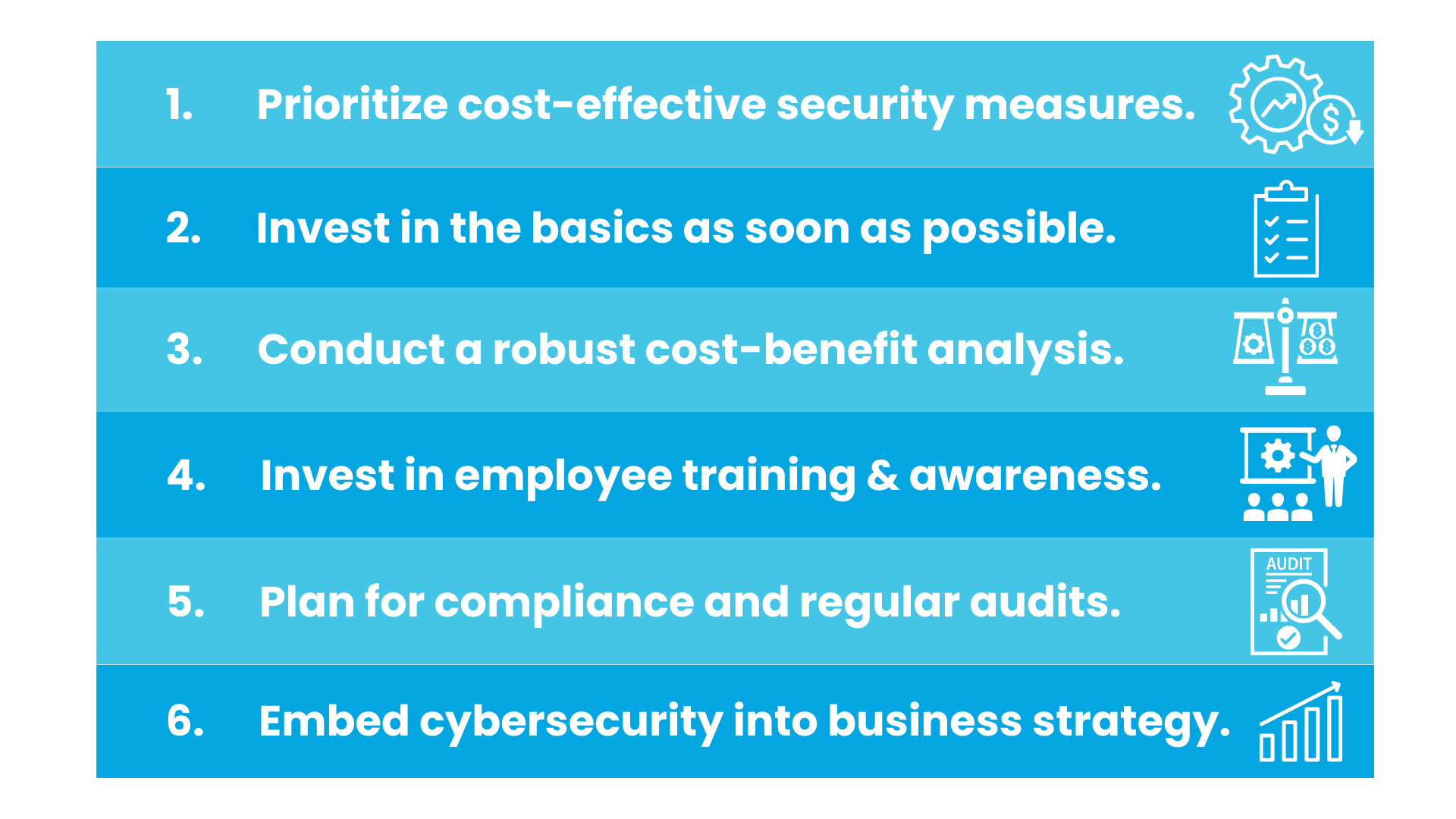
How Rhymetec Provides Effective & Practical SMB Cybersecurity Solutions
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget.
We enable our clients to outsource the complexity of security and focus on what really matters – their business. If you are interested in our services or if you have questions about security, contact our team for more information.
