Meeting NIS2 requirements can be complex regardless of organizational size, especially the requirements around managing third-party risks and incident response. In this article, we go over what NIS2 requires, how to avoid penalties, and how to leverage the requirements to support business growth and operations.
The NIS2 Directive represents another new requirement in an increasingly strict cybersecurity regulatory ecosystem. The law, which came into force in January of 2023, specifically impacts organizations operating in the European Union (EU). Businesses that provide essential or important services must meet the obligations or face regulatory scrutiny.

What Is NIS2?
NIS2 is the EU's updated cybersecurity Directive, expanding on the scope of the original NIS Directive to cover more sectors and introduce even stricter security, risk management, and reporting requirements. If your business provides services in the EU ranging from transportation, banking, healthcare, manufacturing, food production, and more, you are likely required to comply.
The Directive applies to industries including technology, finance, healthcare, energy, and transportation, as well as many digital service providers. Broadly, it requires organizations to implement risk management measures, report significant incidents within 24 hours, and effectively manage third-party risks.
Non-compliance can result in fines of up to €10 million or 2% of global annual turnover, whichever is higher. Compliance impacts not only your regulatory standing but also your contracts, customer trust, and business continuity. Building a compliance strategy early will help avoid last-minute disruptions and potential penalties.
Who Must Comply With NIS2 Requirements?
NIS2 applies to organizations classified as essential or important entities across a variety of sectors. The Directive expands largely on the scope of the original NIS Directive, covering a broader range of industries and lowering the threshold for organizations that must comply.
Essential entities include large organizations in critical sectors where cybersecurity failures could have widespread and serious impacts, such as:
- Energy - Electricity suppliers, gas providers, oil companies, and district heating operators.
- Transport - Airlines, rail operators, shipping companies, and logistics providers.
- Banking - Credit institutions and financial market infrastructure providers.
- Healthcare - Hospitals, clinics, and pharmaceutical manufacturers.
- Drinking Water & Wastewater - Water supply and treatment facilities.
- Digital Infrastructure - Cloud services providers, data center operators, and domain name system (DNS) service providers.
Important entities are medium and large businesses in sectors that are critical but do not require the same level of regulatory scrutiny. These include:
- Manufacturing - Producers of medical devices and electrical equipment.
- Food Production - Businesses that manufacture food and beverages.
- Postal and Courier Services.
- Waste Management Companies.
- Digital Service Providers - Online search engines, marketplaces, and social networking platforms.
- Managed Security Service Providers (MSSPs) - Businesses providing cybersecurity services to other organizations.
It's important to note that both essential and important entities are generally defined as medium or large enterprises, meaning they have at least 50 employees or an annual turnover of €10 million or more. Smaller organizations, however, may still fall under NIS2 if they are critical to a supply chain or if they operate in a high-risk sector.

NIS2 Requirements: What You Need To Plan For
NIS2 entails a range of security and operational requirements, with a particular emphasis on minimizing cybersecurity risks. Below is an explanation of the 5 overarching requirements and what implementing them may look like for your organization.
1. Risk Management & Security Measures
NIS2 requires organizations to take a proactive approach to mitigate cybersecurity risks.
Security measures across areas, including network security, data protection, and system integrity, are required. Here's what this may look like in practice for your organization, particularly if you are a SaaS company:
- Implementing Access Control Measures: Access control measures such as multi-factor authentication (MFA) for all employees and users accessing your platform are required under NIS2. MFA means both a password and app-based token or another second form of verification are needed to log in.
- Enabling Data Encryption Measures: Encrypt sensitive customer data both at rest and in transit. For NIS2, this includes encrypting databases and using TLS (Transport Layer Security) for all data exchanged between clients and your platform.
- Creating A Patch Management Program: Regularly update software and systems to fix vulnerabilities. Additionally, you'll need to implement an automated patching system that ensures no critical updates are missed.
- Conducting Regular Vulnerability Scanning: This requirement entails using automated tools to regularly scan your applications and infrastructure for vulnerabilities. For instance, using tools like Nessus can identify weaknesses.
2. Incident Reporting Obligations
NIS2 mandates relatively quick reporting of cybersecurity incidents in the event they occur. As an example, if you were to experience a breach where an attacker gained access to customer data, you would be required to notify relevant authorities and affected clients within the prescribed timeframe and provide updates on the breach as it is resolved.
In practice, setting up the incident reporting process from beginning to end will likely entail the following for your organization:
- Creating An Incident Response Plan: Internal incident response policies that outline the exact steps to take when a breach occurs, designate a response team, and describe how you will identify the root causes of the breach are required.
- Setting Up Incident Detection Tools: Set up monitoring systems like SIEM (Security Information and Event Management) to detect unusual activity in real-time. Tools like Splunk or Datalog track suspicious logins or data exfiltration are commonly used for this purpose.
- Making A Plan To Follow Compliance with Reporting Deadlines: Lastly, know what your process would be for reporting incidents in a timely fashion to the appropriate authorities and your affected clients.
3. Governance & Accountability
An increasing emphasis on governance is being seen across historically gold standard cybersecurity frameworks such as the NIST Cybersecurity Framework (NIST CSF) with the addition of the NIST governance function. This shift is being seen in recent laws as well, including in the case of NIS2.
In practice, this means that cybersecurity should not be a function of just IT, but a function of corporate governance and should stem from there. Senior management is responsible for making sure that the organization meets NIS2's cybersecurity requirements and that sufficient resources are allocated. Leadership must:
- Appoint Cybersecurity Leadership: Appoint a Chief Information Security Officer (CISO) or designate a cybersecurity lead who will be accountable for ensuring the organization meets NIS2's requirements.
- Ensure Employee Training is Conducted: Employees, particularly those who handle sensitive data, need to be trained in cybersecurity practices and incident reporting procedures. This often takes the form of having mandatory, recurring cybersecurity awareness sessions, phishing training for employees, and/or tabletop exercises.
- Receive Board-Level Reporting: Senior management should regularly receive reports on cybersecurity risks and incidents, and be involved in decision-making processes related to cybersecurity investment. This can take the form of discussing the current cybersecurity posture and resource allocation at quarterly board meetings, for example.
4. Third-Party Risk Management
NIS2 puts the obligation on businesses to manage risks posed by their third-party vendors, especially if those vendors provide business-critical services or have access to sensitive data. A third-party risk management program entails the following elements:
- Vendor Risk Assessments: A vendor risk assessment evaluates the security and compliance practices of third-party providers. This is especially important for vendors that provide services such as cloud hosting, payment processing, or customer support. These vendors and others need to be able to show they meet NIS2's security standards.
- Third-Party Contracts: Contracts with vendors need to define their security obligations (requiring them to comply with certain security standards, report incidents within specific timeframes, and/or undergo audits of their security practices). Your contract for your cloud provider, for example, should outline measures they need to have in place, such as strong access controls and encryption.
- Ongoing Monitoring: Continuously monitoring your vendors. For instance, regularly review their security certifications, check they are staying compliant with relevant laws or frameworks, or conduct periodic assessments.
5. Compliance & Auditing
NIS2 requires maintaining evidence of your cybersecurity practices, with measures such as:
- Internal Audits: Periodic internal audits of security practices to ensure compliance maintenance with NIS2. Internal audits service to verify that measures like encryption and access control are functioning as intended.
- Risk Assessment & Incident Reports Documentation: Keeping up-to-date records of risk assessments, incident reports, and audits helps meet NIS2's governance and accountability requirements.
- External Audits: In some cases, if an organization falls within the essential or important entity categories and is subject to supervisory measures by national authorities, it may be required to undergo an external audit. Some jurisdictions may also require routine external audits for critical infrastructure or high-risk organizations.
NIS2 Requirements: 5 High-Level Requirements

Meeting NIS2's requirements will involve a combination of technical measures, governance practices, and ongoing actions such as continuous monitoring. For organizations like SaaS startups, implementing these requirements ensures you are in compliance with the law and are well-equipped to build a secure platform that protects user data and reduces business risks.
How NIS2 Affects Third-Party Relationships
NIS2 expands security obligations to include third-party vendors and service providers, requiring businesses to manage risks introduced by their supply chain. Practically, this means you must verify that your vendors (including cloud services providers and software vendors) meet security standards and comply with contractual requirements.
With NIS2, due diligence with your vendors' cybersecurity practices is especially important as organizations covered by NIS2 are responsible for security incidents linked to their third parties.
A common way to verify your vendors' security is by requesting to see evidence of their compliance with cybersecurity frameworks and laws relevant to your industry and location. Security questionnaires, audits, and contractual clauses can also be used to clarify your vendors' security practices. However you choose to accomplish this, third-party relationships need to be documented as part of your overall risk management efforts.
Vendor agreements need to set clear security expectations, incident reporting obligations, and liability terms. Due diligence and ongoing monitoring can help identify risks before they lead to regulatory penalties or operational disruptions.

How Do NIS2 Requirements Compare To Other Cybersecurity Regulations In Terms Of Third-Party Risk?
NIS2 places an even stronger emphasis on third-party risk management compared to many other cybersecurity regulations.
Here's how it compares to a few major frameworks:
NIS2 vs. NIS1
The focus on third-party risks is, in fac,t the most substantial change between NIS2 vs. NIS1. NIS1 focused more on internal security measures without expansive supply chain obligations. NIS2, however, expands on the original NIS Directive by explicitly requiring organizations to assess and manage third-party risks.
NIS2 vs. GDPR
GDPR compliance requires third-party risk management in terms of data protection and requires organizations to have contracts with processors handling personal data. NIS2 goes a step further and requires security risk assessments, continuous monitoring, and contractual obligations for security, even for vendors that don't process personal data.
NIS2 vs. ISO 27001
ISO 27001 includes third-party risk management as part of an overall information security management system (ISMS). However, compliance is voluntary. NIS2, meanwhile, mandates risk management practices for third parties and includes enforcement actions for non-compliance.
NIS2 vs. DORA
The Digital Operational Resilience Act (DORA), which applies to financial services organizations, actually has stricter third-party risk requirements than NIS2. DORA requires direct regulatory oversight of critical third-party providers. NIS2 requires strong vendor risk management, but an important distinction is that it does not impose direct regulatory supervision on suppliers.
Where To Start
After you understand whether your organization is in scope and what gaps exist in your current security program, the next step is to develop a compliance plan and begin implementation (see the section above on NIS2 Requirements for what you'll need to plan for).
A popular option for many organizations nowadays is to work with a virtual Chief Information Security Officer (vCISO) at this stage. A vCISO helps translate NIS2 requirements into a plan specifically made for your business. They provide the expertise needed to interpret requirements, assess your risks, and build a compliance roadmap, all without incurring the cost of a full-time security executive or having to build out an in-house team.
Compliance automation tools, which automate risk assessments, track your security controls, and generate documentation, can also vastly simplify the process. Our vCISOs at Rhymetec leverage compliance automation tools on behalf of our clients while also completing all of the manual security work needed to meet requirements.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with over 700 companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.
Penetration testing is one of the most critical and misunderstood security activities for companies. Often, buyers of security services may have difficulty differentiating between penetration tests and vulnerability scans as a result of technical jargon and a lack of clarity from vendors.
Vendors contribute to this confusion by claiming to offer "penetration testing" that, in reality, involves only spending a short time running automated tools. This article explores the differences between a penetration test and a vulnerability scan to clarify how they differ and where each fits into a modern security program.
Let's jump right in with the main differences at a high level:
Penetration Testing Vs. Vulnerability Scanning: 6 Main Differences
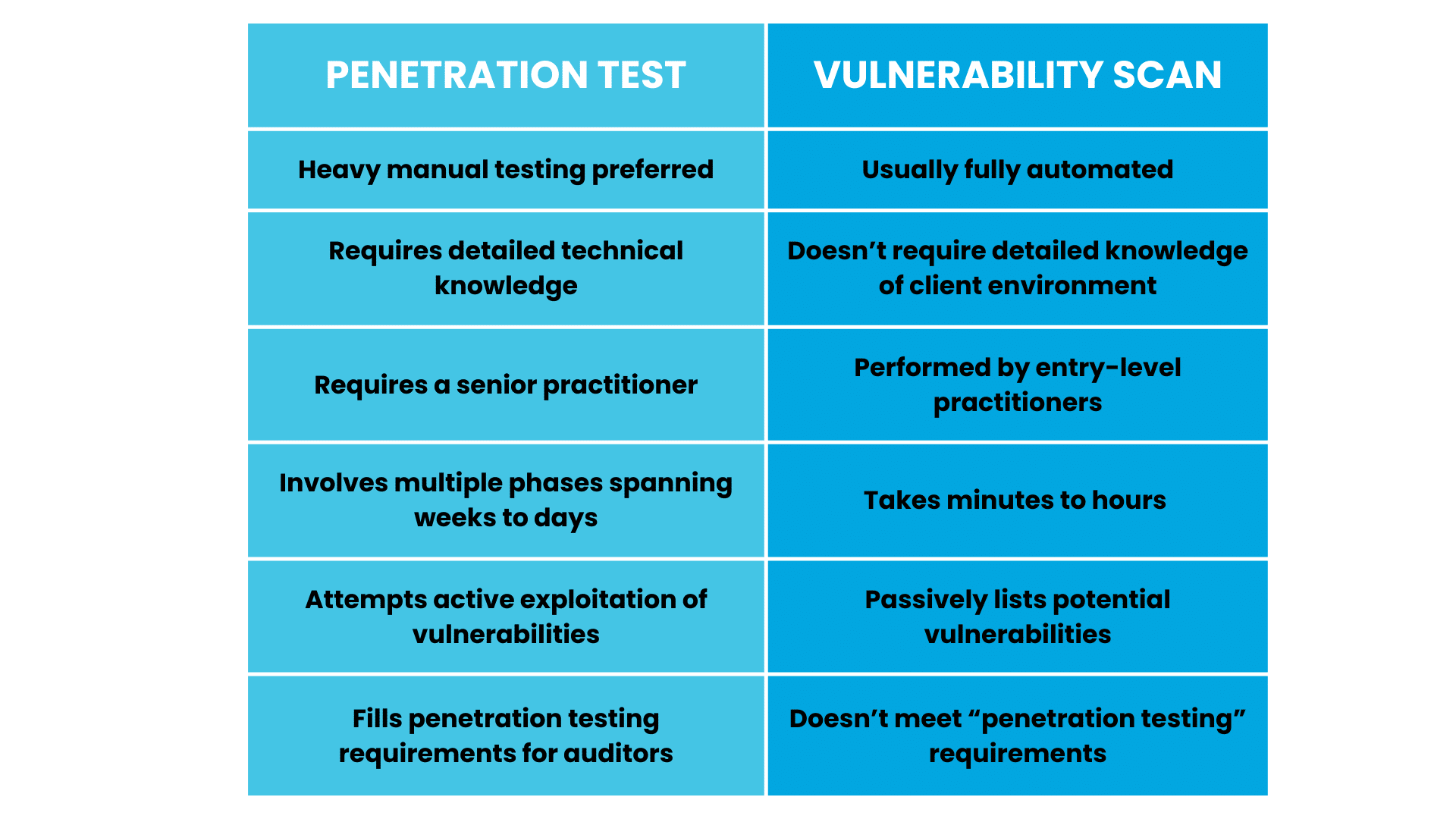
Penetration testing is substantially more involved than vulnerability scanning.
While penetration testing and vulnerability scanning are both important for identifying security risks, they serve different purposes:
Penetration testing is largely manual, requires expert knowledge, and can take weeks. A senior-level practitioner aims to exploit vulnerabilities (just like a real threat actor would do) in order to identify weak points. Vulnerability scanning is mostly automated and needs minimal expertise, but is useful for passively identifying risks on an ongoing basis.
When assessing pen testing vendors, it's critical to know the differences. Some vendors claim to offer "penetration testing" when, in reality, what they are really doing is vulnerability scanning.
Next, let's go over penetration testing vs. vulnerability scanning in more detail to equip you with the information to decide if you need one or the other (or both) for your organization.
What Is A Vulnerability Scan?
Almost all modern software applications have vulnerabilities or weaknesses in the code that can allow an attacker to gain information or privileged access that the software doesn't intend. Major software companies such as Microsoft and Apple routinely deploy patches to both personal computers and to servers to fix identified vulnerabilities.
In their simplest form, vulnerability scans involve using tools like Nessus and Shodan to proactively scan for known vulnerabilities against an IP range to identify unpatched systems and prioritize the highest-risk vulnerabilities.
Vulnerability scans are meant to be run regularly after even minor changes to an organization's IT infrastructure. It's worth noting that threat actors use the same tools as security teams to continuously scan the internet, looking for internet-facing devices with exploitable software vulnerabilities.
Vulnerabilities in Context: Vulnerabilities on externally facing assets (such as hosts and servers exposed to the internet) tend to be more critical than vulnerabilities on computers that are not accessible to the internet. Additionally, not all vulnerabilities are equally risky. Some are "theoretical" in that nobody has actively exploited them before. This type of vulnerability tends to be a lower priority than a vulnerability that is known to be actively exploited by threat actors.
Generally speaking, vulnerability scans can be performed automatically by entry-level team members as the software will automatically identify, prioritize, and report on vulnerabilities. Vulnerability scans do not attempt to exploit the vulnerabilities. They only identify their presence by looking at details such as the source code and software version.
Think of a vulnerability scan like a security guard checking to ensure all of the doors are locked in an office building. Meanwhile, a penetration test is like a skilled lockpicker trying to unlock a door.
What Is A Penetration Test?
The goal of a penetration test is to take the attacker's perspective and actively attempt to gain access to privileged IT systems. The tester will aim to exploit vulnerabilities and leverage exposed servers in order to identify weak points and report on how they did it.
Following up on our security guard analogy, a penetration test involves hiring someone to act as a criminal and try to pick the locks on the building (and the windows, too!). Penetration testing is far more involved, scoped to the individual business, and requires the vendor to have deep expertise.
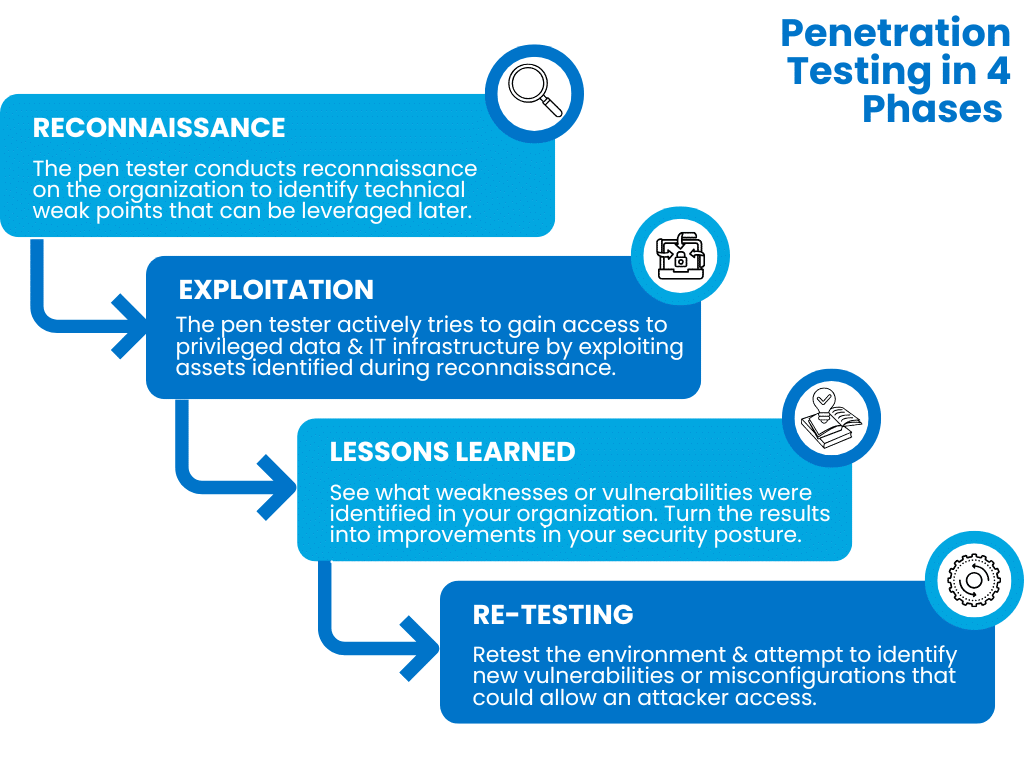
A reputable penetration testing company will work with the client prior to the test, set rules of engagement, and take a multi-phased approach to include:
Reconnaissance: During this phase, the pen tester conducts reconnaissance on the organization to identify technical weak points that can be leveraged later. The pen tester may leverage various proprietary and open-source tools to conduct scanning, identify exposed services, and catalog information to prepare for the exploitation phase.
Exploitation: During the exploitation phase, the penetration testing company will actively try to gain access to privileged data and IT infrastructure by exploiting assets identified during the reconnaissance phase. When successful, a pentester may attempt to move laterally through the network to identify additional resources they can access.
Lessons Learned: This is the most important phase of a penetration test. What weaknesses or vulnerabilities were identified in the target organization? The lessons learned phase is absolutely critical for turning pen testing results into improvements in your organization's security posture.
Re-testing: After a certain period has elapsed, it can be enormously beneficial to retest the environment and attempt to identify new vulnerabilities or misconfigurations that could allow an attacker access.
Security should never be viewed as a one-time fixed event or test. At Rhymetec, we focus on building a continuous security function that proactively meets compliance requirements and identifies gaps in our client's defenses before an attacker does.
Types of Penetration Tests
Penetration tests can be quite varied and are specific to the client's environment.
Rhymetec offers 4 types of testing designed to identify gaps across multiple types of information technology architectures:
- Mobile Application Penetration Testing
- Web Application Penetration Testing
- External Network Penetration Testing
- API Penetration Testing
All types of penetration tests simulate a real attack. They leverage multiple vantage points to attempt to gain access, including exploiting vulnerabilities, but also potentially social engineering, phishing, and even exposed credentials in order to bypass the client's security defenses.
Case Study:
Read the case study on CXO Nexus to see how our penetration testing team at Rhymetec helped them level up their security and compliance, build trust with customers, and improve product development.
Penetration Tests Versus Vulnerability Scans in Context: Compliance
Nearly all major compliance requirements require routine vulnerability scanning and patching. Conducting vulnerability scans is relatively simple and can go a long way toward reducing risk for your organization.
However, for the purposes of compliance, vulnerability scanning is not penetration testing.
Many organizations conduct pen tests solely for the purpose of improving their security posture and uncovering vulnerabilities before attackers do. In many cases, pen tests are required by regulatory compliance requirements as well. The following compliance requirements mandate a penetration test in order to be audit-ready:
- FedRAMP: Requires cloud service providers to conduct penetration tests.
- PCI DSS: Some levels of PCI DSS require a penetration test once per year for most organizations that handle credit card transactions. It can also be required biannually for service organizations that handle credit card transactions and who segment their network to protect cardholder data.
- FISMA: Requires federal agencies to conduct penetration tests and vulnerability assessments on a sampling of their information systems annually.
- NIST's Special Publication 800-53: Requires federal organizations to perform penetration testing under control CA-8.
Companies can also use penetration testing to strengthen their compliance posture and demonstrate proactive cybersecurity to meet other requirements. Requirements that benefit from penetration testing and for which it can be used to fulfill controls (but is not outright required) include:
- HIPAA
- HITRUST
- SOC 2
- ISO 27001
- CCPA
- NIST
- GDPR
We often hear from our customers that although a penetration test is not an explicit requirement under frameworks like SOC 2, their auditors are inquiring about whether or not they've undergone a penetration test.
As the gold standard method of testing the strength of your security, penetration testing adds a strong layer of assurance going into your audit.
Penetration Tests and Security Questionnaires
Almost all compliance requirements and security questionnaires require routine vulnerability scanning. Proactively conducting penetration tests can be an additional high-value way to demonstrate continuous compliance to clients and show that your firm takes security seriously.
Large corporations, in particular, are increasingly requiring potential vendors to answer rigorous security questionnaires. Penetration testing, combined with meeting voluntary compliance requirements such as SOC 2 or ISO 27001, goes a long way toward demonstrating that your organization has a serious security program.
Penetration Testing vs. Vulnerability Scanning FAQ
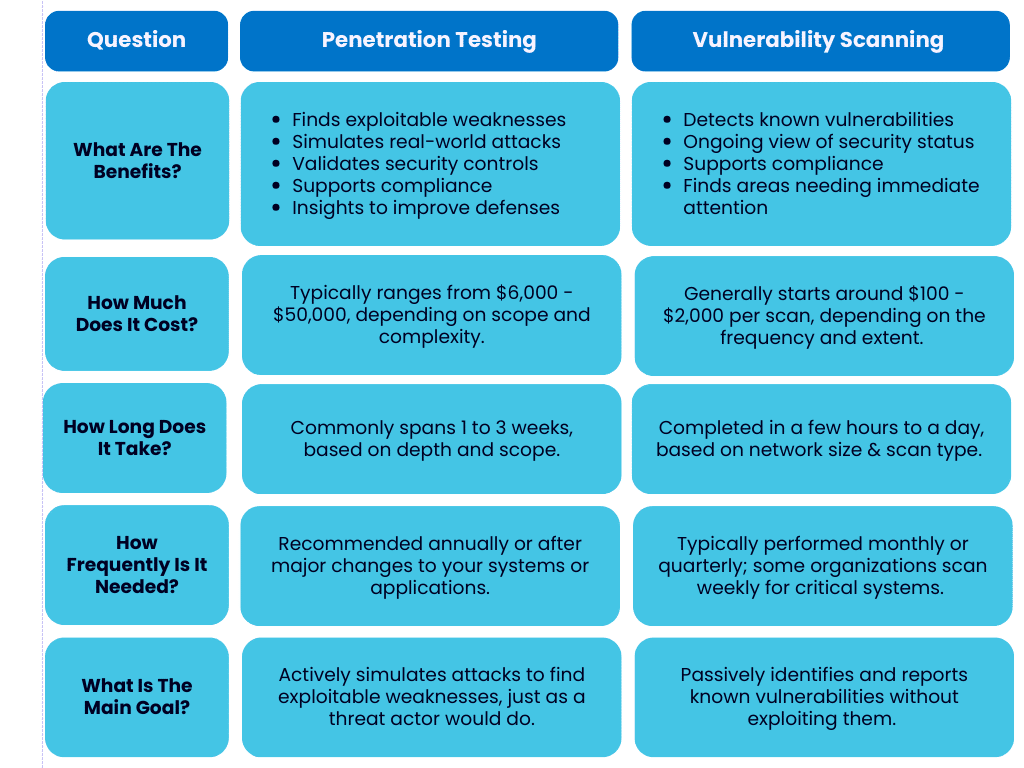
What Are The Benefits of Penetration Testing?
- Identifies exploitable weaknesses in systems.
- Simulates real-world attacks to gauge your organization's response.
- Helps validate security controls.
- Provides practical insights for improving your security defenses.
- Supports compliance with security standards.
What Are The Benefits of Vulnerability Scanning?
- Detects known vulnerabilities.
- Offers a continuous view of your systems' security status.
- Highlights areas needing immediate attention.
- Supports compliance with security standards.
How Much Does Penetration Testing Cost?
- Penetration testing typically ranges from $6,000 to $50,000, depending on scope and complexity.
How Much Does Vulnerability Scanning Cost?
- Vulnerability scanning generally starts around $100 - $2,000 per scan, depending on the frequency and extent.
How Long Does A Pen Test Take?
- A penetration test commonly spans 1 to 3 weeks, based on depth and scope.
How Long Does A Vulnerability Scan Take?
- A vulnerability scan is often completed in a few hours to a day, depending on network size and scan type.
How Frequently Do You Need Penetration Testing vs. Vulnerability Scanning?
- Penetration testing is recommended at a minimum annually or after major changes to your systems or applications.
- Vulnerability scanning is typically performed monthly or quarterly; some organizations scan weekly for critical systems.
What Is The Main Difference Between Penetration Testing and Vulnerability Scanning?
- Penetration testing actively simulates attacks to find exploitable weaknesses, just as a real threat actor would do, while vulnerability scanning passively identifies and reports known vulnerabilities without exploiting them.
Frequently Asked Questions
The Bottom Line: Penetration Testing vs. Vulnerability Scanning
Vulnerability scanning and penetration testing are both critical for your company's security.
We hope at this point it's clear that a vulnerability scan is a single fixed-in-time way to identify unpatched systems that have software vulnerabilities, while penetration testing involves simulating an attacker in a real-life attempt to gain access to your organization's sensitive IT infrastructure.
From an audit perspective, your auditors may expect to see that you've undergone a penetration test. Regular penetration testing will vastly strengthen your security program's credibility with auditors and give your prospects and clients confidence in your security.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering. Under Metin’s leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
Interested in reading more? Check out more content on our blog:
- CISO As a Service: A Scalable Security Solution
- How To Select The Right Pen Testing Vendor for Your SaaS Business
- Security vs. Compliance? A False Dichotomy
The CISO as a service model allows organizations to reap the benefits of an in-house CISO without the need to make a full-time hire. This model can be particularly helpful for startups and small to mid-sized companies that need CISO-level guidance but may not have the resources or demand for a full-time executive. Feel free to contact our team for more information specific to Rhymetec's CISO services:
CISO As A Service: Definition
Terms like "Fractional CISO" and "vCISO" (Virtual CISO) are often used interchangeably with CISO as a service. They all refer to the same concept: Providing part-time or on-demand security leadership tailored to the needs of your business.
With this service model, companies can outsource the role of a Chief Information Security Officer (CISO) to an external expert rather than hire a full-time executive. Whether in-house or outsourced, CISOs provide the guidance and expertise needed to manage your security and compliance needs.
What Will Your CISO Do For You?
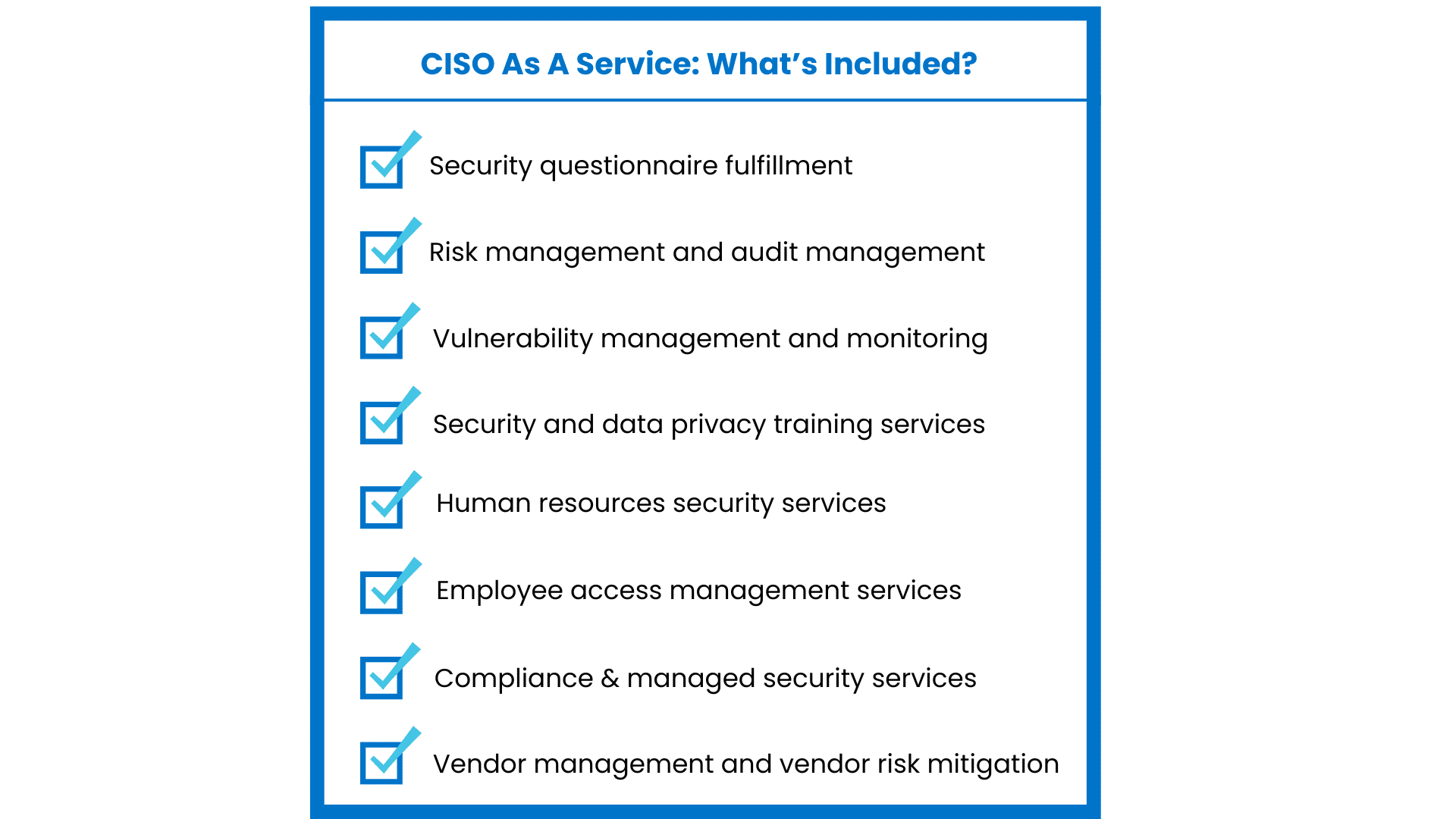
There is a vast range of services your CISO can provide, depending on your industry, your compliance needs, and the scope of service offered by the provider.
Here are just some of the services the CISO as a service model may include:
- Fill out security questionnaires on your behalf
- Risk management and audit management
- Vulnerability management and monitoring
- Security and data privacy training services
- Human resources security services
- Employee access management services
- Fully managed compliance and managed security services
- Vendor management and vendor risk mitigation
At Rhymetec, depending on which level of service you select, our CISOs will accomplish all of the above. We work with many organizations that leverage a compliance automation tool for their compliance needs. If using compliance automation, our team can help deploy it and enable you to maximize your use of your selected compliance automation platform.
For audits such as SOC 2, your CISO will create SOC 2 policies for you and help you select the right SOC 2 trust services criteria for your business. We will fully prepare you for audits that align with your industry standards, such as a PCI audit if relevant to your organization, and conduct gap assessments to identify areas for improvement.
For these items and more, your CISO acts as your go-to resource for all security, compliance, and data privacy matters.
Do You Need CISO As A Service?
If your organization lacks in-house security leadership or if you struggle to keep up with compliance requirements, CISO as a service could be just what you need. This model is ideal if you are:
- A startup without the resources for a full-time CISO hire.
- Under pressure to meet compliance goals and need to fast-track the process.
- Looking for a permanent CISO but need to fill the position temporarily.
- Experiencing rapid growth, expanding operations, or going through due diligence for funding rounds or go-to-market strategies.
Startups entering regulated marketplaces such as healthcare or finance often face pressure to be able to demonstrate their compliance through certifications and attestation reports. In these cases, a CISO helps you build a compliance framework from the ground up, so you can focus on your business.
If you're running a SaaS company and pursuing SOC 2 certification to meet customer demands, a CISO can guide you in setting up the right controls and policies. They can walk you through each phase of a SOC 2 readiness assessment, fully preparing you for your official audit.
For companies experiencing rapid growth and expanding operations, security risk and regulatory requirements change. A CISO can enable you to scale your security program in line with your business growth.
If you find you're handling frequent security questionnaires from clients or going through due diligence for funding rounds, a CISO manages these requests, lightening the load on your team and improving your security posture. If your company has experienced a security incident, a CISO can help develop incident response policies and prevent future breaches.
CISO As a Service Pricing Models
CISO as a service pricing depends on which model you select.
A project-based engagement (where your CISO will perform a one-time task such as a security audit or gap assessment) ranges from $10,000 to $50,000.
Hourly pricing, which may make sense for organizations that require occasional support but don't want a long-term contract, typically costs $200 - $500 per hour.
For a monthly retainer model, which provides the most comprehensive ongoing support and continuous access to your CISO, fees range from $5,000 - $20,000 per month.
For more detailed information on pricing models, how they compare to in-house options, and how Rhymetec structures our pricing, check out our vCISO Pricing blog post.
Job Requirements and Qualifications
A CISO should bring a strong blend of technical knowledge and leadership experience.
At a minimum, the vCISO role requires a deep understanding of security frameworks like SOC 2, PCI DSS, HIPAA, and ISO 27001, along with the ability to implement these standards across various industries. You should seek out someone who is well-versed in managing risk, developing security policies, and leading incident response efforts.
Beyond technical expertise, your CISO should also have strong communication skills to engage with both technical teams and business stakeholders. They'll need to be able to present security issues in a way that drives decision-making at the executive level. Experience leading tabletop exercises, phishing simulations, and security training is an important requirement for the job.
Lastly, a qualified CISO will typically hold certifications like CISSP, CISM, or CISA. A background in governance, risk, and compliance (GRC) and knowledge of regulatory requirements relevant to specific industries coupled with certifications poise them to manage the security challenges your organization faces.

Advantages of the CISO As a Service Model
CISO as a service is a popular option for several reasons.
The model offers many advantages, particularly for startups and companies experiencing rapid growth. It provides access to experienced security leadership without the cost of hiring a full-time executive. You get the expertise you need, tailored to your organization's size and budget.
Flexibility is another key benefit. You can scale the level of support as your business grows or as your compliance requirements change. This allows you to address security and compliance issues on demand without committing to a long-term, fixed-cost resource.
The CISO as a service model brings immediate benefits when preparing for audits or responding to client security requests. As previously discussed, you gain access to a broad range of security services, from policy development to incident response planning, all managed by a dedicated expert who prioritizes fitting security strategies into your unique business needs. An outsourced CISO also eliminates the risk of turnover and retention if bringing someone in-house and full-time.
Lastly, many CISO as a service providers will give you access not only to one highly skilled individual, but to an entire team of security experts with experience across a vast range of disciplines.
In Conclusion: Selecting the Right CISO As a Service Provider For Your Organization
By leveraging the CISO as a service model, you gain access to the security and compliance leadership needed to meet industry standards and client expectations without the overhead of building an internal security team.
Whether you need assistance developing a security program from the ground up, need help preparing for audits, or need guidance on how to respond to security incidents, a fractional or vCISO fills these needs perfectly without the commitment of a full-time hire.
If you have more specific questions, please feel free to contact our team:
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering. Under Metin’s leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
ISO 42001 sets the stage for responsibly managing AI systems within organizations. Taken together, ISO 42001 controls and policies represent the first international AI management system standard. With the proliferation of AI across many industries showing no signs of slowing down, guidance is sorely needed to address potential security, societal, environmental, and other risks posed by the use of AI.
Security concerns around AI are top of mind for many organizations at the moment. Recently, companies like Samsung have gone as far as banning the internal use of generative AI tools after a data leak with ChatGPT. Meanwhile, consumers are becoming increasingly concerned about how companies utilizing AI systems handle their data.
ISO 42001 aims to provide clarity around how organizations can responsibly use AI. Adherence to ISO 42001 controls sends a strong signal that an organization takes the security component of AI seriously. It is the most comprehensive attempt to date to provide clear requirements for implementing and continually managing the use of artificial intelligence. In this article, we go over what it is, who it applies to, and what businesses need to do to implement it.
Who Does ISO 42001 Apply To?
ISO 42001 is a voluntary standard. There are no legal obligations to adhere to it. However, it becomes a must-have for many organizations once their prospects and clients start asking for evidence and reassurance that their data is being safely handled by systems using AI.
Given the wave of media hype around AI, and the rapid improvement of the technology itself, many organizations have started to ask serious questions about the potential risks.
The standard applies to any organization developing or providing products or services that utilize AI systems. Based on official guidelines, ISO/IEC 42001 is for:
"Organizations of any size involved in developing, providing, or using AI-based products or services. It is applicable across all industries and relevant for public sector agencies as well as companies or non-profits."
The implementation of ISO 42001 controls, as well as the responsibilities within the management of AI systems, can vary depending on the individual organization.
What Do Businesses Need To Do To Implement ISO 42001 Controls?
The standard is quite robust but can be summarized into three main action items that organizations must complete in order to implement it. There is a clear focus on risk assessment, the role of governance, and compliance as a continuous process rather than a "check the box" item for businesses. The focus on these trends is reflected across the standard's three main components:
1. Create An AI Management System
A key component of ISO/IEC 42001 is the concept of an Artificial Intelligence Management System (AIMS). An AI management system is a documented system an organization uses to establish and enforce policies that manage assets using AI.
The AI management system also establishes objectives related to the use of AI and creates processes to achieve them. The goal is to have a set strategy for responsibly managing AI that is applied across the organization and aligns with overall business goals.
At a high level, the AI Management System should:
- Align with organizational objectives.
- Define and manage both risks and opportunities associated with AI.
- Oversee the implementation of controls to address AI security risks.
- Manage third-party vendors and partners involved in the development and/or ongoing use of AI systems.
In conjunction with the creation and documentation of an AI Management System, organizations must also conduct an impact analysis (determining the broader potential security and societal impact of AI systems, as well as the impact on business goals), establish clear policies on the use of AI, and implement controls to ensure data is responsibly handled in AI systems.
Lastly, the standard emphasizes the importance of continuous monitoring and improvement of the AI management system.
2. Conduct An Impact Analysis
There is a clear focus on the importance of assessing the societal impacts of AI systems. One of the core controls requires organizations to assess and document the potential impacts of their AI systems in the following areas:
- Environment sustainability (including the impacts on natural resources and greenhouse gas emissions);
- Economic (including access to financial services, employment opportunities, taxes, trade and commerce);
- Government (including legislative processes, misinformation for political gain, national security and criminal justice systems);
- Health and safety (including access to healthcare, medical diagnosis and treatment, and potential physical and psychological harms);
- Norms, traditions, culture and values (including misinformation that leads to biases or harms to individuals or groups of individuals, or both, and societies).
ISO 42001 controls require an AI risk assessment, along with an AI system impact assessment, to be conducted and continuously evaluated. This means that organizations must not only continuously monitor the impact of AI as risks change but must also evaluate the efficacy of their systems intended to mitigate that risk.
3. Implement and Continuously Improve ISO 42001 Controls
There are many areas where controls can be adjusted according to the organization's industry and needs.
Here is a summary of the standard's additional controls and overall implementation guidance:
Establish Roles & Responsibilities, and Document AI Policies: Organizations must establish and document clear policies around AI that are aligned with overall objectives and demonstrate a commitment to continuous improvement. Leadership must communicate the importance of AI management across the organization and share resources with employees. The roles and responsibilities related to the AI management system should be made clear, as well as how the AI management system requirements fit into business processes and goals. AI design choices, including machine learning methods, must also be documented.
Address Risks and Opportunities: Identifying potential risks and establishing a plan to address them is a critical step. This involves conducting an AI risk assessment and then selecting appropriate risk treatment options, implementing controls, and producing a statement of the applicability of controls. Objectives related to the use of AI, as well as a plan to achieve them, must be established and continuously reassessed.
Provide Organization-Wide Resources and Support: Create and distribute resources necessary for the AI management system and its ongoing improvement. Ensure that employees involved in AI-related activities receive appropriate training and education and that employees are aware of their roles within the AI policies.
Evaluate Performance: This involves ongoing monitoring, analysis, and evaluation of the performance of the AI management system. This can take the form of internal audits, intended to ensure conformity to AI management system requirements across the organization. Reviews of the AI management system must be conducted at planned intervals throughout the year.
Continual Improvement and Corrective Action: This last piece highlights the increasing importance being placed on continuous compliance rather than a "check the box" mentality. This is a shift we are seeing across the board for other requirements and standards, such as in the latest version of NIST CSF with the addition of the NIST Governance function.
In the context of ISO 42001, this means that organizations must continually improve their AI management system and take corrective action to make changes as needed.
In Conclusion: What ISO 42001 and The AI Management System Mean For Businesses
Organizations that adhere to ISO 42001 gain several key benefits. First and foremost, they gain the benefit of responsible use of AI and the peace of mind knowing they can provide evidence of that to any partners, prospects, or other business stakeholders.
As is often the case with other voluntary standards (such as SOC 2), organizations often find that their deals cycle becomes shorter, as prospects' questions around security are proactively answered and they no longer need to fill out lengthy security questionnaires.
Secondly, organizations gain the benefit of reputation management. Given the focus on mitigating environmental, societal, and economic damage, adherence to ISO 42001 controls serves as a signal that organizations care about their role in these issues and have taken steps to invest in the responsible use of AI. This can have the effect of improving their reputation as reliable, responsible, and trustworthy.
Lastly, there is an enormous benefit in terms of AI governance. ISO 42001 controls map onto laws and regulations around the use of artificial intelligence, allowing organizations to align the use of AI with laws relevant to their industry and location. As one of the first frameworks to directly address AI, ISO 42001 will serve as a baseline for future standards and laws.
Organizations can take a proactive approach by complying with ISO 42001. This saves time and money down the line when other frameworks and laws catch up.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business.
If your organization is interested in exploring compliance with AI standards, we now offer ISO/IEC 42001 certification readiness and maintenance services and are happy to answer any questions you may have.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering.
Under Metin’s leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
Interested in reading more? Check out additional content on our blog:
- Maximize Your Use of Compliance Automation Platforms
- 7 Factors To Consider Before Implementing AI in Your SaaS Company
- Phishing Training For Employees: 5 Steps To Success
Why is it that cyberattacks are so hard to stop? Why do organizations need to continually invest in security? And why are measures like phishing training for employees mandated under so many cybersecurity regulations and standards?
The answer is a strange one:
Trust.
For better or for worse, humans are naturally trusting. We want to trust that the used car we bought won't have any issues missed by the inspection, that our Grubhub order will arrive when it says it will, that House of the Dragon Season 2 will be as good as Season 1, and that the email purporting to be from our CEO giving us a $500 bonus is legitimate.
Statistically, phishing is the number one way that your organization may fall victim to a cyber attack, and it's precisely because of our tendency to trust:
According to ReliaQuest's 2024 Cyber-Threat Report, threat actors predominantly use methods that work by "exploiting the trust and vulnerability of unsuspecting individuals." To any experienced security professional, it's unsurprising to hear the report found that phishing was used in 71% of all security incidents in 2023.
There are a million terms for phishing: vishing, smishing, whaling, qrishing (yes, somebody has actually made 'qrishing' a word; no, you don't need to know what it means because even Google Docs flags it as made up).
When you cut down to it, every type of phishing involves abusing people's trust in order to gain some advantage, whether financial or informational in nature. If a threat actor or ransomware group gets privileged access to your organization, odds are it will be through phishing.
This fact has both an upside and a downside:
The upside is that it gives you an area to focus on that can help substantially reduce your company's risk. The downside is that stopping phishing attacks is a hard problem.
Fortunately, simulated phishing is an excellent tool that allows you to prepare employees for the real thing before they get an email that could lead to a ransomware attack. This article will answer the following questions:
- How is phishing training conducted?
- Do I need phishing training for employees?
- Which cybersecurity standards and regulatory frameworks require phishing training?
- What are the top current recommendations from experts to mitigate risk from social engineering attacks?
- What is the role and importance of an incident response plan?
Let's jump right into the steps security professionals take to simulate how threat actors carry out phishing attacks and how you can conduct phishing training for employees:

Phishing Training For Employees Phase 1: Reconnaissance
Being with the assumption that you know nothing about your business.
Your job is now to take the perspective of a threat actor. What can you find out about employees and your company through open-source intelligence (OSINT)?
First, you need to find your company's email format, such as [email protected].
This is exactly what a motivated attacker would do.
There are several areas you can look for this information:
- Are employee emails listed on previous press releases?
- Do employees have their work email addresses listed on their LinkedIn profiles? By default, LinkedIn reveals huge amounts of both personal and professional information.
- Are any corporate email addresses related to individuals listed on the website?
Once you have this information, try to find out about the hierarchy of the organization. Who reports to whom? Who does what? A motivated threat actor may send incredibly detailed phishing emails to employees involving key aspects of their role or job duties.
Every piece of information you leverage should be publicly available to make the phishing exercise as realistic as possible.
Phase 2: Write Phishing Emails
Many organizations conduct simulated phishing with hopelessly generic emails that don't mimic the real thing. When building your phishing account and writing emails, take the perspective of a motivated and sophisticated threat actor who has done their homework.
Here are a few tips you can use:
- Register an email with a domain that is very similar to your organization. If your company is called "[email protected]," you can register "[email protected]." (Fun fact: Our brains like to fill in the gaps when letters are omitted. This is one of the many ways phishing attacks prey on human psychology so effectively).
- Don't use ChatGPT or other LLMs. Write the emails with care and precision, and mention key elements of the person's job if you were able to identify them during the reconnaissance phase. If you decide to send out mass emails that aren't targeted, utilize company language or recent company events as a real attacker might.
- Make your subject line an urgent one. For example, depending on the person you are targeting, adding "EMERGENCY" to the subject line is one way to do this. This can help make people miss the key element.
- Have a call to action. Downloading a benign file is common in simulated phishing tests. Another option is to set up a web page to "capture" their corporate credentials, as an attacker might.

Phase 3: Establishing A Baseline
If you do your job well people are going to click.
If you do your job exceptionally well, people are going to click…a lot.
Once you've set up your domain and carefully crafted your phishing emails, it's time to send them out to individual employees. This baseline will help identify which employees are the most susceptible to phishing.
A few tips during this phase:
- Don't punish or shame employees for falling for it. If you punish employees, you will disincentivize them from reporting phishing attacks in the future.
- Make it clear that the purpose of the exercise is to simulate a real attacker and not to embarrass employees. Show employees why it's important to do these exercises.
- Show employees where you found their information that enabled you to craft your emails so that they can reduce their online footprint.
During this phase it can also be worthwhile to have employees review a service such as haveibeenpwned to see if they have credentials that are being traded on the dark web as well, as this is another common vector of attack.
Services like Picnic that search the web for personal information are also helpful to show employees. Picnic provides enterprises with the capability to manage their external human attack surface and to detect, prevent, and protect against social engineering attacks.
Using both dark and clear web monitoring services enables employees to pinpoint exactly where their information is available online and stay ahead of bad actors.
Phase 4: Training Employees
Follow up immediately and personally with employees who have downloaded a file or submitted credentials to your fake web page. There are many free or paid security training courses that you could prescribe to the individual.
Work with them to go over common phishing email tactics and strategies to avoid them:
- Focus on providing customized instruction and time one-on-one. Employees should never be publicly ridiculed for clicking phishing links.
- Showcase real examples of phishing emails that the company has received (or use online resources) to provide examples.
- Emphasize that phishing can come in many forms. Any emails that aren't expected from known entities should be carefully scrutinized.
Don't come across with the mentality of, 'simulated phishing exercises won't end until the click rates get better.' Instead, provide educational material that will help people feel comfortable reporting incidents.
Statistics like the following can be used to help illustrate the importance of coming forward: In the case of a type of phishing attack where threat actors impersonate banks, over 50% of victims are able to recover most of their money.
Example Of A Phishing Email
Here is an example of a more sophisticated phishing email that you might use as part of your training materials:
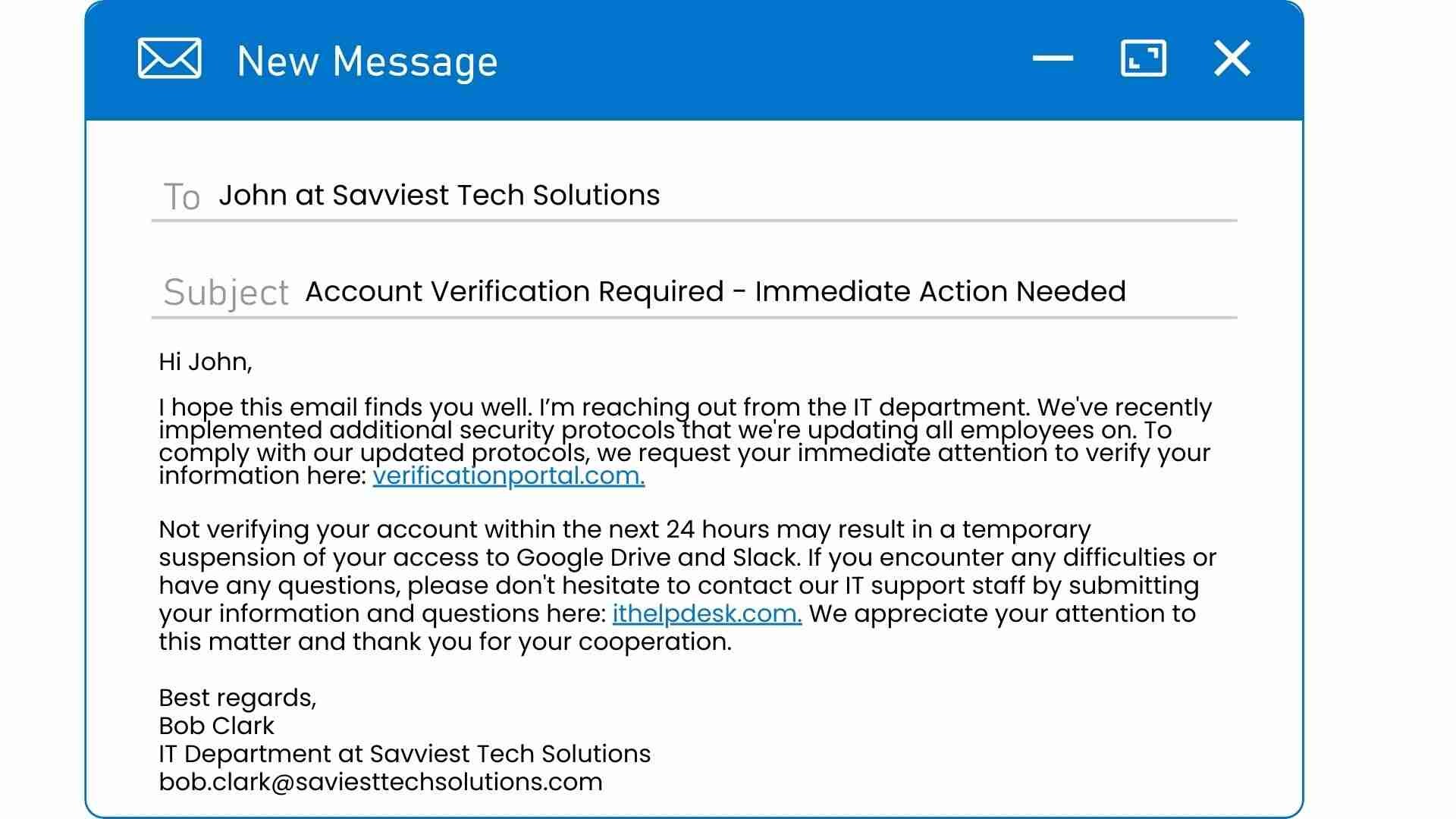
Can you spot what gives it away as phishing?
And, even more importantly, would every single person at your company be able to spot it as phishing if they saw it in their inbox?
The key elements here are:
- The misspelling in the sender's email address: Note the misspelling in the sender's email address ([email protected]). It doesn't match the official domain name of our fake company (Savviest Tech Solutions). This is almost always a sign of phishing.
- The urgent call to action: This is common in many types of scams, not just phishing attempts. The scammer will attempt to instill a sense of urgency to create stress and try to prevent the victim from having time to think.
- The use of a fear tactic: Although not explicitly threatening, the email states that failure to comply may result in the recipient having their access to important systems suspended. This could create a fear of their performance at work being impacted.
- The link with a request for personal information: Any link asking for your credentials should always be thought twice about before clicking.
- The nature of the request itself: The recipient of this email should be extremely wary if this is the first time they're hearing about the new "security protocols" at their company.
Phishing Training For Employees Phase 5: Reiterate and Collect Data
Within weeks to months, you should run another test.
Compare your results to the baseline data:
- Have employees substantially improved?
- Are there repeat offenders who have fallen for multiple tests?
These are excellent statistics to collect and can be powerful, as they enable you to measure your program's effectiveness.
Do You Need Phishing Training For Employees?
If your company uses email (or if your employees have cell phones, as texting can be another vector for phishing), the answer is simple:
Yes.
As stated above, phishing is extremely common and is the number one way organizations fall victim to cyberattacks. In 2023, over 25% of U.S. employees clicked a link in an email that opened a suspicious website.
If you are a startup or a small business, the answer is just an even more emphatic yes!
Cybersecurity for startups and small businesses is critical, as they are being increasingly targeted by threat actors. When it comes to phishing, the risk appears higher for smaller companies:
Consider the fact that an employee at a company with fewer than 100 employees receives 350% more phishing emails in their inbox than an employee at a large company.
This makes security awareness training one of the most effective ways to mitigate cybersecurity risk for SMBs.
Does phishing training for employees actually work?
Yes!
Threat actors engage in phishing because it's one of the most effective and low-effort tools they can use to gain access to usable credentials like passwords. Prevention is key when dealing with threats from phishing, and thankfully, training works:
According to Proofpoint's 2024 State of the Phish Report, 84% of U.S. organizations reported that after their employees underwent security awareness training, the ability to spot phishing attempts improved, and click rates on phishing emails decreased.
That represents a lot of users who avoided clicking a link that would've delivered malware like a virus or ransomware to their computers.

Do I need phishing training to meet controls under cybersecurity standards and regulatory frameworks?
If you are trying to ensure best practices for your cybersecurity - as well as compliance with standards relevant to your industry - you absolutely need to conduct robust security training.
Security awareness training is one of the top Critical Security Controls recommended for SMBs by the Center for Internet Security (CIS):
- Control 14: Security Awareness and Skills Training. Establish and maintain a security awareness program to influence behavior among the workforce to be security conscious and properly skilled to reduce cybersecurity risks to the enterprise.
- Control 14.2: Train Workforce Members to Recognize Social Engineering Attacks.
- Control 14.6: Train Workforce Members on Recognizing and Reporting Security incidents.
The CIS is far from the only entity to include security awareness training in its guidelines.
The laws that require security awareness training include:
- The HIPAA Privacy Rule and the HIPAA Security Rule
- The Gramm-Leach-Bliley Act (GLBA)
- The Federal Information Security Management Act (FISMA)
- Massachusett's Data Security Law
Security awareness training is also required under standards including:
- PCI DSS
- ISO 27002
- NIST Special Publication 800-53.
- GDPR
It is also a standard control organizations must fulfill as part of their SOC 2 audit.
The Bottom Line: Phishing training is one of the number one items addressed in security awareness training. A security awareness program that failed to include phishing training for employees would be viewed by auditors and regulators as insufficient.
The Top Current Recommendations To Mitigate Phishing Risk
The best-of-breed, most up-to-date practices to mitigate the risk of social engineering tactics are outlined in ReliaQuest's 2024 Cyber-Threat Report. Here's a summary from the report:
- Harden MFA Mechanisms: Implement a certificate-based authentication policy. Use digital certificates to verify the authenticity of users during the authentication process. Additionally, consider limiting the token lifetimes for MFA—by setting a shorter timeframe, you reduce the window of opportunity for attackers to exploit them.
- Add or use Alternative Authentication Factors: Consider implementing biometrics and adaptive authentication. Biometrics can include features like fingerprint or facial recognition, and adaptive authentication verifies users based on multiple factors, such as location, user behavior, and registered device.
- Train Employees: Develop regular training sessions and simulation exercises to teach employees how to recognize and report social engineering attempts, such as phishing emails, phone calls, and in-person scams. Teach employees to scrutinize email headers, links, and attachments and to report any suspicious activity.
- Enforce Password Security: Implement password policies requiring complex passwords (12-plus characters, uppercase, lowercase, number, and symbol), prevent password reuse, enforce password changes every 90 days, and enable MFA. Limit Access to Sensitive Information: Restrict information access to a need-to-know basis.
The Bottom Line: Phishing training for employees plays a key role in mitigating the risk of social engineering attacks and is one of the methods most commonly recommended for organizations by industry leaders in cybersecurity.
Why Do Companies Outsource Phishing Training For Employees?
Many companies choose to outsource phishing testing and training for several reasons:
Having a third party conduct your phishing testing and training is generally more robust from a security standpoint and works better from an auditing standpoint as well. The amount of work involved in phishing testing can also be a huge time suck and disruptive to daily business operations.
If your team has the security know-how and the bandwidth, you can certainly conduct phishing training for employees on your own using the 5 steps outlined above. But if you're curious about how outsourcing phishing testing and training to the experts works, here's Rhymetec's methodology that we've implemented with hundreds of clients:
Rhymetec's Method For Phishing Testing and Training
First, our Phishing Simulation Assessment determines the scope of the phishing campaign and which users to include. Our team has decades of experience in offensive security and is easily able to tailor the project to each organization's needs.
We use the exact same techniques cybercriminals use: making minor changes in URLs, crafting convincing email messages, and conducting reconnaissance on employees' online footprints.
The Phishing Simulation is scheduled to be performed at an agreed-upon time.
Once users fall for a phishing email or input their credentials into a phishing website, our team immediately provides security awareness guidance on what phishing is and how to spot phishing attempts in the future.
After the baseline assessment, Rhymetec produces a preliminary written report.
Our Phishing Platform Portal provides robust reporting to equip you with the information needed to create gradual improvements in your organization's security. This is typically represented through a gradual decline in month-on-month phishing click rates.
Our platform provides actionable data on the number of users who viewed a phishing email, users who clicked the link in a phishing email, and users who entered credentials into a phishing website. Post-report, we send additional educational training modules to staff members who did not pass the assessment.
Rhymetec's method is guaranteed to fulfill requirements for phishing training for employees under regulatory and voluntary standards, including SOC 2, GDPR, HIPAA, NIST, PCI DSS, and more.

In Conclusion: Two Key Recommendations For Phishing Training For Employees
We recommend conducting continuous phishing training throughout the year to keep employees mindful of phishing risks. Continuous phishing training can be an extremely powerful tool for reducing the risk that threat actors get access to your environment.
We also recommend having a solid incident response plan in place.
At the end of the day, people are only human, and mistakes happen. While measures like security awareness and phishing training for employees are essential and do work to mitigate a substantial amount of risk, nothing is foolproof when it comes to preventing human error 100% of the time. Having a documented incident response policy is vital:
We encourage companies to invest in prevention by preparing employees as best as they possibly can while also having a plan in place in case an incident were to occur.
Managed Security Services Providers like Rhymetec offer a full arsenal of prevention measures that mitigate a huge amount of risk, while also providing procedures, policies, and assistance in the event of a security incident.
To learn more about how our team can accelerate your security while keeping your budget in mind, contact us for more information.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering. Under Metin’s leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
There were many major releases in 2024. The hit new TV series FX Shogun, Dune Part 2, Taylor Swift's Eras Tour on Disney+, and most importantly, the new NIST Cybersecurity Framework Version 2.0 with the addition of the NIST Governance Function.
Thrilled yet? Well, you should be. The National Institute of Standards and Technology regularly releases technical guidance documents and frameworks for both the public and private sectors to use as best practices guides.
The original NIST Cybersecurity Framework (NIST CSF) serves as the basis for tens of thousands of cybersecurity programs around the world and directly inspires many other compliance frameworks and requirements.
By meeting NIST, organizations automatically cover many controls in other requirements that overlap with NIST. It's widely considered the gold standard of robust cybersecurity across many industries.
This article will explore NIST CSF V2.0, what's changed, and what's likely to change going forward.
If you have more specific questions on what these changes may mean for your organization, please feel free to contact our team for support:
What Is The NIST Cybersecurity Framework?
NIST CSF was originally intended as a cybersecurity framework for critical infrastructure companies.
Some key facts about NIST CSF V1.0:
- The original NIST CSF was released in 2014
- NIST CSF was developed in collaboration with industry and government stakeholders
- Provided a high-level framework for cybersecurity risk management
- Consisted of five core functions: Identify, Protect, Detect, Respond, and Recover
- Each core function is broken down into subcategories and controls
- NIST CSF is voluntary, but it is widely used by organizations of all sizes
- NIST CSF was updated on a regular basis to reflect changes in the cybersecurity landscape
In addition, many regulations (particularly those in the United States) directly drew on controls originally formulated in the NIST Cybersecurity Framework.
NIST CSF is split into five modules reflecting elements of the cybersecurity lifecycle, including:
Identify:
- Get visibility into the network environment, including asset categorization.
- Create continuous monitoring for new assets being brought back online or added to the network.
Protect:
- Implement robust security protocols across the organization to include IDS/IPS, firewalls, EDR systems, and anti-virus
- Create and maintain a regular patching program to reduce exploitable vulnerabilities.
- Utilize strong authentication (such as multi-factor authentication) to reduce the risk of unauthorized access.
Detect:
- Use security monitoring tools to get visibility into suspicious activity such as unauthorized access attempts.
- Set up a notifications and alerts system to inform your security team in a timely manner of potential incidents and threats.
Respond:
- Have a well-documented incident response plan that describes the procedures for responding to security incidents.
- Be able to contain security incidents to minimize their impact and mitigate further damage.
Recover:
- Ensure a comprehensive backup and recovery program is in place to protect critical assets and restore data in the event of a security incident or natural disaster.
- Test back up and recovery programs regularly and update as needed.
NIST CSF V2.0: What's In It?
NIST CSF version two carries on many of the fundamental themes found in the original NIST CSF. However, a new element has been added: NIST Governance.
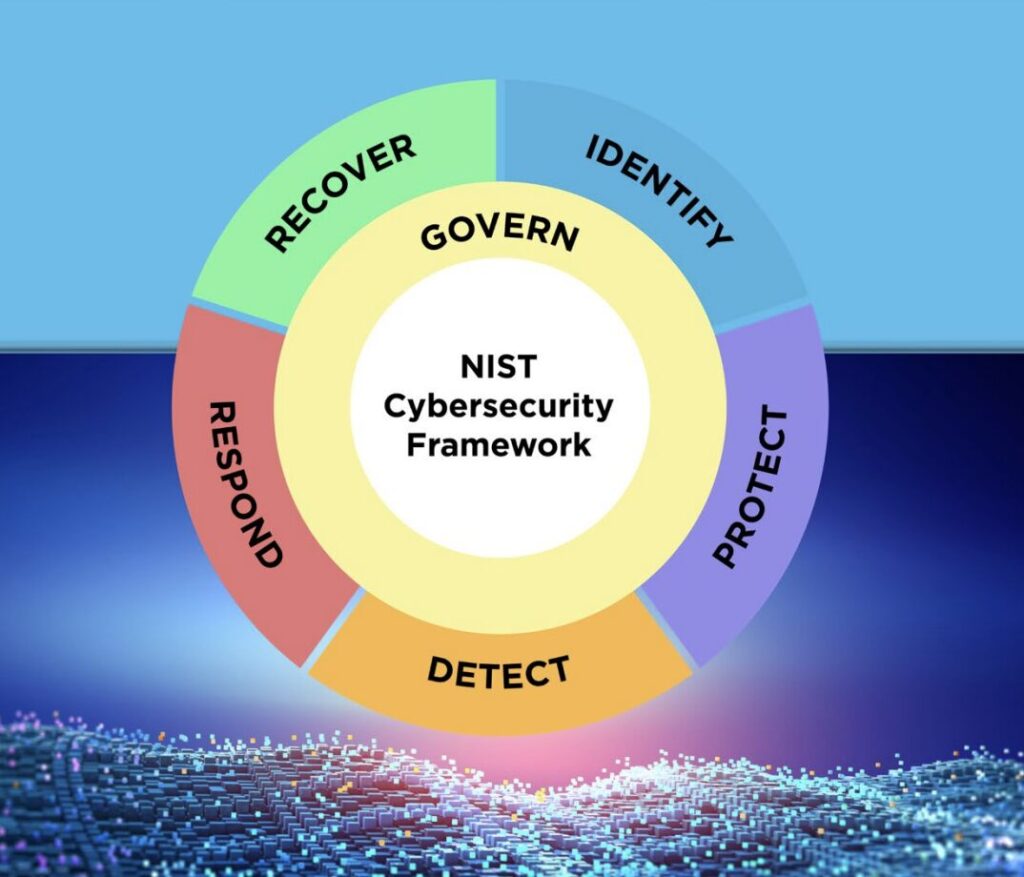
Source: NIST Drafts Major Update To Its Widely Used Cybersecurity Framework.
Note the clear emphasis of the guidance under this new function:
Governance
- Executives take on an active role in organizational risk management and collaborate on how potential cybersecurity gaps across the organization may impact broader objectives.
- Regularly hold dialogue among executives about risk management strategies, roles, and policies.
- Establish security goals tailored to the industry and organization at the executive level.
- Document and communicate security policies and expectations down the line to managers and individuals.
- Encourage collaboration at the executive level and across the organization about risk management strategies, including cybersecurity supply chain risk.
- Ensure cybersecurity risk management is explicitly rolled into overall Enterprise Risk Management (ERM).
In short, the updated CSF is intended to help executives communicate better about cybersecurity, with the goal of ensuring robust security through every level of the organization:
"The CSF helps organizations translate their terminology for cybersecurity and cybersecurity risk management into general risk management language that executives will understand."
The features of the new version also help enforce that the CSF applies to small organizations as well as large ones, and can be easily tailored to fit their needs.
A New Addition: NIST Governance and What It Means For Businesses Going Forward
It's important to remember, that compared to many functions of a business, cybersecurity in its current state is still extremely young.
Cybersecurity began as a sub-discipline of Information Technology.
In the 2010s, business leaders, particularly in industries with a heavy reliance on information technology, increasingly came to see cybersecurity as a standalone field - one that needed adequate resources and provisioning to succeed.
The NIST Governance section is an effort to add concreteness to cybersecurity as a board-level conversation in its own right and not just an offshoot of information technology. NIST states:
"The CSF's governance component emphasizes that cybersecurity is a major source of enterprise risk that senior leaders should consider alongside others such as finance and reputation."
It's worth pausing for a moment and reflecting on what a significant statement this is.
NIST is advising companies to consider cybersecurity as significant of a risk as running out of money or having their reputation destroyed (note that bad cyber practices can cause both of these things).
The new NIST governance function includes six key aspects:
- Organizational Context (GV.OC)
- Risk Management Strategy (GV.RM)
- Roles, Responsibilities, and Authorities (GV.RR)
- Policy (GV.PO)
- Oversight (GV.OV)
- Cybersecurity Supply Chain Risk Management (GV.SC)
The introduction of Cybersecurity Supply Chain Risk Management (C-SCRM) under governance is another critical addition.
Software supply chain attacks have become increasingly common in recent years, such as the 2020 SolarWinds breach and the 2023 MOVEit vulnerability, famously exploited by the CL0P ransomware group.
Rhymetec's Take: The business impact of investing in cybersecurity is exceptionally high. The threat landscape has continued to increase in risk, and organizations are increasingly expecting third-party suppliers to not only meet compliance but also demonstrate security that goes past it. NIST CSF's Governance change is an excellent addition that reflects the growing importance of security for modern businesses.

The Expanded Scope: NIST Governance
NIST CSF V1.0 was focused specifically on critical infrastructure. While this did not stop organizations all over the world from using it as a basis, it did create a sense that it might be overkill for some businesses.
NIST CSF V2.0 has remedied this flaw and makes it clear that the CSF can be tailored to fit any business regardless of size or maturity.
Rhymetec's Take: In this case NIST is catching up to where many organizations already are. NIST has long and widely been used as the basis for cybersecurity programs, but it is a positive development for them to acknowledge and expand the use case.
Additional Resources for Implementation and The NIST Governance Section
One of the most profound and significant changes has been the additional material NIST is publishing to help organizations build their security programs based on the cybersecurity framework.
NIST is publishing several appendix documents, including:
Implementation Guidance for CSF V2.0
The implementation guidance is an extremely valuable addition to the CSF.
Many organizations, particularly those that don't yet have dedicated cybersecurity staff, may struggle to understand what the cybersecurity framework is actually asking of them. The addition of remediation guidance provides an enormous amount of additional clarity.
For example, let's take a control found in the new governance section:
GV.SC-06: Planning and due diligence are performed to reduce risks before entering into formal supplier or other third-party relationships.
For seasoned governance risk and compliance professionals, this may seem straightforward.
But for an organization without GRC staff that is just beginning to think about third-party due diligence, how can this be implemented?
Fortunately, the Implementation Guidance provides real-life, concrete examples for businesses to better understand how to do a practical implementation of a security control. For GV.SC-06, NIST provides 4 implementation examples:
- Ex1: Perform thorough due diligence on prospective suppliers that is consistent with procurement planning and commensurate with the level of risk, criticality, and complexity of each supplier relationship.
- Ex2: Assess the suitability of the technology and cybersecurity capabilities and the risk management practices of prospective suppliers.
- Ex3: Conduct supplier risk assessments against business and applicable cybersecurity requirements, including lower-tier suppliers and the supply chain for critical suppliers.
- Ex4: Assess the authenticity, integrity, and security of critical products prior to acquisition and use.
For many organizations, implementation examples will undoubtedly be key to help clarify the request being made of them by the guidance. Note how each example has slightly different wording: compliance isn't a one-size-fits-all project.
Many compliance requirements leave room for organizations to implement the security control in a way that will optimally benefit their organization.
Working with a vCISO can help by leveraging decades of experience in tailoring security controls to your company's unique risk profile, maximizing your return on investment while also ensuring that your organization meets the technical and intended definition of the control.
For instance, example 4 only has the organization assessing critical suppliers, whereas example 1 has the organization tiering their suppliers and level of due diligence. If an organization is just beginning their C-SCRM program, they may not have the sophistication or resources (or need!) to fully vet every single supplier based on a tiered approach.
While the company matures, only assessing mission-critical suppliers can be an excellent addition to a security program, and it is far better than doing nothing.
Rhymetec's Take: Implementation guidance should substantially help bridge the gap, particularly with small or immature organizations to effectively implement NIST CSF 2.0's guidance. Note that simply claiming you are meeting a control will not pass an auditor's scrutiny. You need to have a documented process for meeting the control, appropriate technology, and evidence that your policy is acted upon.
NIST CSF 2.0 Reference Tool
Another addition with NIST CSF 2.0 is a new reference tool that can be used to identify requirements and export data quickly.
Rather than reading a massive PDF, the new reference tool makes it simple to rapidly identify controls or subsets of controls within NIST and export that section or subset either in machine or human-readable format.
Users are able to filter based on the control family and whether the control is focused on first or third parties and then export the data into JSON or Excel. The reference tool also includes the aforementioned implementation guidance, significantly simplifying the process of understanding and complying with controls.
This makes it considerably more user friendly and allows easy exporting of data.
The reference tool could be helpful for many organizations, but particularly for large or complex organizations that may have many different individuals and functions responsible for implementing the second version of NIST CSF to include updates in alignment with the NIST Governance element.
NIST CSF 2.0 Quick Start Guides
The last major addition to NIST CSF 2.0 we will cover is quick start guides, designed to help organizations get started on implementing controls from NIST Governance and other functions based on their unique circumstances and risk posture.
Quick start guides are segmented into:
- Organizational Profiles: According to NIST, an organizational profile "...describes an organization's current and/or target cybersecurity posture in terms of cybersecurity outcomes from the Cybersecurity Framework (CSF) Core."
- Community Profiles: These are designed to help specific industries and sectors implement the CSF based on their unique risk profile. According to NIST, "A Community Profile can be thought of as guidance for a specific community that is organized around the common taxonomy of the CSF."
- Small Business Resources: The small business section of the quick start guide is focused on providing actionable, easy-to-implement steps that small businesses can use to begin implementing CSF V2.0 controls.
- Cyber Supply Chain Risk Management (C-SCRM): C-SCRM is a growing concern for organizations of all sizes that continues to be highlighted by major supply chain breaches. The C-SCRM quick start guide provides specific guidance on how you can use the CSF to establish your C-SCRM program.
- Enterprise Risk Management: The Enterprise Risk Management quick start guide helps organizations better understand the implementation of NIST CSF 2.0, particularly NIST Governance, in a complex and multifaceted enterprise context.
- Tiers: NIST CSF 2.0 tiers "...can be applied to CSF Organizational Profiles to characterize the rigor of an organization's cybersecurity risk governance and management outcomes. This can help provide context on how an organization views cybersecurity risks and the processes in place to manage those risks."
Concluding Thoughts On NIST Governance and NIST CSF 2.0
NIST CSF 2.0 represents a huge step from the original NIST.
There has clearly been a focus on making it easier to conceptualize, understand, and implement CSF controls in a way that will reduce organizational risk for businesses.
The NIST governance section is a critical addition that helps solidify the case that cybersecurity and cyber risk management are no longer a function of the IT department, but a function that requires whole-business buy-in from the board of directors down to individual department heads.
Contact our team at Rhymetec for more information:
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while also balancing security with budget. We offer a full suite of security services including mobile application penetration testing services, phishing testing services, PCI compliance scanning, and more.
Our team has extensive experience helping organizations implement a variety of security frameworks and compliance requirements, including NIST CSF, SOC 2, HIPAA, GDPR, and many more.
We enable our clients to outsource the complexity of security and focus on what really matters – their business. If you are interested in our services, or if you simply have questions about security, you can contact our team for more information.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering. Under Metin’s leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
So, you've just been handed a security questionnaire by a potential customer, and you're not sure where to start.
What is access control? What should you answer when asked if you utilize strong authentication across all applications with sensitive data?
This Rhymetec guide will not only help you answer these questions but will also provide suggestions that you can use to strengthen your security posture and work with potential customers more confidently, with less risk of non-compliance or a data breach.
What Is A Security Questionnaire?
Security questionnaires are used by your potential customers to assess their third-party vendors and suppliers. Numerous major third-party incidents have occurred in recent years, and threat actors are increasingly attempting "supply chain attacks" - cyberattacks that target a critical element of a particular supply chain and then attempt to move laterally into other parts of the supply chain.
For example, the identity and access management platform Okta recently suffered from numerous compromises that threat actors attempted to use to gain access to Okta's customers' data. All of this was a long way of saying companies with mature cybersecurity programs care about supply chain attacks - a lot.
Enter the security questionnaire.
Security questionnaires are required by some compliance requirements such as HIPAA, GLBA, and PCI DSS. In addition, understanding who you're doing business with, what their security controls are, and what types of data you will be sharing with them is important from a simple risk mitigation perspective.
Security Questionnaire Example Questions
So, what exactly do security questionnaires typically ask?
It can vary a lot, but here are some common types of questions:
- Does your organization employ strong authentication measures such as multi-factor authentication for all corporate applications that hold customer data?
- Does your organization offboard employees within 8 hours of the termination of employment?
- Does your organization conduct routine penetration testing to identify vulnerabilities in your environment?
- Does your organization have documented incident response plans and processes?
- Does your organization routinely train users regarding information security and risk?
Depending on the potential customer you are working with, questions may be very in-depth or very cursory. In many cases, your customers may tier their security questionnaires; a company that stores data about tennis shoe manufacturing needs far less scrutiny than a company storing Protected Health Information (PHI).
Security Questionnaires and Compliance
Security questionnaires aren't only driven by risk requirements. They are also driven by specific legal compliance requirements that your customers fall under. We will provide two examples of major compliance regulations that directly touch on vendor security.
In both of these, notice that nowhere is it mandated that you must send a security questionnaire. Instead, both require that organizations assess their vendors. The security questionnaire is the form that this assessment takes.
The HIPAA Security Rule
The Health Insurance Portability and Accountability Act Security Rule (HIPAA): HIPAA applies to healthcare organizations and other organizations that handle Protected Health Information (PHI).
Under HIPAA, any organization handling PHI that is considered a "covered entity" is required to comply with the HIPAA Security Rule, a specific set of information security standards. In addition, "business associates" of covered entities are also required to meet all requirements in the security rule:
- 164.308 Administrative safeguards. (A) Risk analysis (Required). Conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information held by the covered entity or business associate.
The U.S. Department of Health and Human Services also publishes guidance on how to conduct the risk analysis required by section 164.308.
The Bottom Line: If your organization gets a security questionnaire from a healthcare organization and you will be handing PHI, take it extremely seriously. You may be considered a HIPAA business associate and be required to comply with the HIPAA Security Rule. An experienced vCISO can help guide you on how to answer questions and implement missing security controls.
The Gramm-Leach Bliley Act and The Security Questionnaire
The GLBA applies to financial services organizations. Part of the regulation requires organizations to meet certain information security requirements. eCFR Part 16, § 314.4 spells out specifically what financial institutions need to do in order to maintain compliance regarding third-party suppliers:
- Taking reasonable steps to select and retain service providers that are capable of maintaining appropriate safeguards for the customer information at issue;
- Requiring your service providers by contract to implement and maintain such safeguards; and
- Periodically assessing your service providers based on the risk they present and the continued adequacy of their safeguards.
The Bottom Line: If you are getting a security questionnaire from a financial services organization, they are likely trying to meet their legal requirements under GLBA. The organization likely isn't measuring you against a specific standard where all requirements must be met to do work with your organization. If you don't meet every control in the risk questionnaire, consider having a conversation with the customer about which ones they find totally necessary to work with a vendor, and identify a plan to meet those on a set time scale.
How Do You Answer a Security Questionnaire?
Answers to security questionnaires from customers should be honest, straightforward, and complete.
For example, to answer the following question:
- Does your organization routinely train users regarding information security and risk?
You might reply:
- Users are trained on a monthly basis on information security best practices using the security awareness training platform KnowBe4. In addition, regular simulated phishing campaigns are conducted against employees. If an employee fails a phishing test additional training is mandated.
Notice this answer gives a specific example of not only that the activity is being carried out but how the activity is being carried out (KnowBe4).
It also goes into detail about how often the phishing test takes place, and even provides additional evidence of a serious security posture by describing an interrelated simulated exercise.
However, don't go overboard with information. If your customer is asking a question about training, you don't need to tell them about your amazing vulnerability management practice. Instead, answering questions with additional detail on related policies, procedures, or technology can help make the customer's job easier.
The most important thing to do is never lie.
If there are certain questions that your potential customer has asked that you don't want to disclose, have a frank and honest discussion about what information you can provide, what you can't, and why. Lying on vendor risk questionnaires can put your organization in potential legal jeopardy, both civilly and criminally.
Should I Get Outside Help in Answering a Security Questionnaire?
Many organizations turn to managed security services organizations for help in answering security questionnaires.
Why choose a managed security services company to help you?
There are a few different reasons.
First, cybersecurity can be extremely complex! Answering vendor risk questionnaires isn't always a straightforward exercise. Does your routine security assessment performed by a third party satisfy the definition of a penetration test? Does annual user training meet the question, "Do you regularly engage in security awareness training?"
These types of details matter but aren't always immediately apparent to those answering a security questionnaire.
Secondly, the "why" of a security questionnaire matters. Mistakenly answering a question on a security questionnaire from a customer who is simply doing their due diligence can be damaging. But mistakenly answering a question for an organization assessing your HIPAA compliance under the business associates rule can be fraught with legal peril.
An experienced vCISO can help navigate these waters and ensure that answers are correct and backed with evidence.
Finally, answering security questionnaires doesn't have to be hard! There's no reason that you should be spending weeks fretting over whether your security awareness training program is up to snuff.
Engaging a managed security services company can help you rapidly respond to security questionnaires, unclogging your sales pipeline and turning security compliance into a selling strength.
SOC 2 and The Security Questionnaire
Fortunately, there may be a way that you don't need to answer every security questionnaire that comes your way.
Enter the SOC 2 Report.
SOC 2 is a voluntary framework that organizations can meet and be audited against on an annual basis. By meeting requirements under SOC 2 Type 2 and undergoing an annual audit, you can have a specific report outlining your security controls to provide to prospective customers, dramatically simplifying the process.
SOC 2 isn't just a way to get out of doing security questionnaires, though.
Organizations are increasingly choosing their vendors based on good security practices and continuous compliance. Using a vendor like Rhymetec to help you meet SOC 2 can expedite your sales process, build trust with potential customers, and enable you to engage prospects who want to see evidence of your security before doing business.
The Bottom Line
Many organizations use security questionnaires as a way to screen potential vendors for unacceptable security risks. This is becoming increasingly common, as companies wish to strengthen their third-party risk management in light of recent breaches due to vendors and suppliers.
Hopefully, this guide helped clarify how to answer questions on security questionnaires and how to turn risk assessments into a business enabler rather than a cost center.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while also balancing security with budget.
We enable our clients to outsource the complexity of security and focus on what really matters - their business. If you are interested in our services, or if you simply have questions about security, you can contact our team for more information.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering. Under Metin's leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
Interested in reading more? Check out our blog.
You might be wondering - Why would a threat actor bother targeting a startup? Don't they focus on larger companies?
In 2025, cybersecurity for startups is just as critical as it is for the world's largest organizations. You may be surprised to learn that small businesses nowadays are actually more frequent targets of cyberattacks than larger companies.
According to Verizon's 2023 Data Breach Investigations Report, there's a very clear reason for this:
Regardless of organizational size, companies are increasingly adopting similar services and infrastructure. This means that the attack surface of small organizations - all of the points from which a threat actor can access a system - looks more similar than ever to that of large companies.
When it comes to the attack surface of small versus large businesses, "...by now there is so little difference based on organizational size that we were hard-pressed to make any distinctions whatsoever." (Verizon, 2023).
While it's great that many business-accelerating tools are now equally accessible to small organizations, this democratization of technology has a dark side:
Organizations, from startups to Fortune 500, have increasingly similar risk profiles but do not have the same resources to prevent and respond to attacks.
From a threat actor's perspective, this makes smaller organizations ripe targets. In light of this, what can you do as a startup to improve your security, especially without breaking the bank?
This guide will discuss:
- Why is Cybersecurity for Startups Important?
- 5 Practical Things You Can Do Right Away
- Measures to Further Improve Your Security
- Balancing Security With Budget
- Frequently Asked Questions
- Accelerating Cybersecurity for Startups
Rhymetec was specifically founded with the mission to make cutting-edge security available to startups. We've worked with hundreds of companies to provide practical solutions that enable them to be as secure as possible while also balancing security with budget.
This guide will provide actionable solutions for cybersecurity for startups based on:
- Our experience working with hundreds of startups.
- Current trends in the industry in 2025.
Why is Cybersecurity for Startups Important?
Large companies have the resources to continuously sharpen their security measures and keep up with increasingly stringent compliance requirements. Meanwhile, smaller businesses without the same resources to devote to security are left behind.
Threat actors know this, and that's why an employee at a company with less than 100 employees receives 350% more social engineering attacks in their email than an employee at a large company.
And the smaller the business, the harder the attack hits: For over half of small companies, all it takes is one data breach to go out of business within 6 months.
What does this mean?
Startups need to invest in cybersecurity as much as large companies do, ideally from the onset. Fortunately, nowadays, there are affordable solutions for startups to access cybersecurity services and expertise historically reserved for large companies:
Instead of building out expensive in-house security teams, many startups turn to Virtual CISO Services as an alternative. Additionally, there are measures any startup can take right away to improve security, which we'll discuss in the section "5 Practical Things To Do Right Away".
But first, let's talk about the most common threats faced by startups in 2025. We'll keep these in mind when suggesting security measures you should consider.
Common Security Threats Faced by Startups in 2025
According to Verizon, 92% of tactics threat actors use against small businesses are either:
- Social engineering tactics, such as phishing emails.
- Basic web application attacks.
User credentials (like passwords) are the most frequently compromised type of data. This is because threat actors know this type of data is particularly vulnerable when hosted and processed by small organizations without strong security.
Even if you aren't at the stage where you want to explore building out a comprehensive security program, there are a few things you can do in the short term.
With the most common threats faced by startups in mind, here are 5 solutions that will mitigate a huge amount of risk right off the bat:
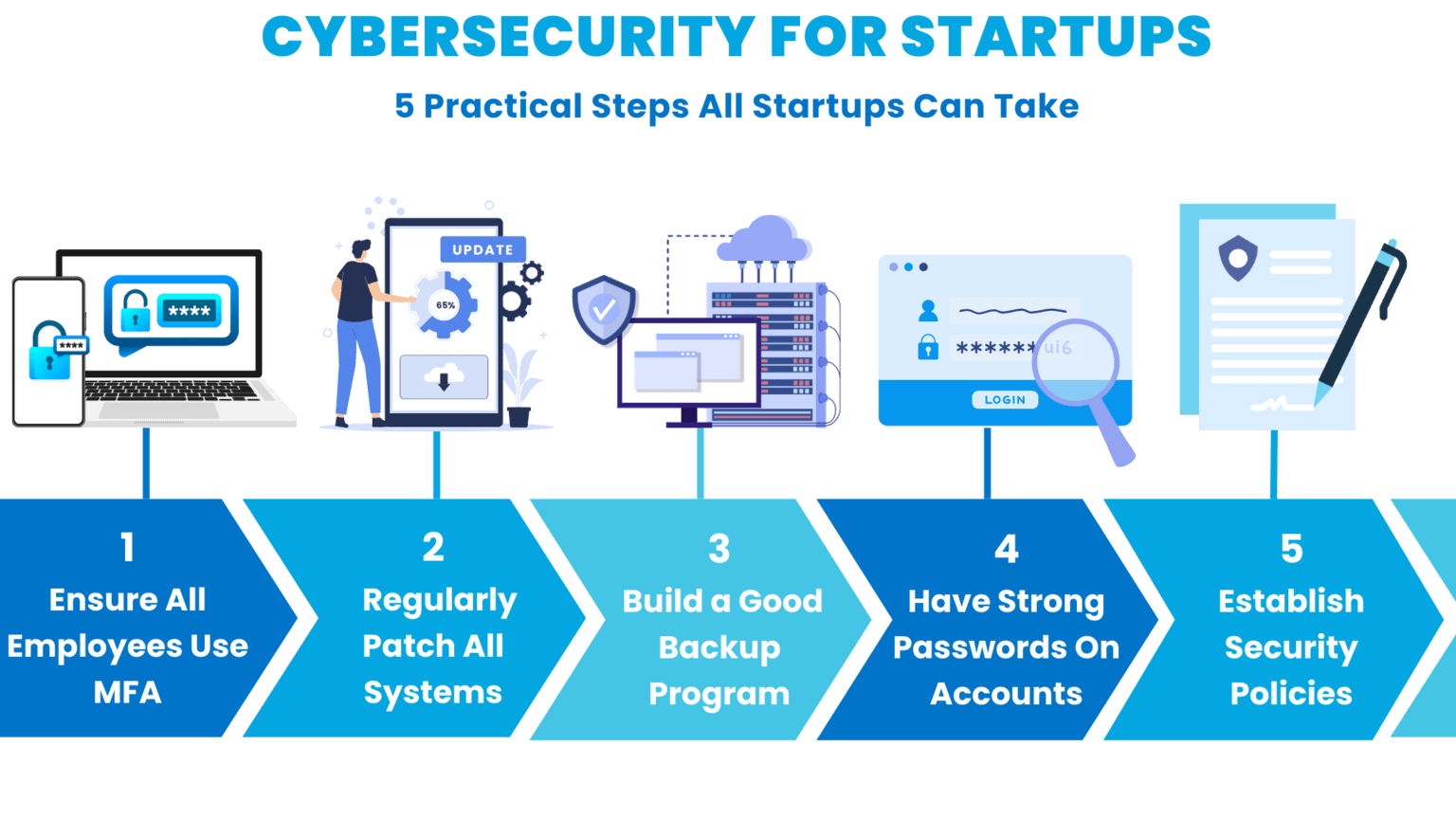
Cybersecurity for Startups: 5 Practical Things To Do Right Away
We get how much running a startup involves on a daily basis.
Even if you're crunched for time and resources, fortunately, there are a few 'quick win' measures you can take to improve your security immediately!
Some of these may seem basic. But you would be stunned how many people, even in high-level positions, are using passwords like "032564Oreo (user's birthday + their cat's name), or "newpassword2025!" (self-explanatory).
It's best to play it safe and operate from the assumption that most people simply don't practice good security hygiene. It's on company leadership to provide guidance and policies.
With this in mind, here are 5 measures you can take right away:
1. Ensure All Employees Use MFA At Your Startup
Multi-factor authentication (MFA) is critical to an effective security program.
Implementing MFA across all accounts, including cloud access, network access, and even SaaS access accounts, is the number one thing you can do to reduce the risk of a major incident or breach.

Without MFA, all a major breach takes is a single employee setting a weak password, which a threat actor then identifies through password spraying or traditional leaks.
Beyond simply setting up and requiring MFA, there are additional steps you should take in light of the current threat landscape in 2025. Unfortunately, threat actors have inventive ways around MFA nowadays.
To mitigate this risk, here are some important tips when setting up MFA controls:
- Understand where your customer data lives. Individual teams and employees may purchase new SaaS applications on their own authority and begin storing customer and other data in these systems. Without adequate controls and visibility, employees may be storing customer data in SaaS solutions without MFA that your IT and security teams are unaware of.
- Set short time-to-live (TLL) on session cookies where possible. Session cookies allow a user to reauthenticate without having to reenter a code for a set duration of time. If session cookies are stolen in the meantime, they can be used in a session replay attack to bypass codes. Setting time-to-live for cookies as shortly as possible does inconvenience users, but reduces the risk that if a threat actor steals cookies, they can be effectively used.
- When implementing MFA, it is strongly recommended to use authenticator applications rather than SMS-based authentication when possible. SMS-based authentication is susceptible through a practice known as "SIM Swapping," in which threat actors either social engineer or steal the means to swap SIM devices at the carrier level, allowing them to hijack a user's cellphone traffic.
2. Make Sure All Systems Are Patched
Many cyberattacks happen as a result of organizations not building a successful vulnerability management practice. Threat actors continuously scan for publicly facing IT assets with known vulnerabilities to identify potential targets to exploit.
A great example of this is the WannaCry ransomware attack in 2017. The exploit used by threat actors had actually been patched in Windows two months prior to the attack. Devices up-to-date on the latest security updates were not impacted by the attack. Meanwhile, devices that hadn't kept up with the latest patches were left vulnerable.
Vulnerability prioritization can be a pain. It isn't always clear when a vulnerability is critical versus when it can be delayed somewhat. Additionally, patches can be extremely disruptive to existing IT infrastructure. All of this makes effectively patching systems quite difficult. Here are a few tips:
- Prioritize vulnerabilities on publicly facing systems first: Threat actors regularly scan the internet looking for known exploitable vulnerabilities on publicly facing systems. An instance of this in 2025 includes the ConnectWise ScreenConnect vulnerability. Another recent example includes the MOVEit vulnerability.
- Prioritize actively exploited vulnerabilities: Not all vulnerabilities are equally high-risk. Vulnerabilities that are theoretical or haven't been known to be "actively exploited in the wild" are likely lower risk and can be deprioritized compared to those that threat actors are utilizing.
- Use a vulnerability management service like Shodan: Shodan can help identify publicly facing IT assets along with services running on them. This can dramatically expedite mapping your organization's attack surface and identifying services that may have exploitable vulnerabilities.
3. Build A Cybersecurity Program With an Extensive Backup and Recovery Program
It's no secret that ransomware groups often encrypt sensitive data belonging to organizations. But ransomware isn't the only reason you should have a strong backup and recovery program.
Natural disasters, unexpected outages, and threat actors can all compromise the confidentiality, integrity, and availability of data. This creates enormous risk.
Create not just a backup system for your startup, but a backup and recovery program that includes technology (either localized or cloud backups), processes (policies and procedures), and people responsible for ensuring it all works together.
Once you have a system that works, test it!
Tabletop exercises can be invaluable in testing real-world examples to make sure that your system works, everyone knows their role, and you can effectively respond to a crisis.
Bonus Tip: Be sure to back up your "less" critical systems.
Don't underestimate the dependencies between data and software applications. Even if your organization has multiple systems, don't isolate backup and recovery to "only" the most critical. It is often easy to overlook data dependencies between systems where one system going down can render another entirely nonfunctional.
4. Ensure All Employees Have A Strong Password
Many organizations make the mistake of believing that if they have strong two-factor authentication, they are adequately protected and don't need to worry too much about weak passwords. This couldn't be further from the truth.
If you have a weak, easily guessable password and two-factor authentication, you only really have single-factor authentication!
IBM's recent X-Force Report showed that identity-based attacks that involve leveraging valid user accounts are now the predominant way threat actors compromise environments. Compromising a single valid user account with administrative privileges can quickly escalate into a full-blown breach.
Multi-factor authentication means your organization has strong passwords and monitors password reuse. Here are a few tips to ensure employees are using good passwords:
- Create strong passwords with a length requirement, special characters, numbers, and letters.
- Use a credential monitoring service like haveibeenpwned to identify if a user's credentials have been compromised in a data breach. Rotate credentials immediately if this has happened.
- Talk extensively about password hygiene during regular security trainings. Emphasize not to reuse passwords across services. Walk users through how reusing passwords can result in the organization being compromised.
Bonus Tip: Use a password manager like 1Password.
Tools like 1Password automatically create strong passwords, which are then encrypted and stored so that only authorized users can access them.
This allows members of your team to share passwords without showing the actual password. Additionally, employees can access business-critical accounts across multiple devices without having to remember complex passwords.
If your startup has a remote workforce and employees are logging into their work accounts on multiple devices, a password manager is a must-have.
5. Establish A Written Security Policy
Establishing a written security policy is one of the most critical things you can do to create a strong cybersecurity baseline for your startup.
Rhymetec's Senior Cybersecurity Analyst, Kyle Jones, recently spoke about how to draft and communicate strong security policies. Here are a few tips he suggested:
- Know your audience. If the people who need to understand and adhere to your security policies aren't security knowledgeable, keep that in mind. Don't use overly technical language in your policies. Instead, tailor your language to your audience.
- Emphasize your policies continuously, and connect policies with the reasons behind them. People will be more likely to follow policies if the reason behind them is explained. Find opportunities, such as when an employee has an IT-related question, to reference the policies and see what they say.
- Make sure your policies reflect current trends. Your risk profile changes depending on what's going on in the world! For instance, the launching of large language models (LLMs) like Google's Gemini should make you rethink your policies.
Here are several critical questions about AI:
- Do you know if your employees are sharing data with any LLMs they may be using for work?
- Do you have an established policy around the use of this technology at your startup?
- What about updates to regulatory language around AI? Do your policies take that into account?
A great example of why these questions need to be visited can be seen in Samsung's 2023 data leak with Chat GPT - the company has since banned the internal use of generative AI tools.
Bonus Tip: Create a culture that prioritizes security and transparency.
Share resources and talk to your team regularly about the importance of security.
Don't fearmonger - you never want your employees to feel like they can't come to you if something happens. Make it clear that your door is open, and you want to know if they receive a suspicious email or if they notice unfamiliar software on their work device.
Cybersecurity for Startups: Measures To Further Improve
So, you've made sure your employees are using MFA and that nobody's password is their cat's name. You regularly update all of your systems, back up your data, and already have security policies in place.
Here are the next steps you should take:
1. Build A Formal Process to Assess The Security of Third-Party Vendors and Suppliers
Third-party risk management continues to grow in importance for organizations of all sizes.
We recommend building a full inventory of all third-party suppliers your organization uses and implementing a standard risk screening. Fortunately, modern standards make it easy to quickly screen to see if a potential third party takes information security seriously.
We recommend asking questions like:
- Does your organization have a SOC 2 Type 2 Report, or other third-party attestation on your information security program?
- Are you compliant with the HIPAA Security Rule, New York Department of Financial Services Cybersecurity Rule, or other formal legal requirements?
- Does your organization have documented security policies?
- Do you share customer data with third parties? If so, which ones?
2. Conduct Routine Pen Testing Engagements
Engage a third party (such as Rhymetec) to regularly put your security controls to the test.
Regular pen testing identifies gaps that potential attackers could exploit. Pen tests should be scoped to the specific risks that your organization faces. For example, Rhymetec can help with:
- Web application pen testing to identify vulnerabilities and misconfigurations in web apps.
- Mobile application penetration testing to identify vulnerabilities or exploits in mobile apps that could be exploited.
- Network penetration testing to identify ways that your organization's network could be exposed.
Pen testing is critical to meeting numerous security requirements. It also enables you to better answer questionnaires about your organization's security provided by potential customers.
3. Conduct Simulated Spear-Phishing Tests
Simulated phishing exercises represent another very significant opportunity to improve your security.
Running realistic simulated phishing tests can help condition employees to be wary of even realistic-looking emails purporting to offer them gift cards and sensitive information. Make sure emails look realistic and are targeted. Sending generic emails generated by a platform can come across as too obvious and fail to adequately test users.
Take an attacker's perspective - what might an attacker write without inside knowledge of users to get users to click links?
Bonus Tip: Have An Incident Response Plan In Place.
An incident response plan is a set of documented procedures to act on in the event of a security incident. For instance, do you know what steps to take in the event your startup experiences a ransomware attack?
To recall an earlier example, during the WannaCry ransomware attack in 2017, many victims paid the ransom to try to get their data back. Security professionals generally do not advise paying ransoms. The threat actors behind the WannaCry attack did not restore people's data even after they'd paid the ransom.
Having a documented incident response plan equips you with important know-how in the event you are to experience an attack or a data breach. This saves time, money, and headaches if an incident were to occur.
Balancing Security With Budget
Building good organizational security is critical. However the cost of protecting an asset shouldn't have to exceed the value of the asset.
Cybersecurity for startups needs to be balanced against ease of access, business processes, and the risks associated with the service, data, or application being secured.
At Rhymetec, we work with a lot of SaaS startups who need to build a security program typically because their customers require it and it's difficult to compete in the marketplace without one. These startups are working off a limited budget.
A good place to start to figure out how to balance security with budget is to think about the answers to the following two questions:
- What does your risk profile look like? Narrowing down the specific risks facing your organization helps prioritize where you need to spend your security dollars. For example, if you are located somewhere that's prone to earthquakes and your servers are stored there, that's a high risk. You would want to prioritize taking steps to remediate this.
- What's your risk appetite? Understand what your own risk tolerance is - If you have a low-risk appetite, you will want to commit to remediating any medium or high risks. Or, at the very least, look at how to reduce your risk from high to low in the areas of highest risk.
At Rhymetec, after we assess your risk profile and answer these questions, we get creative on the best way to proceed with building your information security program while keeping in mind budget constraints.
Frequently Asked Questions (FAQ) for Cybersecurity for Startups in 2025
Here are 5 questions we see frequently from startups in 2025. Knowing the answers to these questions - and implementing corresponding policies - is essential for robust cybersecurity for startups.
1. What are some commonly required or requested compliance frameworks for startups in 2025?
- SOC 2 is a voluntary standard often requested by customers to show you take security seriously and that their data will be in good hands if they share it with you.
- ISO 27001 is the leading international standard for information security.
- PCI DISS is necessary if your startup processes credit card payments.
- GDPR is required in 2025 if you handle the personal data of EU citizens.
- HIPAA privacy regulations require organizations dealing with healthcare data to follow procedures around the confidentiality and security of PHI (Protected Health Information).

2. How does the increasing shift to remote work impact cybersecurity for startups in 2025?
Cloud security is critical in the age of remote work.
Without proper controls, even daily activities like file sharing can result in sensitive information being shared with unauthorized users. Following best practices for cloud storage is essential in 2025, including:
- Make sure your employees have a strong separation between work and personal documents and devices.
- Invest in backing up your data to prevent the loss of important information and documents.
3. What should startups do from a security standpoint with all the AI hype?
AI amplifies existing threats, especially social engineering attacks. For example, AI can be used by threat actors to generate a larger number of personalized phishing emails.
This simply means that the best way to protect your business from AI-assisted threats is to strengthen your core security program. Staff awareness training to protect against social engineering attacks is especially important.
4. What are some best-of-breed tools startups can easily utilize in 2025?
As discussed earlier, the attack surface of small organizations is starting to increasingly resemble that of large organizations. What if you could monitor this, even down to the individual employee level?
Services like Picnic enable you to minimize the human attack surface of your startup and protect executives, contractors, and employees from social engineering attacks.
Nowadays, fortunately, there are tools that make security more accessible. Even if you have zero technical background, you can seamlessly integrate tools like Zip Security that provide enterprise-grade security and endpoint threat detection.
5. When is the right time to start looking into cybersecurity for startups?
The straightforward answer here is that if you're reading this, the right time is now.
Don't wait for the perfect time. The reality is that early-stage startups are unfortunately particularly vulnerable to cyberattacks, precisely because threat actors know they often lack even basic security practices.
Plus, it's always better to start building your security program early on so it can grow in alignment with your needs as your startup scales. Implementing a robust information security program after growth involves even more time, money, and resources to catch up.
How MSSPs Can Accelerate Cybersecurity for Startups in 2025
Hiring an external security team can substantially help organizations, especially in the early stages.
Virtual CISOs at organizations like Rhymetec have extensive experience balancing budgetary needs, usability, and security for start-up cybersecurity programs. It's not an easy balance, but leveraging an experienced partner can deliver huge amounts of specialized talent without the need to spend millions of dollars on an in-house security team.
Managed Security Services Providers like Rhymetec have dozens of professionals across security disciplines like cloud security, compliance, web application security, penetration testing, and others. They have the experience putting these skills to work for startups in a way that drives real security outcomes as you scale while also keeping your budget in mind.
To learn more about how our team can accelerate your security while keeping your budget in mind, contact us for more information.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering. Under Metin's leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
Imagine a large financial institution facing a sophisticated cyberattack. Instead of spending many hours on human analysis to understand and mitigate the danger, an AI-powered security system can swiftly identify the anomaly, analyze the threat in real time, and neutralize it before any significant damage can be done.
This is how AI can transform the cybersecurity landscape in 2024.
In recent years, the adoption of artificial intelligence (AI) in cybersecurity has increased. From a market valuation of over $10 billion in 2020, AI in cybersecurity is likely to reach $46.3 billion by 2027, growing at a compound annual growth rate (CAGR) of 25.51%. With 69% of organizations considering AI essential for responding to cyberattacks, the business world increasingly relies on it to protect cyber assets.
How Ai Will Shape Future Cybersecurity Strategies
Here are eight ways the increasing investment and reliance on AI will shape future cybersecurity strategies.
1. Impacting Compliance
As the use of AI in cybersecurity grows, its ability to process large volumes of data also grows. Strict privacy laws like the GDPR in Europe and the CCPA in the USA create challenges for companies. With 90% of people concerned about data privacy and 72% finding existing regulations inadequate, governments and regulatory agencies are now formulating new guidelines for AI’s use in cybersecurity.
Under these new regulations, organizations should proactively collect and analyze threats that could affect them, ranging from cyberattacks on chat platforms to geopolitical issues and international conflicts. Instead of focusing solely on risk assessments, companies must take a broader approach to identify threats and craft strategies to address or prevent them.
2. Expanding Across Sectors
AI’s use in cybersecurity has expanded across multiple sectors, and leaders should expect this trend to continue. Industries that have experienced significant increases in cyber-attacks in recent years include banking, with a 238% increase in cyberattacks over the past five years, and healthcare, where the number of cyberattacks in the sector rose by 74% in 2022.
As businesses continue to face unprecedented cyber threats, cybersecurity becomes critical. AI’s role in threat detection and response is vital for robust cybersecurity strategies.
3. Enhancing Threat Detection And Response
As AI becomes more entrenched in cybersecurity, its role evolves. It currently includes threat detection, predictive analytics, and response mechanisms. Approximately 51% of businesses use it for threat detection, 34% for predicting potential security incidents, and 18% for response mechanisms.
However, technological advancements in AI will continuously lead to more sophisticated tools, capable of analyzing complex datasets and effectively countering advanced cyber threats. Integrating AI into threat management shows its growing importance in proactive, predictive cybersecurity strategies.
4. Increasing AI And Machine Learning Spend
The trend of increased investment in AI and machine learning for cybersecurity is becoming more pronounced, with 71% of organizations now allocating more budget to these technologies than just two years ago. This growing financial commitment recognizes the benefits AI and machine learning bring to cybersecurity.
These technologies enhance security measures while introducing innovative approaches and greater accuracy in threat detection, predictive analytics, and response strategies. As cyber threats become more complex, reliance on AI and machine learning is expected to grow and drive further advancements and budget allocations.
5. Advancing Technological Innovations
Continuous advancements in AI technology have led to more sophisticated and effective cybersecurity tools. Quantum computing is one of the most significant emerging technologies. It offers superior processing power that enables AI systems to analyze and react to cyber threats faster and more efficiently.
Additionally, developments in areas like natural language processing and predictive analytics enable AI systems to anticipate and neutralize potential threats more accurately. AI-driven cybersecurity tools can learn from past incidents, improving their response strategies. This adaptability ensures cybersecurity measures remain robust against evolving cyber threats.
6. Addressing Complex And Evolving Threats
As cyber threats become more complex and sophisticated, algorithms learn and adapt from each interaction or breach attempt. AI’s ability to rapidly analyze large data sets and recognize patterns makes it invaluable in identifying and countering advanced cyber threats. Adaptability allows it to continuously update and refine its algorithms based on new data and emerging threat patterns.
7. Combating Security Vulnerabilities
While AI enhances cybersecurity, it also poses risks. If misused, it can facilitate network breaches and unintentionally expose sensitive information, impacting large organizations’ reputation and customer trust. Ethical AI frameworks and robust security protocols ensure AI operates within defined moral and ethical boundaries, preventing misuse or biases that could lead to security vulnerabilities.
As AI becomes more sophisticated, so do the methods to exploit it. The human element of cybersecurity is often the first line of defense against AI-related risks. Leaders should ensure that cybersecurity systems are safeguarded against manipulation, data poisoning, and other forms of attack. To do this, organizations must invest in training and awareness programs about the risks associated with AI systems and the best practices for avoiding them.
8. Contributing Positively To Cybersecurity
AI’s enhanced threat intelligence significantly boosts cybersecurity through its ability to analyze vast amounts of data faster and more efficiently to identify and respond to potential threats. Algorithms establish normal network behaviors and quickly identify anomalies to minimize the impact of attacks.
Meanwhile, AI-driven chatbots have transformed customer support by providing around-the-clock operational assistance. The technology automates the initial stages of an incident response, freeing up security teams to focus on threat analysis and mitigation.
Building A More Resilient Security Posture
In the long term, integrating AI into cybersecurity leads to a more resilient security posture. AI’s continuous learning and adaptation mean that security systems can evolve alongside the ever-changing cyber threat landscape. This approach keeps your cybersecurity measures up to date, providing robust protection against current and future threats. And that, as they say, is priceless.
Kortak is the Chief Information Security Officer at Rhymetec, an industry-leading cybersecurity firm for SaaS companies.
You can read the original article posted in Fast Company by Rhymetec CISO, Metin Kortak
About Rhymetec
Rhymetec was founded in 2015 as a Penetration Testing company. Since then, we have served hundreds of SaaS businesses globally in all their cybersecurity, compliance, and data privacy needs. We’re industry leaders in cloud security, and our custom services align with the specific needs of your business. If you want to learn more about how our team can help your business with your security needs, contact our team for more information.
If your organization is interested in exploring compliance with AI standards, we now offer ISO/IEC 42001 certification readiness and maintenance services and are happy to answer any questions you may have.
Contact Us
Interested in reading more? Check out our other content:
- 6 Ways Cybersecurity Is Important For Business Growth
- Maximizing Your Use Of Compliance Automation Platforms: A Complete Solution
- Understanding ISO 42001 Controls: Implementing and Managing Artificial Intelligence Responsibly
The new cybersecurity directive is the first to propose mandates for securing data. Here’s what that could mean for SaaS firms...
In recent years, report after report has highlighted how cyber attackers have made short work of accessing everything from personally identifiable information to research data and other intellectual property. Reports show that hackers have targeted healthcare since 2014. Russia is suspected of a series of cyberattacks during the COVID-19 pandemic, and the U.S. Department of Health and Human Services reported that there were 642 healthcare data breaches in 2020, exposing over 27 million patient records. These incidents highlight the ongoing threat of cyberattacks and the need for increased security measures to protect sensitive data.
3 Steps Companies Can Take to Prepare for the National Cybersecurity Strategy Proposal
- Build a cybersecurity program using a globally accepted cybersecurity framework.
- Implement data privacy controls using guidelines from GDPR and CCPA.
- Implement fundamental cybersecurity best practices such as encryption at rest, IDS/IPS, regular vulnerability scans and annual penetration testing, etc.
The Biden administration has made cybersecurity a clear priority. While every administration since 2008 has issued Presidential Directives on cybersecurity, the current strategy is the first to propose mandates for securing data and making organizations liable for not implementing cybersecurity controls.
This strategy has important connotations for SaaS businesses and impacts the steps they take to improve their security posture.
What to Know About the Proposed Cybersecurity Strategy
The Biden-Harris administration's proposed National Cybersecurity Strategy aims to close the current gap between compliance standards and government regulations. Many private entities comply with cybersecurity frameworks such as SOC 2 and ISO 27001 that require preventive security controls, such as continuous monitoring and regular vulnerability assessments. However, these frameworks are optional.
While government organizations implement privacy laws such as GDPR and CCPA, they haven’t released laws that require private organizations to implement specific cybersecurity measures.
The proposal recommends implementing several cybersecurity strategy best practices. These include:
- Expanding the use of minimum cybersecurity requirements in critical sectors.
- Defending and modernizing federal networks.
- Updating federal incident response policies.
- Engaging the private sector in disruption activities through scalable mechanisms.
- Addressing the ransomware threat through a comprehensive federal approach.
- Shifting the liability for software products and services to promote secure development practices.
Engaging the private sector and shifting liability of cybersecurity to software products and services is a major change in the U.S. government’s cybersecurity strategy. By shifting liabilities to private software products and services, the U.S. government can hold private entities liable for not implementing certain cybersecurity controls.
For example, if the new strategy were to become law, it could potentially make it illegal for organizations to collect sensitive data without encrypting it. Currently, when private organizations don’t comply with security controls from compliance frameworks, they simply don’t receive their certification or report.
Under the new proposal, organizations could be fined or even face legal ramifications if they do not comply with the security controls required by the U.S. government. This could upend the entire tech industry, and suddenly, many organizations would become out of compliance if they don't have the necessary security measures in place.
How the National Cybersecurity Policy Impacts SaaS Companies
It’s important to note that the strategy is not yet a law but a policy document, so it doesn’t change how we deal with cyberattacks as of now.
Still, the proposal’s shift of liabilities to software products and services is likely to ring alarm bells for SaaS business owners. Currently, consumers are responsible for software vulnerabilities that result in cyberattacks. For example, if a user downloads new software that introduces a vulnerability and allows access by an attacker, the software manufacturer is protected by the software licensing agreement signed by the user accepting the risk of liability.
Under the new strategy, however, the software producer would be liable for enabling the vulnerability to be introduced to the user’s computer. If this strategy is signed into law, SaaS businesses will need to reallocate funds and other resources to cybersecurity to comply with government regulations. This change will require new roles, responsibilities and assets in cyberspace.
What SaaS Companies Can Do to Prepare for the New Cybersecurity Strategy Policy
To best prepare, organizations should implement some fundamental cybersecurity controls and follow best practices. If an organization is already complying with some of the most common frameworks such as NIST 800-53, SOC 2 or ISO 27001, then they are already one step ahead.
There are however three actions organizations can take right now to prepare for this potential law, and those include:
- Build a cybersecurity program using a globally accepted cybersecurity framework.
- Implement data privacy controls using guidelines from GDPR and CCPA.
- Implement fundamental cybersecurity best practices such as encryption at rest, IDS/IPS, regular vulnerability scans and annual penetration testing, etc.
Currently, private entities are responsible for securing the majority of U.S. citizens’ data. Shifting liabilities to software products and services is a major change to protect data privacy that will significantly strengthen the nation’s cybersecurity posture. The proposed National Cybersecurity Strategy is a significant step in promoting secure development practices and protecting data privacy.
While the strategy is still in the proposal stage, it has the potential to shift liability from consumers to software producers. That means SaaS businesses need to begin adapting their focus and resources now, both to comply with future regulations and to ensure their cybersecurity posture is strong — regardless of what happens at a national level. By implementing minimum security requirements, modernizing your networks and updating your incident response policies, you can take a giant leap toward protecting your company from attack.
Click here to view the original post on Built-In by Rhymetec CISO, Metin Kortak.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering. Under Metin’s leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
Rhymetec also offers a range of penetration testing services including:
- Mobile Application Penetration Testing
- Web Application Penetration Testing
- External Network Penetration Testing
- API Penetration Testing
Interested in reading more? Check out our other blogs: