
Meet Aaron!
Hi, I'm Aaron!
I originally grew up in South Florida and have built my career around Cybersecurity and Service.
I recently achieved my CISSP this year, which was a huge hallmark achievement.
I am also extremely active in the local Atlanta Cybersecurity scene and have dedicated most of my spare time to enabling others in their careers.
Tell us a surprising fact about yourself…
I was once very briefly a DJ, and have played 3 different instruments in the past, including being in 2 different marching bands.
If you could have any superpower, what would it be?
Give me the powers of Statics Shock, the ability to control electricity!
What are some things you enjoy doing outside of work?
I enjoy a variety of hobbies which include video games and car meets, as well as travel.
And of course, who doesn't love sleep?
Tell us about your role at Rhymetec…
I was hired in February and work as a Cloud Security Compliance Analyst; my responsibilities include driving compliance programs to maturity and preparing them for audits.
I also perform audits here and offer our clients insight into the Cybersecurity Industry based on my knowledge and experience.
Why did you pursue a career in the cybersecurity industry?
I always knew I wanted to be in Cybersecurity since I was 14 and moved out of state to pursue my career.
I have the natural aptitude and gifts for cybersecurity related principles and I feel confident every day because I am doing what I love, and just happen to be pretty good at it, so I've been told.
What is your favorite quote or the best advice you have ever received?
"There is no losing, either you win, or you learn, and try again".

From a security or compliance perspective, what advice would you give to a potential client or SaaS business?
Rhymetec clients receive benefits beyond just Compliance Attestation for Trust Certifications (Such as SOC 2 and ISO 27001).
Though this is important and drives value and revenue for every business, there are other benefits that should also be recognized.
Ultimately, there is a huge misconception that "Security" and "Compliance" are equivalent and this is simply not true; Rhymetec addresses this divergence with our blended offerings which simultaneously educate our clients on best practices and industry standards while providing easy to understand guidance to help promote security awareness.
Between all our staff we employ decades of expertise from a wide range of backgrounds within the cybersecurity industry that contributes to our unique insight and ability to protect our clients' businesses from cyber risk.
Connect with Aaron
So, you're a quickly growing startup. One of the last things you want to be thinking about is security and compliance. You want to focus on what really matters - moving your business forward. As a small business ourselves, at Rhymetec, we understand that completely.
But maybe you recently suffered a breach, or maybe a potential client asked you for a security questionnaire, and you realized completing one on the spot was probably not going to cut it.
In any case, you've decided to enter the extremely interesting world of security and compliance for startups. We're going to cover the different types of cybersecurity firms that work with startups, which types of consulting engagements make the most sense for startups, and how to wade through the noise and pick a firm that will act as a partner.
Compliance For Startups: The Maze of Acronyms & Types of Engagements
If you're just getting into looking for a cybersecurity firm that works with startups, be warned in advance - you are going to run into a lot of acronyms. Below are some of the most common acronyms and what they mean:
AV - Anti-virus software that is used on a computer (which is also often referred to as an endpoint because why not complicate everything).
SOC - Security Operations Center, which handles day-to-day alerts aggregated by the SIEM and other systems.
EDR - Endpoint detection and response software that is deployed to an endpoint (since we might as well use a term that acts as both a monitoring tool to detect malicious software and also as a mechanism to contain the device or respond to potential incidents).
SIEM - Security intelligence and event management software that serves as the brain of a security operation, pulling in logs and data from dozens of different systems to act as a single source of truth for a security program.
ISO 27001 - An international standard for information security management systems (ISMS) that provides a framework for managing and securing sensitive information. It focuses on risk management and data protection.
GDPR - Europe's General Data Protection Regulation, enacted in 2016. GDPR requires organizations to safeguard EU consumer data and build governance processes that enable the correct handling of EU citizen data.
SOC 2 - System Organization Controls. A voluntary compliance framework that demonstrates to potential customers that your organization has a security program with standard security controls in place.
HIPAA - The U.S. Health Insurance Portability and Accountability Act. A data privacy law relating to healthcare that also includes a "Security Rule" requiring organizations to take predefined steps to secure patient data.
CISO - The Chief Information Security Officer is the individual responsible for the security of the organization.
vCISO - A virtual Chief Information Security Officer is an outsourced CISO as a service option. This individual (or team) provides strategic security leadership, risk management, and compliance guidance and implementation without the need for a full-time, in-house executive. This option can be ideal for startups and SMBs who may not need to make a full-time hire for this role. vCISO pricing can vary widely depending on the scope of work and level of assistance you need.
MSSP- A Managed Security Services Provider is a company that provides outsourced compliance and security services, such as threat monitoring, incident response, vulnerability management, and more, to protect clients' digital assets.
Some of these terms may be extremely relevant to you, depending on what has sparked your interest in exploring compliance for your startup. Let's take an example:
The Need To Build Security Into The Foundation of Your Business
Imagine your organization has just been the victim of a significant ransomware attack. Many of your sensitive files are now published on a ransomware site, creating enormous disruption to your business.

