With 88% of organizations now using AI in at least one business function, the race to innovate has never been faster. But as these applications scale, they drastically expand the web application attack surface. Without the right security frameworks, deploying generative AI can introduce severe model, prompt, and integration risks that traditional security tools simply weren't built to catch.
This guide breaks down what every organization needs to know about LLM penetration testing, how it differs from standard security assessments, and how to build a resilient AI ecosystem that supports compliance and growth.
What Is LLM Penetration Testing And Why Is It Different?
LLM penetration testing is a specialized security assessment designed to evaluate how generative AI systems behave under adversarial conditions.
Traditional web application penetration testing was designed to uncover vulnerabilities like SQL injection, cross-site scripting (XSS), and server misconfigurations. It focuses heavily on static infrastructure.
LLM penetration testing evaluates the logic, behavior, and integration layers of generative AI systems. Traditional automated scanners like Burp Suite or Nessus were not designed to test the probabilistic nature of AI. Instead of attacking the infrastructure alone, LLM testing uses adversarial tactics to manipulate prompts, bypass guardrails, and attempt sensitive data extraction.
To understand the scope of an LLM penetration test, it helps to break down the core components of the AI ecosystem:
- The Model: The underlying backend intelligence (e.g., Claude, OpenAI, Gemini).
- The Agent: An API-hooked action the AI can perform, such as sending an email, querying a database, or creating a support ticket.
- The Message Prompt: The user-facing text input, which serves as the primary entry point for most attack vectors.
Even if you are utilizing a highly secure, third-party foundational model, your specific implementation layer, like system prompts, plugins, agents, and data handling workflows, creates new points of exposure.
The Regulatory Push for AI Security
Compliance frameworks and international regulations are rapidly catching up to generative AI. Security is no longer just a best practice; it is a legal requirement.
The EU AI Act is already fundamentally shifting how companies approach AI risk. With Article 5 prohibitions in effect and the strict compliance deadline for high-risk models looming on August 2, 2026, companies handling EU resident data must prove their AI systems are safe, unbiased, and secure.
In addition to European regulations, comprehensive LLM penetration testing supports emerging governance frameworks like the NIST AI Risk Management Framework (AI RMF) and ISO/IEC 42001. Delivering structured reporting that demonstrates validated safety testing is now a prerequisite for passing enterprise procurement reviews and maintaining executive confidence.
Top AI Vulnerabilities You Need to Assess
A robust LLM penetration test aligns directly with the OWASP Top 10 for Large Language Model Applications. Because LLMs are probabilistic, meaning the exact same prompt can generate different answers on different days, testing requires highly manual, creative, and persistent adversarial prompt engineering.
A thorough assessment should target these critical vulnerabilities:
- Prompt Injection: The most common attack vector, where an attacker uses clever wording to bypass instructions, override guardrails, or force the system to execute unintended commands.
- Sensitive Information Disclosure: Manipulating the model to reveal restricted content, PII, or sensitive data about other users.
- System Prompt Leakage: Tricking the AI into revealing its own backend instructions, guardrails, or safety features, allowing attackers to map out loopholes.
- Vector Embedding Weakness (RAG Assessments): Exploiting a Retrieval Augmented Generation (RAG) pipeline to force the AI to retrieve unauthorized internal data.
- Unbounded Consumption: Testing system limits to ensure an attacker cannot abuse the AI to trigger massive cloud infrastructure costs or a Denial-of-Service (DoS) state.
How Rhymetec Approaches LLM Penetration Testing
At Rhymetec, our methodology combines adversarial prompt engineering, automated red-teaming, and expert manual logic validation to assess risk across your entire generative AI lifecycle. Each engagement aligns with the OWASP Top 10 for Large Language Model Applications, ensuring your testing reflects the latest standards in generative AI security.
Rather than a one-size-fits-all approach, we scope our testing to match your specific AI architecture:
Evaluating Core Models and Chat Interfaces: For standard public-facing or internal assistants, we focus heavily on foundational vulnerabilities. Using manual, creative prompt injection, we test the system's resilience against sensitive data leakage, system prompt extraction, and unbounded consumption attacks aimed at exhausting your cloud resources.
Assessing RAG Pipelines and Internal Knowledge Bases: If your application retrieves contextual data from an internal database (Retrieval-Augmented Generation), the stakes are significantly higher. We conduct deep-dive assessments to identify vector embedding weaknesses, ensuring your system cannot be manipulated into bypassing guardrails to access or expose compartmentalized proprietary data.
Validating Agents and Integrations: As your AI ecosystem grows, so does your attack surface. We thoroughly evaluate agentic workflows, such as API-hooked actions that allow the AI to send emails, query databases, or create tickets, to ensure tool and plugin access stays strictly within intended controls.
Expanding the Scope: To ensure complete security from the database to the chat interface, we highly recommend pairing your LLM assessment with a standard Web Application Penetration Test. This guarantees that your surrounding implementation layer does not become the weak entry point for attackers.
Insights That Speed Up Innovation
Your AI systems deserve more than surface-level testing. By actively hunting for prompt injection, jailbreak risks, and guardrail evasion before public exposure, you can strengthen trust in your customer-facing AI systems without degrading performance.
At the end of a Rhymetec engagement, you receive an executive presentation and a comprehensive report featuring validated prompt-based exploits, prioritized severity ratings, and prescriptive remediation guidance.
Looking for LLM Penetration Testing Services? We can help.
Accelerate your AI deployment without compromising security. Contact Rhymetec to learn how our LLM Penetration Testing services can secure your generative AI architecture and keep your innovation moving forward.
Artificial intelligence is accelerating software development and reshaping the security expectations that surround it. Developers are shipping code faster than ever, often with the assistance of AI tools.
However, this same technology has also changed the economics of attacking software. Adversaries are using AI to lower the cost of reconnaissance and iterate through exploits at scale.
In a recent webinar hosted by Rhymetec and XBOW, Christian Mouer, Director of Offensive Security at Rhymetec and Bill Nichols, Head of Customer Success at XBOW explored how an AI-powered penetration testing model allows organizations to increase testing velocity, validate real attack paths faster, and gain broader visibility across modern applications, while maintaining the depth and context required for meaningful risk reduction.
Why Traditional Penetration Testing Timelines No Longer Match Modern Development
Many organizations still rely on annual or semi-annual point-in-time tests, an engagement begins, a snapshot is taken, and a report is delivered weeks later. That approach worked when applications changed slowly and release cycles were measured in quarters.
Today, development moves continuously. New features, endpoints, and integrations are introduced on a weekly, sometimes daily, basis. By the time a traditional test is completed, the environment it assessed has already evolved.
To keep pace, defenders cannot simply scale humans linearly with software output: it is cost and time-prohibitive. This is where autonomous offensive security comes in.
From Theoretical Exposure to Proven Exploitability
One of the most consistent pain points for security teams is the volume of unverified findings produced by automated tools. Large scan outputs require significant internal effort to determine what is real, what is exploitable, and what actually matters to the business.
The approach demonstrated in the webinar prioritizes validation. Exploits are executed against the live environment, attack paths are confirmed, and results are correlated before they are ever delivered.
That shift changes the nature of the final report. Instead of a backlog of potential issues, organizations receive a focused set of confirmed vulnerabilities with clear evidence of impact.
“Hypotheses are cheap. Proof isn’t. We don’t surface a finding unless the system can validate that it’s real.” — Bill Nichols, XBOW
For security and engineering teams, this significantly reduces the time spent reproducing issues and allows remediation efforts to begin immediately.
Expanding Coverage Without Extending Engagement Length
Application ecosystems have grown far beyond a single web interface. Modern environments include large API surfaces, multiple user roles, third-party integrations, and complex authorization logic.
Manually mapping and testing that entire landscape within a standard engagement window forces difficult tradeoffs. Teams must choose between depth in a few areas or lighter coverage across the whole application.
Autonomous execution removes that constraint. Continuous attack surface mapping and parallel exploit testing allow a far greater portion of the environment to be assessed in the same timeframe.
“It’s another pen tester on the team. If we work together, we're able to cover so much more ground than we would have otherwise." — Christian Mouer, Rhymetec
This expanded coverage is what makes deeper, human-led analysis possible later in the engagement.
Reallocating Human Expertise to High-Value Security Work
When the most time-intensive phases of testing, such as reconnaissance, enumeration, and initial exploitation, are handled autonomously, the role of the tester changes.
Instead of spending the majority of the engagement identifying entry points, offensive security experts are able to focus on:
- Chaining multi-step attack paths
- Analyzing real business impact
- Validating complex authorization scenarios
- Working directly with developers on practical remediation strategies
“When we’re cutting down that investigative time, it gives us additional days to validate, find more vulnerabilities, and explore more deep-dive attack paths.” — Christian Mouer, Rhymetec
This is where the greatest risk reduction occurs and where human experience delivers the most value.
The Hybrid Approach: Why AI Doesn't Replace Humans
A common misconception about AI powered penetration testing is that it aims to replace human testers. In practice, the model works as an extension of the testing team rather than a substitute for it.
While XBOW can map an attack surface and execute exploits 24/7, it lacks the business context and nuance that a Rhymetec offensive security expert provides.
Business Logic and Context
AI might flag that a user can see all emails in a system. However, a human tester understands the context: if that user is an HR Administrator, that access is intended. Rhymetec’s team supplies the critical business logic to ensure findings are relevant to the organization's specific operations.
Complex Remediation
Finding a bug is only half the battle. Fixing it without breaking the application is the other half. Rhymetec provides the "human element" of advising on remediation strategies that align with the client’s tech stack and resources.
Parallelism and Depth
The ideal workflow involves running XBOW in parallel with manual testing.
Real-World Impact: Speed and Scalability
The combination of XBOW’s automation and Rhymetec’s expertise delivers results that were previously difficult to obtain in both timeline and scope.
During the webinar, the team shared a case study of a massive web application containing approximately 650 endpoints.
- Traditional Timeline: A thorough manual test would typically take 10 to 15 business days.
- AI-Accelerated Timeline: The XBOW agent mapped and tested the environment in roughly 48 hours.
This acceleration allowed the Rhymetec team to spend the remaining time validating complex findings and exploring deep-dive attack paths that the AI surfaced, ultimately delivering a comprehensive report in five days rather than three weeks.
“We’re able to turn around that pen test confidently within five business days rather than going 10 to 15 days out.” — Christian Mouer, Rhymetec
In Conclusion: AI as a Force Multiplier
As 76% of CISOs anticipate a material cyber attack in the next 12 months, the need for speed and accuracy in testing has never been higher.
Rhymetec’s AI-Powered Penetration Testing partnership with XBOW offers the perfect balance of intelligence and intuition. By automating the reconnaissance and vulnerability identification phases, we allow our certified penetration testers to focus on what they do best: validating impact, analyzing business risk, and guiding remediation.
Key Benefits of the Rhymetec x XBOW Partnership:
- Accelerated Timelines: Reduce testing time from weeks to days.
- Reduced Noise: AI-driven validation eliminates false positives common in traditional scanners.
- Deeper Coverage: Test vast attack surfaces and thousands of endpoints simultaneously.
- Actionable Intelligence: Receive reports validated by expert human testers, not just automated logs.
Contact us to learn more about how to integrate AI-powered testing into your security strategy.
Watch the Full Webinar
In this penetration testing FAQ, we go over the most common questions around penetration testing and its role in a modern security program.
According to IBM's annual report, in 2024, the average cost of a data breach reached $4.88 million globally, reflecting a 10% increase from 2023. This is the highest total ever and is projected to continue to increase.
The best way to protect yourself from financial, reputational, and other damages that can result from a data breach is to prevent attacks from happening in the first place.
This is the main goal of penetration testing. Penetration testing is one of the single most effective ways to reduce risk, as it is preventative rather than reactive. A penetration test finds weaknesses in your security before attackers do, thus taking the advantage away from bad actors.
This Rhymetec penetration testing FAQ explores key questions, including what penetration testing is, how it works, why it matters for organizations, how it compares to a vulnerability scan, and how much it can cost.

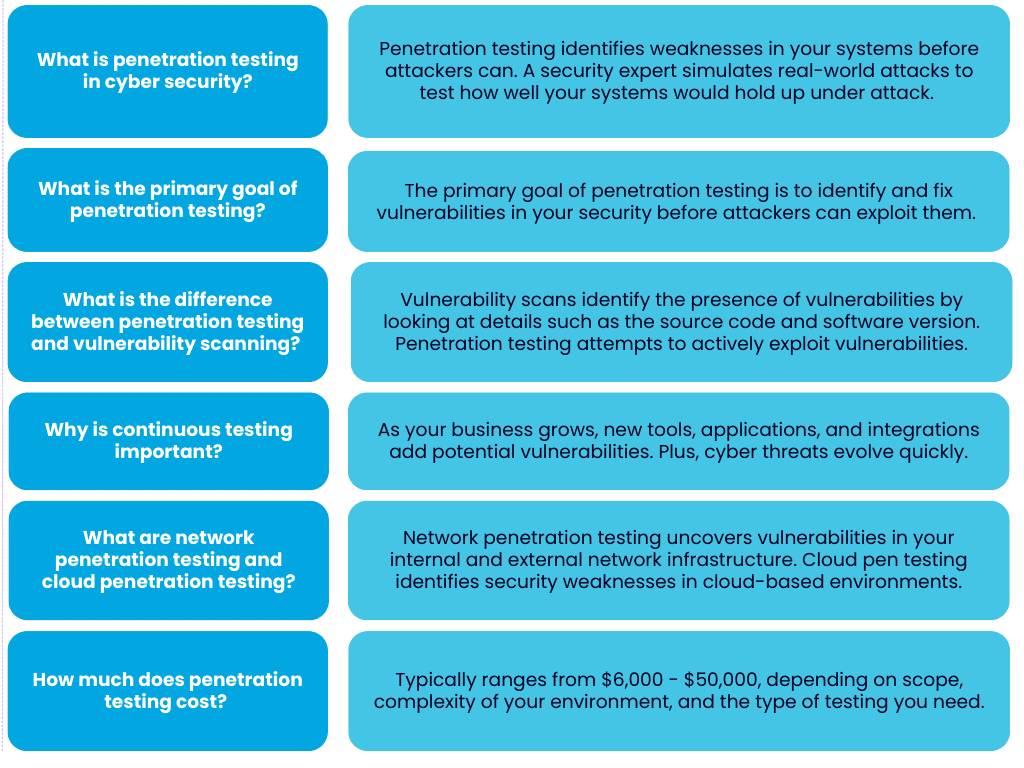
What is penetration testing in cyber security?
Penetration testing is a way to identify weaknesses in your systems before an attacker does:
During a penetration test, a security expert will simulate real-world attacks to test how well your systems would hold up if they were actually under attack. This allows them to pinpoint vulnerabilities that could allow a real attacker to gain unauthorized access and/or expose your sensitive data.
At the end of your penetration test, you'll have a clear picture of the gaps in your defenses.
You can think of a penetration test like hiring a professional to test the locks on your building's doors and windows, but the locks are your firewalls, applications, and networks. After uncovering your potential vulnerabilities, a good pen testing firm will also advise you on where to go from there and provide you with a roadmap to remediate gaps.
What is the primary goal of penetration testing?
The primary goal of penetration testing is to identify and fix vulnerabilities in your security before attackers can exploit them.
The process simulates how a real attacker may attempt to breach your defenses, providing you with insights to act on that are vastly more informative than results from automated scans or theoretical security risks.
After a penetration test, you'll have a clear list of vulnerabilities that need to be addressed, as well as an understanding of the risks these issues pose to your business.
Understanding the tangible impact these risks could have enables you to prioritize which vulnerabilities need to be remediated first. Being able to effectively prioritize risks and allocate resources accordingly (and within the constraints of budgets and resources) is another goal of penetration testing.

Example of Security and Compliance Risks Addressed by Penetration Testing
Let's take an example of a vulnerability that is frequently uncovered during a penetration test and its potential impact:
An overlooked patch could lead to financial loss, downtime, or even damage customer trust. By conducting a penetration test, you bring issues like this to light and can then prioritize actions that have the most significant impact.
In terms of risks of non-compliance, it's important to know that penetration testing is often a compliance requirement and is an industry-standard way to fulfill a range of controls. For SOC 2 compliance, for example, penetration testing can address the risk of unauthorized access to systems that process or store customer data.
Including a penetration test in your SOC 2 readiness assessment prepares you to show auditors that you've covered a range of requirements.
However, compliance alone shouldn't be the end goal! A good pen test helps you align security measures with the unique threats and challenges your business faces, creating a more resilient system overall as your business continues to grow.
Bonus Tip For Startups: Penetration testing can strengthen your position with investors. Demonstrating a commitment to cybersecurity via gold standard measures like penetration testing signals that your business is ready to handle risks that could impact revenue or reputation.
Additionally, as previously mentioned, penetration testing fulfills requirements under a vast range of both voluntary standards and legal requirements that investors may want to see, particularly if you're targeting enterprise clients.

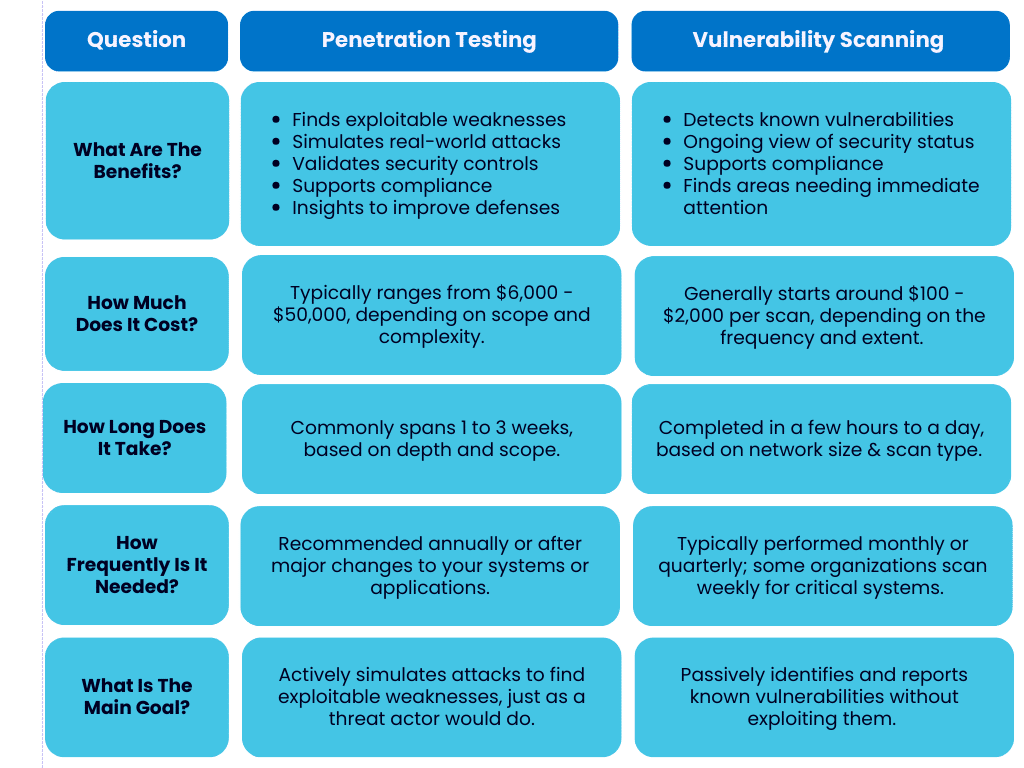
What is the difference between penetration testing and vulnerability scanning?
Both penetration testing and vulnerability scanning should be cornerstones in your cybersecurity strategy.
However, it's important to understand the key differences between these two measures:
The key difference between penetration testing and vulnerability scanning is that vulnerability scans identify the presence of vulnerabilities by looking at details such as the source code and software version but do not attempt to exploit the vulnerabilities.
Penetration testing goes further. Ethical hackers attempt to exploit vulnerabilities to see if they could lead to a security incident. Penetration testing is significantly more robust than vulnerability scanning and allows you to identify the most critical real-world risks and focus your remediation efforts on them.
A vulnerability scan is a great first step for identifying surface-level issues and known vulnerabilities, while penetration testing gives you an understanding of how these issues could be exploited in practice, finds additional potential issues beyond what a vulnerability scan would uncover, and enables you to strategically prioritize remediation of your most pressing risks.
Bonus Tip: If your organization is looking for a firm to run vulnerability scans or conduct a penetration test for you, it's extremely important to understand the differences between penetration testing and vulnerability scanning.
Buyers of security services may encounter issues differentiating between these two measures as a result of technical jargon and a lack of transparency from vendors. Unfortunately, some vendors will claim to offer "penetration testing" that is really just vulnerability scanning and may not be suited to meet your security or compliance goals.
What are the differences between a manual and automated penetration test?
The main difference between manual and automated penetration testing is how vulnerabilities are discovered. What firms may refer to as "automated penetration testing" identifies potential vulnerabilities by scanning for known issues.
Although this is an effective way to discover vulnerabilities quickly, it limits the test to what is already documented in the vulnerability database and does not provide an idea of how these vulnerabilities could be exploited in a real-world scenario by a bad actor.
Zero-Day Attacks and Automated Penetration Testing
A major limitation of automated penetration testing is it cannot detect issues that could lead to zero-day attacks, a type of attack that exploits a vulnerability that is entirely unknown to the security community. Because these vulnerabilities have not been documented, they are some of the most dangerous threats organizations face.
Automated penetration testing relies on databases of known vulnerabilities, leaving a major gap in your security assessment if you rely solely on automated methods. Manual penetration testing is much more involved and remediates this issue by leveraging human expertise and creativity.
The Stuxnet attack is a notorious example of a sophisticated zero-day attack. This malware targeted Iran's nuclear facilities in 2010 and exploited multiple zero-day vulnerabilities in Windows systems and industrial control software. The attack was able to bypass traditional security measures because it exploited flaws that no one knew existed at the time.
While no test can accurately predict every possible zero-day vulnerability, manual penetration testing greatly reduces the risk by finding security gaps that automated tools miss.
Attackers Leverage Both Automated and Manual Tools
Attackers don't rely solely on automated tools, so neither should your penetration testing!
While automated tools can provide a baseline of security by revealing common issues, without manual testing, you risk overlooking a range of serious issues that could lead to a breach.
Manual testing is also more specific. The tester considers your specific business context, such as the value of your data, the risk associated with your technology stack, your risk appetite, and the tactics an attacker would be most likely to use against your organization.
Red Flags Indicating An Overly Automated Penetration Test
If your penetration test feels rushed, provides generic results, or lacks detailed explanations specific to your business, it may rely on heavily automated tools.
Additionally, if the timeline seems unusually short for the scope of work, or if the report lists vulnerabilities without contexts or recommendations, your provider may be running scans without performing the deeper analysis that manual testing entails.
You should always ask your provider about their process and request a scope of work. A reputable firm will explain how they combine automated tools with manual techniques, provide examples of past testing scenarios, and describe the skills and experience of their pen testers.
Why is it important to continuously conduct penetration testing for a strong security system?
Your systems and environments are not static.
As your business grows, new tools, applications, and integrations are introduced - each adding potential vulnerabilities. Cyber threats evolve just as quickly, with attackers developing new techniques to bypass existing defenses.
Continuous penetration testing helps you keep up with these changes and minimizes the likelihood of an unknown vulnerability turning into an incident.
Compliance requirements also often call for regular penetration testing, but compliance isn't the only reason you should be conducting pen testing. Regular penetration testing creates a process where risks are identified and addressed, rather than waiting and having to react to what could have been avoidable incidents.
For organizations like startups where change is constant, ongoing penetration testing helps you stay informed and ahead of threats as the threat landscape evolves.
Continuously conducting penetration testing protects sensitive data and reduces the overall cost of addressing vulnerabilities by catching them early while reassuring stakeholders and customers that security is a consistent priority for your business.
What is network penetration testing?
Network penetration testing uncovers vulnerabilities in your internal and external network infrastructure:
Internal networks include devices and systems within your organization, such as local file shares, servers, and employee workstations. External networks are the points where your systems interact with the internet, such as public-facing websites or VPN gateways.
A network penetration test mimics the actions of a hacker attempting to exploit weak points specifically in your network. For example, this could take the shape of testing firewalls to see if they're properly configured, identifying open ports that could allow unauthorized access, or determining if you have any outdated protocols leaving your systems exposed.
Bonus Tip: Network penetration testing is particularly relevant as remote work and cloud adoption expand! These trends increase the complexity of network environments and expand your attack surface. Regular network testing helps you maintain visibility and control over your infrastructure and minimizes the risk of unauthorized access or disruption.

What is cloud penetration testing?
Cloud penetration testing identifies security weaknesses in cloud-based environments by testing the security of APIs, the configuration of your cloud infrastructure, how access controls are managed, and more.
An example of a common issue in cloud environments that cloud penetration testing often reveals the presence of is misconfigured storage. Sensitive data can be easily left exposed to the internet if storage is misconfigured.
Another example is overly permissive access controls that allow unauthorized users to interact with resources they should not have access to. Cloud penetration testing simulates attacks to help you find and remediate these risks, among others.
Bonus Tip: Cloud security is often a shared responsibility with your cloud provider. While providers like AWS or Azure manage the security of the underlying infrastructure, you are responsible for securing how you use their services. A penetration test helps you verify that your configurations align with both security best practices and your business needs.
How much does penetration testing cost?
The cost of a penetration test depends on the scope of the test, the size and complexity of your environment, and the type of testing you need.
For smaller organizations with a relatively straightforward network or a single application, a test may range from a few thousand to several thousand dollars. Larger organizations with more complex systems can anticipate higher costs due to the amount of time and resources required.
Specialized tests, such as those targeting cloud environments, APIs, or compliance requirements, may also carry a heavier price tag. A basic external test that focuses on your public-facing systems will generally cost less than a more comprehensive internal test that examines your entire network.
While penetration testing is an investment, it helps reduce the potential costs of a breach, which can include lost revenue, damaged reputation, and non-compliance issues. Understanding and remediating your risks early on can save your business substantially in the long run. Hopefully this penetration testing FAQ provided a solid idea of the cost-benefit analysis of investing in pen testing for your organization.
Penetration Testing FAQ:
In Conclusion: Penetration Testing FAQ
We hope this penetration testing FAQ provided helpful information and gave you a deeper understanding of penetration testing and what to look for when assessing vendors.
If you have further questions, our experts at Rhymetec are happy to help. We offer a range of penetration testing services, including:
- API Penetration Testing
- External Network Penetration Testing
- Mobile Application Penetration Testing
- Web Application Penetration Testing
Contact us today to learn more.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.
Did you know that most data leaks and vulnerabilities don't stem from highly sophisticated hackers exploiting zero-day vulnerabilities, but rather from simple misconfigurations and poor access controls?
It's no secret that cloud environments are complex - actually, "incredibly complex" might be a better description. It's also well known that people are prone to errors. Sometimes these are as simple as misplacing keys; other times, they involve your cloud admin making their password "admin" and leading to a major breach.
You might be thinking, "My team is experienced and highly competent; there's no way we'd make such basic mistakes."
Well, cloud penetration testing lets you put that belief to the test.
A cloud penetration test is conceptually similar to a traditional network penetration test: A white hat hacker attempts to breach your cloud environment while documenting the vulnerabilities and misconfigurations they exploit to gain access. Cloud penetration testing applies this same framework to cloud environments.

What Exactly Is Cloud Penetration Testing?
Cloud penetration testing involves an outside party (usually a specialized security provider like Rhymetec) taking on the role of a threat actor attempting to gain access to your cloud environment. How the firm or individual gains access can include many forms, such as:
- Configuration analysis - Examining network access controls and service configurations for vulnerabilities.
- Identity federation testing - Examining cross-account access, third-party integrations, and federation configurations.
- Storage assessment - Checking for improperly secured storage buckets, publicly accessible data, and inadequate encryption.
- Identity and Access Management (IAM) exploitation - Testing for overly permissive roles, misconfigured policies, and compromised credentials.
- API security testing - Probing API endpoints for vulnerabilities, authentication bypasses, and authorization flaws.
- Container security evaluation - Analyzing container configurations, image vulnerabilities, and orchestration misconfigurations.
- Serverless function testing - Examining function permissions, runtime vulnerabilities, and dependency issues.
- Network security assessment - Testing VPC configurations, firewall rules, and network segmentation.
- Service-specific testing - Evaluating the security of managed services like databases, load balancers, and compute instances.
- Compliance validation - Ensuring cloud resources meet regulatory requirements and security standards.
A good cloud penetration testing company will spend the time to scope out the work with you prior to the engagement.
Working with a pen testing firm that takes the time to understand your organization's context and needs is critical. This is because penetration testing shouldn't be done in a vacuum - it's a small piece of a larger puzzle that creates effective risk mitigation for an organization.
Ideally, a cloud penetration test is aligned with an organization's risk assessment and broader security architecture to maximize the value that the pen test brings.
The Stages of a Cloud Penetration Testing Engagement
A cloud penetration testing firm begins with reconnaissance and planning, the foundation of any successful security assessment.
A pen testing team or individual takes the time to thoroughly map out your cloud infrastructure landscape. This entails listing assets, understanding how your cloud services interact, establishing clear boundaries for testing, and ensuring that the firm and client agree to a fixed set of rules of engagement.
Ideally, this should be closely aligned with your organization's risk assessment. If you don't have a formal risk assessment documented, ask questions like:
- What cloud infrastructure holds the most sensitive data?
- What would be the legal, reputation, and compliance risks if a certain system was breached?
- Which parts of cloud infrastructure contain the most essential elements required for business continuity?
- Has the cloud admin actually set his password as admin (ok we're slightly kidding with this one, but ensuring good password hygiene is a critical step!).
- What dependencies do core business functions have on various elements of the cloud infrastructure?
Next comes the discovery and enumeration phase.
This is where a pen testing firm actively probes your cloud environment, looking for exploitable vulnerabilities or other flaws in your cloud security. For example, a team will scan for public-facing assets, identifying potential entry points, and mapping the web of relationships between different cloud services.
The vulnerability assessment phase is where a security team actively begins attempting to gain access. This is where theory meets practice - the pen testing team is not just identifying potential vulnerabilities. At this stage, they're determining if they're actually exploitable.
A competent security team will dig deep into IAM roles and permissions, probe API endpoints, and examine storage configurations. It's like pressure testing every door and window in your digital house.
Then comes active exploitation. The pen testing firm will attempt to chain vulnerabilities together, gain access, move laterally, and escalate privileges. Think of it as stress-testing your security controls under real-world conditions. The team will document every successful path to build a map of potential vulnerabilities, misconfigurations, and weaknesses in your cloud security approach.
Post-exploitation explores the potential impact of any successful breaches. What sensitive data could the team access? How far could they move through the environment? What business-critical systems were within reach?
This phase often reveals the true business impact of technical vulnerabilities - turning technical findings into business risks that leadership can understand and act on.
Finally, we reach the documentation and reporting phase, where all these findings transform into actionable intelligence. This shouldn't be just a dry technical report, but rather, a roadmap for improving your security posture.
At Rhymetec, our team provides detailed vulnerability reports, clear exploitation paths, and prioritized remediation steps. Most importantly, we translate technical findings into business impact, helping everyone understand not just what we found, but why it matters.
Going Beyond MFA
Many organizations mistakenly believe that just because they have implemented multi-factor authentication (MFA) means that pen tests and deeper security measures aren't necessary. Unfortunately, this couldn't be further from the truth.
Security only works when organizations take a defense-in-depth approach - they layer security controls one on top of the other to mitigate as much as possible the risk of a breach of confidentiality, integrity, or availability of core IT systems. If a threat actor finds a stolen credential that works, you're back down to single-factor authentication.
2FA is also bypassable. Threat actors use stolen session cookies that result from malware infections and MFA fatigue attacks to bypass authenticator codes directly (or if the MFA is via SMS, they can use SIM swapping).
MFA is a fantastic first step and is a baseline cybersecurity measure for startups and other organizations. It should be an initial strong layer of security but not your be-all-end-all approach to ensuring the confidentiality, availability, and integrity of your cloud environment.
Choose Rhymetec For Your Cloud Penetration Test
Unfortunately, with today's highly commoditized cybercrime landscape, the question isn't whether your cloud environment will face attempted breaches - it's when. Whether you're running a startup with a simple cloud setup or managing a complex enterprise environment, the stakes have never been higher. Your customers trust you with their data, your employees rely on your systems, and your business depends on the integrity of your cloud infrastructure.
A Rhymetec pen test entails an intentional launching of simulated cyberattacks by our own penetration testers to access or exploit computer systems, networks, websites, and applications. Our pen testers will identify exploitable issues so that effective security controls can be implemented or will test the robustness of your current infosec program.
Our cloud penetration testing experts will work with you to develop and execute on a comprehensive penetration testing plan that puts your business in a position to defeat attackers and ensure the confidentiality, availability, and integrity of your cloud environment.
About Rhymetec
At Rhymetec, our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- 25 Cybersecurity Memes For 2025: The Ultimate List of Security and Compliance Memes
- Penetration Testing vs. Vulnerability Scanning: What Are The Differences?
- Compliance For Startups: The Definitive Guide to Picking The Right Consultant
Penetration testing is one of the most critical and misunderstood security activities for companies. Often, buyers of security services may have difficulty differentiating between penetration tests and vulnerability scans as a result of technical jargon and a lack of clarity from vendors.
Vendors contribute to this confusion by claiming to offer "penetration testing" that, in reality, involves only spending a short time running automated tools. This article explores the differences between a penetration test and a vulnerability scan to clarify how they differ and where each fits into a modern security program.
Let's jump right in with the main differences at a high level:
Penetration Testing Vs. Vulnerability Scanning: 6 Main Differences
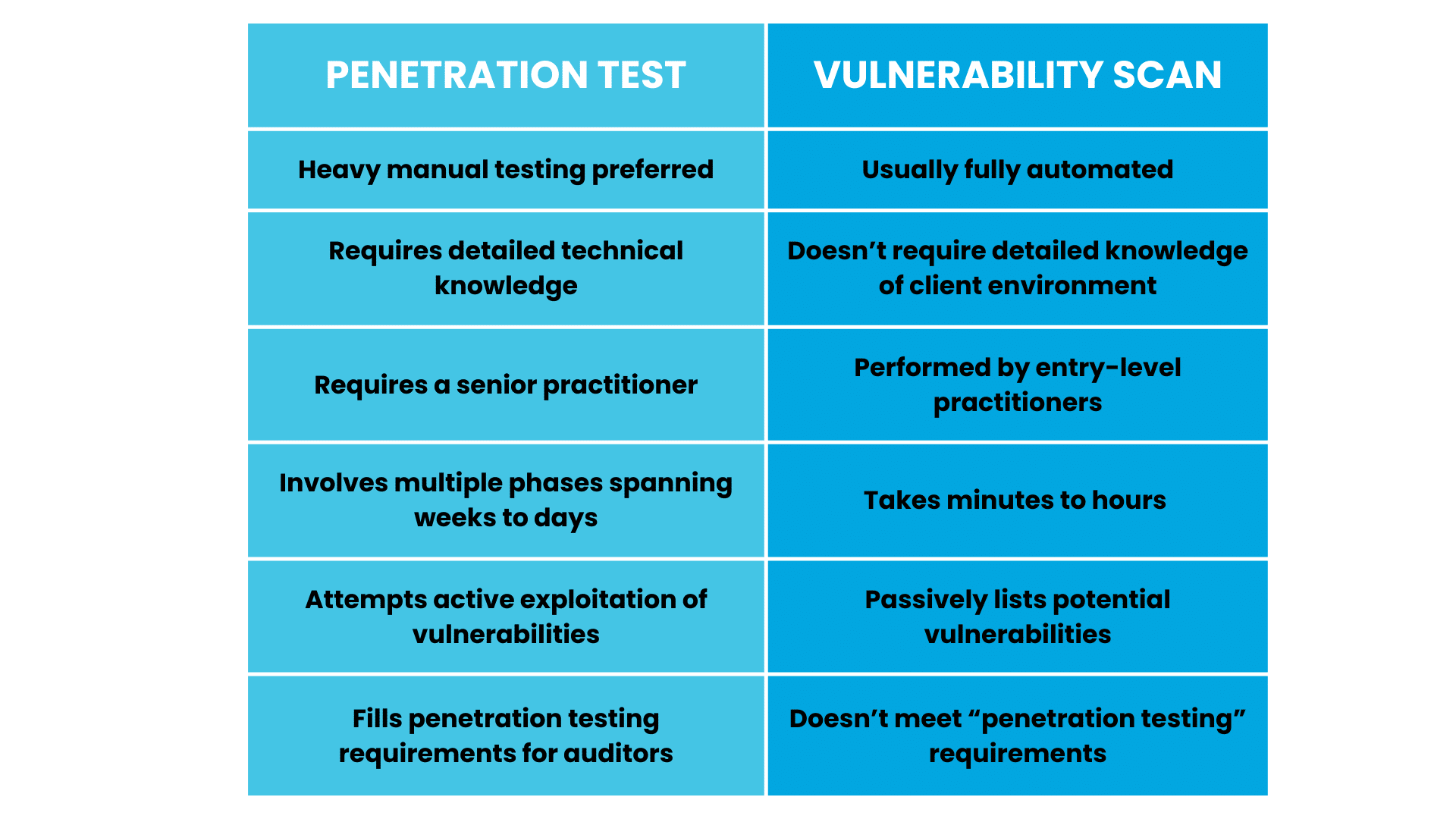
Penetration testing is substantially more involved than vulnerability scanning.
While penetration testing and vulnerability scanning are both important for identifying security risks, they serve different purposes:
Penetration testing is largely manual, requires expert knowledge, and can take weeks. A senior-level practitioner aims to exploit vulnerabilities (just like a real threat actor would do) in order to identify weak points. Vulnerability scanning is mostly automated and needs minimal expertise, but is useful for passively identifying risks on an ongoing basis.
When assessing pen testing vendors, it's critical to know the differences. Some vendors claim to offer "penetration testing" when, in reality, what they are really doing is vulnerability scanning.
Next, let's go over penetration testing vs. vulnerability scanning in more detail to equip you with the information to decide if you need one or the other (or both) for your organization.
What Is A Vulnerability Scan?
Almost all modern software applications have vulnerabilities or weaknesses in the code that can allow an attacker to gain information or privileged access that the software doesn't intend. Major software companies such as Microsoft and Apple routinely deploy patches to both personal computers and to servers to fix identified vulnerabilities.
In their simplest form, vulnerability scans involve using tools like Nessus and Shodan to proactively scan for known vulnerabilities against an IP range to identify unpatched systems and prioritize the highest-risk vulnerabilities.
Vulnerability scans are meant to be run regularly after even minor changes to an organization's IT infrastructure. It's worth noting that threat actors use the same tools as security teams to continuously scan the internet, looking for internet-facing devices with exploitable software vulnerabilities.
Vulnerabilities in Context: Vulnerabilities on externally facing assets (such as hosts and servers exposed to the internet) tend to be more critical than vulnerabilities on computers that are not accessible to the internet. Additionally, not all vulnerabilities are equally risky. Some are "theoretical" in that nobody has actively exploited them before. This type of vulnerability tends to be a lower priority than a vulnerability that is known to be actively exploited by threat actors.
Generally speaking, vulnerability scans can be performed automatically by entry-level team members as the software will automatically identify, prioritize, and report on vulnerabilities. Vulnerability scans do not attempt to exploit the vulnerabilities. They only identify their presence by looking at details such as the source code and software version.
Think of a vulnerability scan like a security guard checking to ensure all of the doors are locked in an office building. Meanwhile, a penetration test is like a skilled lockpicker trying to unlock a door.
What Is A Penetration Test?
The goal of a penetration test is to take the attacker's perspective and actively attempt to gain access to privileged IT systems. The tester will aim to exploit vulnerabilities and leverage exposed servers in order to identify weak points and report on how they did it.
Following up on our security guard analogy, a penetration test involves hiring someone to act as a criminal and try to pick the locks on the building (and the windows, too!). Penetration testing is far more involved, scoped to the individual business, and requires the vendor to have deep expertise.
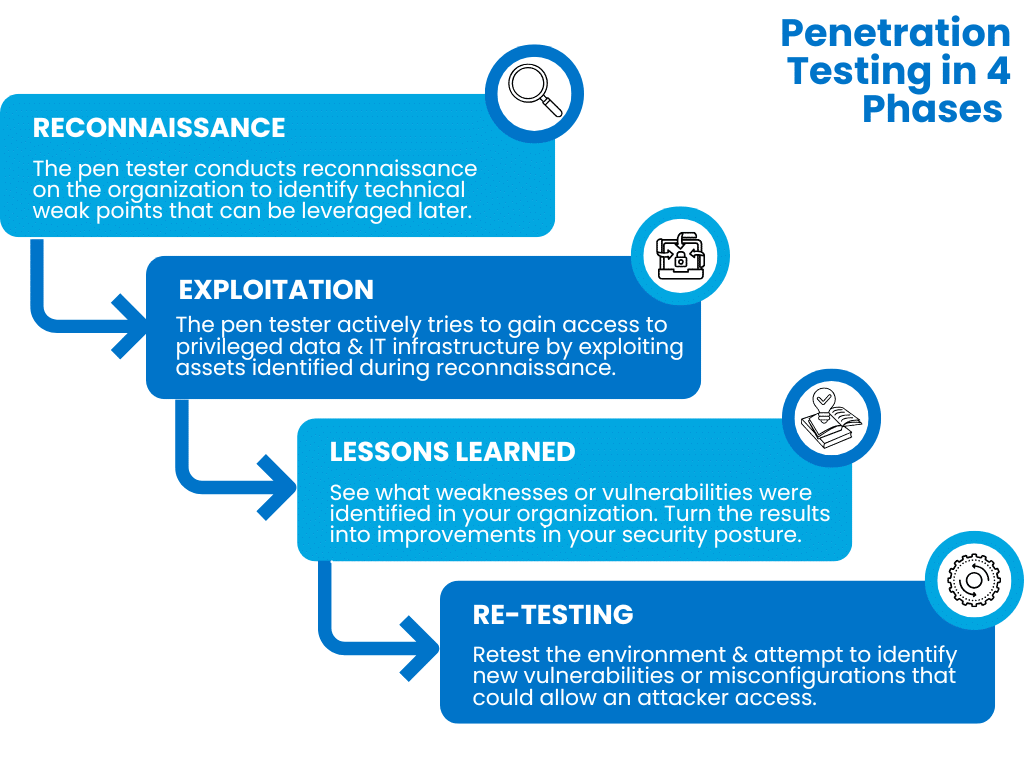
A reputable penetration testing company will work with the client prior to the test, set rules of engagement, and take a multi-phased approach to include:
Reconnaissance: During this phase, the pen tester conducts reconnaissance on the organization to identify technical weak points that can be leveraged later. The pen tester may leverage various proprietary and open-source tools to conduct scanning, identify exposed services, and catalog information to prepare for the exploitation phase.
Exploitation: During the exploitation phase, the penetration testing company will actively try to gain access to privileged data and IT infrastructure by exploiting assets identified during the reconnaissance phase. When successful, a pentester may attempt to move laterally through the network to identify additional resources they can access.
Lessons Learned: This is the most important phase of a penetration test. What weaknesses or vulnerabilities were identified in the target organization? The lessons learned phase is absolutely critical for turning pen testing results into improvements in your organization's security posture.
Re-testing: After a certain period has elapsed, it can be enormously beneficial to retest the environment and attempt to identify new vulnerabilities or misconfigurations that could allow an attacker access.
Security should never be viewed as a one-time fixed event or test. At Rhymetec, we focus on building a continuous security function that proactively meets compliance requirements and identifies gaps in our client's defenses before an attacker does.
Types of Penetration Tests
Penetration tests can be quite varied and are specific to the client's environment.
Rhymetec offers 4 types of testing designed to identify gaps across multiple types of information technology architectures:
- Mobile Application Penetration Testing
- Web Application Penetration Testing
- External Network Penetration Testing
- API Penetration Testing
All types of penetration tests simulate a real attack. They leverage multiple vantage points to attempt to gain access, including exploiting vulnerabilities, but also potentially social engineering, phishing, and even exposed credentials in order to bypass the client's security defenses.
Case Study:
Read the case study on CXO Nexus to see how our penetration testing team at Rhymetec helped them level up their security and compliance, build trust with customers, and improve product development.
Penetration Tests Versus Vulnerability Scans in Context: Compliance
Nearly all major compliance requirements require routine vulnerability scanning and patching. Conducting vulnerability scans is relatively simple and can go a long way toward reducing risk for your organization.
However, for the purposes of compliance, vulnerability scanning is not penetration testing.
Many organizations conduct pen tests solely for the purpose of improving their security posture and uncovering vulnerabilities before attackers do. In many cases, pen tests are required by regulatory compliance requirements as well. The following compliance requirements mandate a penetration test in order to be audit-ready:
- FedRAMP: Requires cloud service providers to conduct penetration tests.
- PCI DSS: Some levels of PCI DSS require a penetration test once per year for most organizations that handle credit card transactions. It can also be required biannually for service organizations that handle credit card transactions and who segment their network to protect cardholder data.
- FISMA: Requires federal agencies to conduct penetration tests and vulnerability assessments on a sampling of their information systems annually.
- NIST's Special Publication 800-53: Requires federal organizations to perform penetration testing under control CA-8.
Companies can also use penetration testing to strengthen their compliance posture and demonstrate proactive cybersecurity to meet other requirements. Requirements that benefit from penetration testing and for which it can be used to fulfill controls (but is not outright required) include:
- HIPAA
- HITRUST
- SOC 2
- ISO 27001
- CCPA
- NIST
- GDPR
We often hear from our customers that although a penetration test is not an explicit requirement under frameworks like SOC 2, their auditors are inquiring about whether or not they've undergone a penetration test.
As the gold standard method of testing the strength of your security, penetration testing adds a strong layer of assurance going into your audit.
Penetration Tests and Security Questionnaires
Almost all compliance requirements and security questionnaires require routine vulnerability scanning. Proactively conducting penetration tests can be an additional high-value way to demonstrate continuous compliance to clients and show that your firm takes security seriously.
Large corporations, in particular, are increasingly requiring potential vendors to answer rigorous security questionnaires. Penetration testing, combined with meeting voluntary compliance requirements such as SOC 2 or ISO 27001, goes a long way toward demonstrating that your organization has a serious security program.
Penetration Testing vs. Vulnerability Scanning FAQ
What Are The Benefits of Penetration Testing?
- Identifies exploitable weaknesses in systems.
- Simulates real-world attacks to gauge your organization's response.
- Helps validate security controls.
- Provides practical insights for improving your security defenses.
- Supports compliance with security standards.
What Are The Benefits of Vulnerability Scanning?
- Detects known vulnerabilities.
- Offers a continuous view of your systems' security status.
- Highlights areas needing immediate attention.
- Supports compliance with security standards.
How Much Does Penetration Testing Cost?
- Penetration testing typically ranges from $6,000 to $50,000, depending on scope and complexity.
How Much Does Vulnerability Scanning Cost?
- Vulnerability scanning generally starts around $100 - $2,000 per scan, depending on the frequency and extent.
How Long Does A Pen Test Take?
- A penetration test commonly spans 1 to 3 weeks, based on depth and scope.
How Long Does A Vulnerability Scan Take?
- A vulnerability scan is often completed in a few hours to a day, depending on network size and scan type.
How Frequently Do You Need Penetration Testing vs. Vulnerability Scanning?
- Penetration testing is recommended at a minimum annually or after major changes to your systems or applications.
- Vulnerability scanning is typically performed monthly or quarterly; some organizations scan weekly for critical systems.
What Is The Main Difference Between Penetration Testing and Vulnerability Scanning?
- Penetration testing actively simulates attacks to find exploitable weaknesses, just as a real threat actor would do, while vulnerability scanning passively identifies and reports known vulnerabilities without exploiting them.
Frequently Asked Questions
The Bottom Line: Penetration Testing vs. Vulnerability Scanning
Vulnerability scanning and penetration testing are both critical for your company's security.
We hope at this point it's clear that a vulnerability scan is a single fixed-in-time way to identify unpatched systems that have software vulnerabilities, while penetration testing involves simulating an attacker in a real-life attempt to gain access to your organization's sensitive IT infrastructure.
From an audit perspective, your auditors may expect to see that you've undergone a penetration test. Regular penetration testing will vastly strengthen your security program's credibility with auditors and give your prospects and clients confidence in your security.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering. Under Metin’s leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
Interested in reading more? Check out more content on our blog:
- CISO As a Service: A Scalable Security Solution
- How To Select The Right Pen Testing Vendor for Your SaaS Business
- Security vs. Compliance? A False Dichotomy
You might be wondering - Why would a threat actor bother targeting a startup? Don't they focus on larger companies?
In 2025, cybersecurity for startups is just as critical as it is for the world's largest organizations. You may be surprised to learn that small businesses nowadays are actually more frequent targets of cyberattacks than larger companies.
According to Verizon's 2023 Data Breach Investigations Report, there's a very clear reason for this:
Regardless of organizational size, companies are increasingly adopting similar services and infrastructure. This means that the attack surface of small organizations - all of the points from which a threat actor can access a system - looks more similar than ever to that of large companies.
When it comes to the attack surface of small versus large businesses, "...by now there is so little difference based on organizational size that we were hard-pressed to make any distinctions whatsoever." (Verizon, 2023).
While it's great that many business-accelerating tools are now equally accessible to small organizations, this democratization of technology has a dark side:
Organizations, from startups to Fortune 500, have increasingly similar risk profiles but do not have the same resources to prevent and respond to attacks.
From a threat actor's perspective, this makes smaller organizations ripe targets. In light of this, what can you do as a startup to improve your security, especially without breaking the bank?
This guide will discuss:
- Why is Cybersecurity for Startups Important?
- 5 Practical Things You Can Do Right Away
- Measures to Further Improve Your Security
- Balancing Security With Budget
- Frequently Asked Questions
- Accelerating Cybersecurity for Startups
Rhymetec was specifically founded with the mission to make cutting-edge security available to startups. We've worked with hundreds of companies to provide practical solutions that enable them to be as secure as possible while also balancing security with budget.
This guide will provide actionable solutions for cybersecurity for startups based on:
- Our experience working with hundreds of startups.
- Current trends in the industry in 2025.
Why is Cybersecurity for Startups Important?
Large companies have the resources to continuously sharpen their security measures and keep up with increasingly stringent compliance requirements. Meanwhile, smaller businesses without the same resources to devote to security are left behind.
Threat actors know this, and that's why an employee at a company with less than 100 employees receives 350% more social engineering attacks in their email than an employee at a large company.
And the smaller the business, the harder the attack hits: For over half of small companies, all it takes is one data breach to go out of business within 6 months.
What does this mean?
Startups need to invest in cybersecurity as much as large companies do, ideally from the onset. Fortunately, nowadays, there are affordable solutions for startups to access cybersecurity services and expertise historically reserved for large companies:
Instead of building out expensive in-house security teams, many startups turn to Virtual CISO Services as an alternative. Additionally, there are measures any startup can take right away to improve security, which we'll discuss in the section "5 Practical Things To Do Right Away".
But first, let's talk about the most common threats faced by startups in 2025. We'll keep these in mind when suggesting security measures you should consider.
Common Security Threats Faced by Startups in 2025
According to Verizon, 92% of tactics threat actors use against small businesses are either:
- Social engineering tactics, such as phishing emails.
- Basic web application attacks.
User credentials (like passwords) are the most frequently compromised type of data. This is because threat actors know this type of data is particularly vulnerable when hosted and processed by small organizations without strong security.
Even if you aren't at the stage where you want to explore building out a comprehensive security program, there are a few things you can do in the short term.
With the most common threats faced by startups in mind, here are 5 solutions that will mitigate a huge amount of risk right off the bat:
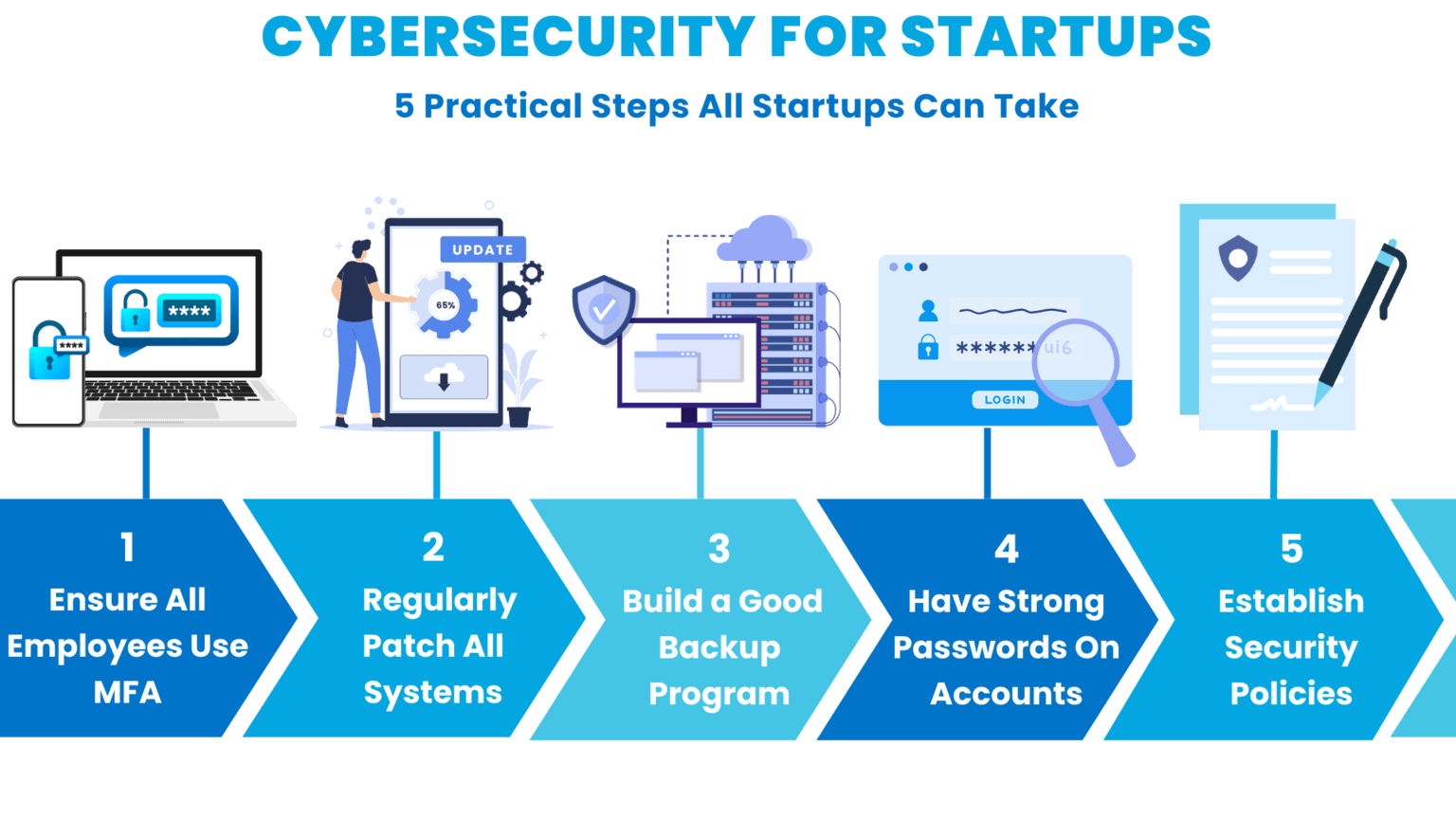
Cybersecurity for Startups: 5 Practical Things To Do Right Away
We get how much running a startup involves on a daily basis.
Even if you're crunched for time and resources, fortunately, there are a few 'quick win' measures you can take to improve your security immediately!
Some of these may seem basic. But you would be stunned how many people, even in high-level positions, are using passwords like "032564Oreo (user's birthday + their cat's name), or "newpassword2025!" (self-explanatory).
It's best to play it safe and operate from the assumption that most people simply don't practice good security hygiene. It's on company leadership to provide guidance and policies.
With this in mind, here are 5 measures you can take right away:
1. Ensure All Employees Use MFA At Your Startup
Multi-factor authentication (MFA) is critical to an effective security program.
Implementing MFA across all accounts, including cloud access, network access, and even SaaS access accounts, is the number one thing you can do to reduce the risk of a major incident or breach.

Without MFA, all a major breach takes is a single employee setting a weak password, which a threat actor then identifies through password spraying or traditional leaks.
Beyond simply setting up and requiring MFA, there are additional steps you should take in light of the current threat landscape in 2025. Unfortunately, threat actors have inventive ways around MFA nowadays.
To mitigate this risk, here are some important tips when setting up MFA controls:
- Understand where your customer data lives. Individual teams and employees may purchase new SaaS applications on their own authority and begin storing customer and other data in these systems. Without adequate controls and visibility, employees may be storing customer data in SaaS solutions without MFA that your IT and security teams are unaware of.
- Set short time-to-live (TLL) on session cookies where possible. Session cookies allow a user to reauthenticate without having to reenter a code for a set duration of time. If session cookies are stolen in the meantime, they can be used in a session replay attack to bypass codes. Setting time-to-live for cookies as shortly as possible does inconvenience users, but reduces the risk that if a threat actor steals cookies, they can be effectively used.
- When implementing MFA, it is strongly recommended to use authenticator applications rather than SMS-based authentication when possible. SMS-based authentication is susceptible through a practice known as "SIM Swapping," in which threat actors either social engineer or steal the means to swap SIM devices at the carrier level, allowing them to hijack a user's cellphone traffic.
2. Make Sure All Systems Are Patched
Many cyberattacks happen as a result of organizations not building a successful vulnerability management practice. Threat actors continuously scan for publicly facing IT assets with known vulnerabilities to identify potential targets to exploit.
A great example of this is the WannaCry ransomware attack in 2017. The exploit used by threat actors had actually been patched in Windows two months prior to the attack. Devices up-to-date on the latest security updates were not impacted by the attack. Meanwhile, devices that hadn't kept up with the latest patches were left vulnerable.
Vulnerability prioritization can be a pain. It isn't always clear when a vulnerability is critical versus when it can be delayed somewhat. Additionally, patches can be extremely disruptive to existing IT infrastructure. All of this makes effectively patching systems quite difficult. Here are a few tips:
- Prioritize vulnerabilities on publicly facing systems first: Threat actors regularly scan the internet looking for known exploitable vulnerabilities on publicly facing systems. An instance of this in 2025 includes the ConnectWise ScreenConnect vulnerability. Another recent example includes the MOVEit vulnerability.
- Prioritize actively exploited vulnerabilities: Not all vulnerabilities are equally high-risk. Vulnerabilities that are theoretical or haven't been known to be "actively exploited in the wild" are likely lower risk and can be deprioritized compared to those that threat actors are utilizing.
- Use a vulnerability management service like Shodan: Shodan can help identify publicly facing IT assets along with services running on them. This can dramatically expedite mapping your organization's attack surface and identifying services that may have exploitable vulnerabilities.
3. Build A Cybersecurity Program With an Extensive Backup and Recovery Program
It's no secret that ransomware groups often encrypt sensitive data belonging to organizations. But ransomware isn't the only reason you should have a strong backup and recovery program.
Natural disasters, unexpected outages, and threat actors can all compromise the confidentiality, integrity, and availability of data. This creates enormous risk.
Create not just a backup system for your startup, but a backup and recovery program that includes technology (either localized or cloud backups), processes (policies and procedures), and people responsible for ensuring it all works together.
Once you have a system that works, test it!
Tabletop exercises can be invaluable in testing real-world examples to make sure that your system works, everyone knows their role, and you can effectively respond to a crisis.
Bonus Tip: Be sure to back up your "less" critical systems.
Don't underestimate the dependencies between data and software applications. Even if your organization has multiple systems, don't isolate backup and recovery to "only" the most critical. It is often easy to overlook data dependencies between systems where one system going down can render another entirely nonfunctional.
4. Ensure All Employees Have A Strong Password
Many organizations make the mistake of believing that if they have strong two-factor authentication, they are adequately protected and don't need to worry too much about weak passwords. This couldn't be further from the truth.
If you have a weak, easily guessable password and two-factor authentication, you only really have single-factor authentication!
IBM's recent X-Force Report showed that identity-based attacks that involve leveraging valid user accounts are now the predominant way threat actors compromise environments. Compromising a single valid user account with administrative privileges can quickly escalate into a full-blown breach.
Multi-factor authentication means your organization has strong passwords and monitors password reuse. Here are a few tips to ensure employees are using good passwords:
- Create strong passwords with a length requirement, special characters, numbers, and letters.
- Use a credential monitoring service like haveibeenpwned to identify if a user's credentials have been compromised in a data breach. Rotate credentials immediately if this has happened.
- Talk extensively about password hygiene during regular security trainings. Emphasize not to reuse passwords across services. Walk users through how reusing passwords can result in the organization being compromised.
Bonus Tip: Use a password manager like 1Password.
Tools like 1Password automatically create strong passwords, which are then encrypted and stored so that only authorized users can access them.
This allows members of your team to share passwords without showing the actual password. Additionally, employees can access business-critical accounts across multiple devices without having to remember complex passwords.
If your startup has a remote workforce and employees are logging into their work accounts on multiple devices, a password manager is a must-have.
5. Establish A Written Security Policy
Establishing a written security policy is one of the most critical things you can do to create a strong cybersecurity baseline for your startup.
Rhymetec's Senior Cybersecurity Analyst, Kyle Jones, recently spoke about how to draft and communicate strong security policies. Here are a few tips he suggested:
- Know your audience. If the people who need to understand and adhere to your security policies aren't security knowledgeable, keep that in mind. Don't use overly technical language in your policies. Instead, tailor your language to your audience.
- Emphasize your policies continuously, and connect policies with the reasons behind them. People will be more likely to follow policies if the reason behind them is explained. Find opportunities, such as when an employee has an IT-related question, to reference the policies and see what they say.
- Make sure your policies reflect current trends. Your risk profile changes depending on what's going on in the world! For instance, the launching of large language models (LLMs) like Google's Gemini should make you rethink your policies.
Here are several critical questions about AI:
- Do you know if your employees are sharing data with any LLMs they may be using for work?
- Do you have an established policy around the use of this technology at your startup?
- What about updates to regulatory language around AI? Do your policies take that into account?
A great example of why these questions need to be visited can be seen in Samsung's 2023 data leak with Chat GPT - the company has since banned the internal use of generative AI tools.
Bonus Tip: Create a culture that prioritizes security and transparency.
Share resources and talk to your team regularly about the importance of security.
Don't fearmonger - you never want your employees to feel like they can't come to you if something happens. Make it clear that your door is open, and you want to know if they receive a suspicious email or if they notice unfamiliar software on their work device.
Cybersecurity for Startups: Measures To Further Improve
So, you've made sure your employees are using MFA and that nobody's password is their cat's name. You regularly update all of your systems, back up your data, and already have security policies in place.
Here are the next steps you should take:
1. Build A Formal Process to Assess The Security of Third-Party Vendors and Suppliers
Third-party risk management continues to grow in importance for organizations of all sizes.
We recommend building a full inventory of all third-party suppliers your organization uses and implementing a standard risk screening. Fortunately, modern standards make it easy to quickly screen to see if a potential third party takes information security seriously.
We recommend asking questions like:
- Does your organization have a SOC 2 Type 2 Report, or other third-party attestation on your information security program?
- Are you compliant with the HIPAA Security Rule, New York Department of Financial Services Cybersecurity Rule, or other formal legal requirements?
- Does your organization have documented security policies?
- Do you share customer data with third parties? If so, which ones?
2. Conduct Routine Pen Testing Engagements
Engage a third party (such as Rhymetec) to regularly put your security controls to the test.
Regular pen testing identifies gaps that potential attackers could exploit. Pen tests should be scoped to the specific risks that your organization faces. For example, Rhymetec can help with:
- Web application pen testing to identify vulnerabilities and misconfigurations in web apps.
- Mobile application penetration testing to identify vulnerabilities or exploits in mobile apps that could be exploited.
- Network penetration testing to identify ways that your organization's network could be exposed.
Pen testing is critical to meeting numerous security requirements. It also enables you to better answer questionnaires about your organization's security provided by potential customers.
3. Conduct Simulated Spear-Phishing Tests
Simulated phishing exercises represent another very significant opportunity to improve your security.
Running realistic simulated phishing tests can help condition employees to be wary of even realistic-looking emails purporting to offer them gift cards and sensitive information. Make sure emails look realistic and are targeted. Sending generic emails generated by a platform can come across as too obvious and fail to adequately test users.
Take an attacker's perspective - what might an attacker write without inside knowledge of users to get users to click links?
Bonus Tip: Have An Incident Response Plan In Place.
An incident response plan is a set of documented procedures to act on in the event of a security incident. For instance, do you know what steps to take in the event your startup experiences a ransomware attack?
To recall an earlier example, during the WannaCry ransomware attack in 2017, many victims paid the ransom to try to get their data back. Security professionals generally do not advise paying ransoms. The threat actors behind the WannaCry attack did not restore people's data even after they'd paid the ransom.
Having a documented incident response plan equips you with important know-how in the event you are to experience an attack or a data breach. This saves time, money, and headaches if an incident were to occur.
Balancing Security With Budget
Building good organizational security is critical. However the cost of protecting an asset shouldn't have to exceed the value of the asset.
Cybersecurity for startups needs to be balanced against ease of access, business processes, and the risks associated with the service, data, or application being secured.
At Rhymetec, we work with a lot of SaaS startups who need to build a security program typically because their customers require it and it's difficult to compete in the marketplace without one. These startups are working off a limited budget.
A good place to start to figure out how to balance security with budget is to think about the answers to the following two questions:
- What does your risk profile look like? Narrowing down the specific risks facing your organization helps prioritize where you need to spend your security dollars. For example, if you are located somewhere that's prone to earthquakes and your servers are stored there, that's a high risk. You would want to prioritize taking steps to remediate this.
- What's your risk appetite? Understand what your own risk tolerance is - If you have a low-risk appetite, you will want to commit to remediating any medium or high risks. Or, at the very least, look at how to reduce your risk from high to low in the areas of highest risk.
At Rhymetec, after we assess your risk profile and answer these questions, we get creative on the best way to proceed with building your information security program while keeping in mind budget constraints.
Frequently Asked Questions (FAQ) for Cybersecurity for Startups in 2025
Here are 5 questions we see frequently from startups in 2025. Knowing the answers to these questions - and implementing corresponding policies - is essential for robust cybersecurity for startups.
1. What are some commonly required or requested compliance frameworks for startups in 2025?
- SOC 2 is a voluntary standard often requested by customers to show you take security seriously and that their data will be in good hands if they share it with you.
- ISO 27001 is the leading international standard for information security.
- PCI DISS is necessary if your startup processes credit card payments.
- GDPR is required in 2025 if you handle the personal data of EU citizens.
- HIPAA privacy regulations require organizations dealing with healthcare data to follow procedures around the confidentiality and security of PHI (Protected Health Information).

2. How does the increasing shift to remote work impact cybersecurity for startups in 2025?
Cloud security is critical in the age of remote work.
Without proper controls, even daily activities like file sharing can result in sensitive information being shared with unauthorized users. Following best practices for cloud storage is essential in 2025, including:
- Make sure your employees have a strong separation between work and personal documents and devices.
- Invest in backing up your data to prevent the loss of important information and documents.
3. What should startups do from a security standpoint with all the AI hype?
AI amplifies existing threats, especially social engineering attacks. For example, AI can be used by threat actors to generate a larger number of personalized phishing emails.
This simply means that the best way to protect your business from AI-assisted threats is to strengthen your core security program. Staff awareness training to protect against social engineering attacks is especially important.
4. What are some best-of-breed tools startups can easily utilize in 2025?
As discussed earlier, the attack surface of small organizations is starting to increasingly resemble that of large organizations. What if you could monitor this, even down to the individual employee level?
Services like Picnic enable you to minimize the human attack surface of your startup and protect executives, contractors, and employees from social engineering attacks.
Nowadays, fortunately, there are tools that make security more accessible. Even if you have zero technical background, you can seamlessly integrate tools like Zip Security that provide enterprise-grade security and endpoint threat detection.
5. When is the right time to start looking into cybersecurity for startups?
The straightforward answer here is that if you're reading this, the right time is now.
Don't wait for the perfect time. The reality is that early-stage startups are unfortunately particularly vulnerable to cyberattacks, precisely because threat actors know they often lack even basic security practices.
Plus, it's always better to start building your security program early on so it can grow in alignment with your needs as your startup scales. Implementing a robust information security program after growth involves even more time, money, and resources to catch up.
How MSSPs Can Accelerate Cybersecurity for Startups in 2025
Hiring an external security team can substantially help organizations, especially in the early stages.
Virtual CISOs at organizations like Rhymetec have extensive experience balancing budgetary needs, usability, and security for start-up cybersecurity programs. It's not an easy balance, but leveraging an experienced partner can deliver huge amounts of specialized talent without the need to spend millions of dollars on an in-house security team.
Managed Security Services Providers like Rhymetec have dozens of professionals across security disciplines like cloud security, compliance, web application security, penetration testing, and others. They have the experience putting these skills to work for startups in a way that drives real security outcomes as you scale while also keeping your budget in mind.
To learn more about how our team can accelerate your security while keeping your budget in mind, contact us for more information.
About The Author: Metin Kortak, CISO
Metin Kortak is the Chief Information Security Officer at Rhymetec. Metin began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC 2, ISO 27001, PCI, FedRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. He joined Rhymetec to build data privacy and compliance as a service offering. Under Metin's leadership, these offerings have grown to more than 200 customers, positioning the company as a leading SaaS security service provider in the industry.
Pen testing, or penetration testing, is a cornerstone of security for SaaS businesses. However, companies often overlook its significance, viewing it as “just another expense.” But with cyber threats becoming increasingly sophisticated, it's more than just checking a box; it's a proactive approach to safeguarding your business and your customer’s data. With the cost of cybercrime forecast to increase continuously and reach USD 5.7 trillion by 2028, ensuring robust security measures is essential. Investing in quality pen testing is not only a must but is a strategic move to protect businesses and data.
The Value of Quality Penetration Testing
Pen testing involves experts conducting simulated cyberattacks on a computer system to unveil vulnerabilities. It is more than a security check. A comprehensive pen test provides an in-depth examination of a system's strengths and weaknesses, delivering actionable insights that significantly bolster a company's security posture.
Quality pen testing also assesses an organization’s resilience against malicious attacks and ability to safeguard sensitive data. While budget-friendly, low-cost pen testing might seem economical; it often results in superficial assessments that overlook crucial vulnerabilities that could expose businesses to unforeseen risks and costly repercussions.
A comprehensive pen test enables businesses to make informed decisions, prioritize necessary fixes, and enhance their overall security posture. Continuous engagement with the pen tester throughout the process enhances its value even more, and instead of just receiving a final report, businesses benefit from real-time communication and a collaborative approach.
Questions to Ask When Choosing Penetration Testing Vendors
Now that you know why you need a quality pen test, choosing the right vendor is essential. But where do you start? Here are some critical questions to ask to help guide your decision:
Talent and Quality Factors
- Where is the pen testing team located? The location of the pen tester can affect the understanding and application of regional or industry-specific regulations. This information helps establish whether the pen tester has the relevant local knowledge to conduct a thorough and compliant assessment.
- Who will be conducting the pen test? Are they full-time or contract employees? Knowing who will perform the test helps assess the reliability and quality. Full-time employees may offer consistency and a higher level of accountability than contractors. The answer provides insights into the professionalism and commitment of the team handling the pen test, which can influence the quality and reliability of the results.
- What are their qualifications and past experiences? The qualifications and experience level directly impact the value and relevance of the pen test. A pen tester with substantial, hands-on experience is vital to provide confidence in the results. Knowing the pen tester's background allows assessment of their competence, expertise, and ability to handle the task.
- How many hours will be dedicated? The time devoted reflects the depth and thoroughness of the pen test. Understanding the hours allocated helps gauge the comprehensiveness and whether it will be a detailed and valuable assessment.
Communication and Engagement
- How will the pen tester communicate the findings? Effective communication is key to understanding and acting upon the findings. Get clarity from the vendor on how they share findings and if this will include a written report with actionable steps. The communication method impacts how easily the findings can be interpreted and applied to improve security measures. Ideally, you should be able to communicate directly with the pen tester to get clarification on any issues.
- Will there be regular updates or just a final report? Determine in advance whether the chosen vendor provides regular updates in addition to the final report. Updates can drive a more responsive and adaptive approach to identified vulnerabilities; continuous engagement indicates a committed vendor. Knowing the frequency and style helps determine how engaged and collaborative the process will be, allowing for timely actions and decisions.
Outsourcing and Location
- Do you outsource any services overseas? If so, where? Outsourcing can impact a vendor's control and oversight over the pen testing process. Different locations may also have varying regulations and standards concerning cybersecurity, which can affect the quality. The answer will give insights into the vendor's operational model and whether they maintain complete control over the process. It also provides information on the geographical locations, which might have different cybersecurity norms and regulations.
- How does this impact the quality and security of the data? This question addresses the potential risks associated with outsourcing, such as data integrity and confidentiality. It helps in understanding how the vendor ensures that the quality of the pen test and the security of the data are not compromised. The response will reveal the vendor's commitment to maintaining high-quality services and data security despite outsourcing. It will show the measures they have in place to safeguard data and ensure that the pen testing process remains robust and reliable.
Post-Penetration Testing Actions
After receiving a pen test report, the journey towards enhanced cybersecurity isn't complete. The subsequent steps and actions based on the report's findings are paramount.
Read the Report
Understanding the pen test report is essential. Focus on extracting clear, actionable insights, and avoid getting overwhelmed by technical jargon. Recognize where your vulnerabilities exist and formulate strategies to address them effectively.
Prioritize Remediation
All vulnerabilities are not of equal consequence. Address the most critical issues promptly and manage risks effectively. Adopt a strategic approach to remediation, prioritizing actions based on each vulnerability's severity and potential impact.
Stay Vigilant
Cybersecurity is a continuous journey. A single pen test is not a comprehensive solution but a component of an ongoing security strategy. Maintain regular testing and monitoring practices to ensure your defenses evolve, keeping your systems robust and secure.
Providing Profound Protection Value
Pen testing is a critical requirement for SaaS companies. It's not just about identifying vulnerabilities; it's about understanding the profound value it brings in safeguarding a business's digital assets.
For businesses aiming to thrive in a digital landscape filled with uncertainties and threats, investing in quality pen testing is not merely an option; it's a necessity. Organizations must make strategic decisions to secure a resilient and prosperous future.
You can read the original article posted in Forbes by Rhymetec CEO, Justin Rende.
Exploring Penetration Testing Services?
Rhymetec was founded in 2015 as a Penetration Testing company. Since then, we have served hundreds of SaaS businesses in all their cybersecurity, compliance, and data privacy needs. We're industry leaders in cloud security, and our custom services align with the specific needs of your business.
A Rhymetec pen test entails an intentional launching of simulated cyberattacks by our own penetration testers to access or exploit computer systems, networks, websites, and applications. Our pen testers will identify exploitable issues so that effective security controls can be implemented or will test the robustness of your current infosec program.
Rhymetec's suite of Penetration Tests offers Blackbox, Greybox, and Whitebox testing, including:
- Web Application Penetration Tests
- Mobile Application Penetration Tests
- External Network Penetration Tests
- API Penetration Tests
New pen test reporting dashboard increases speed and quality of penetration testing results
NEW YORK (March 31, 2023) — Rhymetec, the industry leader in cloud security that provides innovative cybersecurity and data privacy services to modern-day SaaS businesses, announced today the launch of a new penetration testing report dashboard with on-demand customized reporting that unifies penetration testing for clients more clearly and precisely.
This new penetration testing workflow management and productivity tool is a centralized source for testing results, provided in an easy-to-consume and consistent format that will save clients time while also helping to enhance levels of communication. This new service offering up levels prior lengthy, multi-page static reports that quickly went out of date and were a burden to get through.
“In our ongoing efforts to enhance our existing offerings and the experience of our clients, we are excited to provide this new reporting platform to our penetration testing services,” said Justin Rende, CEO and founder of Rhymetec. “Clients will now be able to receive their own portal with workflows to unify penetration testing across teams and enterprises, saving them time, money, and frustration.”
The new penetration testing report dashboard allows for greater collaboration by utilizing a centralized location to address vulnerabilities in remediation. Clients have increased visibility into their businesses with a clearer view of vulnerable areas helping them to know real weaknesses that can lead to harm.
“Rhymetec’s dashboard is great, it’s a place I can return to get more clarification and get the best results quickly,” said Becky Klein, VP of technical operations, CXO Nexus. “It is the ideal centralized location for information to be passed back and forth between our team.”
To learn more about Rhymetec and its suite of cybersecurity services, including penetration testing, please visit www.rhymetec.com.
About Rhymetec
Rhymetec is an industry leader in cloud security, providing innovative cybersecurity and data privacy services to the modern-day SaaS business. The company builds, deploys and manages compliant information security and data privacy programs directly within their clients’ unique environments, allowing them to focus on their core competencies within their business. Over the years, Rhymetec’s services have grown to include a vCISO (Virtual CISO) program, ISO Internal Audits, a variety of Penetration Testing services, ASV Scans for PCI Compliance, and Phishing Testing and Training services. For more information, please visit www.rhymetec.com and follow us on Twitter or LinkedIn.
Media Contact
Kristin Hege
[email protected]
480.540.6496
View more of our Blogs here
To Learn More About Rhymetec's
Penetration Testing Services
Contact Our Team