Interested in reading more? Check out additional content on our blog.
An incident response policy is a comprehensive plan for the role of personnel and technologies in the aftermath of a cybersecurity incident. The primary goal is to minimize damage, contain threats, and quickly restore normal operations. The policies should be specific, tailored to the types of assets your organization has, and crafted according to best practices as laid out by entities like NIST.
Ever received a lengthy security questionnaire from a potential customer?
Your organization's incident response policy is one area that security questionnaires may focus on. Here are several questions you may find on a security questionnaire on this topic:
- Does your organization have documented incident response plans and processes?
- How quickly do you aim to respond to security incidents, and what factors influence your response time?
- What roles and responsibilities are defined within your incident response team?
- Can you outline your process for containing and mitigating security incidents?
These are just some of the questions you may see on a lengthy security questionnaire. Additionally, under SOC 2, Incident Response & Business Continuity/Disaster Recovery appear throughout the criteria all organizations must meet (the Common Criteria) regardless of the selected Trust Services Criteria.
This article will give you the tools to develop a robust incident response policy or to assess the strength of your existing policies and ensure they will hold up under scrutiny from potential customers, partners, and other stakeholders.
What Is The Role of An Incident Response Policy?
There is an asymmetry between attackers and defenders.
Even organizations that spend tens or hundreds of millions of dollars on cybersecurity can be breached. Building a cybersecurity program based on the warfare principle of defense in depth is absolutely critical, and so is planning for when it fails.
A robust incident response policy and planning exercises should equip your team, your executives, and your board to deal with a range of potential incidents and scenarios if the worst happens. An incident response policy provides a plan to carry out a set of concrete and specific actions that your organization will take to manage the aftermath of a major security incident.
Security incidents can come in many shapes and sizes. An employee losing a laptop in an airport with customer data is a security incident, and so is a ransomware group exfiltrating ten terabytes of data. The difference is in scale. Your incident response plan should serve as a business enabler that allows you to react quickly in the event of both small and large security incidents.
Big Picture Elements of Your Incident Response Policy
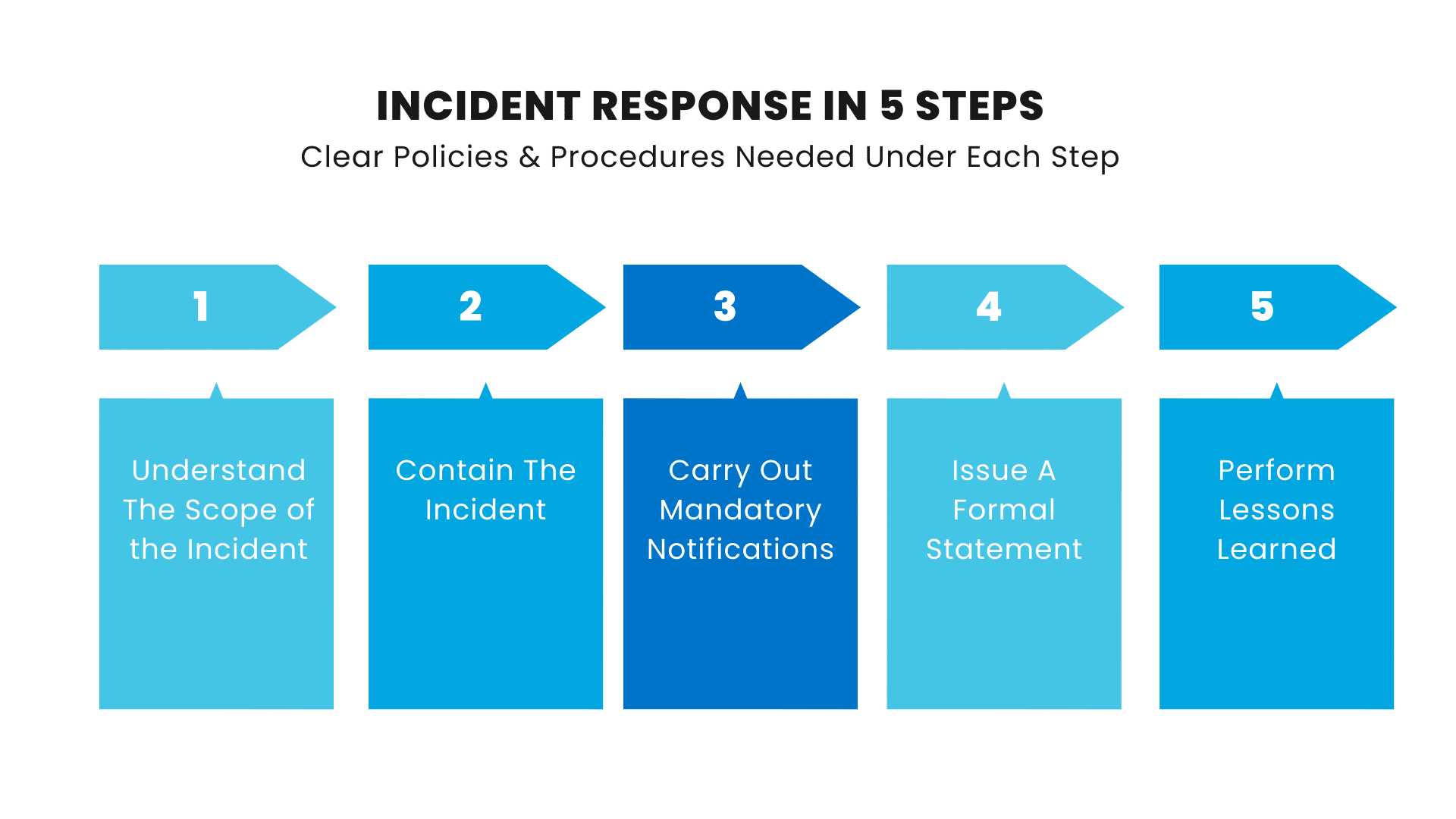
An incident response plan should be comprised of a set of policies and procedures that provide a clear game plan for:
1. Understanding the scope of the incident: The first and most important question to answer during an incident response process is to get a handle on the scope. Is customer data affected? Is employee data compromised? What IT systems or infrastructure is affected? What else could be affected? What core business processes do the IT systems enable? These are just some of the myriad of questions that need to be answered early.
2. Containing the incident: Your incident response plan should also spell out specific policies that will guide how you contain the incident. Critical systems may need to be shut off - who is responsible for making the decision? What is the backup plan if, for example, your company's CRM is unavailable for an extended period of time? These types of questions around incident response planning need a robust and coherent answer.
3. Notification: All 50 U.S. states have data breach notification laws, requiring companies to notify consumers when their data has been stolen. In addition, organizations such as the U.S. Securities and Exchange Commission have regularly implemented new rules requiring financial institutions to notify them of a breach within 24 hours.
4. PR and Communication: For a severe enough event, particularly one that falls under notification requirements, it is likely that you will need to issue a formal statement. We recommend being clear, concise, and not attempting to hide or obfuscate information. It is a good practice to explain which systems were affected, which types of data may have been compromised - and which types were not compromised - in addition to any recommended actions for customers or others who may have had sensitive data exposed.
5. Lessons Learned: After an incident is resolved, you should perform lessons learned. Ask questions like: How did the plan work? Were there any failures or portions that weren't adequately carried out? Was it clear who was responsible for each piece of the incident response process?
Putting Your Incident Response Plan Into Practice
Incident response plans are only as valuable as the amount of damage they mitigate in a real-life incident. At Rhymetec, we recommend doing tabletop exercises. Schedule time every year to practice going through an imagined incident in order to understand how well your plan works in practice. This gives your team hands-on practice in reacting to real-life incidents, quickly getting a grasp on what has been compromised, and examining which systems and core business functions will be compromised.
During incident response planning exercises, it's also important to involve different stakeholders across the organization that may be impacted by sudden outages or other problems. Test out different scenarios to better understand which systems are essential for the business to continue to operate with and which controls might fail in the event of a real incident.

Let's go over the phases of an incident response plan. Here's what you should do before an incident, during an incident, and after an incident:
Before An Incident: Pre-Conditions For Effective Recovery
Not all incident response teams are equally effective. NIST regularly publishes general guidance on cybersecurity event recovery. NIST's special publications serve as a great resource for in-depth incident response steps for malware incident handling and ransomware protection and response.
Here are a few best practices for pre-conditions to enable effective recovery. These are things you should already have in place before an incident occurs and should be continuously updated:
- Recovery Playbook: Create a formal plan with security policies specific to ransomware or malware attacks (note that security policies for small businesses are just as important as they are for larger companies). A clear plan should be set forth for communication with backup and recovery teams, company management, law enforcement, other stakeholders, and PR. Maintain a list of all personnel and technology to be involved in the recovery process.
- Regular Training: Conduct regular drills for team members to ensure everyone is ready to react in the event of an incident and to refine the recovery process.
- Critical Asset Mapping: Maintain up-to-date inventories of all hardware, software, and data assets. This involves maintaining security dependency maps that prioritize restoration. Keep an ongoing, updated list of resources ranked by priority that are required to keep things running across the organization.
- Preventative Security Measures: Use network monitoring tools to detect suspicious activity and employ endpoint detection and response solutions to notify of potential malware.
- Additional Defensive Security Measures: Use antivirus software, intrusion detection systems, and firewalls. Implement MFA policies and conduct phishing training for employees.
During & After The Incident
Here are a few best practices, again based on the guidelines set forth by NIST, that you can use to make sure you are maximally efficient when responding to a serious IT infrastructure or security incident:
- Determine The Scope: The first step is to confirm the scope of infected systems. Set specific recovery goals for your team in 12-hour increments.
- Containment: Next, isolate infected systems from the network to stop further distribution in the case of malware. Identify and disable any accounts that have been compromised.
- Eradication: Use antivirus or anti-malware tools to remove the malware from infected systems. Patch any known exploited vulnerabilities to protect against future events, and conduct a forensic analysis to understand the scope of the compromise and find any remaining backdoors.
- Recovery: Restore impacted systems and data from backups (after ensuring the backups are not infected with malware), and continuously monitor restored systems for any signs of reinfection. Provide impacted users with access to alternative systems as needed.
- Post-Incident Analysis: Document lessons learned, update the incident response policy based on the experience, and maintain open communication with senior management, IT staff, and legal counsel.
In Conclusion: The Importance of Having A Documented Incident Response Policy
According to IBM, it takes companies nearly 70 days to contain a security incident on average, and only 45% of companies have an incident response plan in place. Going forward, it is important to get that number up across the board, especially for smaller organizations that often lack the same in-house security resources large companies have.
Cybersecurity for startups and SMBs is just as critical as it is for large companies. Organizations are increasingly using similar services and infrastructure, which means companies' attack surface looks more and more similar regardless of size.
Having a plan in place enables organizations to respond swiftly and effectively in the event of a security incident. At Rhymetec, we work closely with our clients to respond effectively to incidents, document the recovery process, and create detailed post-mortem reports based on lessons learned.
About Rhymetec
Our experts have been disrupting the cybersecurity, compliance, and data privacy space since 2015. We make security simple and accessible so you can put more time and energy into other critical areas of your business. What makes us unique is that we act as an extension of your team. We consult on developing stronger information security programs within your environment and provide the services to meet these standards. Most organizations offer one or the other.
From compliance readiness (SOC 2, ISO/IEC 27001, HIPAA, GDPR, and more) to Penetration Testing (Web Application Pentest, API Pentest, External Network Pentest, and Mobile Application Pentest) and ISO Internal Audits/ISO Compliance, we offer a wide range of consulting, security, vendor management, and compliance management services that can be tailored to your business environment.
If you're ready to learn about how Rhymetec can help you, contact us today to meet with our team.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering. Under Metin’s leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
Interested in reading more? Check out additional content on our blog:
- Maximize Your Use of Compliance Automation Platforms
- Understanding ISO 42001 Controls: Implementing and Managing Artificial Intelligence Responsibly
- Phishing Training For Employees: 5 Steps To Success