Many companies that find themselves in this situation panic and immediately engage the first MSSP they can find to help them recover. This is due to the fact that many organizations tend to take a siloed view of information security.
If you are the victim of a breach, you may think you need to work with one firm. If you need compliance, you might think you need to work with a different firm, and you may also think it's only worth seeking out the right firm when there's an issue.
This mindset could not be further from the truth. A good security firm will help with building a program that effectively addresses compliance, governance, technical controls, and incident response in a way that minimizes friction and effectively leverages people, processes, and technology to holistically reduce both the risk of security incidents and the risk of compliance violations.
Choosing the Right Compliance Firm For Your Startup: What Are Common Red Flags To Watch Out For?
Let's start by talking about what to look out for (and be wary of) when evaluating different potential service providers for your organization to work with:
Organizations that promise 100% risk reduction or similar vague and aspirational promises. Unfortunately, we live in a world where 100% security is not possible. These vendors are likely selling snake oil.
Service providers that start by trying to sell you something rather than understanding your needs. Security is a process and needs customization for the end client.
Consultants who have you only speaking to sales without talking directly to the practitioners (like a vCISO) who are doing the work. Good salespeople can be extraordinarily helpful in coordinating engagements but shouldn't take the place of security expertise if you have more technical questions or concerns.
Organizations that plan all communication through email and don't set up regular engagements with you (the customers). Security should be a continuously integrated part of your business. An email a month from your "security team" won't cut it.
Firms that cap hours. MSSPs that set strict hour limits can leave your business vulnerable if issues arise outside of the allotted time. Security needs don't follow a clock, and your provider should be able to respond effectively without arbitrary limitations.
Firms that outsource their services. Some MSSPs may outsource critical functions to third parties, leading to potential inconsistencies in quality and responsiveness. Your security provider should have a clear, direct line of accountability for all services they offer.
Be sure to ask if they outsource any services overseas in particular, and if so, where. Outsourcing overseas can impact a vendor's control and oversight, and certain locations may have different regulations and standards around security.
5 Green Flags To Look For In Firms Providing Security & Compliance Services For Startups
Now, what types of characteristics should you look for in a firm that will help your organization succeed?
Geographically Local Talent
There are incredible security professionals all over the world. However, organizations have dramatically different risk profiles based on their local geography and regulatory environments. A healthcare practice in Italy has an entirely different set of laws and regulations than a medical clinic in New York. Choosing a security provider that has staff and experience in your country helps streamline the process and avoid miscommunication and knowledge gaps that may occur by trying to outsource the work.
Strong Communication
A reputable security services firm should be willing to join a Slack channel with you or establish another near-instant way to communicate directly between security practitioners and corporate staff. Effective communication is absolutely critical to building a great cybersecurity program.
Experience Across Compliance For Startups And Cyber Risk Reduction
Many people view cybersecurity compliance as a tradeoff with risk reduction. You can be compliant, or you can run a "serious" security program focused on reducing risk. This is reductive and untrue. Building an information security program that also reduces risk for an organization should be the goal of every security team.
They Ask Good Questions
What business problem are you trying to solve by working with a firm that specializes in compliance for startups?
This is an important question that all firms should be asking their prospects. When a consultant tries to understand the business problems you are trying to solve, it improves their ability to generate positive outcomes from the engagement.
Transparent Pricing
Security programs are complex, and they can be hard to price. These facts are both true, but that doesn't mean the vendor should put that complexity on you.
Look for a vendor that is willing to provide straightforward, transparent, and honest pricing that makes sense for your organization.
Compliance For Startups: Pricing
So, how do firms price their security offerings? There are a few different methods:
Fixed Price/Project-Based: Using this method, the vendor estimates the work that needs to be done, writes a statement of work (SOW), and quotes a single fixed price for completion of the SOW. This is often the simplest option. In some cases, vendors can split payments into quarterly or monthly.
Flat Monthly Recurring Fee: Many vendors charge a flat monthly recurring fee, particularly for ongoing projects such as compliance maintenance, endpoint detection and response, or security operations center monitoring. This provides simplicity to the end client and avoids surprise billing.
Hourly: Many MSSPs and security consulting vendors charge an hourly rate. While hourly can be valuable in some cases, it can also be quite risky and lead to surprise billing and contractual disagreements.
Check out our blog post on vCISO pricing for more information on standard industry fees for security and compliance for startups.
From here, you should have a good idea of what to look for in a firm specializing in compliance for startups and be ready to start assessing vendors. As you select your MSSP or security consultant, it's important to take the time to thoroughly interview them and pick one that is right for your organization.
Lastly, it's important to work with a firm that stays on top of the latest changes in the regulatory landscape and integrates them into their service offerings. As new regulations like the Digital Operational Resilience Act (DORA) go into effect this year, you need to understand if these requirements impact your business and, if so, partner with a firm that already offers DORA Compliance Services.
If you have more specific questions, please feel free to contact our team:
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- 25 Cybersecurity Memes For 2025: The Ultimate List of Security and Compliance Memes
- Cybersecurity Tabletop Exercise: A Guide For Startups and SMBs
- vCISO Pricing Breakdown: Find The Best Fit For Your Needs
With data breaches and cyber threats seemingly making headlines every day, the importance of ethics in cybersecurity cannot be overstated. As businesses increasingly rely on digital solutions to manage sensitive information, trust becomes the cornerstone of successful relationships between companies and their clients.
But what happens when unethical practices enter the arena? Let’s take a deeper look at the role of ethics in cybersecurity and how businesses can build and maintain trust in a digital era.
The Ethics Of Outsourcing
One of the most pressing moral debates in cybersecurity today is about the outsourcing of services, often to overseas vendors. Many companies, driven by cost-cutting measures, turn to platforms like Fiverr or Upwork to handle critical aspects of their cybersecurity needs. But while outsourcing itself isn’t inherently unethical, the lack of transparency and control over who has access to sensitive data in these particular cases raises significant concerns.
When a company outsources its cybersecurity services without informing its clients, it risks violating their trust. Clients believe their data is being handled securely and locally, only to discover it has been outsourced to unknown entities worldwide. This practice not only undermines the trust of clients but also poses a significant security risk. After all, how can a company guarantee the security of its data if it doesn’t even know who is handling it?
Due Diligence: The Foundation Of Trust
This is another critical aspect of ethics in cybersecurity. Bringing on vendors without thoroughly vetting them or understanding who they, in turn, might outsource the work to exposes companies to major risks. Trusting a vendor based on their word or a polished presentation is not enough. Businesses must conduct thorough research to ensure their vendors have robust security measures in place and are transparent about their operations.
At my company, for instance, we conduct quarterly reviews of all our vendors to assess their security posture. This isn’t just a one-time check but a continual process of monitoring and evaluation. We look at key factors such as network security, business continuity, and any past breaches to determine whether a vendor remains a trustworthy partner. By doing so, we ensure our vendors uphold the same high standards of ethics and security that we promise to our clients.
Identifying Red Flags
Make sure you know who you’re working with and accept their claims with a healthy dose of skepticism. For example, if a vendor claims to have thousands of clients but only has a handful of employees on LinkedIn, consider it a red flag. Such a discrepancy suggests the company might be outsourcing work to unknown third parties, potentially compromising client data. If this isn’t the case, then it might suggest they’re lying about the number of clients they have, which is still another glaring red flag.
As a business, it’s essential to do your due diligence when hiring vendors or full-time employees in the cybersecurity space. This means looking beyond surface-level claims and digging deeper into their background, certifications, and past performance. Asking for referrals, checking their LinkedIn profiles, and verifying their claims are all part of this process. It’s about ensuring the people you’re entrusting with your data are both technically competent and ethically sound.
Transparency: The Hallmark Of Ethical Cybersecurity
Once you’ve established a strong foundation of ethics within your cybersecurity practices, the next step is to communicate this to the marketplace. Marketing your ethical standards is not just about showcasing security badges on your website. It’s about demonstrating an ongoing commitment to maintaining and improving your security posture.
For instance, some companies might claim to be SOC 2 compliant and proudly display this on their websites. However, if they are not undergoing an annual SOC 2 audit through an AICPA-accredited firm, their security posture might not be as robust as they suggest.
At my company, we emphasize the importance of continuous monitoring and evaluation. We encourage clients to take advantage of our partner solutions that offer a real-time view of their security posture. This way, they can see we’re not just resting on past achievements but are actively working to maintain the highest security standards, too.
Transparency is a key component of building trust in cybersecurity. Companies that are open about their security practices and publicize their security posture are typically more trustworthy. This doesn’t mean revealing every detail of your security measures but rather being upfront about your processes, controls, and commitment to ethical practices.
Ethics As A Competitive Advantage
Ethics can be a powerful differentiator in the highly competitive field of cybersecurity. Companies prioritizing ethical practices, from vendor management to operations, are better positioned to build and maintain client trust. As digital threats evolve, so must our commitment to ethical cybersecurity practices. By doing so, we can not only protect our clients’ data but also uphold the trust that is essential to our industry’s success.
You can read the original article posted in Fast Company by Rhymetec CEO, Justin Rende.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.
Regular cybersecurity audits are the best way to ensure your business continuously meets security and compliance requirements while reaping the business benefits of investing in security. This post will go over the different types of audits, their benefits for your organization, how to prepare, and common findings to be aware of.
For many fast-growing startups and SMBs, cybersecurity might not feel like a top priority. But with increasingly complex data regulations, rising threats, and growing client expectations, security can no longer be an afterthought, regardless of company size or industry.
The good news is that organizations that invest in improving their security posture and undergo regular cybersecurity audits start to see a wide range of benefits, especially once they have evidence they've successfully completed their audit through a certification or a report:
Barriers are removed in their deal flows, the time spent on filling out onerous security questionnaires is eliminated, and they can get back to what really matters - moving their business forward.
Why Cybersecurity Audits Matter For Your Organization
A cybersecurity audit is a thorough review of an organization's security posture, assessing the adequacy of protections in place to defend against cyber threats and meet regulatory requirements. You can think of an audit as a health check for your security practices, allowing you to identify potential vulnerabilities before they can lead to an actual security incident.
Audit findings provide valuable insight into how secure your organization is and how well you are meeting any relevant requirements. Knowing how well your security practices measure up against industry standards allows you to pinpoint where improvements need to be made, and make only the changes you actually need.
Cybersecurity audits identify vulnerabilities and show where your security measures align with or diverge from relevant frameworks like ISO 27001, SOC 2, and HIPAA. After an audit, as you enact necessary changes to address the audit's findings, you'll reduce the risk of regulatory penalties, reputational damage, and security incidents. Decision-makers can use the results of an audit to prioritize security improvements and guide their compliance efforts.
When clients, investors, regulators, or other stakeholders expect evidence of your security controls, having third-party verification of the strength of your security posture is important. It shows that you've addressed security requirements upfront, creates confidence in your security approach, and helps meet stakeholder expectations.

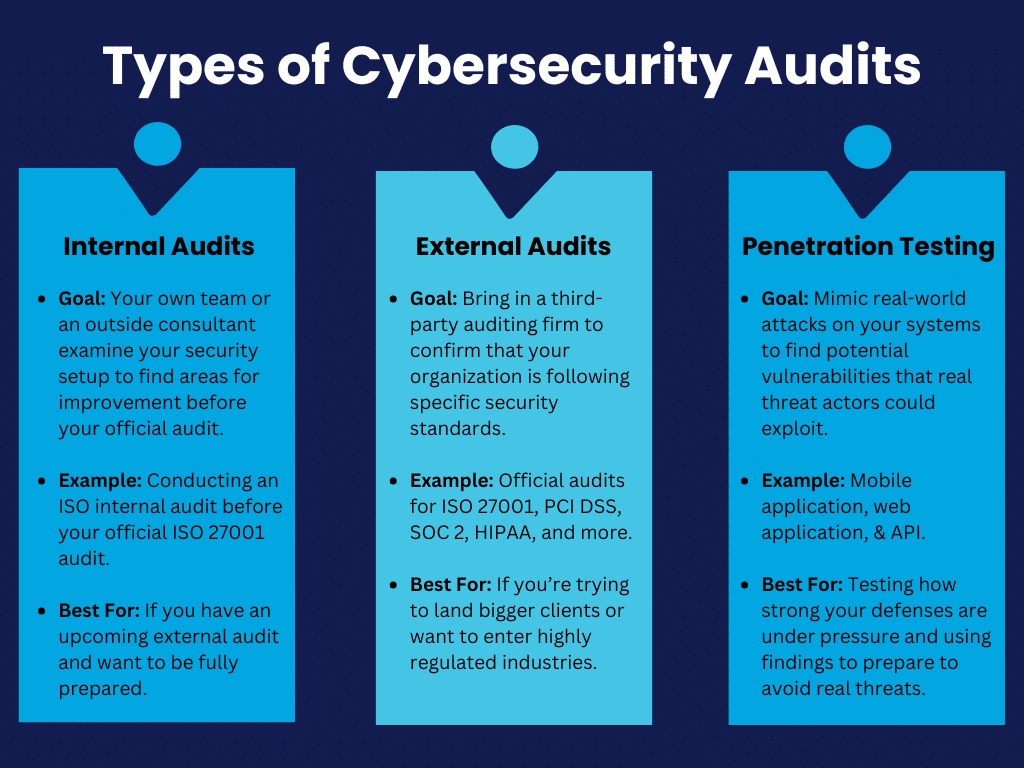
Types of Cybersecurity Audits Every Startup Should Be Aware Of
Startups should know about a few different types of cybersecurity audits:
Internal audits are when your own team or an outside consultant examines your security setup. The goal is to conduct a gap assessment and find any areas for improvement to help better prepare you for future external audits. For example, an ISO internal audit provides a way to spot weaknesses early and adjust them before your official audit for frameworks like ISO 27001 and ISO 42001.
External audits bring in a third-party auditing firm to confirm that your organization is following specific security standards such as ISO 27001, PCI DSS, SOC 2, HIPAA, and more. Passing an external audit is vital if you're trying to land bigger clients or want to enter highly regulated industries.
Penetration testing mimics real-world attacks on your systems to find potential vulnerabilities. Penetration tests give you an idea of how strong your defenses really are under pressure, and the findings help prepare you to avoid real threats:
How to Prepare For a Cybersecurity Audit
To prepare for an audit, the first step is to take a close look at your existing policies and procedures: Are they actually being followed?
It's common for companies to write policies that look great on paper but fall short in practice. You'll want to make sure everyone on your team knows their roles, especially around access controls, data handling, and your organization's incident response policies.
Don't neglect the tech side. Run vulnerability scans, review your logging and monitoring, and make sure your backups are up to date. Auditors will likely examine these areas regardless of which type of audit you undergo. Lastly, keep your documentation extremely organized. Auditors appreciate easily accessible and well-organized documentation. Having it ready can be the difference between a smooth audit and a chaotic scramble.
Bonus Tip: A compliance automation tool can come in extremely handy at this stage, as it allows a single place to upload and keep track of all of your documentation. Your auditor will appreciate being able to easily access everything in one place!
Preparing ahead of time as much as possible puts you in control of the process rather than reacting to questions or findings that may come up. Providers like Rhymetec offer internal audits and gap assessment services that are conducted before your audit, leading to fewer surprises during your official audit.
Common Findings in Cybersecurity Audits (And How To Address Them)
Cybersecurity audits often reveal a few common recurring issues that many startups and SMBs face:
One of the most common findings across a variety of different types of audits is weak access controls. Cybersecurity audits frequently find gaps in access control requirements, meaning that too many people have unnecessary access to sensitive data or systems.
The fix here is straightforward:
- Review who has access to what.
- Limit permissions to those who need it.
- Implement multi-factor authentication to add a last additional layer of security to make it harder for unauthorized users to gain access.
Another issue that often comes up is missing or outdated documentation. Auditors will expect to see things like security policies, incident response plans, and training records. If you can't provide these documents or if they're outdated, that's a red flag.
To address this issue, you should:
- Create clear, up-to-date policies that reflect what's actually happening at your organization.
- Make documentation a regular part of your operations, so you're not scrambling to pull everything together before an audit.
- Consider using compliance automation software to organize all of your documentation for auditors in one place.
Another common area where audits also tend to find vulnerabilities is in systems that haven't been patched or updated.
Leaving old software as is is like leaving your door unlocked. You should be regularly updating and patching systems to close off potential entry points for attackers. Simply setting up automated reminders or systems to handle updates can be extremely helpful.
Third-party risk management is another area that is often overlooked by organizations and comes up in audit findings. For PCI DSS audits, for example, this is one of the most common challenges our experts at Rhymetec see that organizations encounter. For many frameworks, you need to make sure your third-party vendors are also compliant.

Finally, many audits reveal a lack of proper employee training. As noted by our experts in Rhymetec's Cybersecurity Awareness Month Tips, your people are often the first line of defense. If they're not aware of basic security practices or don't follow steps to adhere to them on a daily basis, it's a problem.
Ongoing security awareness training and phishing training for employees help everyone in your company recognize and avoid common vectors of attack like phishing attempts.
If possible, address these common issues ahead of time for a smoother audit process.
Cybersecurity Audits and Penetration Testing
Penetration testing is the best way to understand how well your defenses would stand up to real-world attacks.
While not every audit requires a pen test, it's often necessary for audits tied to specific compliance frameworks like PCI DSS and certain SOC 2 reports. These audits don't just ask if you've set up your security controls - they want tangible proof that your system can actually withstand an attack.
Penetration testing is recommended when you need more than a surface-level review of your security and need to go beyond checking boxes to meet compliance requirements; experts simulate actual cyberattacks to try to break through your defenses. Think of it as having someone attempt to lockpick your door, rather than just checking if your door is locked.
Note: If your organization is preparing for a major compliance audit, working with clients that demand high levels of security, or going through rapid growth, a penetration test is highly recommended!
If you incorporate penetration into your regular security checks, you'll get a clear picture of how well you're protected and will be able to tackle weaknesses before they become costly problems down the line. Getting a test done annually or after major changes to your systems helps you stay ahead of emerging threats.
Rhymetec offers a variety of penetration testing services, including:
- Mobile application penetration testing
- API penetration tests
- Web application penetration testing
- External network penetration tests
Choosing The Right Partner for Your Audit
Not all auditors are created equal, so it's important to select a partner who's not only experienced but also a good fit for your company's size, structure, and industry. You need someone who understands both your industry and the specific compliance requirements you're facing.
Audit Partner Factors To Consider
First, check out their track record. Have they worked with startups or SMBs before? It's one thing to know the rules, but another to understand the unique challenges small to midsized companies and startups face regarding security and compliance.
Ask about their previous clients and whether they've helped similar businesses successfully meet their compliance goals. Request to see case studies from their prior engagements with companies with similar profiles as yours.
Another factor to consider is how hands-on you want your audit partner to be. Some partners take a more hands-on approach by choosing to work with select MSSPs to help you improve your security along the way, while others are more focused on just performing the audit and reporting findings.

Audit Report "Red Flags" To Look Out For
A thorough audit report gives you a roadmap for improving your security with clear steps, while a deficient one can leave you with more questions than answers.
Plus, 69% of organizations report that the quality of compliance reports is extremely important. Your clients and stakeholders will want to see evidence of a thorough, high-quality audit.
So, how do you tell the difference between a thorough audit report and a deficient one?
1. First, look at how the findings are communicated:
A high-quality audit report won't just tell you that there's an issue - it will explain where the problem is, why it matters, and how it could impact your business. Look for specifics, like which systems or processes failed, how attackers could exploit weaknesses, and what steps to take next. If your report is filled with vague statements or broad recommendations without context specific to your organization, that's a sign it's not as thorough as it should be.
2. A high-quality report will also show you how issues across different areas are connected:
If weak access controls, for example, show up in multiple places - whether in your cloud setup, employee accounts, or vendor portals - a good report will explain how these issues are linked. A deficient report might mention them individually without showing the bigger picture.
3. Findings on your documentation is another area where a thorough report stands out from a deficient one:
A high-quality report points out exactly where your policies or training records are lacking and provides actionable steps to fix them. If your report glosses over missing documentation or doesn't dig into whether your policies match actual practices, you're likely looking at a surface-level, boilerplate review rather than a meaningful and tailored audit.
4. Finally, a quality report doesn't simply list issues but will categorize them based on their severity and urgency:
This helps guide you on which areas to focus on first. A deficient report may give you a laundry list of issues but won't help you understand which ones pose the most immediate threat.
In short, a thorough audit report provides clarity, context, and a plan. A deficient one leaves you guessing and unsure of how to proceed and may not hold up under scrutiny from your customers and stakeholders.
How Working With An MSSP Simplifies Cybersecurity Audits
Partnering with a Managed Security Services Provider (MSSP) can take a lot of stress out of cybersecurity audits. An MSSP handles much of the ongoing work for you, so when it's time for your audit, you're not rushing to get everything in order.
With continuous monitoring, regular updates, and fully managed compliance services, an MSSP ensures that your security posture stays audit-ready all year round. For example, if your business needs to meet standards like PCI DSS or ISO 27001, an MSSP can keep your policies and security controls aligned with the latest requirements and make sure you're up-to-date on your recurring audits.
Working with an experienced MSSP is the best way to minimize the risk of non-compliance and saves your internal team from having to devote time to it themselves. When you work with an MSSP, you're essentially outsourcing the complex, technical aspects of security to a team that specializes in it, freeing up your business to focus on growth while staying secure and compliant.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.

Meet Nicole!
Hi, I’m Nicole! I was born and raised in Connecticut, with no plans to leave! I graduated from Central Connecticut State University with a BS in Marketing and took pride in being active in my university’s community. I founded our Women’s Club Soccer team and was part of the School of Business Student Advisory Council & Marketing Club.
After graduation, I found myself working in events and have since transitioned into the world of cybersecurity! In my spare time, I love cooking and trying new recipes, and I enjoy spending time with my family, friends, and all the four-legged loved ones in my life.
Tell us a surprising fact about yourself…
I helped my mom try out for Shark Tank! They had an open casting call in Washington, D.C., so we drove down there from CT. We had to create a video as part of the submissions, so I filmed and edited her video. Once we got to the open casting auditions, my role was mostly moral support and showcasing her products; she did all the pitching! Unfortunately, we did not meet any sharks, just staff who were part of vetting pitches.
If you could have any superpower, what would it be?
Without a doubt teleportation. I never did a ton of leisure travel in my lifetime, so would love to be able to go places across the world in seconds! Plus, who wants to sit in cars, planes, or traffic for hours on end? If I could teleport, I could be anywhere at any time!
What are some things you enjoy doing outside of work?
I love being home and taking time to relax. On a typical night in, you can find me (and my soon-to-be husband) cooking, with some of our favorite music running in the background, and a glass of wine in hand. Once all is said and done, we like hanging out on the couch and catching up on our latest shows with our dog and two cats. Other than that, we stay active by going for walks or to the gym!
Tell us about your role at Rhymetec…
I started at Rhymetec in March 2022 as the Marketing Manager. I was tasked with establishing a Marketing program as Rhymetec was starting to grow rapidly! I launched new branding and a new website as the foundation of our marketing efforts and aided our sales and customer success teams.
Today, my current role is the GTM (Go-To-Market) Director, where my primary goal is to establish strategic initiatives that will support Marketing, Sales, and Customer Success—continuing to increase revenue and market presence.

Why did you pursue a career in the cybersecurity industry?
A career in cybersecurity somewhat found me. I was working in events for almost 5 years, when a previous colleague reached out to me about the opportunity to work at Rhymetec. At the time I was hesitant as this was a completely new field for me, but with a brother-in-law who has worked in cybersecurity for some time, along with other individuals influencing me to take the risk, I decided to move forward! It’s been one of the most challenging and rewarding experiences to be a part of, and it makes me excited for the road ahead!
What is your favorite part about working at Rhymetec, or in the cybersecurity industry?
My favorite part about working at Rhymetec is the limitless potential we have as a team. We’re constantly finding new ways to enhance our services and better support our clients. It’s truly refreshing to be part of a company that prioritizes continuous improvement and innovation, rather than sticking to the status quo or relying on the mentality of 'we’ve always done it this way.' As a result, it’s incredibly humbling and rewarding to look back and see how much we’ve accomplished together.
What is your favorite quote or the best advice you have ever received?
My parents raised me to have a mentality of “if you don’t ask you don’t get.” This has always taught me to be my own advocate and to push for the things that I believe in. Because of this mentality, I heard this quote, and it stuck with me.
“You don’t get what you deserve in this life, you get what you fight for.”
The quote highlights the idea that success and achievement are not guaranteed by simply deserving them. Instead, it suggests that life often rewards those who actively pursue their goals, confront challenges, and persistently work for what they want.
It implies that effort, resilience, and the willingness to struggle are what ultimately lead to outcomes, rather than entitlement or expectation. This mindset encourages taking responsibility for one's own success by striving and fighting for it, rather than waiting passively for things to happen.
From a security or compliance perspective, what advice would you give to a potential client or SaaS business?
Security should always be proactive, not reactive. There are a lot of things organizations can do at a foundational level to protect their data and their business as a whole. Simply conducting regular risk assessments, hosting ongoing employee security training, and implementing MFA are proactive measures that can have big impacts!

Connect with Nicole Shorette
Compliance Gap Assessments, ISO 42001 Guide and a New Strategic Hire, Highlight Rhymetec's Growth and Commitment to Excellence
NEW YORK, Oct. 1, 2024 - PRNewswire -
Rhymetec, the industry leader in cloud security that provides innovative cybersecurity, compliance, and data privacy services to modern-day SaaS businesses, today announces notable company updates. The company spent the quarter expanding service offerings, including compliance gap assessments, to support a new market of clients, continuing to build a market presence at conferences globally, and creating new resources including a comprehensive ISO 42001 guide. Additionally, Rhymetec made a vital hire to evolve and lead their penetration testing efforts.
"Q3 has been a remarkable period of growth for us," said Justin Rende, CEO and founder of Rhymetec. "From making our compliance gap assessments accessible to clients outside of our vCISO services to introducing our ISO 42001 guide, we've hit key milestones that enhance both our service offering and industry presence. Bringing on additional penetration testing leadership also underscores our dedication to strengthening our security expertise as we continue to scale."
Rhymetec's new offering of compliance gap assessments as an individual service, was historically offered as a perk of Rhymetec's managed vCISO services. Gap assessments help businesses identify areas where they may fall short of compliance requirements and also help them determine how well their organization aligns with key security and privacy frameworks like NIST, SOC 2, GDPR, HIPAA, FedRAMP, and ISO 27001. The assessments' real value is in what comes next–a clear roadmap to compliance that prioritizes resources and offers actionable steps to close any gaps. By offering this new service a wider array of SaaS businesses can take full advantage of a 3rd party assessment on their infosec program in preparation for external audits and certifications.
In addition to adding compliance gap assessments, Rhymetec:
- Participated in SaaStr in September and will have a presence at the Web Summit in Lisbon, Portugal in November.
- Further strengthening its already robust security team by hiring a highly-successful penetration tester with 21 licenses and certifications, including his CJIS - Level 4 from the Federal Bureau of Investigation (FBI), numerous credentials and certifications from CompTIA
- Created a thorough guide to help organizations prepare for their ISO 42001 audit. Broken into four critical phases, including Foundation, Execution, Audit Preparation, and Certification, the handbook was written to help busy SaaS and tech leaders shorten their timelines, reduce their team's level of effort, and successfully guide their company through ISO 42001 compliance.
"ISO 42001 is essential for organizations looking to build trustworthy AI systems, but navigating compliance requirements can be challenging," said Metin Kortak, CISO at Rhymetec. "At Rhymetec, we've developed a comprehensive ISO 42001 guide to streamline this process, offering a clear checklist to break down readiness steps, a timeline cheat sheet to assess certification duration, and a detailed FAQs section that addresses the most common concerns. With these tools, we aim to empower businesses to implement ISO 42001, enhancing their AI governance while aligning compliance efforts with broader business goals."
To learn more about Rhymetec and its suite of cybersecurity services, please visit www.rhymetec.com.
About Rhymetec
Rhymetec is an industry leader in cloud security, providing innovative cybersecurity and data privacy services to the modern-day SaaS business. The company builds, deploys and manages compliant information security and data privacy programs directly within their customers' unique environments, allowing them to focus on their core competencies within their business. Over the years, Rhymetec's services have grown to include a vCISO (Virtual CISO) program, ISO Internal Audits, and a variety of Penetration Testing services. For more information, please visit www.rhymetec.com and follow us on Twitter or LinkedIn.
To Learn More About Rhymetec's Services
October isn't just a month of scary movies, sweater weather, and all things pumpkin spice - this month is dedicated to cybersecurity awareness and is a time for the public and private sectors to raise awareness about the importance of cybersecurity.
For the general public and organizations that do not specialize in cybersecurity, this month is a great opportunity to learn their role in protecting their digital assets, avoiding cyber threats, and staying safe online.
Here at Rhymetec, our cybersecurity experts are keenly aware of the risks clients face across many industries. Our experts act both in an advisory capacity and build and manage infosec programs for over 700 organizations.
This October, in honor of Cybersecurity Awareness Month, we've asked them for one piece of advice they would give to a potential client or SaaS business. Here's what they said:
Cybersecurity Awareness Month Tips From Our Experts
The following Cybersecurity Awareness Month tips are directly from Rhymetec's experts, based on their experience working with a variety of clients across different industries:

"The best advice I would give to a potential client is to start with your employees! Humans are the biggest security risk. When planning to become compliant in any framework or just wanting to mature your security posture, start with personnel. You are only as strong as your weakest team member. Recurring security awareness training should be mandatory for all employees. Educating and reminding employees of malicious tactics used by cyber attackers will decrease the likelihood of your organization being victim to a security incident. Awareness is key."
- Memori Hill

“You don’t have to go it alone! Security and Compliance are deep and ever-evolving wells of information. It can be difficult to dedicate effort and resources to building out an effective information security management system while also focusing on the day-to-day activities required to support and expand your business. We have an excellent team of Security experts eager and ready to help out.”
– Dakota Wright

“There are never too many controls in place to prevent a potential breach or a future incident. Depending on your geographical location as well as the type of data you handle, there are different types of compliances that may be required. Here at Rhymetec we offer a wide array of frameworks that we not only implement for you but manage as well, ranging from SOC 2 to FedRAMP. It’s not about if it will happen, but when it will happen.”
– Endri Domi

“Consistency is important. Staying on top of digital tools can help in staying efficient and avoid missing links and flaws. Use tools and software to help simplify compliance.”
– Leena Niazi

“Security for your cloud product should be between 7-15% of your overall monthly cloud budget to ensure you’re adequately protecting your assets. You wouldn’t buy an expensive car and then leave it unlocked with the keys inside in your driveway.”
– Aaron Butler

“Becoming compliant is more than just checking a few boxes on an excel sheet or pressing a button. True compliance requires security hardening measures that are customized to your business and tailored to your environment and customer base. A dedicated compliance team is the most successful way to pursue achieving a compliant status, as well as protecting yourself from internal and external threats.”
– Christian Mouer

“Never underestimate the bad guys.”
– Allan Cavazos

“Cyber security is not a DIY job. There are several domains within cyber security, and you need to have the skills and knowledge to understand these different domains. My one advice would be to hire professionals who understand governance/compliance and technical aspects of cyber security.”
– Metin Kortak

“Compliance may seem like an impossible feat, however, know it is possible, and Rhymetec can help you get there.”
– Pamela Tobón
“Although becoming compliant will improve the overall security posture of your business, no organization is truly infallible. Developing repeatable processes and a workplace culture that prioritizes security education and training will help reduce risk and allow your organization to adapt to the ever-changing threat landscape that SaaS solutions face today.”
– Sam Brokaw

Cybersecurity Awareness Month Tips: Common Themes
A common theme that emerged from our experts' Cybersecurity Awareness Month tips was the importance of proactive security measures. The bottom line is that you can never be too prepared.
It's always better to have as many defensive measures in place as possible and avoid a security incident in the first place. Measures like security awareness training for employees to mitigate the human risk factor, putting your security hygiene to the test through regular penetration tests, and allocating sufficient resources to continuously improve your cybersecurity posture are crucial.
Another frequent answer we saw was that cybersecurity is not a DIY job! Hiring an external security team can substantially help organizations, especially in the early stages so that your security program can scale with your business growth. Virtual CISOs at organizations like Rhymetec have extensive experience balancing budgetary needs, usability, and security for start-up cybersecurity programs.
It's not an easy balance, but leveraging an experienced partner can deliver huge amounts of specialized talent without the need to spend millions of dollars on an in-house security team. Managed Security Services Providers like Rhymetec have dozens of professionals across security disciplines like cloud security, compliance, web application security, penetration testing, and others.
They have experience applying these skills to startups and SaaS businesses in a way that drives real security outcomes as you scale while also considering your budget.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- Cybersecurity For Startups: A Rhymetec Guide
- vCISO Pricing Breakdown: Find The Best Fit For Your Needs
- Cybersecurity for SMBs: 10 Key Measures and Statistics
Secure file transfer protocol (SFTP) is a secure and encrypted method of transferring files over a network. It uses secure shell (SSH) connections to keep sensitive data safe during transfer, making it a top choice for businesses and IT professionals. With the average data breach now costing more than $4.45 million, a 15 percent rise over three years, SFTP's role in protecting data is more important than ever.
SFTP Explained
Secure file transfer protocol (SFTP) is an encrypted method of transferring files over a network. It uses SSH connection to encrypt both the commands and the data being transferred, making it a safer option than traditional file transfer methods.
By understanding how to establish and maintain SFTP connections, you can ensure your data is transferred securely and efficiently, safeguarding against potential security threats.
What Is Secure File Transfer Protocol (SFTP)?
Unlike traditional file transfer methods, which can expose your data to potential risks, SFTP uses SSH connections to offer a higher level of security. This function encrypts both the commands and the data being transferred, ensuring that sensitive information remains protected from being intercepted during transit.
In addition to security, SFTP offers reliability and performance efficiency, making it a preferred choice for organizations that require a secure and efficient way to transfer files across networks.
How to Establish an SFTP Session
Establishing an SFTP session requires an SSH client, which is typically pre-installed on most operating systems, including Windows, macOS and Linux. This availability makes it convenient for users across different platforms to initiate secure file transfers without the need for additional software installations.
There are two primary methods of establishing an SFTP connection:
SFTP clients: Tools like Cyberduck, Filezilla and Transmit 5 provide user-friendly interfaces that simplify the process of secure file transfers. These clients require users to input authentication information and relevant file transfer data, streamlining the process for end-users.
Command line: For more advanced users, the command line interface offers a powerful and flexible way to establish SFTP connections. This method is favored by software engineers and system administrators who prefer not to rely on third-party clients. While it may seem more complex, it provides greater control and is considered safer by some users.
Here’s how you can initiate secure file transfers via a command line interface. If you choose to use a third-party SFTP client, you can view their instructions by going to the client's website.
Steps to Initiate Secure File Transfer With SFTP
To initiate a secure file transfer using SFTP through the command line, first set up your connection.
1. Connecting to a Remote Server
Open your terminal or command prompt.
Connect to the remote server or device, which is similar to connecting a remote machine via SSH. Instead of entering SSH username@host_name, enter SFTP username@host_name.
2. Transferring Files
Upon establishing the connection, you can now start transferring files. The following commands will enable you to copy and transfer files to and from both machines.
To download a file from the remote server to your local machine, enter: 'get remote_path local_path'
To upload a file from your local machine to the remote server, use: 'put local_path remote_path'
3. Set Your Security Settings
Always ensure you connect to a remote server via a VPN connection and enable only the necessary network ports. Since SFTP uses port TCP 22, you must ensure this port is open on both machines.
Port 22 should never be open to the public for security purposes. If you must open Port 22, you must do so within a virtual private network (VPN), ensuring that only your own device and the remote machine you're connecting to have access to Port 22.
These steps provide a straightforward method for initiating secure file transfers using SFTP, ensuring your data remains protected during transit.
Basic File Maintenance Using SFTP
Regular file maintenance is crucial for keeping your system organized, ensuring data integrity and optimizing performance. Proper file management helps prevent data loss, reduces clutter and makes locating and managing your files easier. Neglecting file maintenance can lead to inefficient storage use, increased security risks and potential data corruption. You can maintain a clean, efficient and secure file system by routinely performing basic file maintenance tasks.
Once you’re connected to an SFTP server, maintaining and managing files becomes straightforward with a set of basic commands:
put: Copy a file from the local machine to the remote machine.
get: Copy a file from the remote machine to the local machine.
ls: List the contents of a directory on the remote machine.
cd: Change the current working directory on the remote machine.
lls: List the contents of a directory on the local machine.
lcd: Change the current working directory on the local machine.
These commands facilitate efficient file management, making it simple to navigate and organize files on both local and remote systems.
Other Useful SFTP Commands to Know
In addition to basic file transfer commands, SFTP provides several other commands that enhance file management capabilities. These commands are essential for performing more advanced tasks, granting users greater control over their file systems. However, improper use of the commands can lead to unintended changes or security vulnerabilities, so it’s crucial to understand their functions and use them cautiously.
Beyond the basic file transfer and maintenance commands, SFTP offers additional functionalities to enhance your file management capabilities:
chmod: Change file permissions on the remote host.
chown: Change file ownership on the remote host.
mkdir: Create a directory on the remote host.
rm: Delete a file on the remote host.
rmdir: Remove a directory on the remote host.
rename: Rename a file on the remote host.
lpwd: Show the present working directory on the local computer.
pwd: Show the present working directory on the remote host.
These commands offer comprehensive control over file operations, ensuring that you can manage your files securely and efficiently.
Frequently Asked Questions
What is the difference between FTP, FTPS and SFTP?
Understanding the differences between various file transfer protocols is crucial for choosing the right tool for secure file transfers. Here's a brief comparison:
FTP: Traditional file transfer protocol that transmits data without encryption, making it vulnerable to interception.
FTPS: An extension of FTP that adds SSL/TLS encryption for secure transmissions. While more secure than FTP, it doesn't offer the comprehensive security of SFTP.
SFTP: Integrates SSH to encrypt both the commands and data, providing the highest level of security among these protocols.
Is SFTP still relevant today?
SFTP remains highly relevant in today's digital landscape. It is a reliable and cost-effective method for transferring files securely between servers. System administrators and software engineers commonly use SFTP due to its robust security features and ease of integration into existing systems.
Despite the emergence of newer file transfer technologies, SFTP's encryption and secure transmission capabilities make it a preferred choice for maintaining server databases and internal file transfers. Its continued use in various organizations underscores its importance and reliability in ensuring data security.
You can read the original article posted in Built In by Rhymetec CISO, Metin Kortak.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- vCISO Pricing Breakdown: Find The Best Fit For Your Needs
- Cybersecurity for SMBs: 10 Key Measures and Statistics
- A Log Analysis Tutorial
Preparing for your PCI audit isn't a matter of simply "checking the boxes" to meet compliance requirements. Ongoing compliance with PCI DSS builds trust with customers and stakeholders, protects your customers' data, and helps with long-term reputation management.
With recent updates in PCI DSS 4.0, there's been an increased focus on compliance maintenance. This article will help you understand the core principles of PCI DSS, how to apply them to your organization, and how to stay compliant over time.
What Is A PCI Audit and How Does It Work At A High Level?
A PCI audit is an assessment of an organization's compliance with the Payment Card Industry Data Security Standard (PCI DSS), a set of security requirements that protect cardholder data. The auditor reviews your organization's security measures, policies, and technical infrastructure to verify that you meet requirements.
In our recent webinar on Compliance to Confidence: Simplifying PCI Security Standards, Rhymetec CISO Metin Kortak discussed frequently asked questions and concerns around PCI DSS Version 4.0 with Kevin Whalen, Head of PCI at Prescient Security.
"The Version 4 standard has a number of new requirements, but I don't think any of the changes are overly difficult. There are a few that are, but a lot of what the update did was simplify and consolidate some of the requirement language. But there are some new enhancements to it to be aware of," noted Kevin Whalen during our webinar.
One such enhancement is the new focus on ensuring organizations maintain compliance over time. As we have seen with other recent updates to cybersecurity and compliance frameworks like NIST CSF Version 2.0, there is a stronger focus in the updated PCI DSS 4.0 on continuous compliance. This means businesses need to show they maintain compliance on an ongoing basis rather than just at the time of the audit.
The PCI compliance readiness process starts with a gap analysis to identify areas that need remediation. Once gaps are addressed, the formal audit is conducted by a Qualified Security Assessor (QSA). This individual reviews documentation, interviews staff, and tests controls to validate compliance. Following your audit, they will provide a report on the findings and note any corrective actions you need to take.
Core Principles and Requirements Under PCI DSS
There are five core principles under PCI DSS. Each of the following requirements is important from a compliance perspective and will also vastly improve your security if you did not have them in place previously.
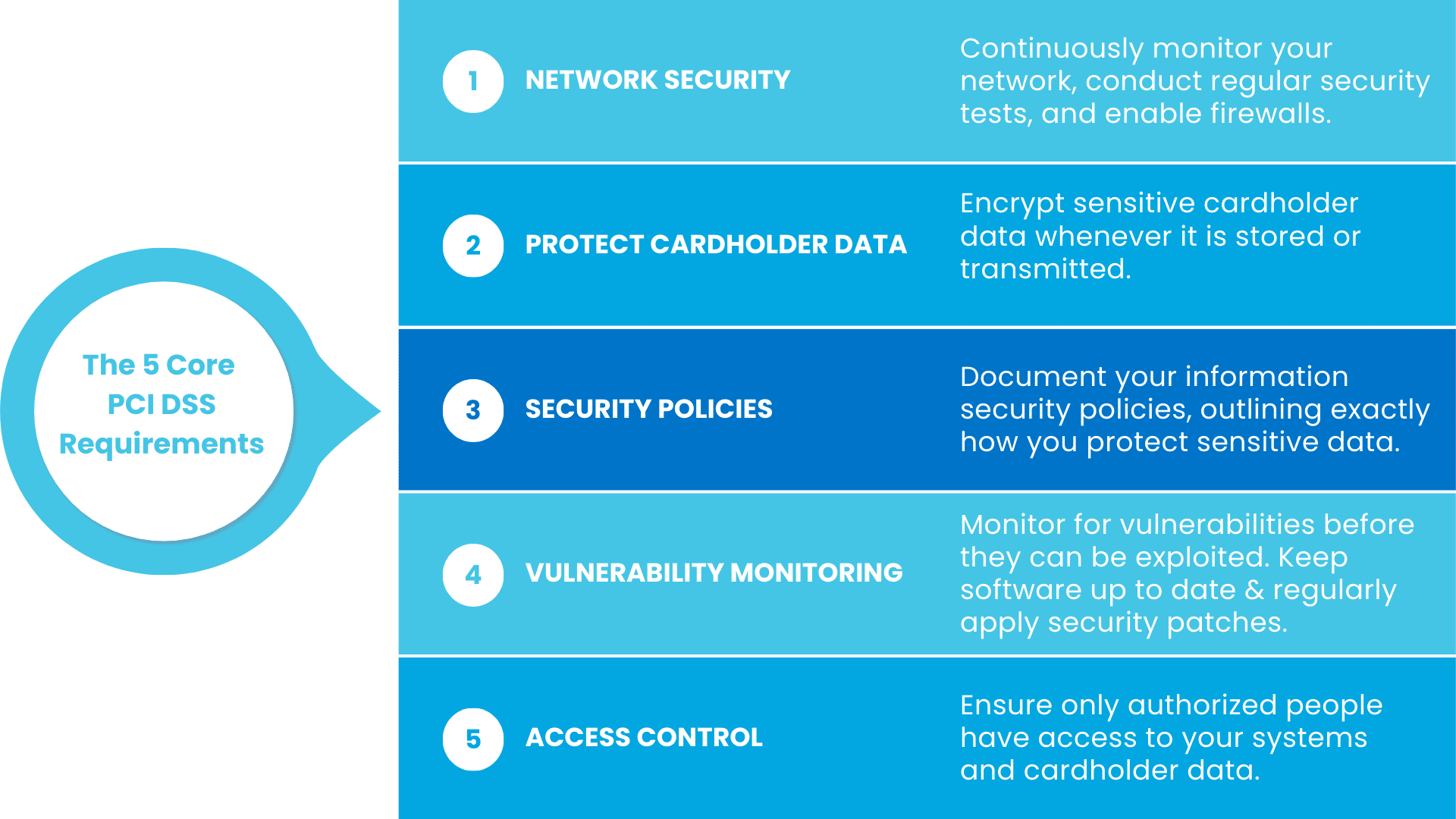
Let's go over each principle in more detail, and explain how they help prevent breaches and keep your customers' data safe:
1. Securing and Monitoring Your Network
PCI DSS requires that you set your network up with security top-of-mind.
This includes measures like firewalls to block unauthorized traffic and making sure your systems are configured securely. You also should set up ways to constantly monitor your network for suspicious activity and conduct regular security tests.
Let's say you run a SaaS platform offering payment processing for small retailers:
If your network isn't secured properly, it's easier for hackers to intercept cardholder data during transactions. By setting up proper firewall measures, you can block unwanted traffic and limit access to only those who really need it.
Regular network monitoring, meanwhile, will alert you to unusual activity, such as an unexpected increase in traffic to your payment systems. Lastly, ASV scans for PCI, vulnerability scans, and penetration tests can help identify weak points and enable you to fix them before they can be exploited.
2. Protecting Cardholder Data
Under PCI DSS, you must encrypt sensitive cardholder data whenever it's stored or transmitted. Encryption makes the data unreadable to anyone without the decryption key, so even if it's intercepted, it's useless to bad actors.
As an example, if a platform offers subscription services and stores credit card information for recurring payments, under PCI DSS they must have encryption enabled to prevent hackers from being able to steal readable credit card data. This is a particularly important measure if your business deals with large volumes of recurring transactions where cardholder data may be stored for longer periods of time.
3. Updating Security Policies For Your PCI Audit
Under PCI DSS, organizations must have a set of documented information security policies. Your policies should outline precisely how you protect sensitive data, and how different members of your teams play a role in this.
For example, your policies may require that all developers at your company use secure coding practices, or that support staff avoid accessing customer payment data directly.
*Note: Having strong security policies in place is critical regardless of organization size, but small businesses or those without designated security members on staff often struggle to set up clear and usable policies. Check out our blog on crafting security policies for small businesses for guidance on how to not only write, but how to effectively communicate your security policies so they are followed by employees.

4. Vulnerability Monitoring
Vulnerability monitoring entails common sense security measures like keeping antivirus software up to date and regularly applying security patches to your systems. The idea is to address security vulnerabilities before they can be exploited.
If a known vulnerability exists in one of the software components your project management tool relies on to work, for example, threat actors could use that to access your customers' data. Continuously monitoring for potential vulnerabilities and having a plan to address them is critical not only for your PCI audit but also from a baseline security perspective.
5. Access Control
Access control measures need to be implemented to ensure only the right people can get into your systems and access sensitive cardholder data. Baseline security measures that all organizations should ideally be doing, like multi-factor authentication (MFA), also help with access control.
You never want everyone internally to have full access to cardholder data. By limiting access to only the employees who absolutely need it - and by also adding MFA to verify their identity - you reduce the risk of unauthorized access enormously.
Why Is PCI DSS Compliance Important For Your Business?
Businesses that handle cardholder data are required to obtain PCI DSS compliance. Non-compliance can result in fines, legal penalties, and damage to your organization's reputation. Breaches can lead to financial losses, erode customer trust, and cause disruptions to your business operations.
Compliance also reduces the risk of fraud and theft of payment data, which can result in financial harm to both your business and your customers. With the introduction of PCI DSS 4.0, businesses are expected to demonstrate continuous compliance and show that they are taking a proactive approach to managing security risks.
Types of PCI DSS Audits and Their Scope
The type of PCI audit your business requires depends on your merchant level and the volume of transactions you process annually. Each audit type covers all of the requirements in the PCI DSS standard, but may vary in depth based on the size of your business and the sensitivity of the cardholder data you process:
Self-Assessment Questionnaire (SAQ)
This is a self-evaluation tool used by smaller businesses that don't handle large volumes of cardholder data. The SAQ is basically a checklist where you answer a series of questions about your security practices, and is broken down into different versions depending on how you process payments. There are specific versions for businesses that process payments online, through a physical point-of-sale system, or over the phone.
As an example, if you run a SaaS business that provides a billing platform for freelancers, and you rely on a third-party payment processor like Stripe to handle the actual transactions, you wouldn't be storing or processing cardholder data directly. Therefore, you'd likely fall under the SAQ version that applies to businesses that outsource their payment processing, and it would serve to validate that your company never stores or has access to that data.
Report on Compliance (RoC)
For larger organizations or those processing a large volume of transactions, a PCI audit conducted by a Qualified Security Assessor (QSA) is required.
This audit is more extensive and includes on-site assessments of your security controls, and is generally required for larger businesses or those processing a significant number of transactions. If your company processes more than 6 million transactions per year, you'll likely need an RoC.
5 Steps To Prepare For Your PCI Audit
At a high level, the following 5 steps illustrate the process leading up to your PCI DSS audit.
At any one of these steps, it can be helpful to consult an outside expert, such as a Managed Security Services Provider (MSSP), with ample prior experience helping organizations achieve PCI DSS compliance.
1. Understand your scope.
Mapping out the scope of your audit is the first step. You'll need to determine which of your systems, networks, and processes handle cardholder data. Merchants have to request additional information from customers under certain circumstances:
"When we start our scoping process, what we usually try to understand in the beginning is how the payments are being processed…Where it gets complex is when the physical card is not present when you're making a purchase. Because the physical card is not present, PCI has certain requirements in place so that when you make a purchase online, for example, you have to provide some additional information like your billing address," said Rhymetec CISO Metin Kortak on this topic during our webinar.
You also need to define your Cardholder Data Environment (CDE).
"What that means is we need to understand exactly where the card information is being processed. Is it only processed by the customer's hosting provider? Or does the card information also reside in other third-party applications or physical servers? It's important to understand the entire scope so that when we go through an audit, we can give them the proper scope and make sure that the PCI security controls are implemented on all of those hosting providers and other vendors," said Metin.
2. Conduct a gap analysis leading up to your official PCI audit.
Perform an internal assessment to pinpoint areas where your organization does not meet PCI DSS audit requirements. This is important to do before your formal audit, as it will give you a chance to address any deficiencies beforehand. MSSPs that are experienced in compliance and offer one-off gap assessment services can be a great resource during this step.
3. Remediate any identified gaps.
Next, address any gaps found during your internal assessment. Common security measures that may need to be addressed at this stage include updating your firewalls, strengthening encryption protocols, or further formalizing your access controls.
4. Update your documentation.
Prior to your audit, make sure all of your policies and security measures are well-documented in a format that will make it easy for your auditor to keep track of. Using a compliance automation tool can be extremely helpful with this, as they provide a single, easily accessible place to upload all of your documentation for your auditors to see.
5. Perform ongoing monitoring for your next PCI audit.
This element is one of the heaviest lifts of the current version of PCI DSS.
Compliance maintenance under PCI DSS 4.0 is expected, and ongoing monitoring will help you stay compliant throughout the year. You should be regularly monitoring security systems and processes to detect any potential misconfigurations or vulnerabilities. This includes automated monitoring of various controls, such as payment page script security:
"The most significant change of 4.0 is the payment page script security, where they've added some new requirements in the software development controls as well as automated security controls around monitoring for changes to the construction of your pages that contain input fields for cardholder data." - Kevin Whalen, Prescient Security
Common Challenges and What To Do
Some common challenges businesses face when preparing for PCI DSS audits include:
Defining the Scope of Your PCI Audit
Many businesses struggle with understanding the full scope of systems that must be in compliance with requirements under PCI DSS. To address this, perform an inventory of systems handling cardholder data. As an example, you will have more strict requirements that apply to your scope if you take payments over the phone instead of in person.
"Depending on how the payments are being processed, how the credit card information is being collected by the buyers - that impacts the level of work that we're going to do for our customer," Metin Kortak, Rhymetec
Maintaining Compliance Over Time After Your PCI Audit
Maintaining an effective compliance maintenance program that scales with your business can be a challenge. Using automated monitoring and logging tools to track compliance in real-time can be helpful, as can working with an outside expert like a Managed Security Services Provider with specific expertise in enabling organizations to stay compliant over time.
Documentation
Many organizations lack adequate documentation of their security policies and controls.
You need this documentation not only for compliance purposes but also as a common-sense security measure: All of your employees should be aware of your security policies and procedures, such as your policy on measures like multi-factor authentication (MFA).
Bonus Tip: For your PCI DSS audit, a compliance automation platform can be incredilby helpful with documentation. Compliance automation tools provide a single location with all of your documentation clearly laid out, so that you and your auditors can easily access and keep track of it.
Third-Party Risk
Third-party risk management plays an important role in PCI compliance. If you're using a third party to process or store credit card information, you generally need to obtain that company's own attestation or certification document to include in your own PCI audit.
"Collecting your third parties' PCI certifications is important, especially if the vendor is processing or transmitting credit card information. Aside from that, you still need to conduct vendor assessments on all of your vendors. And that needs to go beyond just collecting the PCI certifications. That might mean checking that those vendors have proper information security policies in place, if they have conducted their own business continuity tabletop exercises, if they conduct access reviews…Just really conducting a thorough due diligence." - Metin Kortak, Rhymetec
In sum, you need to make sure your third-party vendors that process or store your cardholder data in any way are also PCI DSS compliant.

Post PCI Audit Action Items: How To Stay Compliant
After your audit, there are several steps to help maintain compliance:
Address audit findings.
The first step post-audit is to thoroughly review the auditor's report and remediate any identified deficiencies as needed.
Be sure you've implemented continuous monitoring measures.
Set up monitoring systems to track your compliance with key PCI DSS controls discussed previously, including encryption, access management, and vulnerability scanning. As noted above, a compliance automation tool can be incredibly helpful with this.
Update your policies as needed.
It can help to schedule regular intervals to review your security policies going forward. This will enable you to change your policies as needed to reflect any changes in your organization's operations, your risk profile, or the PCI DSS standard.
Have regular internal audits.
Schedule periodic reviews to assess your compliance posture between your annual PCI DSS audits.
Vendor management.
Lastly, remaining in compliance with PCI DSS requires ongoing monitoring of your third-party vendors to confirm their continued compliance, especially if they are involved in how you handle cardholder data.
In Conclusion
Although it may seem daunting to prepare for your PCI audit, by following the steps outlined in this article, you can feel confident that you are well prepared for your audit and that your customers' data is protected.
PCI DSS compliance is not just a one-time effort - compliance requires ongoing attention, especially with the updates introduced in PCI DSS 4.0. After your PCI audit, be sure to continue monitoring your network, confirming third-party due diligence, and updating your policies as needed. Staying proactive will help your business stay secure, remain in compliance, and build long-term trust with your customers and stakeholders.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- Generative AI Security Risks For Businesses: Practical Advice For The Concerned
- vCISO Pricing Breakdown: Find The Best Fit For Your Needs
- Cybersecurity for SMBs: 10 Key Measures and Statistics
Metin Kortak, CISO with Rhymetec, talks about how organizations are approaching data privacy and security compliance, and thinking about risk management policies, when it comes to generative AI in the workplace.
Below is a lightly edited transcript from the Decipher podcast conversation.

Decipher Podcast: Metin Kortak
Lindsey O'Donnell Welch: This is Lindsey O'Donnell Welch with Decipher and I'm here today with Metin Kortak, CISO with Rhymetec. Thank you so much for coming on today. It's really nice to speak to you.
Metin Kortak: Thank you very much for having me.
Lindsey O'Donnell Welch: Can you talk about your path into the cybersecurity industry and what drew you to the CISO role?
Metin Kortak: Yeah, absolutely. I have a computer science background, and when I first started working at Rhymetec, we were actually only offering penetration testing as a service to our customers, and then later on, we realized that with our customers, there's this demand for becoming compliant with various cybersecurity frameworks, which at that time wasn't my specialty - I was more of a network security person. But as we realized that this is a very big demand from our customers, we expanded our business more for compliance and providing cyber security solutions services.
Lindsey O'Donnell Welch: I know that you do a lot with compliance and privacy, and I wanted to talk a little bit about what you're seeing there, specifically with AI being such a big topic over the past year with generative AI and the general availability there. How does AI fit into companies' existing compliance and privacy frameworks, from your perspective?
Metin Kortak: Yeah I always say that because technology evolves so fast, laws, regulations, any sort of compliance frameworks, they always come after the technology has been created and actually built in a proper manner. We have been actually working with AI systems for the past couple of years but not until recently there has been some more compliance frameworks and regulations that became more solid. Recently we've been working with ISO 42001, which has been a recent cybersecurity framework that was really created to secure artificial intelligence systems.
But this framework hasn't even been in place up until just a couple of months ago, and even with the auditors that we're working with they're not even yet accredited to conduct audits against these frameworks. So it's all just very new and there are a lot of concerns from our customers because they want to make sure that they're doing the right thing, they want to make sure that they're complying with certain regulations. But at the same time, the regulations are not really available to them. So they don't have a lot of guidance from the government or from other cybersecurity framework providers. So it has definitely been difficult, and what we have been doing is following these guidelines, and sometimes we have to create our own guidelines for ensuring data privacy on data security.
Lindsey O'Donnell Welch: Outside of the Biden administration's executive order around AI and security, there haven't been really any official types of things that people or companies can point to and say, here's what we need to do about AI and privacy and security. I know in the EU they recently passed the AI Act that outlined some of the governance policies that companies need to follow. Is that something that is top of mind for companies?
Metin Kortak: Yeah, absolutely, we've been following the key frameworks, we have also been following the NIST AI frameworks that have been released but are not really being used by a lot of companies right now. But on top of that, as you know, GDPR, has been around for a long time.
And on top of that, in California, there has been CCPA for data privacy acts, and even if there wasn't an official artificial intelligence cybersecurity framework, what we have been doing to kind of like get around that is ensuring that our customers are still complying with frameworks like GDPR, CCPA, while they are producing artificial intelligence systems because even though there aren't specific AI guidelines, there are guidelines around data privacy and data security and we can interpret those guidelines and ensure that AI systems are still complying with those frameworks.
"It has definitely been difficult and what we have been doing is following these guidelines and sometimes we have to create our own guidelines for ensuring data privacy and data security."
Lindsey O'Donnell Welch: Yeah, so it seems like the main approach here is to look at the the existing frameworks and see if those policies can encompass what we're seeing with AI and lean on those existing ones?
Metin Kortak: Correct. For example, when we're working with artificial intelligence systems, there are language learning models - LLMs- language learning models capture personal information and other data, and based on that data, they will yield results. And they continue to learn from that data. And when we're talking about a data privacy framework like GDPR, end users do have the option for their data to be removed. So what we do is implement procedures in place so that their personal data can not only be removed from databases but also from language learning models, so that data cannot be used for teaching the artificial intelligence learning behavior.
Lindsey O'Donnell Welch: Do you see companies thinking about data governance at all, is that top of mind or people as it relates to AI, or are people mostly just diving in headfirst and saying, “Here's this really cool AI application that we can deploy," and then not really [thinking about] dealing with the consequences after?
Metin Kortak: Yeah I've been seeing a lot of companies just like jumping on the bandwagon. Whenever AI is out there, they're like, "We have to do something AI, we have to do something AI," and they're working with all of these third-party providers, they're trying to build their own artificial intelligence systems. But they're trying to do it in a fast way because it's no longer about data security governance and privacy, and it's more about competing in the marketplace.
Everybody wants to make sure that they have some type of AI product because now it makes them better than the competitor that doesn't. So I have been seeing very little attention to cybersecurity and data privacy when implementing these artificial intelligence systems because companies mostly care about how they can be better when it comes to their competitors. And because there weren't a lot of regulation/compliance frameworks, it was almost like a free for all - you can do whatever you want, you can create your AI system, you can opt your users in, you can capture their data without really having some solid consequences from a legal standpoint.
I think that's why a lot of those recent laws in the European Union and other countries have been making a bigger difference because companies actually now care more about data governance and privacy as it relates to artificial intelligence systems. But before that, what I have seen is that companies just try to utilize these AI systems as much as they can without having a lot of consequences.
Lindsey O'Donnell Welch: Yeah, that seems to be kind of the overall trend. When you're looking at the data governance policies themselves, what I'm seeing for one best practice for companies that are implementing AI systems is to map out all the different data sources that are being used in the AI model training. And there's so much there, right? It's crazy. But a lot of the types of models aren't really publicly available. So what's the best way to navigate something like that?
Metin Kortak: Yeah, a lot of these companies are now using open-source artificial intelligence systems, meaning the AI platforms are learning from publicly available data, publicly available images, text, Google searches. So there's definitely a difference between publicly available data versus privately owned data by end users. If data is publicly available, there aren't any regulations there that prevent companies from using publicly available information. I can go do a Google search, I can use information I see from articles and other links that I see, and utilize that information to teach my AI model to respond in a certain way.
Where it gets more tricky is when behavior is based on personal information, like if a lot of people like the color yellow, and they say that they like the color yellow on their Instagram stories, or they say it on their Facebook posts or whatever, that information can be personal data, and if AI models are making decisions based on private information like that, then that's when it becomes an issue from a data governance and some privacy standpoint, because now the AI model is not just learning from publicly available information. It is actually obtaining that data from individual user accounts and utilizing their personal information to make certain decisions.
"I think that's why a lot of those recent laws in the European Union and other countries have been making a bigger difference because companies actually now care more about data governance and privacy as it relates to artificial intelligence systems."
Lindsey O'Donnell Welch: I'm curious more from the defense side of things, how you're seeing AI transforming actual cyber security practices this year. How does that compare to what you've seen in the past as well?
Metin Kortak: Yeah, so like I said, when I started working at Rhymetec, we were just in penetration testing services, and penetration testing is pretty manual labor. You have to understand what vulnerabilities are in place and then, at times, exploit those vulnerabilities in order to identify any issues with the networks, any issues with servers and other platforms.
With artificial intelligence recently, we have been seeing that AI models have also been used in aiding penetration testing, or they have been actually conducting the penetration test on their own by identifying security vulnerabilities and eventually exploiting them. Now, this is great from a pen tester standpoint because now they have an easier way to conduct these penetration tests and understand these vulnerabilities. However, it can also be dangerous in the hands of the wrong people, because that means now people have a much faster way of identifying and exploiting security vulnerabilities.
So how I see this impacting the future of cybersecurity is that I think in the beginning, it might be definitely dangerous because people will be able to identify these security vulnerabilities a lot faster, but at the same time, I think that if this practice became more common then a lot of organizations can also implement much better security controls in place and the standard for cybersecurity can be a lot higher.
Lindsey O'Donnell Welch: I think you bring up a really interesting point - this has been kind of one of the biggest discussions around AI - which is who's this going to help more - the defenders or the threat actors? And when I was at RSA a couple of weeks ago, it seemed like the consensus was that right now the defenders and the ways that you know we're using this on the defense side seem to be more sophisticated right now than what they're seeing from threat actors which is kind of basic uses for content and phishing lures, things like that.
Metin Kortak: I think that if a sophisticated threat actor is actually attempting to breach a network, they're likely not using artificial intelligence. I think that they're likely using more manual and sophisticated ways to reach networks. But I think that on the defense side, absolutely, I think using artificial intelligence can be very beneficial. I think it can help us identify these vulnerabilities a lot faster, a lot quicker and then remediate them. But I think that if somebody is really looking to breach a network, they probably have a lot better options than relying on artificial intelligence models.
Lindsey O'Donnell Welch: How is AI being used in differing capacities in ways across different industry verticals, whether that's health care or banking, and as a follow-up question to that, given the compliance challenges that each of these industries deal with, how is that a factor in how AI is being used?
Metin Kortak: So in the cybersecurity field, I have been saying that artificial intelligence has been used more in things like intrusion detection platforms to identify anomalies and suspicious activity. We already have intrusion detection systems in place, but they usually identify the anomalies and other suspicious activity and other security-related issues using a certain algorithm.
With AI, because it is using learned behavior, it is able to identify these security incidents a lot better than simply just following an algorithm. So we have seen that with things like intrusion detection systems, and vulnerability monitoring platforms, there is definitely an added benefit to utilizing artificial intelligence systems. In addition to that, we have also been seeing artificial intelligence systems and platforms, for example, answering security questionnaire services or like answering RFPs for customers. With those really tedious processes that take a lot of time manually, I think that using artificial intelligence has actually helped us complete those types of work in a much faster way.
When it comes to other industries like healthcare and banking, artificial intelligence is never 100 percent. It may give you a very solid answer and then it might give you a really bad answer the next time. So when an industry is impacting someone's life, like when you're in the healthcare industry, we don't really see artificial intelligence being used that much because it is still unpredictable, and there are still answers that we can get that may not yield good results. I think that it can still be used to aid doctors and other systems that they're using for healthcare, but I do not see it really being used for systems that might directly impact a person's life.
"I think that if a sophisticated threat actor is actually attempting to breach a network, they're likely not using artificial intelligence."
Lindsey O'Donnell Welch: As a CISO, what do you see in terms of CISO interest in AI use cases and then also how it fits into security programs within companies?
Metin Kortak: Yeah, so recently, I've been seeing a lot of third-party vendors that we work with automatically enabling artificial intelligence learning models without really asking us. Especially if you're using a SaaS product, there is a likely chance that if you go to the settings stage, there is an option to disable artificial intelligence or keep it enabled, and you will see that also the time it has been enabled by default. So we have been really just seeing that option enabled by default, and it has been really making our jobs a lot more difficult because it's essentially a new product that's being enabled without really asking our consent, and that's creating issues with third-party security assessments.
So because of that, we have been actually reviewing some of our customers' products and other critical third-party vendors that they work with and either disabling the AI tools or conducting further assessments to ensure that enabling AI will not really cause any compliance or other governance-related security concerns.
So that has really caused some issues with third-party security assessments. However, we have also been using artificial intelligence for things like answering RFPs, answering security questionnaires, analyzing logs, and analyzing security reports to better gather information in a much faster way. So I do think that it has been very valuable to us. I think that it has made our jobs a lot easier, but at the same time, we have been doing a lot more strict due diligence because of how common AI has become recently in the platforms that we use on a day-to-day basis.
Lindsey O'Donnell Welch: I think that brings up a good point which is, a lot of companies I talked to are saying, "We want AI, but we want to make sure that it solves a business problem that we have. We don't just want it slapped onto a product." As a CISO, when you're looking at different things for AI, what sticks out to you where you say, "This could be something that is applicable and might be useful for an organization," versus, "Okay, that seems like it's more hype."
Metin Kortak: I really see AI as an efficiency improvement. I think that if something is taking a long time manually, it can be likely done faster using artificial intelligence, which is why we started using AI for analyzing security logs and also identifying certain security incidents, because doing manual log reviews or reviewing certain systems manually, it just takes up a lot of time. And I think at the end of it this saves organizations a lot of money and resources because they can actually allocate those resources for solving better problems.
Lindsey O'Donnell Welch: Are there any trends related to AI and cybersecurity that you think are going to be big or something to keep our eyes on over the next year?
Metin Kortak: I would definitely keep your eyes open for any other cybersecurity regulations that are coming up. I think ISO 42001 has been becoming a lot bigger. We have a lot of customers asking us about that framework. We have already started working on that framework with some of our customers.
But on top of that we are expecting some additional cybersecurity frameworks and regulations to be released soon. So I think those should be definitely important to watch out for. Because we're expecting that in the next couple of years, a lot of organizations are going to start requiring these frameworks if you're utilizing an AI system. If you have not implemented these security controls or if you haven't really followed the guidance from some of these cybersecurity frameworks, that means you might have a lot more work to do later down the line.
You can read the original article posted in Decipher Podcast, by Lindsey O'Donnell Welch and Metin Kortak.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog: