Meeting NIS2 requirements can be complex regardless of organizational size, especially the requirements around managing third-party risks and incident response. In this article, we go over what NIS2 requires, how to avoid penalties, and how to leverage the requirements to support business growth and operations.
The NIS2 Directive represents another new requirement in an increasingly strict cybersecurity regulatory ecosystem. The law, which came into force in January of 2023, specifically impacts organizations operating in the European Union (EU). Businesses that provide essential or important services must meet the obligations or face regulatory scrutiny.

What Is NIS2?
NIS2 is the EU's updated cybersecurity Directive, expanding on the scope of the original NIS Directive to cover more sectors and introduce even stricter security, risk management, and reporting requirements. If your business provides services in the EU ranging from transportation, banking, healthcare, manufacturing, food production, and more, you are likely required to comply.
The Directive applies to industries including technology, finance, healthcare, energy, and transportation, as well as many digital service providers. Broadly, it requires organizations to implement risk management measures, report significant incidents within 24 hours, and effectively manage third-party risks.
Non-compliance can result in fines of up to €10 million or 2% of global annual turnover, whichever is higher. Compliance impacts not only your regulatory standing but also your contracts, customer trust, and business continuity. Building a compliance strategy early will help avoid last-minute disruptions and potential penalties.
Who Must Comply With NIS2 Requirements?
NIS2 applies to organizations classified as essential or important entities across a variety of sectors. The Directive expands largely on the scope of the original NIS Directive, covering a broader range of industries and lowering the threshold for organizations that must comply.
Essential entities include large organizations in critical sectors where cybersecurity failures could have widespread and serious impacts, such as:
- Energy - Electricity suppliers, gas providers, oil companies, and district heating operators.
- Transport - Airlines, rail operators, shipping companies, and logistics providers.
- Banking - Credit institutions and financial market infrastructure providers.
- Healthcare - Hospitals, clinics, and pharmaceutical manufacturers.
- Drinking Water & Wastewater - Water supply and treatment facilities.
- Digital Infrastructure - Cloud services providers, data center operators, and domain name system (DNS) service providers.
Important entities are medium and large businesses in sectors that are critical but do not require the same level of regulatory scrutiny. These include:
- Manufacturing - Producers of medical devices and electrical equipment.
- Food Production - Businesses that manufacture food and beverages.
- Postal and Courier Services.
- Waste Management Companies.
- Digital Service Providers - Online search engines, marketplaces, and social networking platforms.
- Managed Security Service Providers (MSSPs) - Businesses providing cybersecurity services to other organizations.
It's important to note that both essential and important entities are generally defined as medium or large enterprises, meaning they have at least 50 employees or an annual turnover of €10 million or more. Smaller organizations, however, may still fall under NIS2 if they are critical to a supply chain or if they operate in a high-risk sector.

NIS2 Requirements: What You Need To Plan For
NIS2 entails a range of security and operational requirements, with a particular emphasis on minimizing cybersecurity risks. Below is an explanation of the 5 overarching requirements and what implementing them may look like for your organization.
1. Risk Management & Security Measures
NIS2 requires organizations to take a proactive approach to mitigate cybersecurity risks.
Security measures across areas, including network security, data protection, and system integrity, are required. Here's what this may look like in practice for your organization, particularly if you are a SaaS company:
- Implementing Access Control Measures: Access control measures such as multi-factor authentication (MFA) for all employees and users accessing your platform are required under NIS2. MFA means both a password and app-based token or another second form of verification are needed to log in.
- Enabling Data Encryption Measures: Encrypt sensitive customer data both at rest and in transit. For NIS2, this includes encrypting databases and using TLS (Transport Layer Security) for all data exchanged between clients and your platform.
- Creating A Patch Management Program: Regularly update software and systems to fix vulnerabilities. Additionally, you'll need to implement an automated patching system that ensures no critical updates are missed.
- Conducting Regular Vulnerability Scanning: This requirement entails using automated tools to regularly scan your applications and infrastructure for vulnerabilities. For instance, using tools like Nessus can identify weaknesses.
2. Incident Reporting Obligations
NIS2 mandates relatively quick reporting of cybersecurity incidents in the event they occur. As an example, if you were to experience a breach where an attacker gained access to customer data, you would be required to notify relevant authorities and affected clients within the prescribed timeframe and provide updates on the breach as it is resolved.
In practice, setting up the incident reporting process from beginning to end will likely entail the following for your organization:
- Creating An Incident Response Plan: Internal incident response policies that outline the exact steps to take when a breach occurs, designate a response team, and describe how you will identify the root causes of the breach are required.
- Setting Up Incident Detection Tools: Set up monitoring systems like SIEM (Security Information and Event Management) to detect unusual activity in real-time. Tools like Splunk or Datalog track suspicious logins or data exfiltration are commonly used for this purpose.
- Making A Plan To Follow Compliance with Reporting Deadlines: Lastly, know what your process would be for reporting incidents in a timely fashion to the appropriate authorities and your affected clients.
3. Governance & Accountability
An increasing emphasis on governance is being seen across historically gold standard cybersecurity frameworks such as the NIST Cybersecurity Framework (NIST CSF) with the addition of the NIST governance function. This shift is being seen in recent laws as well, including in the case of NIS2.
In practice, this means that cybersecurity should not be a function of just IT, but a function of corporate governance and should stem from there. Senior management is responsible for making sure that the organization meets NIS2's cybersecurity requirements and that sufficient resources are allocated. Leadership must:
- Appoint Cybersecurity Leadership: Appoint a Chief Information Security Officer (CISO) or designate a cybersecurity lead who will be accountable for ensuring the organization meets NIS2's requirements.
- Ensure Employee Training is Conducted: Employees, particularly those who handle sensitive data, need to be trained in cybersecurity practices and incident reporting procedures. This often takes the form of having mandatory, recurring cybersecurity awareness sessions, phishing training for employees, and/or tabletop exercises.
- Receive Board-Level Reporting: Senior management should regularly receive reports on cybersecurity risks and incidents, and be involved in decision-making processes related to cybersecurity investment. This can take the form of discussing the current cybersecurity posture and resource allocation at quarterly board meetings, for example.
4. Third-Party Risk Management
NIS2 puts the obligation on businesses to manage risks posed by their third-party vendors, especially if those vendors provide business-critical services or have access to sensitive data. A third-party risk management program entails the following elements:
- Vendor Risk Assessments: A vendor risk assessment evaluates the security and compliance practices of third-party providers. This is especially important for vendors that provide services such as cloud hosting, payment processing, or customer support. These vendors and others need to be able to show they meet NIS2's security standards.
- Third-Party Contracts: Contracts with vendors need to define their security obligations (requiring them to comply with certain security standards, report incidents within specific timeframes, and/or undergo audits of their security practices). Your contract for your cloud provider, for example, should outline measures they need to have in place, such as strong access controls and encryption.
- Ongoing Monitoring: Continuously monitoring your vendors. For instance, regularly review their security certifications, check they are staying compliant with relevant laws or frameworks, or conduct periodic assessments.
5. Compliance & Auditing
NIS2 requires maintaining evidence of your cybersecurity practices, with measures such as:
- Internal Audits: Periodic internal audits of security practices to ensure compliance maintenance with NIS2. Internal audits service to verify that measures like encryption and access control are functioning as intended.
- Risk Assessment & Incident Reports Documentation: Keeping up-to-date records of risk assessments, incident reports, and audits helps meet NIS2's governance and accountability requirements.
- External Audits: In some cases, if an organization falls within the essential or important entity categories and is subject to supervisory measures by national authorities, it may be required to undergo an external audit. Some jurisdictions may also require routine external audits for critical infrastructure or high-risk organizations.
NIS2 Requirements: 5 High-Level Requirements

Meeting NIS2's requirements will involve a combination of technical measures, governance practices, and ongoing actions such as continuous monitoring. For organizations like SaaS startups, implementing these requirements ensures you are in compliance with the law and are well-equipped to build a secure platform that protects user data and reduces business risks.
How NIS2 Affects Third-Party Relationships
NIS2 expands security obligations to include third-party vendors and service providers, requiring businesses to manage risks introduced by their supply chain. Practically, this means you must verify that your vendors (including cloud services providers and software vendors) meet security standards and comply with contractual requirements.
With NIS2, due diligence with your vendors' cybersecurity practices is especially important as organizations covered by NIS2 are responsible for security incidents linked to their third parties.
A common way to verify your vendors' security is by requesting to see evidence of their compliance with cybersecurity frameworks and laws relevant to your industry and location. Security questionnaires, audits, and contractual clauses can also be used to clarify your vendors' security practices. However you choose to accomplish this, third-party relationships need to be documented as part of your overall risk management efforts.
Vendor agreements need to set clear security expectations, incident reporting obligations, and liability terms. Due diligence and ongoing monitoring can help identify risks before they lead to regulatory penalties or operational disruptions.

How Do NIS2 Requirements Compare To Other Cybersecurity Regulations In Terms Of Third-Party Risk?
NIS2 places an even stronger emphasis on third-party risk management compared to many other cybersecurity regulations.
Here's how it compares to a few major frameworks:
NIS2 vs. NIS1
The focus on third-party risks is, in fac,t the most substantial change between NIS2 vs. NIS1. NIS1 focused more on internal security measures without expansive supply chain obligations. NIS2, however, expands on the original NIS Directive by explicitly requiring organizations to assess and manage third-party risks.
NIS2 vs. GDPR
GDPR compliance requires third-party risk management in terms of data protection and requires organizations to have contracts with processors handling personal data. NIS2 goes a step further and requires security risk assessments, continuous monitoring, and contractual obligations for security, even for vendors that don't process personal data.
NIS2 vs. ISO 27001
ISO 27001 includes third-party risk management as part of an overall information security management system (ISMS). However, compliance is voluntary. NIS2, meanwhile, mandates risk management practices for third parties and includes enforcement actions for non-compliance.
NIS2 vs. DORA
The Digital Operational Resilience Act (DORA), which applies to financial services organizations, actually has stricter third-party risk requirements than NIS2. DORA requires direct regulatory oversight of critical third-party providers. NIS2 requires strong vendor risk management, but an important distinction is that it does not impose direct regulatory supervision on suppliers.
Where To Start
After you understand whether your organization is in scope and what gaps exist in your current security program, the next step is to develop a compliance plan and begin implementation (see the section above on NIS2 Requirements for what you'll need to plan for).
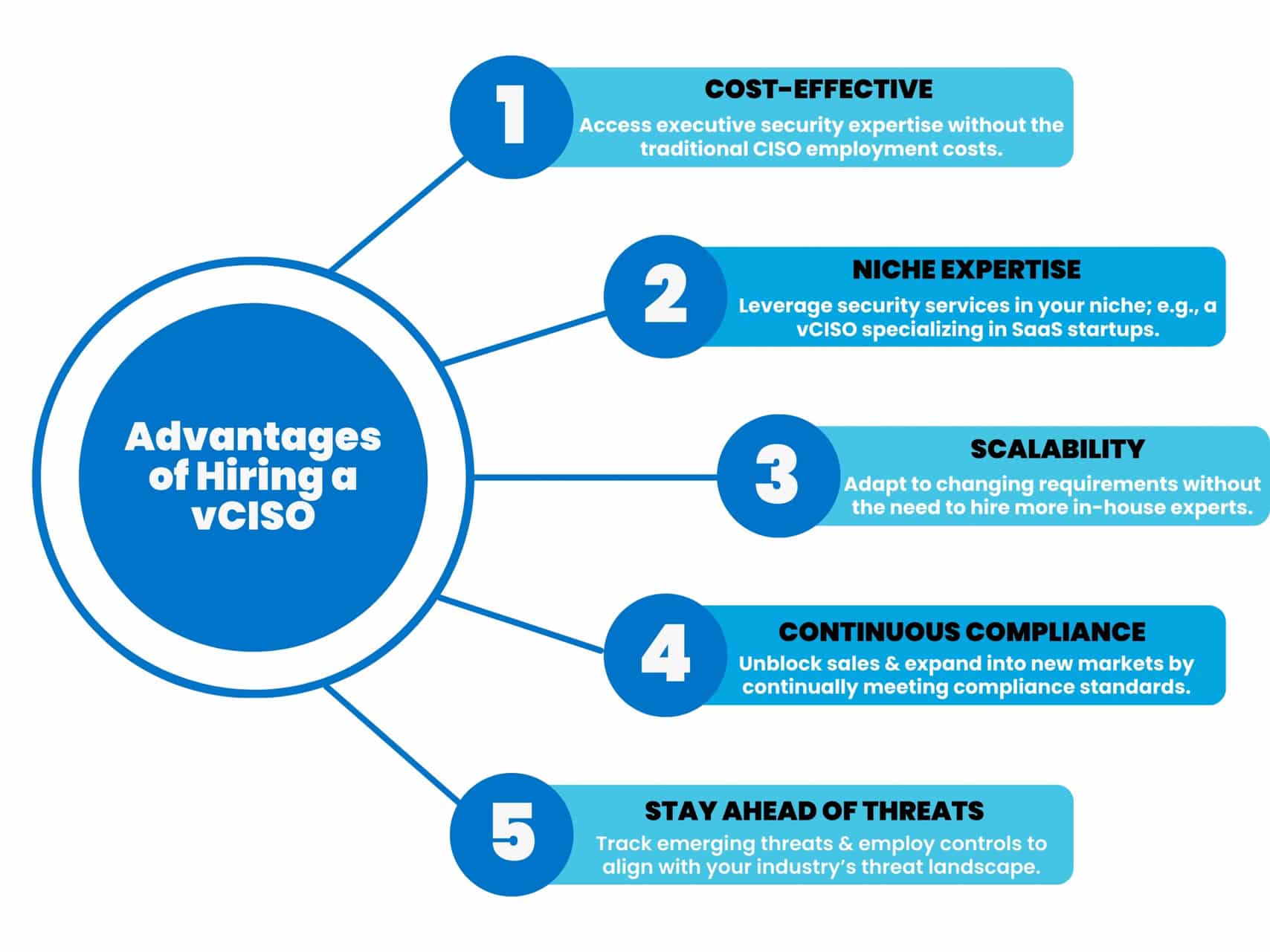
A popular option for many organizations nowadays is to work with a virtual Chief Information Security Officer (vCISO) at this stage. A vCISO helps translate NIS2 requirements into a plan specifically made for your business. They provide the expertise needed to interpret requirements, assess your risks, and build a compliance roadmap, all without incurring the cost of a full-time security executive or having to build out an in-house team.
Compliance automation tools, which automate risk assessments, track your security controls, and generate documentation, can also vastly simplify the process. Our vCISOs at Rhymetec leverage compliance automation tools on behalf of our clients while also completing all of the manual security work needed to meet requirements.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with over 700 companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog.
In this blog, we'll go over frequently asked questions about conducting a cybersecurity tabletop exercise, including how it works, why it's important for startups and SMBs, which voluntary and legal compliance requirements you need one for, and more.
What Is a Cybersecurity Tabletop Exercise?
You're sitting in a meeting with your leadership team, the IT lead, and a couple of personnel from operations. Someone kicks things off by saying, "Alright, here's the situation: You've just received an email from a threat actor claiming they've gained access to our production environment. They've encrypted customer data and are demanding a $50,000 ransom in the 48 hours. What do we do first?".
That's a cybersecurity tabletop exercise in action. A tabletop exercise allows your team to practice handling a cybersecurity incident without the actual crisis. Your team works through a realistic scenario step by step, discussing who's responsible for what and how decisions will be made. During the exercise, gaps in your existing plan and questions you need to answer going forward will likely surface:
Who decides if the ransom should be paid? What happens if legal or PR resources are tied up? Is your team ready to handle questions from customers or regulators?
These are the types of issues that otherwise may not come up unless you are in the middle of a real incident, but a tabletop exercise allows you to address them before they actually happen.

These exercises enable you to see how your team will react when/if you experience a real threat, based on your specific situation: Maybe your team has a strong technical foundation but hasn't worked out all the details for responding to an attack. Or maybe you're growing quickly, and roles like security and IT are spread across multiple people who wear a lot of hats.
Regardless of your situation, tabletop exercises strengthen your security posture by giving you a chance to run through various scenarios, fine-tune how to respond, and stress-test your existing processes.
They also need to be conducted to meet many voluntary and legal requirements. For this reason, they're especially critical for organizations seeking to land bigger clients or meet compliance requirements like SOC 2 or ISO 27001.
Why Do Startups and SMBs Need Tabletop Exercises?
Let's say your startup just landed a major client. Part of the contract includes a requirement to prove you can handle a security incident without putting their data at risk (or, they simply ask to see your SOC 2 report).
You've got your security policies written up, but when it comes to how your team would respond to a real incident, you need to make sure everyone is on the same page and that you have documented proof of your processes.
Enter the tabletop exercise.
Startups and SMBs often operate with lean teams, where people juggle multiple responsibilities. In a crisis, this reality can often cause confusion over who does what and how to make decisions. A cybersecurity tabletop exercise allows you to clarify responsibilities and builds confidence in your ability to respond to incidents.
Besides disrupting your daily business operations and creating downtime, an incident like ransomware or a data breach can harm the trust of your customers and hurt your ability to grow. Knowing how you'll respond greatly reduces that risk and helps minimize the fallout.
Compliance is another factor. Frameworks like SOC 2 require you to put your incident response policies and plan to the test, and tabletop exercises are an easy way to meet that requirement. Tabletop exercises are just as critical for startups and SMBs as they are for large enterprises.
For startups looking to scale, being able to demonstrate that you've done this makes a big difference when building trust with investors, partners, and customers.
Cybersecurity Tabletop Exercises and Compliance: SOC 2 and More
Under the SOC 2 Trust Services Criteria, tabletop exercises meet the incident response testing requirement of the security criteria (which is not amongst the optional criteria under SOC 2!). Criteria CC7.1 and CC7.2 require organizations to test out an incident response plan. Auditors will therefore ask to see evidence that you've actually put your plans to the test and don't simply have them written down as policies.
ISO 27001, often seen as the baseline for global security standards, also calls for incident response testing. Annex A.16.1.5 requires the periodic testing of information security incident response plans. Tabletop exercises are the simplest, most effective, and industry-standard way to satisfy this requirement.
PCI DSS Version 4.0, which applies to organizations that handle payment card data, also includes a specific requirement for incident response testing. Noncompliance with PCI DSS can lead to fines and additional transaction fees. Requirement 12.10.2 states that companies must "test incident response procedures at least annually". Again, tabletop exercises are the most straightforward and widely accepted way to meet this requirement.
For privacy regulations like GDPR and the California Consumer Privacy Act (CCPA), there are various stipulations around the importance of having processes in place to be ready in the event of a security incident.

For instance, GDPR's Article 32 emphasizes the need for "…a process for regularly testing, assessing and evaluating the effectiveness of technical and organisational measures for ensuring the security of the processing." While tabletop exercises aren't explicitly named, CCPA has similar expectations for businesses handling sensitive consumer information.
Putting your response to a security incident into practice through a tabletop exercise allows you to prove to auditors that you can meet these requirements.
Enterprise clients in particular will want reassurance that you can handle incidents without putting their data at risk. Many enterprise contracts (which can be used as either an alternative or an add-on to compliance by some organizations) also include requirements for incident response testing. This can be especially important if your organization handles sensitive data or will be integrating with an enterprise client's systems.
3 Ways MSSPs Support Tabletop Exercises for Organizations
Organizations often choose to work with a Managed Security Services Provider (MSSP) in order to guide them through tabletop exercises. Here are three ways MSSPs offer valuable support through this process while ensuring you meet compliance requirements:
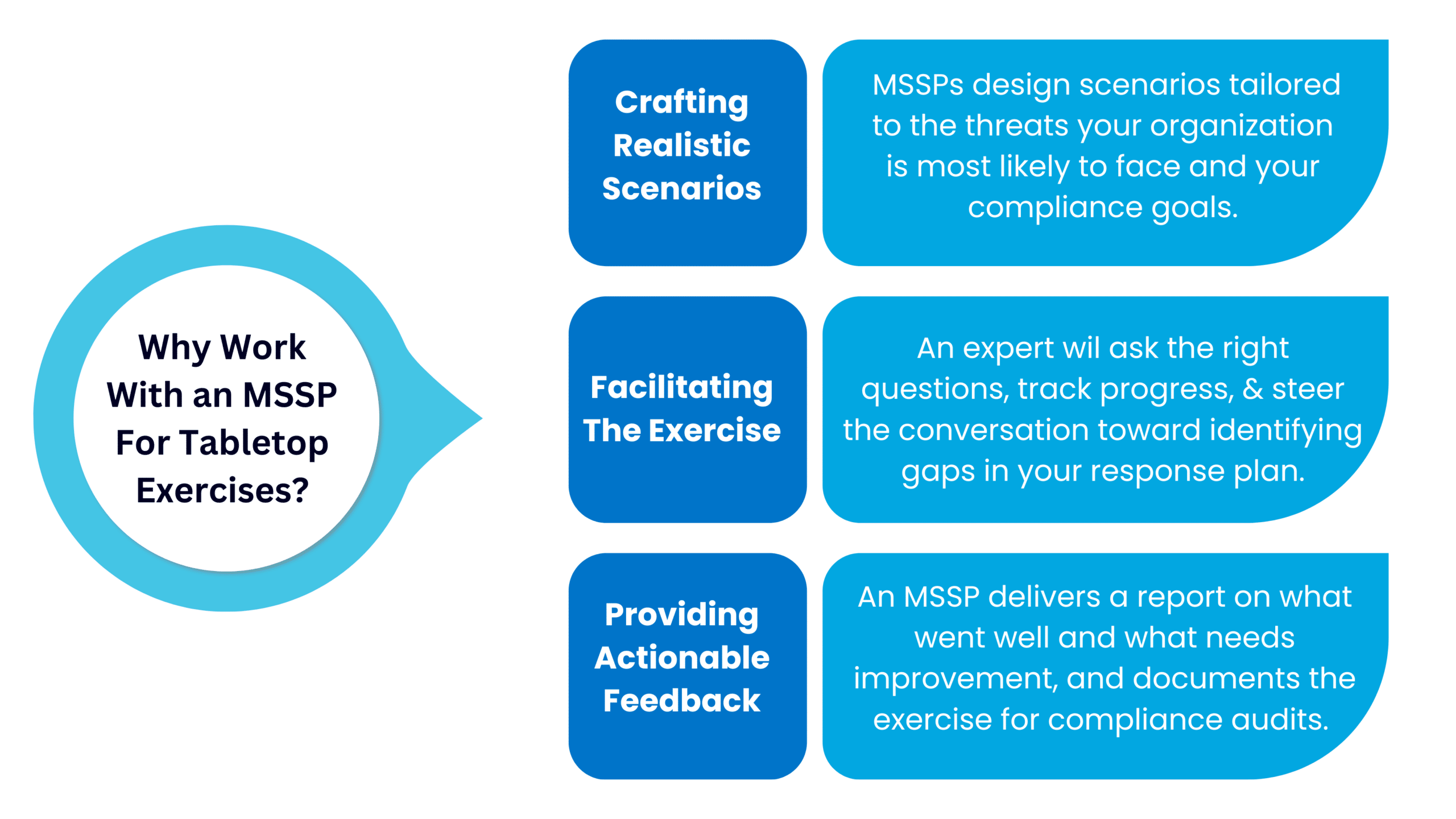
1. Crafting Realistic Scenarios For Your Cybersecurity Tabletop Exercise
Creating a scenario that makes sense for your business is critical. MSSPs can design scenarios tailored to the threats your organization is most likely to face and your compliance goals.
For example, if your company handles customer payment data and you are trying to obtain PCI DSS compliance, the exercise may focus on a ransomware attack targeting your payment processing systems. If you're in SaaS, it could take the form of a simulated compromise of user accounts.
2. Facilitating the Exercise
To conduct tabletop exercises, you need a neutral facilitator to guide the discussion and keep the team on track. A security expert (such as a Virtual CISO, vCISO) at an MSSP can take on this role, asking the right questions, tracking progress, and steering the conversation toward identifying gaps in your response plan.
Working with an outside expert allows your team to engage in the exercise without worrying about having to run it themselves. They bring an outsider's point of view, which can enable you to gain insight into areas your internal team may overlook.
3. Providing Actionable Feedback
After the exercise, an MSSP delivers a report on what went well and what needs improvement. They can help you prioritize updates to your incident response plan and recommend additional security measures based on gaps uncovered during the exercise. They can also document the exercise for compliance audits.
Working with an MSSP provides access to expertise, allows you to strengthen your response capabilities without pulling your internal team away from their day-to-day work, and provides deliverables you can use to demonstrate your security posture to auditors and customers.
Getting Started: Partnering With Experts
Cybersecurity tabletop exercises can be used to meet a vast range of both legal and voluntary requirements, and having conducted them builds trust with your clients and prospects. They provide both the evidence auditors need and the confidence customers expect.
However, startups and smaller organizations may lack the resources or internal expertise needed to effectively run cybersecurity tabletop exercises. An external expert, such as a vCISO, solves this issue and provides specialized knowledge. At Rhymetec, our vCISOs have walked dozens of organizations through their tabletop exercises and provided reports that fulfill compliance requirements.
Check out details on our vCISO services to get started today if you are interested in conducting exercises for your organization.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
About the Author
Metin Kortak has been the Chief Information Security Officer at Rhymetec since 2017. He began his career working in IT security and gained extensive knowledge of compliance and data privacy frameworks such as SOC, ISO 27001, PCI, FEDRAMP, NIST 800-53, GDPR, CCPA, HITRUST and HIPAA. Metin joined Rhymetec to build data privacy and compliance as a service offering. Under his leadership, these offerings have grown to more than 700 customers, and the company is now a leading SaaS security service provider in the industry.
Interested in reading more? Check out more content on our blog.
So, you're a quickly growing startup. One of the last things you want to be thinking about is security and compliance. You want to focus on what really matters - moving your business forward. As a small business ourselves, at Rhymetec, we understand that completely.
But maybe you recently suffered a breach, or maybe a potential client asked you for a security questionnaire, and you realized completing one on the spot was probably not going to cut it.
In any case, you've decided to enter the extremely interesting world of security and compliance for startups. We're going to cover the different types of cybersecurity firms that work with startups, which types of consulting engagements make the most sense for startups, and how to wade through the noise and pick a firm that will act as a partner.
Compliance For Startups: The Maze of Acronyms & Types of Engagements
If you're just getting into looking for a cybersecurity firm that works with startups, be warned in advance - you are going to run into a lot of acronyms. Below are some of the most common acronyms and what they mean:
AV - Anti-virus software that is used on a computer (which is also often referred to as an endpoint because why not complicate everything).
SOC - Security Operations Center, which handles day-to-day alerts aggregated by the SIEM and other systems.
EDR - Endpoint detection and response software that is deployed to an endpoint (since we might as well use a term that acts as both a monitoring tool to detect malicious software and also as a mechanism to contain the device or respond to potential incidents).
SIEM - Security intelligence and event management software that serves as the brain of a security operation, pulling in logs and data from dozens of different systems to act as a single source of truth for a security program.
ISO 27001 - An international standard for information security management systems (ISMS) that provides a framework for managing and securing sensitive information. It focuses on risk management and data protection.
GDPR - Europe's General Data Protection Regulation, enacted in 2016. GDPR requires organizations to safeguard EU consumer data and build governance processes that enable the correct handling of EU citizen data.
SOC 2 - System Organization Controls. A voluntary compliance framework that demonstrates to potential customers that your organization has a security program with standard security controls in place.
HIPAA - The U.S. Health Insurance Portability and Accountability Act. A data privacy law relating to healthcare that also includes a "Security Rule" requiring organizations to take predefined steps to secure patient data.
CISO - The Chief Information Security Officer is the individual responsible for the security of the organization.
vCISO - A virtual Chief Information Security Officer is an outsourced CISO as a service option. This individual (or team) provides strategic security leadership, risk management, and compliance guidance and implementation without the need for a full-time, in-house executive. This option can be ideal for startups and SMBs who may not need to make a full-time hire for this role. vCISO pricing can vary widely depending on the scope of work and level of assistance you need.
MSSP- A Managed Security Services Provider is a company that provides outsourced compliance and security services, such as threat monitoring, incident response, vulnerability management, and more, to protect clients' digital assets.
Some of these terms may be extremely relevant to you, depending on what has sparked your interest in exploring compliance for your startup. Let's take an example:
The Need To Build Security Into The Foundation of Your Business
Imagine your organization has just been the victim of a significant ransomware attack. Many of your sensitive files are now published on a ransomware site, creating enormous disruption to your business.

Many companies that find themselves in this situation panic and immediately engage the first MSSP they can find to help them recover. This is due to the fact that many organizations tend to take a siloed view of information security.
If you are the victim of a breach, you may think you need to work with one firm. If you need compliance, you might think you need to work with a different firm, and you may also think it's only worth seeking out the right firm when there's an issue.
This mindset could not be further from the truth. A good security firm will help with building a program that effectively addresses compliance, governance, technical controls, and incident response in a way that minimizes friction and effectively leverages people, processes, and technology to holistically reduce both the risk of security incidents and the risk of compliance violations.
Choosing the Right Compliance Firm For Your Startup: What Are Common Red Flags To Watch Out For?
Let's start by talking about what to look out for (and be wary of) when evaluating different potential service providers for your organization to work with:
Organizations that promise 100% risk reduction or similar vague and aspirational promises. Unfortunately, we live in a world where 100% security is not possible. These vendors are likely selling snake oil.
Service providers that start by trying to sell you something rather than understanding your needs. Security is a process and needs customization for the end client.
Consultants who have you only speaking to sales without talking directly to the practitioners (like a vCISO) who are doing the work. Good salespeople can be extraordinarily helpful in coordinating engagements but shouldn't take the place of security expertise if you have more technical questions or concerns.
Organizations that plan all communication through email and don't set up regular engagements with you (the customers). Security should be a continuously integrated part of your business. An email a month from your "security team" won't cut it.
Firms that cap hours. MSSPs that set strict hour limits can leave your business vulnerable if issues arise outside of the allotted time. Security needs don't follow a clock, and your provider should be able to respond effectively without arbitrary limitations.
Firms that outsource their services. Some MSSPs may outsource critical functions to third parties, leading to potential inconsistencies in quality and responsiveness. Your security provider should have a clear, direct line of accountability for all services they offer.
Be sure to ask if they outsource any services overseas in particular, and if so, where. Outsourcing overseas can impact a vendor's control and oversight, and certain locations may have different regulations and standards around security.
5 Green Flags To Look For In Firms Providing Security & Compliance Services For Startups
Now, what types of characteristics should you look for in a firm that will help your organization succeed?
Geographically Local Talent
There are incredible security professionals all over the world. However, organizations have dramatically different risk profiles based on their local geography and regulatory environments. A healthcare practice in Italy has an entirely different set of laws and regulations than a medical clinic in New York. Choosing a security provider that has staff and experience in your country helps streamline the process and avoid miscommunication and knowledge gaps that may occur by trying to outsource the work.
Strong Communication
A reputable security services firm should be willing to join a Slack channel with you or establish another near-instant way to communicate directly between security practitioners and corporate staff. Effective communication is absolutely critical to building a great cybersecurity program.
Experience Across Compliance For Startups And Cyber Risk Reduction
Many people view cybersecurity compliance as a tradeoff with risk reduction. You can be compliant, or you can run a "serious" security program focused on reducing risk. This is reductive and untrue. Building an information security program that also reduces risk for an organization should be the goal of every security team.
They Ask Good Questions
What business problem are you trying to solve by working with a firm that specializes in compliance for startups?
This is an important question that all firms should be asking their prospects. When a consultant tries to understand the business problems you are trying to solve, it improves their ability to generate positive outcomes from the engagement.
Transparent Pricing
Security programs are complex, and they can be hard to price. These facts are both true, but that doesn't mean the vendor should put that complexity on you.
Look for a vendor that is willing to provide straightforward, transparent, and honest pricing that makes sense for your organization.
Compliance For Startups: Pricing
So, how do firms price their security offerings? There are a few different methods:
Fixed Price/Project-Based: Using this method, the vendor estimates the work that needs to be done, writes a statement of work (SOW), and quotes a single fixed price for completion of the SOW. This is often the simplest option. In some cases, vendors can split payments into quarterly or monthly.
Flat Monthly Recurring Fee: Many vendors charge a flat monthly recurring fee, particularly for ongoing projects such as compliance maintenance, endpoint detection and response, or security operations center monitoring. This provides simplicity to the end client and avoids surprise billing.
Hourly: Many MSSPs and security consulting vendors charge an hourly rate. While hourly can be valuable in some cases, it can also be quite risky and lead to surprise billing and contractual disagreements.
Check out our blog post on vCISO pricing for more information on standard industry fees for security and compliance for startups.
From here, you should have a good idea of what to look for in a firm specializing in compliance for startups and be ready to start assessing vendors. As you select your MSSP or security consultant, it's important to take the time to thoroughly interview them and pick one that is right for your organization.
Lastly, it's important to work with a firm that stays on top of the latest changes in the regulatory landscape and integrates them into their service offerings. As new regulations like the Digital Operational Resilience Act (DORA) go into effect this year, you need to understand if these requirements impact your business and, if so, partner with a firm that already offers DORA Compliance Services.
If you have more specific questions, please feel free to contact our team:
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- 25 Cybersecurity Memes For 2025: The Ultimate List of Security and Compliance Memes
- Cybersecurity Tabletop Exercise: A Guide For Startups and SMBs
- vCISO Pricing Breakdown: Find The Best Fit For Your Needs
Regular cybersecurity audits are the best way to ensure your business continuously meets security and compliance requirements while reaping the business benefits of investing in security. This post will go over the different types of audits, their benefits for your organization, how to prepare, and common findings to be aware of.
For many fast-growing startups and SMBs, cybersecurity might not feel like a top priority. But with increasingly complex data regulations, rising threats, and growing client expectations, security can no longer be an afterthought, regardless of company size or industry.
The good news is that organizations that invest in improving their security posture and undergo regular cybersecurity audits start to see a wide range of benefits, especially once they have evidence they've successfully completed their audit through a certification or a report:
Barriers are removed in their deal flows, the time spent on filling out onerous security questionnaires is eliminated, and they can get back to what really matters - moving their business forward.
Why Cybersecurity Audits Matter For Your Organization
A cybersecurity audit is a thorough review of an organization's security posture, assessing the adequacy of protections in place to defend against cyber threats and meet regulatory requirements. You can think of an audit as a health check for your security practices, allowing you to identify potential vulnerabilities before they can lead to an actual security incident.
Audit findings provide valuable insight into how secure your organization is and how well you are meeting any relevant requirements. Knowing how well your security practices measure up against industry standards allows you to pinpoint where improvements need to be made, and make only the changes you actually need.
Cybersecurity audits identify vulnerabilities and show where your security measures align with or diverge from relevant frameworks like ISO 27001, SOC 2, and HIPAA. After an audit, as you enact necessary changes to address the audit's findings, you'll reduce the risk of regulatory penalties, reputational damage, and security incidents. Decision-makers can use the results of an audit to prioritize security improvements and guide their compliance efforts.
When clients, investors, regulators, or other stakeholders expect evidence of your security controls, having third-party verification of the strength of your security posture is important. It shows that you've addressed security requirements upfront, creates confidence in your security approach, and helps meet stakeholder expectations.

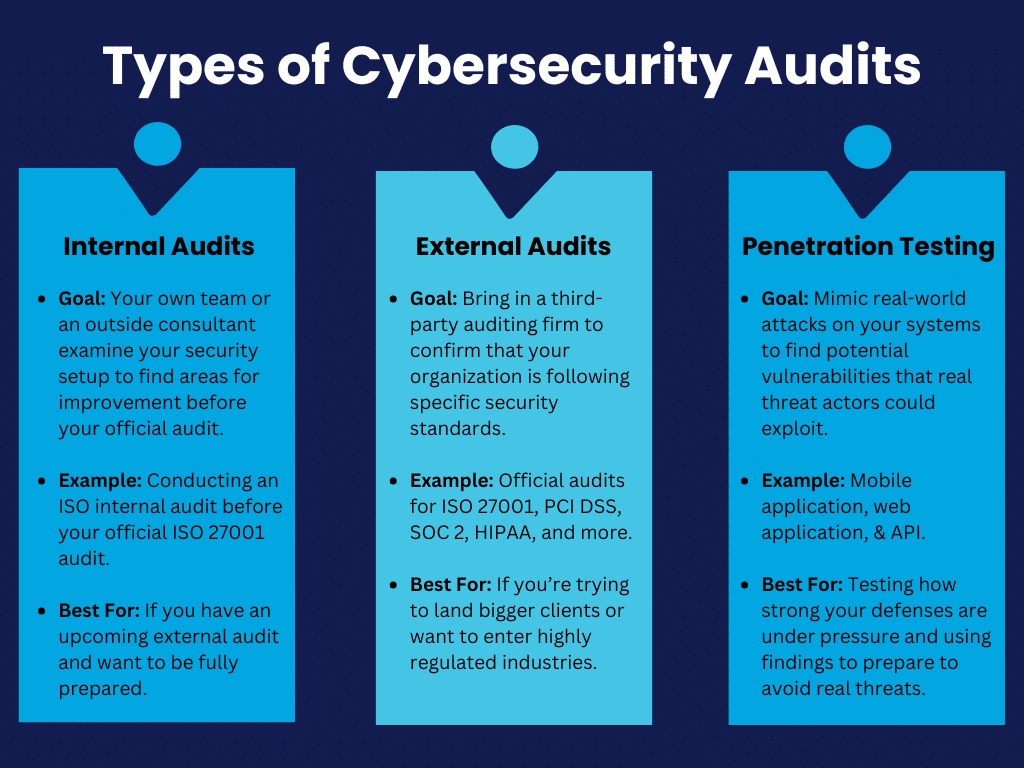
Types of Cybersecurity Audits Every Startup Should Be Aware Of
Startups should know about a few different types of cybersecurity audits:
Internal audits are when your own team or an outside consultant examines your security setup. The goal is to conduct a gap assessment and find any areas for improvement to help better prepare you for future external audits. For example, an ISO internal audit provides a way to spot weaknesses early and adjust them before your official audit for frameworks like ISO 27001 and ISO 42001.
External audits bring in a third-party auditing firm to confirm that your organization is following specific security standards such as ISO 27001, PCI DSS, SOC 2, HIPAA, and more. Passing an external audit is vital if you're trying to land bigger clients or want to enter highly regulated industries.
Penetration testing mimics real-world attacks on your systems to find potential vulnerabilities. Penetration tests give you an idea of how strong your defenses really are under pressure, and the findings help prepare you to avoid real threats:
How to Prepare For a Cybersecurity Audit
To prepare for an audit, the first step is to take a close look at your existing policies and procedures: Are they actually being followed?
It's common for companies to write policies that look great on paper but fall short in practice. You'll want to make sure everyone on your team knows their roles, especially around access controls, data handling, and your organization's incident response policies.
Don't neglect the tech side. Run vulnerability scans, review your logging and monitoring, and make sure your backups are up to date. Auditors will likely examine these areas regardless of which type of audit you undergo. Lastly, keep your documentation extremely organized. Auditors appreciate easily accessible and well-organized documentation. Having it ready can be the difference between a smooth audit and a chaotic scramble.
Bonus Tip: A compliance automation tool can come in extremely handy at this stage, as it allows a single place to upload and keep track of all of your documentation. Your auditor will appreciate being able to easily access everything in one place!
Preparing ahead of time as much as possible puts you in control of the process rather than reacting to questions or findings that may come up. Providers like Rhymetec offer internal audits and gap assessment services that are conducted before your audit, leading to fewer surprises during your official audit.
Common Findings in Cybersecurity Audits (And How To Address Them)
Cybersecurity audits often reveal a few common recurring issues that many startups and SMBs face:
One of the most common findings across a variety of different types of audits is weak access controls. Cybersecurity audits frequently find gaps in access control requirements, meaning that too many people have unnecessary access to sensitive data or systems.
The fix here is straightforward:
- Review who has access to what.
- Limit permissions to those who need it.
- Implement multi-factor authentication to add a last additional layer of security to make it harder for unauthorized users to gain access.
Another issue that often comes up is missing or outdated documentation. Auditors will expect to see things like security policies, incident response plans, and training records. If you can't provide these documents or if they're outdated, that's a red flag.
To address this issue, you should:
- Create clear, up-to-date policies that reflect what's actually happening at your organization.
- Make documentation a regular part of your operations, so you're not scrambling to pull everything together before an audit.
- Consider using compliance automation software to organize all of your documentation for auditors in one place.
Another common area where audits also tend to find vulnerabilities is in systems that haven't been patched or updated.
Leaving old software as is is like leaving your door unlocked. You should be regularly updating and patching systems to close off potential entry points for attackers. Simply setting up automated reminders or systems to handle updates can be extremely helpful.
Third-party risk management is another area that is often overlooked by organizations and comes up in audit findings. For PCI DSS audits, for example, this is one of the most common challenges our experts at Rhymetec see that organizations encounter. For many frameworks, you need to make sure your third-party vendors are also compliant.

Finally, many audits reveal a lack of proper employee training. As noted by our experts in Rhymetec's Cybersecurity Awareness Month Tips, your people are often the first line of defense. If they're not aware of basic security practices or don't follow steps to adhere to them on a daily basis, it's a problem.
Ongoing security awareness training and phishing training for employees help everyone in your company recognize and avoid common vectors of attack like phishing attempts.
If possible, address these common issues ahead of time for a smoother audit process.
Cybersecurity Audits and Penetration Testing
Penetration testing is the best way to understand how well your defenses would stand up to real-world attacks.
While not every audit requires a pen test, it's often necessary for audits tied to specific compliance frameworks like PCI DSS and certain SOC 2 reports. These audits don't just ask if you've set up your security controls - they want tangible proof that your system can actually withstand an attack.
Penetration testing is recommended when you need more than a surface-level review of your security and need to go beyond checking boxes to meet compliance requirements; experts simulate actual cyberattacks to try to break through your defenses. Think of it as having someone attempt to lockpick your door, rather than just checking if your door is locked.
Note: If your organization is preparing for a major compliance audit, working with clients that demand high levels of security, or going through rapid growth, a penetration test is highly recommended!
If you incorporate penetration into your regular security checks, you'll get a clear picture of how well you're protected and will be able to tackle weaknesses before they become costly problems down the line. Getting a test done annually or after major changes to your systems helps you stay ahead of emerging threats.
Rhymetec offers a variety of penetration testing services, including:
- Mobile application penetration testing
- API penetration tests
- Web application penetration testing
- External network penetration tests
Choosing The Right Partner for Your Audit
Not all auditors are created equal, so it's important to select a partner who's not only experienced but also a good fit for your company's size, structure, and industry. You need someone who understands both your industry and the specific compliance requirements you're facing.
Audit Partner Factors To Consider
First, check out their track record. Have they worked with startups or SMBs before? It's one thing to know the rules, but another to understand the unique challenges small to midsized companies and startups face regarding security and compliance.
Ask about their previous clients and whether they've helped similar businesses successfully meet their compliance goals. Request to see case studies from their prior engagements with companies with similar profiles as yours.
Another factor to consider is how hands-on you want your audit partner to be. Some partners take a more hands-on approach by choosing to work with select MSSPs to help you improve your security along the way, while others are more focused on just performing the audit and reporting findings.

Audit Report "Red Flags" To Look Out For
A thorough audit report gives you a roadmap for improving your security with clear steps, while a deficient one can leave you with more questions than answers.
Plus, 69% of organizations report that the quality of compliance reports is extremely important. Your clients and stakeholders will want to see evidence of a thorough, high-quality audit.
So, how do you tell the difference between a thorough audit report and a deficient one?
1. First, look at how the findings are communicated:
A high-quality audit report won't just tell you that there's an issue - it will explain where the problem is, why it matters, and how it could impact your business. Look for specifics, like which systems or processes failed, how attackers could exploit weaknesses, and what steps to take next. If your report is filled with vague statements or broad recommendations without context specific to your organization, that's a sign it's not as thorough as it should be.
2. A high-quality report will also show you how issues across different areas are connected:
If weak access controls, for example, show up in multiple places - whether in your cloud setup, employee accounts, or vendor portals - a good report will explain how these issues are linked. A deficient report might mention them individually without showing the bigger picture.
3. Findings on your documentation is another area where a thorough report stands out from a deficient one:
A high-quality report points out exactly where your policies or training records are lacking and provides actionable steps to fix them. If your report glosses over missing documentation or doesn't dig into whether your policies match actual practices, you're likely looking at a surface-level, boilerplate review rather than a meaningful and tailored audit.
4. Finally, a quality report doesn't simply list issues but will categorize them based on their severity and urgency:
This helps guide you on which areas to focus on first. A deficient report may give you a laundry list of issues but won't help you understand which ones pose the most immediate threat.
In short, a thorough audit report provides clarity, context, and a plan. A deficient one leaves you guessing and unsure of how to proceed and may not hold up under scrutiny from your customers and stakeholders.
How Working With An MSSP Simplifies Cybersecurity Audits
Partnering with a Managed Security Services Provider (MSSP) can take a lot of stress out of cybersecurity audits. An MSSP handles much of the ongoing work for you, so when it's time for your audit, you're not rushing to get everything in order.
With continuous monitoring, regular updates, and fully managed compliance services, an MSSP ensures that your security posture stays audit-ready all year round. For example, if your business needs to meet standards like PCI DSS or ISO 27001, an MSSP can keep your policies and security controls aligned with the latest requirements and make sure you're up-to-date on your recurring audits.
Working with an experienced MSSP is the best way to minimize the risk of non-compliance and saves your internal team from having to devote time to it themselves. When you work with an MSSP, you're essentially outsourcing the complex, technical aspects of security to a team that specializes in it, freeing up your business to focus on growth while staying secure and compliant.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Preparing for your PCI audit isn't a matter of simply "checking the boxes" to meet compliance requirements. Ongoing compliance with PCI DSS builds trust with customers and stakeholders, protects your customers' data, and helps with long-term reputation management.
With recent updates in PCI DSS 4.0, there's been an increased focus on compliance maintenance. This article will help you understand the core principles of PCI DSS, how to apply them to your organization, and how to stay compliant over time.
What Is A PCI Audit and How Does It Work At A High Level?
A PCI audit is an assessment of an organization's compliance with the Payment Card Industry Data Security Standard (PCI DSS), a set of security requirements that protect cardholder data. The auditor reviews your organization's security measures, policies, and technical infrastructure to verify that you meet requirements.
In our recent webinar on Compliance to Confidence: Simplifying PCI Security Standards, Rhymetec CISO Metin Kortak discussed frequently asked questions and concerns around PCI DSS Version 4.0 with Kevin Whalen, Head of PCI at Prescient Security.
"The Version 4 standard has a number of new requirements, but I don't think any of the changes are overly difficult. There are a few that are, but a lot of what the update did was simplify and consolidate some of the requirement language. But there are some new enhancements to it to be aware of," noted Kevin Whalen during our webinar.
One such enhancement is the new focus on ensuring organizations maintain compliance over time. As we have seen with other recent updates to cybersecurity and compliance frameworks like NIST CSF Version 2.0, there is a stronger focus in the updated PCI DSS 4.0 on continuous compliance. This means businesses need to show they maintain compliance on an ongoing basis rather than just at the time of the audit.
The PCI compliance readiness process starts with a gap analysis to identify areas that need remediation. Once gaps are addressed, the formal audit is conducted by a Qualified Security Assessor (QSA). This individual reviews documentation, interviews staff, and tests controls to validate compliance. Following your audit, they will provide a report on the findings and note any corrective actions you need to take.
Core Principles and Requirements Under PCI DSS
There are five core principles under PCI DSS. Each of the following requirements is important from a compliance perspective and will also vastly improve your security if you did not have them in place previously.
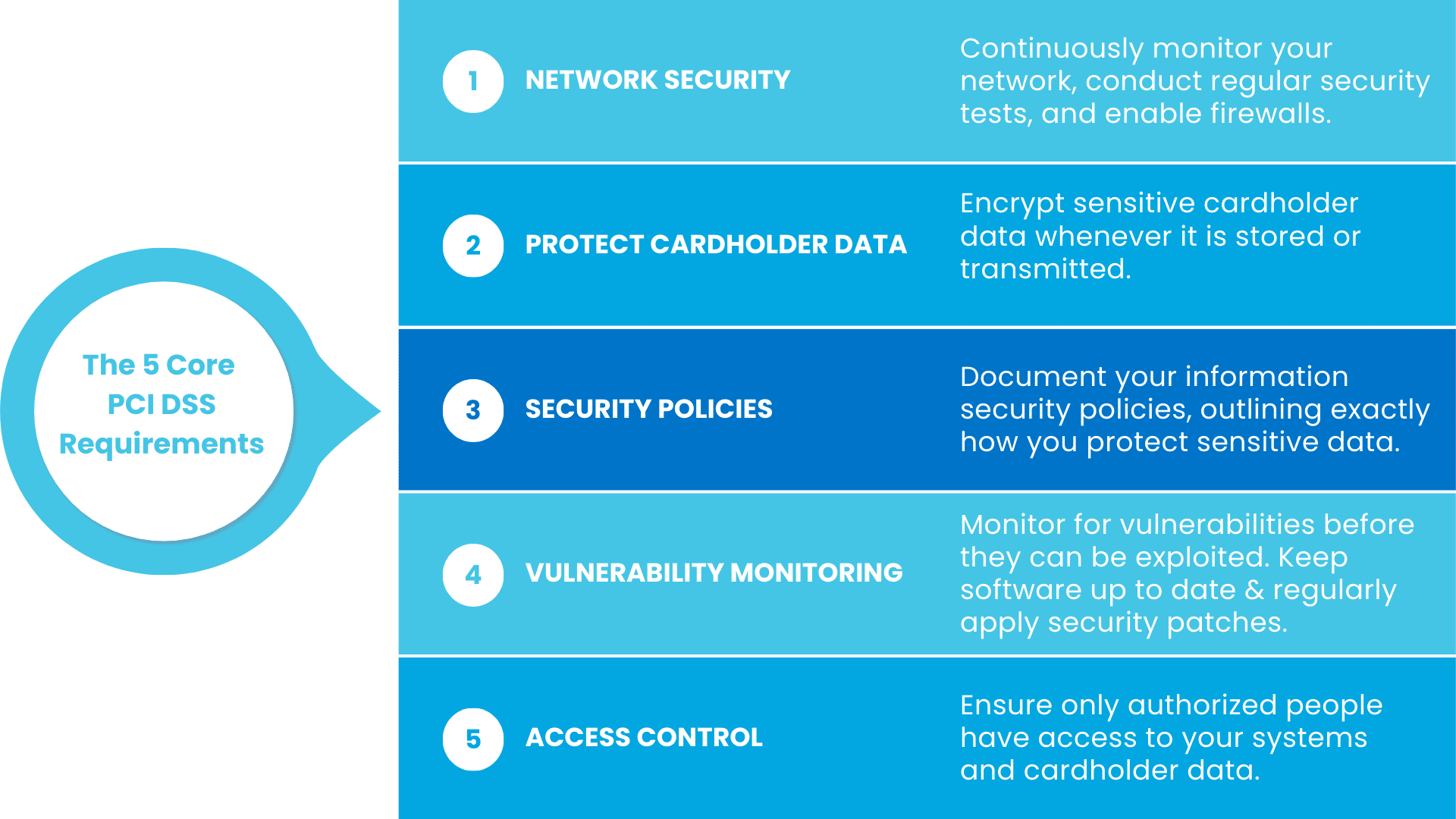
Let's go over each principle in more detail, and explain how they help prevent breaches and keep your customers' data safe:
1. Securing and Monitoring Your Network
PCI DSS requires that you set your network up with security top-of-mind.
This includes measures like firewalls to block unauthorized traffic and making sure your systems are configured securely. You also should set up ways to constantly monitor your network for suspicious activity and conduct regular security tests.
Let's say you run a SaaS platform offering payment processing for small retailers:
If your network isn't secured properly, it's easier for hackers to intercept cardholder data during transactions. By setting up proper firewall measures, you can block unwanted traffic and limit access to only those who really need it.
Regular network monitoring, meanwhile, will alert you to unusual activity, such as an unexpected increase in traffic to your payment systems. Lastly, ASV scans for PCI, vulnerability scans, and penetration tests can help identify weak points and enable you to fix them before they can be exploited.
2. Protecting Cardholder Data
Under PCI DSS, you must encrypt sensitive cardholder data whenever it's stored or transmitted. Encryption makes the data unreadable to anyone without the decryption key, so even if it's intercepted, it's useless to bad actors.
As an example, if a platform offers subscription services and stores credit card information for recurring payments, under PCI DSS they must have encryption enabled to prevent hackers from being able to steal readable credit card data. This is a particularly important measure if your business deals with large volumes of recurring transactions where cardholder data may be stored for longer periods of time.
3. Updating Security Policies For Your PCI Audit
Under PCI DSS, organizations must have a set of documented information security policies. Your policies should outline precisely how you protect sensitive data, and how different members of your teams play a role in this.
For example, your policies may require that all developers at your company use secure coding practices, or that support staff avoid accessing customer payment data directly.
*Note: Having strong security policies in place is critical regardless of organization size, but small businesses or those without designated security members on staff often struggle to set up clear and usable policies. Check out our blog on crafting security policies for small businesses for guidance on how to not only write, but how to effectively communicate your security policies so they are followed by employees.

4. Vulnerability Monitoring
Vulnerability monitoring entails common sense security measures like keeping antivirus software up to date and regularly applying security patches to your systems. The idea is to address security vulnerabilities before they can be exploited.
If a known vulnerability exists in one of the software components your project management tool relies on to work, for example, threat actors could use that to access your customers' data. Continuously monitoring for potential vulnerabilities and having a plan to address them is critical not only for your PCI audit but also from a baseline security perspective.
5. Access Control
Access control measures need to be implemented to ensure only the right people can get into your systems and access sensitive cardholder data. Baseline security measures that all organizations should ideally be doing, like multi-factor authentication (MFA), also help with access control.
You never want everyone internally to have full access to cardholder data. By limiting access to only the employees who absolutely need it - and by also adding MFA to verify their identity - you reduce the risk of unauthorized access enormously.
Why Is PCI DSS Compliance Important For Your Business?
Businesses that handle cardholder data are required to obtain PCI DSS compliance. Non-compliance can result in fines, legal penalties, and damage to your organization's reputation. Breaches can lead to financial losses, erode customer trust, and cause disruptions to your business operations.
Compliance also reduces the risk of fraud and theft of payment data, which can result in financial harm to both your business and your customers. With the introduction of PCI DSS 4.0, businesses are expected to demonstrate continuous compliance and show that they are taking a proactive approach to managing security risks.
Types of PCI DSS Audits and Their Scope
The type of PCI audit your business requires depends on your merchant level and the volume of transactions you process annually. Each audit type covers all of the requirements in the PCI DSS standard, but may vary in depth based on the size of your business and the sensitivity of the cardholder data you process:
Self-Assessment Questionnaire (SAQ)
This is a self-evaluation tool used by smaller businesses that don't handle large volumes of cardholder data. The SAQ is basically a checklist where you answer a series of questions about your security practices, and is broken down into different versions depending on how you process payments. There are specific versions for businesses that process payments online, through a physical point-of-sale system, or over the phone.
As an example, if you run a SaaS business that provides a billing platform for freelancers, and you rely on a third-party payment processor like Stripe to handle the actual transactions, you wouldn't be storing or processing cardholder data directly. Therefore, you'd likely fall under the SAQ version that applies to businesses that outsource their payment processing, and it would serve to validate that your company never stores or has access to that data.
Report on Compliance (RoC)
For larger organizations or those processing a large volume of transactions, a PCI audit conducted by a Qualified Security Assessor (QSA) is required.
This audit is more extensive and includes on-site assessments of your security controls, and is generally required for larger businesses or those processing a significant number of transactions. If your company processes more than 6 million transactions per year, you'll likely need an RoC.
5 Steps To Prepare For Your PCI Audit
At a high level, the following 5 steps illustrate the process leading up to your PCI DSS audit.
At any one of these steps, it can be helpful to consult an outside expert, such as a Managed Security Services Provider (MSSP), with ample prior experience helping organizations achieve PCI DSS compliance.
1. Understand your scope.
Mapping out the scope of your audit is the first step. You'll need to determine which of your systems, networks, and processes handle cardholder data. Merchants have to request additional information from customers under certain circumstances:
"When we start our scoping process, what we usually try to understand in the beginning is how the payments are being processed…Where it gets complex is when the physical card is not present when you're making a purchase. Because the physical card is not present, PCI has certain requirements in place so that when you make a purchase online, for example, you have to provide some additional information like your billing address," said Rhymetec CISO Metin Kortak on this topic during our webinar.
You also need to define your Cardholder Data Environment (CDE).
"What that means is we need to understand exactly where the card information is being processed. Is it only processed by the customer's hosting provider? Or does the card information also reside in other third-party applications or physical servers? It's important to understand the entire scope so that when we go through an audit, we can give them the proper scope and make sure that the PCI security controls are implemented on all of those hosting providers and other vendors," said Metin.
2. Conduct a gap analysis leading up to your official PCI audit.
Perform an internal assessment to pinpoint areas where your organization does not meet PCI DSS audit requirements. This is important to do before your formal audit, as it will give you a chance to address any deficiencies beforehand. MSSPs that are experienced in compliance and offer one-off gap assessment services can be a great resource during this step.
3. Remediate any identified gaps.
Next, address any gaps found during your internal assessment. Common security measures that may need to be addressed at this stage include updating your firewalls, strengthening encryption protocols, or further formalizing your access controls.
4. Update your documentation.
Prior to your audit, make sure all of your policies and security measures are well-documented in a format that will make it easy for your auditor to keep track of. Using a compliance automation tool can be extremely helpful with this, as they provide a single, easily accessible place to upload all of your documentation for your auditors to see.
5. Perform ongoing monitoring for your next PCI audit.
This element is one of the heaviest lifts of the current version of PCI DSS.
Compliance maintenance under PCI DSS 4.0 is expected, and ongoing monitoring will help you stay compliant throughout the year. You should be regularly monitoring security systems and processes to detect any potential misconfigurations or vulnerabilities. This includes automated monitoring of various controls, such as payment page script security:
"The most significant change of 4.0 is the payment page script security, where they've added some new requirements in the software development controls as well as automated security controls around monitoring for changes to the construction of your pages that contain input fields for cardholder data." - Kevin Whalen, Prescient Security
Common Challenges and What To Do
Some common challenges businesses face when preparing for PCI DSS audits include:
Defining the Scope of Your PCI Audit
Many businesses struggle with understanding the full scope of systems that must be in compliance with requirements under PCI DSS. To address this, perform an inventory of systems handling cardholder data. As an example, you will have more strict requirements that apply to your scope if you take payments over the phone instead of in person.
"Depending on how the payments are being processed, how the credit card information is being collected by the buyers - that impacts the level of work that we're going to do for our customer," Metin Kortak, Rhymetec
Maintaining Compliance Over Time After Your PCI Audit
Maintaining an effective compliance maintenance program that scales with your business can be a challenge. Using automated monitoring and logging tools to track compliance in real-time can be helpful, as can working with an outside expert like a Managed Security Services Provider with specific expertise in enabling organizations to stay compliant over time.
Documentation
Many organizations lack adequate documentation of their security policies and controls.
You need this documentation not only for compliance purposes but also as a common-sense security measure: All of your employees should be aware of your security policies and procedures, such as your policy on measures like multi-factor authentication (MFA).
Bonus Tip: For your PCI DSS audit, a compliance automation platform can be incredilby helpful with documentation. Compliance automation tools provide a single location with all of your documentation clearly laid out, so that you and your auditors can easily access and keep track of it.
Third-Party Risk
Third-party risk management plays an important role in PCI compliance. If you're using a third party to process or store credit card information, you generally need to obtain that company's own attestation or certification document to include in your own PCI audit.
"Collecting your third parties' PCI certifications is important, especially if the vendor is processing or transmitting credit card information. Aside from that, you still need to conduct vendor assessments on all of your vendors. And that needs to go beyond just collecting the PCI certifications. That might mean checking that those vendors have proper information security policies in place, if they have conducted their own business continuity tabletop exercises, if they conduct access reviews…Just really conducting a thorough due diligence." - Metin Kortak, Rhymetec
In sum, you need to make sure your third-party vendors that process or store your cardholder data in any way are also PCI DSS compliant.

Post PCI Audit Action Items: How To Stay Compliant
After your audit, there are several steps to help maintain compliance:
Address audit findings.
The first step post-audit is to thoroughly review the auditor's report and remediate any identified deficiencies as needed.
Be sure you've implemented continuous monitoring measures.
Set up monitoring systems to track your compliance with key PCI DSS controls discussed previously, including encryption, access management, and vulnerability scanning. As noted above, a compliance automation tool can be incredibly helpful with this.
Update your policies as needed.
It can help to schedule regular intervals to review your security policies going forward. This will enable you to change your policies as needed to reflect any changes in your organization's operations, your risk profile, or the PCI DSS standard.
Have regular internal audits.
Schedule periodic reviews to assess your compliance posture between your annual PCI DSS audits.
Vendor management.
Lastly, remaining in compliance with PCI DSS requires ongoing monitoring of your third-party vendors to confirm their continued compliance, especially if they are involved in how you handle cardholder data.
In Conclusion
Although it may seem daunting to prepare for your PCI audit, by following the steps outlined in this article, you can feel confident that you are well prepared for your audit and that your customers' data is protected.
PCI DSS compliance is not just a one-time effort - compliance requires ongoing attention, especially with the updates introduced in PCI DSS 4.0. After your PCI audit, be sure to continue monitoring your network, confirming third-party due diligence, and updating your policies as needed. Staying proactive will help your business stay secure, remain in compliance, and build long-term trust with your customers and stakeholders.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We’ve worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business. Contact us today to get started.
Interested in reading more? Check out more content on our blog:
- Generative AI Security Risks For Businesses: Practical Advice For The Concerned
- vCISO Pricing Breakdown: Find The Best Fit For Your Needs
- Cybersecurity for SMBs: 10 Key Measures and Statistics
This article goes over vCISO pricing models and services, how to choose the right option for your business, and how to make sure you receive the guidance and services you need without unnecessary expenditure.
For startups and SMBs, cybersecurity and regulatory compliance are challenges that demand expert attention. However, many organizations either lack the resources or don't need to hire a full-time Chief Information Security Officer (CISO) to meet their needs. A Virtual CISO (vCISO) offers a practical alternative, delivering high-level security leadership on a flexible, cost-effective basis.
Today, vCISO services are used not only by startups but also by enterprises that need executive-level security leadership without the full-time salary overhead. By partnering with an MSSP like Rhymetec, organizations of all sizes gain access to compliance expertise across SOC 2, ISO 27001, HIPAA, GDPR, and CMMC, plus global regulations like NIS2 and GDPR for European expansion.
vCISO Pricing Structures
Let's go over the three main vCISO pricing structures and their average costs right off the bat:
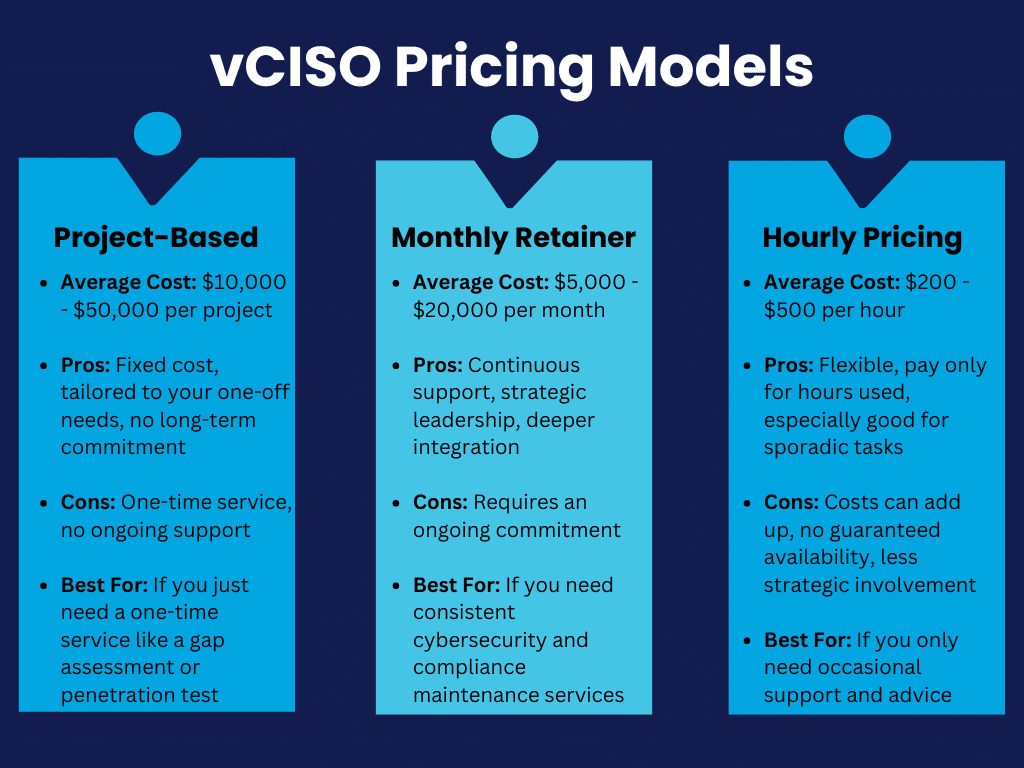
Project-Based Pricing
Businesses often select this option if they need one-time tasks like security audits, risk assessments, or gap assessments. As you can probably imagine, the cost varies widely depending on the specific project.
As an estimate, project-based vCISO pricing ranges from $10,000 (for services like gap & risk assessments) - to $50,000 (prices can go up this high for things like penetration testing and compliance certifications).
This option is best for companies tackling immediate needs, such as preparing for a SOC 2 or HIPAA readiness assessment, or validating new cloud infrastructure security controls.
Hourly vCISO Pricing
Hourly vCISO pricing typically falls between $200 - $500 per hour. This option may be suitable for companies that need occasional expert input or are looking to address specific tasks without a long-term contract.
However, a major con of hourly pricing is that your hours may be capped on a weekly or monthly basis. This means that if you need extra support if something comes up, you may not be able to receive it on demand.
For example, Rhymetec’s Executive Tier provides what is essentially a full-time vCISO, fully integrated into your systems, offering audit preparation, vendor management, and direct collaboration with trusted auditors and partners such as A-LIGN.
Monthly Retainers
Monthly retainer fees typically range from $5,000 - $20,000 per month, depending on the level of service and the vCISO's involvement.
This pricing model allows you to have continuous access to a vCISO, offering the most comprehensive support. This benefits businesses that need ongoing direction and hands-on management of their infosec programs.
What Does The vCISO Role Entail?
A Virtual Chief Information Security Officer (vCISO) is a seasoned cybersecurity professional who provides the strategic leadership and services of a traditional CISO, but operates remotely and often on a part-time basis.
vCISOs work with businesses to develop and manage their security programs, maintain overall good security hygiene, and protect the company's data and systems. This role is particularly appealing to startups and SMBs that need expert guidance and support but without the full-time commitment or cost of an in-house CISO.
vCISOs assist with a wide range of services, including risk management, compliance with regulatory standards, incident response, and security policy development. Some Managed Security Services Providers (MSSPs), such as Rhymetec, offer comprehensive vCISO services that provide an elegant solution for businesses aiming to improve their security posture without the overhead of a full-time CISO.
In practice, a vCISO helps organizations evaluate risk, implement security frameworks, maintain audit readiness, and navigate changing regulatory environments. They often work hand-in-hand with compliance automation platforms for evidence collection and reporting, setting them up and leveraging them on your behalf.
What Are The Advantages of a vCISO vs. In-House Security?
For SMBs and startups, the choice between a vCISO and an in-house security team often comes down to three main considerations:
- Cost
- Expertise
- Flexibility
Hiring a full-time CISO can be prohibitively expensive, with salaries often exceeding six figures. Not to mention, there are the additional costs of benefits, training, and other resources required to support the role.
A vCISO, on the other hand, offers the expertise of a seasoned CISO at a fraction of the cost, often working part-time or on a retainer basis. vCISOs bring a breadth of experience from working with multiple clients across various industries, which can be particularly beneficial for smaller companies that may not have the resources to stay on top of the latest threats and regulatory changes.
For instance, Rhymetec's Executive Tier vCISO Service provides not just a dedicated vCISO, but also full integration with the client's systems, providing a level of support that rivals that of an in-house team. This allow startups and scaling enterprises to achieve enterprise-grade security without building costly in-house departments.
Factors Impacting vCISO Pricing
vCISO pricing can vary substantially depending on the scope of services, the requirements specific to your location and industry, and the complexity of your existing infrastructure. The broader the scope of services - such as adding compliance frameworks or expanding to full-time support - the higher the cost.
For example, Rhymetec's pricing structure adjusts based on the level of service required. Our Mentor Tier starts at $2,500 per month, which covers essential advisory services and assistance in maximizing your use of a compliance automation platform.
However, if a client needs additional services, such as manual security services to meet requirements under a framework like SOC 2 or align with new NIST governance requirements, the monthly fee increases by a minimum of $500. Companies in highly regulated industries may face higher costs due to the need for specialized expertise and more comprehensive services.
For instance, a vCISO can act as a CMMC consultant and help defense contractors navigate the requirements by determining which certification level applies to them and how to reach compliance efficiently. Many organizations begin by reviewing a CMMC Level 1 Checklist, but a vCISO builds on that by mapping the right controls and managing implementation. They help also clarify higher-level common doubts such as when CMMC versus FedRAMP is the right framework to pursue, since both can impact federal contracts.
Pricing Models for vCISO Services
As discussed previously at a high level, there are several common pricing models for vCISO services:
The most straightforward and popular option is a flat monthly fee. Businesses often find that this option allows them to budget more effectively and provides predictability. This model is often tiered, with different levels of service available depending on the company's needs.
Rhymetec, for instance, offers three tiers of service on a monthly basis: Mentor, Manager, and Executive. The Mentor Tier is ideal for startups and SMBs needing strategic guidance, while the Manager Tier adds more hands-on management of security and compliance.
The Executive Tier, with custom scoping, offers the equivalent of a full-time vCISO, including advanced services like penetration testing and vendor risk management:

Another model is an hourly-based arrangement, where the vCISO is available for a set number of hours per month. This model offers flexibility but can lead to variable costs depending on how much time is used.
Some providers also offer project-based vCISO pricing for specific initiatives, such as phishing training for employees, a security audit, gap assessments, penetration testing, or compliance certification.
vCISO Pricing Compared To In-House Options
Taking a look at the differences in vCISO pricing and in-house options reveals substantial cost savings:
The average salary for a full-time CISO can exceed $200,000 per year, not including bonuses, benefits, and investing in necessary resources. Companies often need to invest in ongoing training and potentially expand their IT team to support the CISO's initiatives.
In contrast, a vCISO from Rhymetec's Mentor Tier, as an example, costs a total average of $30,000 per year, with options to scale services as needed. Even the top-tier Executive service, which provides comprehensive, full-time support, is more cost-effective than hiring an in-house CISO, particularly when considering the added value of expert-level services that might otherwise require multiple hires!
Consider the average cost of the following positions:
Job Title (Salary range for an in-house full-time hire in 2024):
- CISO ($215,000 – $275,000 per year)
- Cloud Security Specialist ($110,000 – $150,000 per year)
- Application Security Specialist ($130,000 – $180,000 per year)
- Penetration Tester ($110,000 – $150,000 per year)
- Security Operations Analyst ($110,000 – $160,000 per year)
- Threat Intelligence Analyst ($80,000 – $140,000 per year)
- Governance, Risk and Compliance Specialist ($65,000 – $100,000 per year)
- Vulnerability Management Analyst ($100,000 – $165,000 per year)
SMBs and startups need the same level of expertise but not necessarily the same amount of work as large enterprises that spend millions of dollars on a security team with many highly specialized individuals.
Small businesses need the same level of experience but not necessarily the same amount of work. Many organizations choose to work with a Managed Security Services Provider with vCISO support precisely for this reason, as they fill this gap perfectly. At Rhymetec, our vCISO pricing model centralizes all of these skillsets under a single engagement, giving SMBs access to the same expertise as large enterprises without the payroll overhead.
vCISO Pricing & Scope of Work
When considering working with a vCISO, understanding the scope of work and exactly what will be delivered is crucial.
A typical vCISO proposal will outline the specific services offered, the frequency of engagements (such as weekly meetings or monthly reports), and the expected outcomes. Rhymetec's Mentor Tier includes weekly virtual meetings, gap assessments, and policy development, while the Manager and Executive Tiers expand the scope to include incident management, vendor management, and even penetration testing upon request.
The proposal will also detail if and how the vCISO will integrate with your existing team. In Rhymetec's Executive Tier, this includes not just virtual support but also on-site meetings and close collaboration with the client's internal IT team. This helps align your tailored vCISO services with your business objectives and cybersecurity needs.
Case Studies: SMBs and Startups Leveraging vCISOs
In our experience with clients, particularly with B2B startups, the vCISO program enables companies to meet their security and compliance goals in a much shorter timeframe than other options would have allowed for:
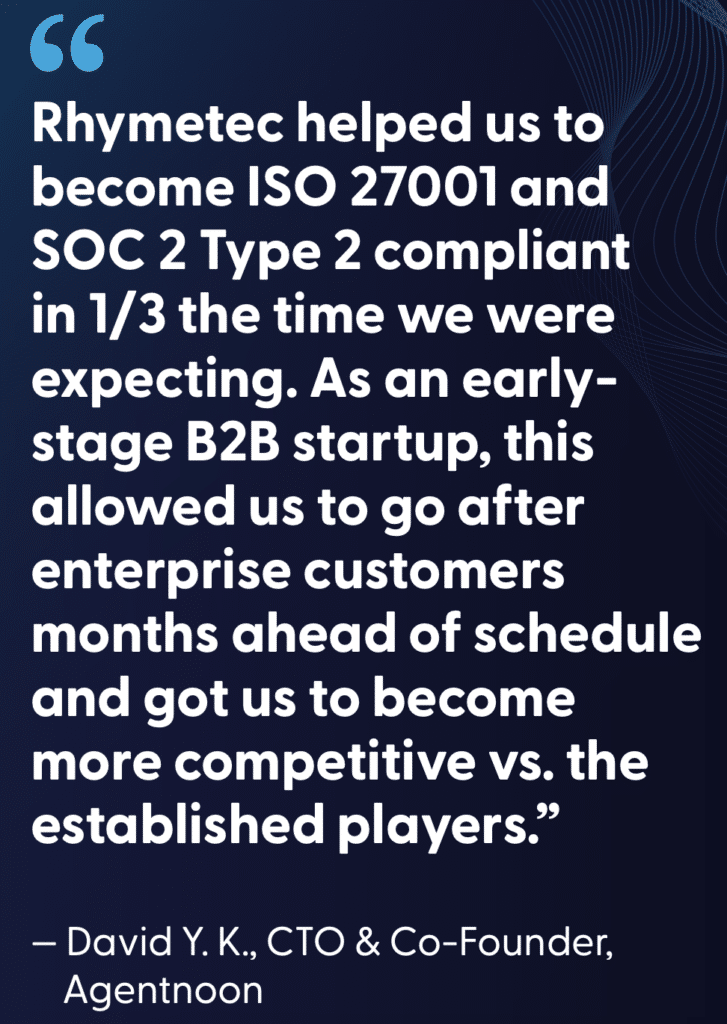
In our cybersecurity case studies, we've found that the vCISO pricing model and services provide several key advantages for companies. First and foremost, when working with a vCISO, specifically through an MSSP, it allows access to a vast set of skills:
"You can rely on a single individual, or you can have the benefit of a whole team of deep expertise and process knowledge. It's a small investment when you're considering in-house resources versus an entire team available on call at a fractional need – the ROI is really compelling."
– Harry Karamitopoulos, President, Modicum
Customers leveraging a vCISO program also find that it enables them to stay on track with their security and compliance goals, while being able to move their business forward and eliminating the need to build out expensive in-house teams:
"It kind of is like my 'security blanket.' I am a team of one for security and I need support. Having the Rhymetec team to lean on, help me consider options, weigh the pros and cons for different assets around security, and have someone else to bounce ideas off of has been helpful. Also, helping me stay on track and act as a copilot to help manage and navigate those decisions are all things that are essential to me. Without it, I would have to go out and hire more people, and the vCISO essentially cuts out the workforce I would need to hire full-time."
– Rolland Miller, Vice President of Security and Compliance, Orum
Lastly, we often hear from clients that working with their vCISO provides the level of experience and knowledge they need to meet their goals, and their vCISO's established relationships with auditors and compliance automation companies are a critical resource during the audit process:
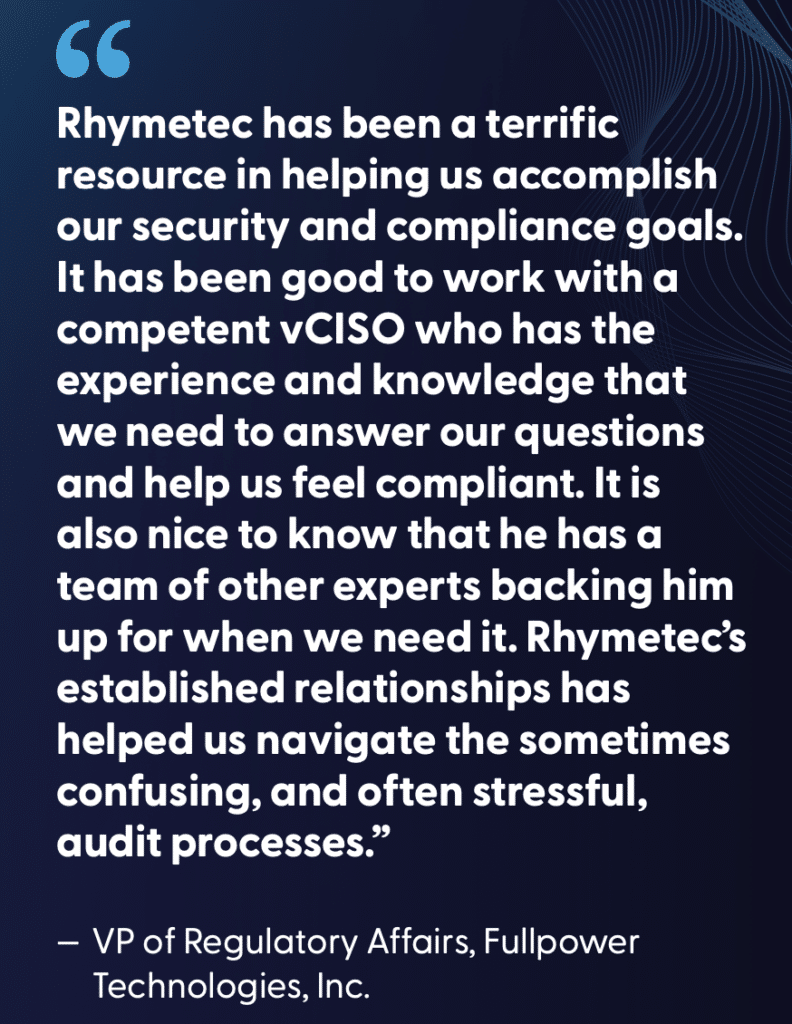
Maximize The Value of Your vCISO Investment
To get the most value from a vCISO, businesses should do the following:
- Make sure your objectives from working with a vCISO are clearly defined
- Communicate regularly with your vCISO
- Establish metrics for success and periodic reviews of your security posture as it evolves
Rhymetec's vCISO services are designed with flexibility in mind, allowing businesses to begin with basic services and scale up as their needs grow. For example, a startup might begin with the Mentor Tier to establish a security foundation and achieve security advisement, then transition to the Manager or Executive Tier as their operations and the marketplaces they sell to expand. This not only helps manage costs but also ensures that the vCISO's services evolve in tandem with the business.
An effective engagement with a vCISO enables you to vastly improve your company's overall security posture over time, and serves as a business enabler as you break into new marketplaces and grow your business.
At Rhymetec, we act as both strategic advisors and hands-on operators, making advanced security and compliance attainable for companies of any size through our vCISO pricing options.
Concluding Thoughts: A Model for vCISO Pricing & Services With Busy Technology Executives Top of Mind
Whether you're looking to start out with basic advisory services or invest in full-time support, the right vCISO can provide the expertise required to protect your business and take security off your plate so you can focus on what really matters - your business.
Rhymetec's vCISO pricing tiers and vCISO services were created with busy technology executives and their workflows in mind. Our goal is to help you shorten your timelines, reduce your team's level of effort, and successfully guide your company through all of your cybersecurity and compliance needs so you can continue to move your business forward. Contact us today to learn more:
FAQs - vCISO Pricing & Services
What is a vCISO and how is it different from a full-time CISO?
A vCISO provides the same strategic leadership as a Chief Information Security Officer but works on a part-time or flexible basis. This makes it far more cost-effective while still delivering deep expertise.
How much does a vCISO cost?
Costs vary depending on scope and pricing model. Project-based engagements can range from $10K–$50K, hourly rates run $200–$500, and monthly retainers average $5K–$20K. Rhymetec offers tiered services beginning at $2,500/month.
Why would a company choose a vCISO over hiring in-house?
Hiring in-house requires salaries exceeding $200K annually plus benefits. A vCISO gives access to equivalent expertise at a fraction of the cost, with the flexibility to scale services as needed.
Can a vCISO help with compliance certifications?
Yes. vCISOs often lead compliance readiness efforts for SOC 2, ISO 27001, HIPAA, GDPR, CMMC, and other frameworks. They manage everything from gap assessments to evidence collection to audit prep.
Do vCISOs work with partners or tools?
Many vCISOs, including Rhymetec’s team, collaborate with audit partners like A-LIGN and leverage compliance automation platforms such as Drata and Anecdotes to streamline readiness.
What industries benefit most from vCISO services?
Startups, SaaS companies, healthcare, fintech, and government contractors all benefit. Any organization that needs to prove compliance to customers, investors, or regulators can use a vCISO to reduce cost and complexity.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with thousands of organizations to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business.
Interested in reading more? Check out more content on our blog:
- Managed Compliance: An Updated Approach For The Cyber Regulatory World
- Why Managed Security Services? In-House vs External Security
- AI Frameworks: What They Are & Why We Need Them
When evaluating vendors to build and audit your information security (infosec) program, there are many important questions to ask: Who exactly will be handling your data? What are the team's credentials and prior experience? Will the vendor be outsourcing services internationally, and if so, how will their control and oversight of the process be impacted?
Is the vendor claiming to be able to both build your infosec program AND conduct your official audit?
Some MSSPs and "compliance as a service" providers are now advertising that they can help organizations meet required controls and conduct their certification audit. In this article, we'll go over the potential issues with this from a legal, reputational, and ethical perspective.
Let's be clear about a few of the potential pitfalls of this approach right off the bat:
Potential Pitfalls Of Engaging "All In One" Vendors
Having the same entity create and assess your infosec controls introduces a blatant conflict of interest. This presents clear ethical issues, as it's essentially like having a restaurant conduct its own health inspection.
They may not provide a fully objective assessment and could be inclined to overlook issues to hand you a more favorable report. Your audit may not hold up under scrutiny from stakeholders in the future, especially if you were to experience a security incident.
Another red flag is if an "all in one" vendor is claiming to be able to implement your security controls and conduct your audit at a suspiciously cheap price tag. Meeting requirements such as SOC 2, HIPAA, GDPR, and dozens of others can be fairly economically efficient and not break the bank. However, compliance isn't incredibly cheap either. As in many cases in life, when something seems too good to be true, it probably is.
Meeting information security compliance requirements isn't always an easy process. It often takes making many complex decisions involving business outcomes, processes, technologies, and acceptable risk. In other cases, it means fundamentally reworking a core business process to meet a requirement.
When done correctly, meeting requirements provides regulators and potential customers the assurance that your organization takes security seriously.
When done poorly, it can result in expensive boondoggles that cost your organization legal fees and valuable customer relationships. Engaging separate entities to develop and audit your infosec program is a safeguard against bias and helps you uphold the integrity of your compliance efforts.

So, what are the actual requirements and guidelines from which the robustness of your compliance can be judged?
Let's take a look at what a few entities and guidelines have to say on audit independence:
Guidelines and Best Practices To Ensure Audit Independence
Sarbanes-Oxley (SOX) is a U.S. federal law aiming to protect investors by improving the reliability of corporate disclosures. Although it primarily applies to publicly traded companies, it can indirectly impact privately held SaaS companies, for example, that may plan to go public in the future or those that provide services to public companies.
For instance, a SaaS company that handles financial data or provides financial reporting services to public companies may need to make sure its controls align with SOX requirements.
Section 404 of Sarbanes-Oxley requires that companies have an independent audit of internal controls over financial reporting.
The Public Company Accounting and Oversight Board (PCAOB) states the following:
A registered public accounting firm and its associated persons must be independent of the firm's audit client throughout the audit and professional engagement period.
Note 1: Under Rule 3520, a registered public accounting firm or associated person's independence obligation with respect to an audit client encompasses not only an obligation to satisfy the independence criteria applicable to the engagement set out in the rules and standards of the PCAOB, but also an obligation to satisfy all other independence criteria applicable to the engagement, including the independence criteria set out in the rules and regulations of the Commission under the federal securities laws.
Note 2: Rule 3520 applies only to those associated persons of a registered public accounting firm required to be independent of the firm's audit client by standards, rules or regulations of the Board or Commission or other applicable independence criteria.
Now that description is a bit heavy on jargon, so we can consult another source. SOC 2 is overseen by the American Institute of Certified Public Accountants (AICPA). AICPA has (fortunately for the non-accountants and lawyers among us) published a "Plain English Guide to Independence," which provides the following guidance:
Independence of mind is the state of mind that permits a member to perform an attest service without being affected by influences that compromise professional judgment, thereby allowing an individual to act with integrity and exercise objectivity and professional skepticism.
Independence in appearance is the avoidance of circumstances that would cause a reasonable and informed third party, who has knowledge of all relevant information, including safeguards applied, to reasonably conclude that the integrity, objectivity or professional skepticism of a firm or member of the attest engagement team is compromised.

Image Source: AICPA
In even plainer English, AICPA is saying that auditors should avoid any conflicts of interest that could impair their objectivity. This includes scenarios where they might audit their own work or the work of close colleagues, which would naturally apply to building and then auditing the same infosec program.
The AICPA's guidance, particularly under the SOC standards, prohibits organizations from auditing their own services, stating that:
"The auditor's responsibility is to provide an independent assessment of the service organization's controls that may affect user entities' financial reporting."
AICPA's emphasis on independence effectively makes it clear that an organization both implementing security controls for compliance and conducting the audit would risk impairing the auditor's independence and objectivity, thus not aligning with best practices. It's clear from their guidance that auditors should avoid any conflicts of interest that could impair their objectivity.
Lastly, many standards and frameworks, such as ISO/IEC 27001 and NIST, emphasize the importance of independence in the auditing process. They recommend that audits be conducted by individuals who are not involved in the day-to-day operations or implementation of the security program.
Assessing Audit Independence and Quality
Now, let's imagine a SOC 2 audit. Say you've hired an accounting firm with a security branch to help implement controls pursuant to SOC 2. Now imagine that the very same firm is going to audit your organization for compliance. Could a reasonable and informed observer conclude that the firm auditing the controls may be biased as a result of the fact that they were the ones who also implemented the controls?
To recall an earlier analogy, it's as if a restaurant were to perform its own health inspection. What are the odds that they are going to find major violations? Probably pretty low. When the same person who designed and implemented the infosec program also audits it, there is a significant risk of bias. They may inadvertently overlook issues or be less critical of their own work.
Even if this "all in one firm" issues a SOC 2 report without findings, your organization could still be at substantial risk. Imagine you have a major cyber event in the future, and customers find out that your SOC 2 report wasn't entirely accurate and that the firm you hired took shortcuts through the process. Information security isn't just a legal risk; it's a business and reputational risk.
A reputable information security compliance provider (whether an accounting firm or a managed security services provider) should do the following:
- Be able to provide reference customers, either publicly or privately, who have worked with the firm in the past to implement controls.
- Work with a reputable outside auditing firm that conducts independent audits of control implementation.
- Ensure that all employees adhere to industry standards, guidelines, and best practices such as those set by the AICPA.

Some firms, such as Rhymetec, have identified specific high-quality third-party firms that we often recommend to our clients to complete the audit process. But if clients prefer a different audit partner, that is okay too.
Information security compliance requirements shouldn't be considered a burden to businesses. Implementing requirements such as SOC 2, GDPR, HIPAA, and others should help organizations be assured that they are meeting relevant legal and ethical requirements while taking adequate and appropriate measures to safeguard customer data.
When conducted by ethical providers, standards like SOC 2 can substantially enhance a business's confidence and security protocols without disruption and without massive cost. Independent audits provide greater credibility to your stakeholders, including management, customers, and regulatory bodies. You can be confident that the audit findings are impartial and accurate.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business.
Interested in reading more? Check out more content on our blog:
- Maximize Your Use of Compliance Automation Platforms
- Cybersecurity For Startups: A Rhymetec Guide
- Security vs. Compliance? A False Dichotomy
This ISO 42001 checklist will walk you through the four phases of achieving certification.
These steps are based on our security team's process for helping organizations complete their ISO/IEC 42001 certification readiness. Our security team at Rhymetec has helped hundreds of companies achieve their security goals and meet compliance requirements. To find out how we can fast-track you to ISO 42001 compliance, contact our team today:
Hopefully, this checklist will give you a clear idea of the work ahead needed for ISO 42001 compliance and will help you create a project plan.
We'll start with a high-level overview of your ISO 42001 checklist and then dive into each phase in detail:
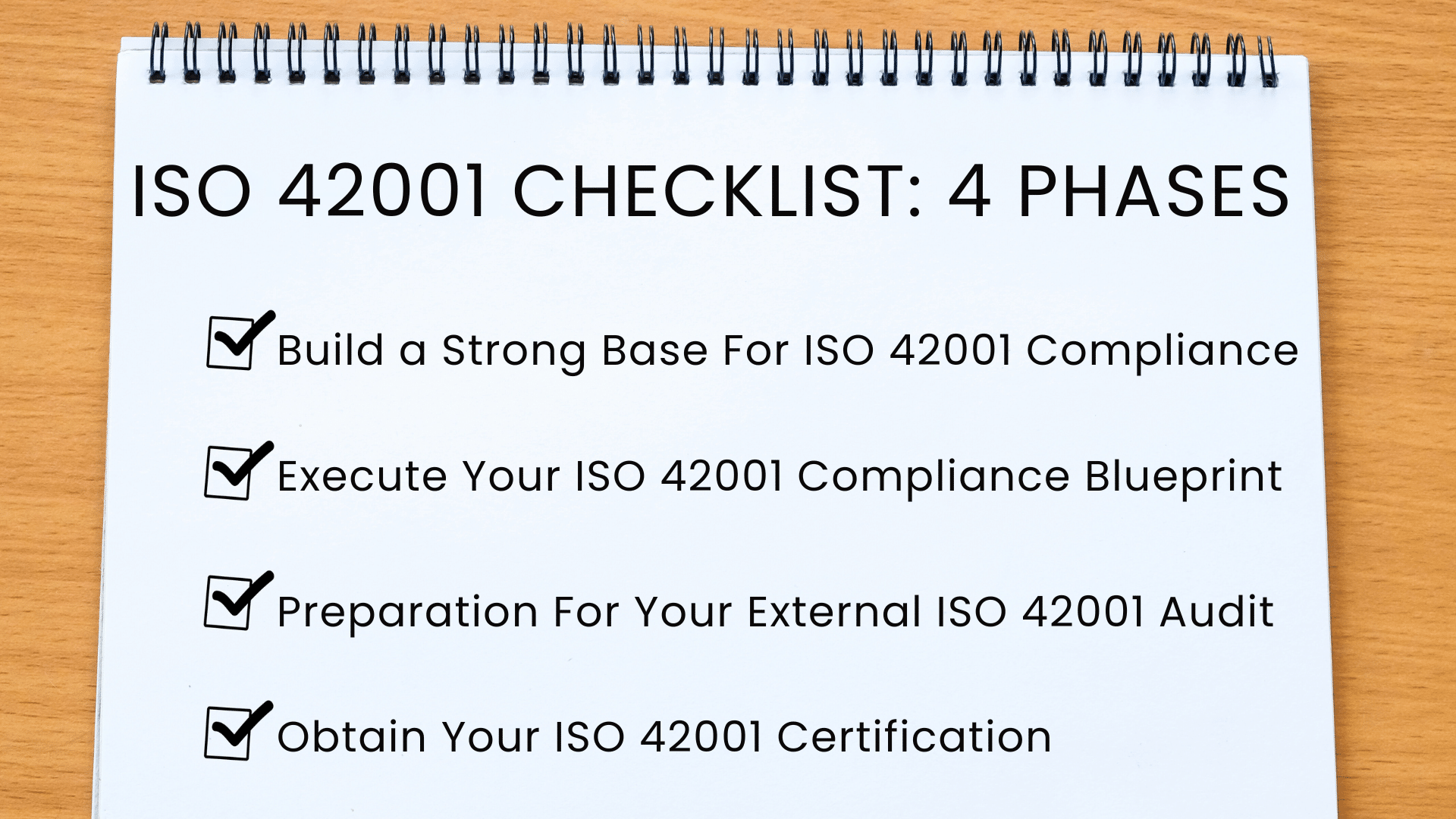
ISO 42001 Checklist Overview
1. Build a Strong Base for ISO 42001 Compliance.
- Understand Your ISO 42001 Requirements
- Conduct An Initial Gap Analysis
- Conduct A Risk Assessment
- Obtain Executive Support
2. Execute Your ISO 42001 Compliance Blueprint.
- Designate a Compliance Project Leader
- Draft An Implementation Roadmap For AIMS
- Set Up The AIMS Structure
- Create Organization-Wide Awareness
- Apply Necessary AIMS Controls
- Conduct Executive AIMS Evaluations
3. Preparation for Your External Audit.
- Conduct Internal Audits
- Select an ISO 42001 Certification Body
- Prepare Documentation
- Pre-audit Meeting
4. Obtain Your Certification.
- Undergo Your Audit
- Address Any Identified Issues
- Ongoing Improvements & Post-Audit Plan
Let's go over detailed steps under each phase:
Phase 1: Build A Strong Base For ISO 42001 Compliance
In this phase, you'll lay the groundwork for your organization to build an Artificial Intelligence Management System (AIMS) and achieve ISO 42001 compliance.
Establishing an AIMS is not just about compliance; it's about crafting a concrete strategy to improve decision-making and risk management around AI technologies. After this phase, you'll have a clear direction for responsible AI use and be on the right path to work towards ISO 42001 compliance:
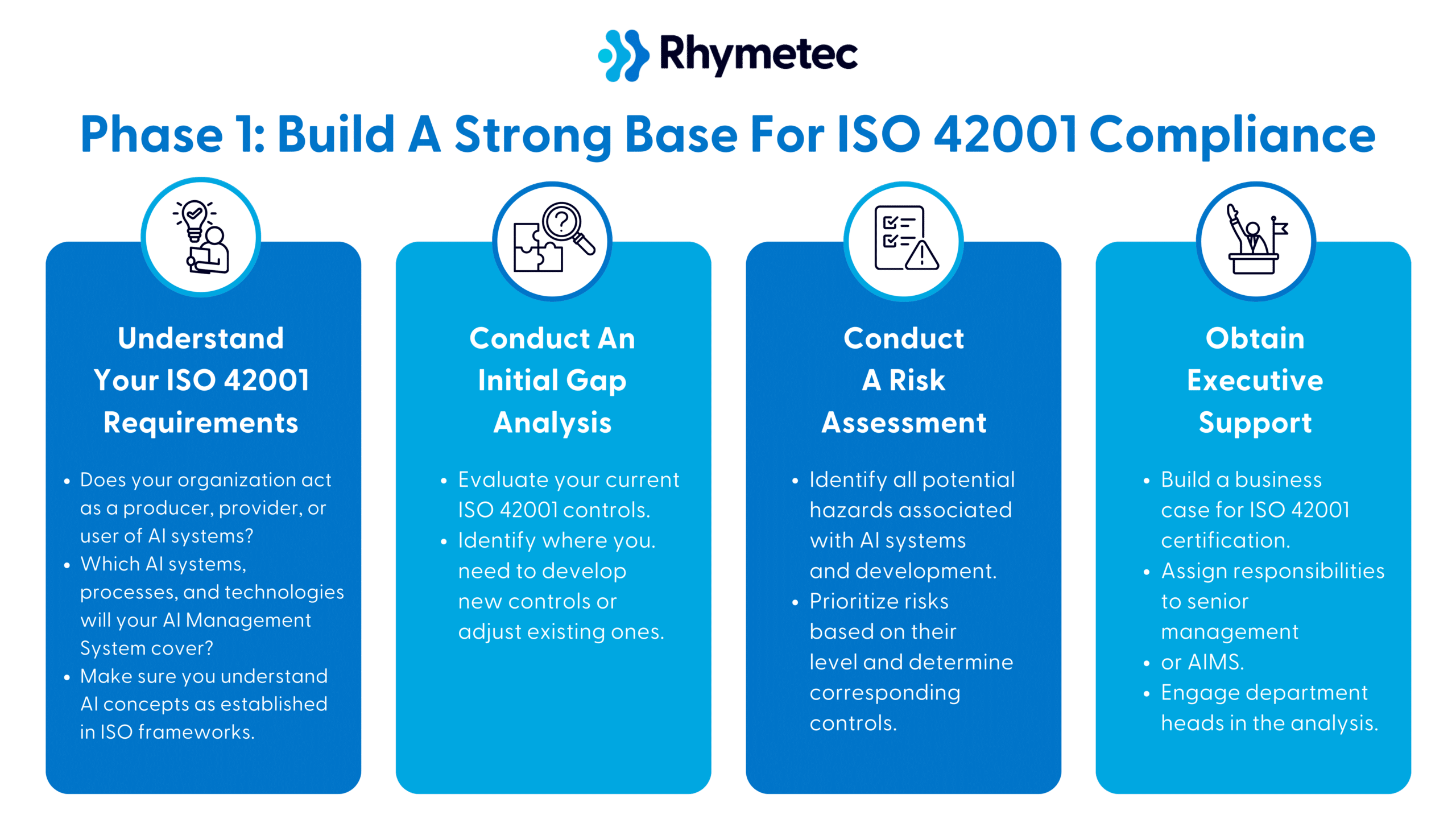
1. Understand Your ISO 42001 Requirements
Does your organization act as a producer, provider, or user of AI systems?
You'll have different requirements depending on which of these your organization falls under.
Providers are companies such as OpenAI that build AI models like ChatGPT. Service providers customize and use these models. Users can include any business that uses AI services either directly from producers or via services from providers.
Which AI systems, processes, and technologies will your AI Management System cover?
Which technologies and assets do you have that incorporate AI? You will need to identify what will be included to map out the boundaries of your Artificial Intelligence Management System (AIMS).
Make sure you understand AI concepts as established in ISO frameworks.
Are you already familiar with how ISO frameworks define terms like "AI systems" and "machine learning models"?
If so, great! If not, ISO provides a glossary of terms you can use to see exactly what the frameworks mean when they use these terms. It's important to familiarize yourself with the terminology to understand each step of the compliance process, speak the same language as your auditors, and avoid miscommunications.
2. Conduct An Initial Gap Analysis
Evaluate your current ISO 42001 controls.
Compare your existing practices against ISO 42001 controls. Do you have any current practices to mitigate AI risks? What about ethical concerns related to AI, and data integrity concerns? You may already have a basis for some of the controls, especially if you already have another ISO framework.
Identify where you need to develop new controls or adjust existing ones.
Now that you have an idea of how your current practices map onto ISO 42001 controls, draft up a complete list of what you need to do to develop new controls or adjust existing ones. You will need this going forward.
3. Conduct A Risk Assessment
Identify all potential hazards associated with AI systems and development.
Unlike frameworks like ISO 27001, ISO 42001 does not focus heavily on security.
Security is an element of the framework, but a relatively small one. Instead, the potential hazards associated with AI, such as ethical issues, environmental considerations, and concerns around fairness and bias, are key.
Focusing on the areas mentioned above, come up with a list of potential AI risks related to your products, services, and all other activities.

Prioritize risks based on their level and determine corresponding controls.
Assess the likelihood and potential consequences of each risk. You will need this documentation later on. Start drafting an action plan to remediate risks, focusing on the highest risks first. Assess your list of existing practices and their effectiveness in mitigating risks.
Threats range from cybersecurity attacks to operational risks like system failures or errors in the AI's decision-making process. For each AI-related risk that your organization could potentially encounter, the impact level needs to be assessed:
Impact is categorized as low, medium, or high based on factors like financial loss, legal repercussions, and damage to customer trust. As an example, if your AI handles sensitive or critical data, the risk of a data breach would be considered high risk (as a breach could result in substantial legal and reputational damage).
A medium risk could be data bias in functions that are not critical to core operations but could impact user satisfaction or minor decision-making processes. A threat with a low-risk level could be any potential minor AI performance fluctuations. If you use an AI-driven customer support chatbot, for example, the risk of users experiencing minor delays in response time or slight inaccuracies in non-critical responses could be considered low risk.
Think ahead when conducting your risk assessment: What would happen if your organization experienced each risk? How complex would remediation be? How would employees, stakeholders, and your business operations be impacted?
4. Obtain Executive Support
Build a business case for ISO 42001 certification.
Create a compelling business case that shows the strategic benefits of ISO 42001 certification. Include how it will enable AI governance, help your organization comply with regulations, ease concerns that customers and prospects may have, and build stakeholder trust.
A formalized AI management system offers a lot of long-term value. What this looks like will depend on your specific organization. Try to emphasize not only the ways in which ISO 42001 mitigates risk but also how it offers opportunity and innovation potential.
Assign responsibilities to senior management for AIMS.
Assign senior management responsibilities to align the AIMS with your goals and provide them with the necessary resources.
Engage department heads in the analysis.
Bringing in department heads from IT, legal, operations, and human resources into the gap analysis process, for example, is a great way to create engagement across the organization. Plus, their involvement ensures all potential impacts of AI systems are being considered.
ISO 42001 Checklist Phase 2: Execute Your ISO 42001 Compliance Blueprint
Here, you'll activate the plans laid out above. This phase involves hands-on tasks such as appointing a project manager, setting up the structures for your AIMS, and implementing controls. This phase of your ISO 42001 checklist ends with your internal audit to assess your ISO 42001 certification readiness before moving on to external evaluations:
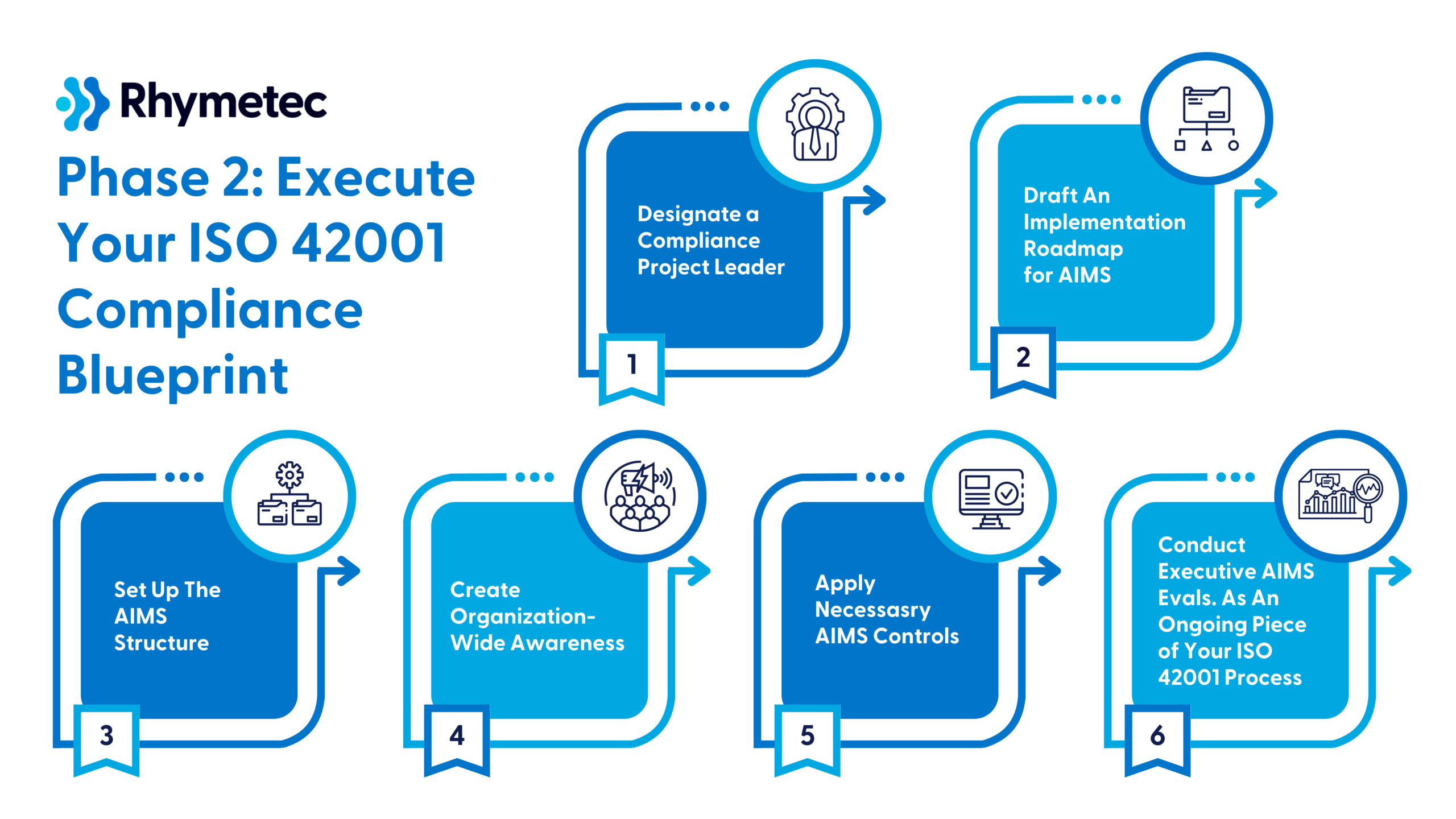
1. Designate a Compliance Project Leader
Select a qualified compliance leader.
Appoint a project manager with a solid understanding of AI and compliance issues. This individual will coordinate all activities related to achieving ISO 42001 certification and act as the point of communication between departments and external auditors.
2. Draft An Implementation Roadmap For AIMS
Develop a detailed project plan for your ISO 42001 process.
Solidify your project plan using the gap analysis conducted earlier as a baseline. Your plan should include deadlines, resource allocations, and every stage from the initial assessment to the final audit.
Budget appropriately.
Allocate sufficient financial and human resources to support the project. This includes funding for training, external consultants, auditing costs for certification, and technology upgrades needed to comply with ISO 42001.
*TIP: When implementing ISO 42001, you should not rely on checklists alone from external sources. Purchasing the standard should be in your budget for successful implementation.
3. Set Up The AIMS Structure
Define Your AI Management System Structure.
Set up a structure for your AIMS that integrates with existing organizational processes. The structure should support all stages of AI lifecycle management, from development to deployment and maintenance.
Document All Processes.
Make sure you are documenting everything as you work through these steps. You'll need everything from workflows, decision-making processes, and control measures documented when it comes time for your audit.
*TIP: Using a compliance automation tool at this point can be tremendously helpful. Compliance automation platforms allow you to easily organize your documentation. When it comes time for your audit, it makes your auditor's job easier and more efficient to be able to see everything clearly laid out in one central place.
4. Create Organization-Wide Awareness
Develop training programs.
Organize training sessions to improve your employees' AI and compliance knowledge base. Focus on ethical AI use, data security, and the legal implications of AI technologies.
Circulate information across the organization.
Distribute informational materials and regular updates about AIMS and its importance to encourage organization-wide understanding and engagement. Internal communications channels such as newsletters, intranets, and staff meetings are all good avenues for dissemination.
5. Apply Necessary AIMS Controls
Implement controls.
ISO 42001 controls address risk management, data protection, system reliability, and transparency.
The way controls are implemented will vary depending on your organization's industry, needs, risks, and the types of AI applications you use. (A complete control list can be found in ISO/IEC 42001:2023, Annex A).
*TIP: Consulting with a compliance expert at this step may be necessary. Many startups choose to work with a Managed Security Services Provider (MSSP) at this stage. Rhymetec's vCISO program provides hands-on managed security services, taking the complexity of compliance off your plate, and doing the readiness and audit phases for you.
Plan to regularly update control measures.
Continuous improvement is required by ISO 42001. You should plan to continuously monitor and update controls to adapt to new technologies, changes in organizational processes, and shifts in regulatory requirements.
6. Conduct Executive AIMS Evaluations As An Ongoing Piece of Your ISO 42001 Process
Organize regular review meetings.
Hold management review meetings periodically to assess the AIMS' performance. Reviews should involve top management and key stakeholders to help AI systems & applications align with broader organizational goals.
Update your executive team regularly.
The last step in this phase of your ISO 42001 checklist is to regularly update your executive team. Keep them informed about the outcomes of management reviews, including challenges, achievements, and the effectiveness of the AIMS.
ISO 42001 Checklist Phase 3: Preparation for External ISO 42001 Audit
This stage is where you make sure everything is in perfect order for your audit.
Choosing the right auditor is critical - you want to choose a reputable certification body that will conduct a legitimate and fair audit, providing credible validation of your AIMS.
Each step in this phase is also an opportunity to solidify stakeholder confidence and demonstrate your proactive approach to responsible AI management and compliance.
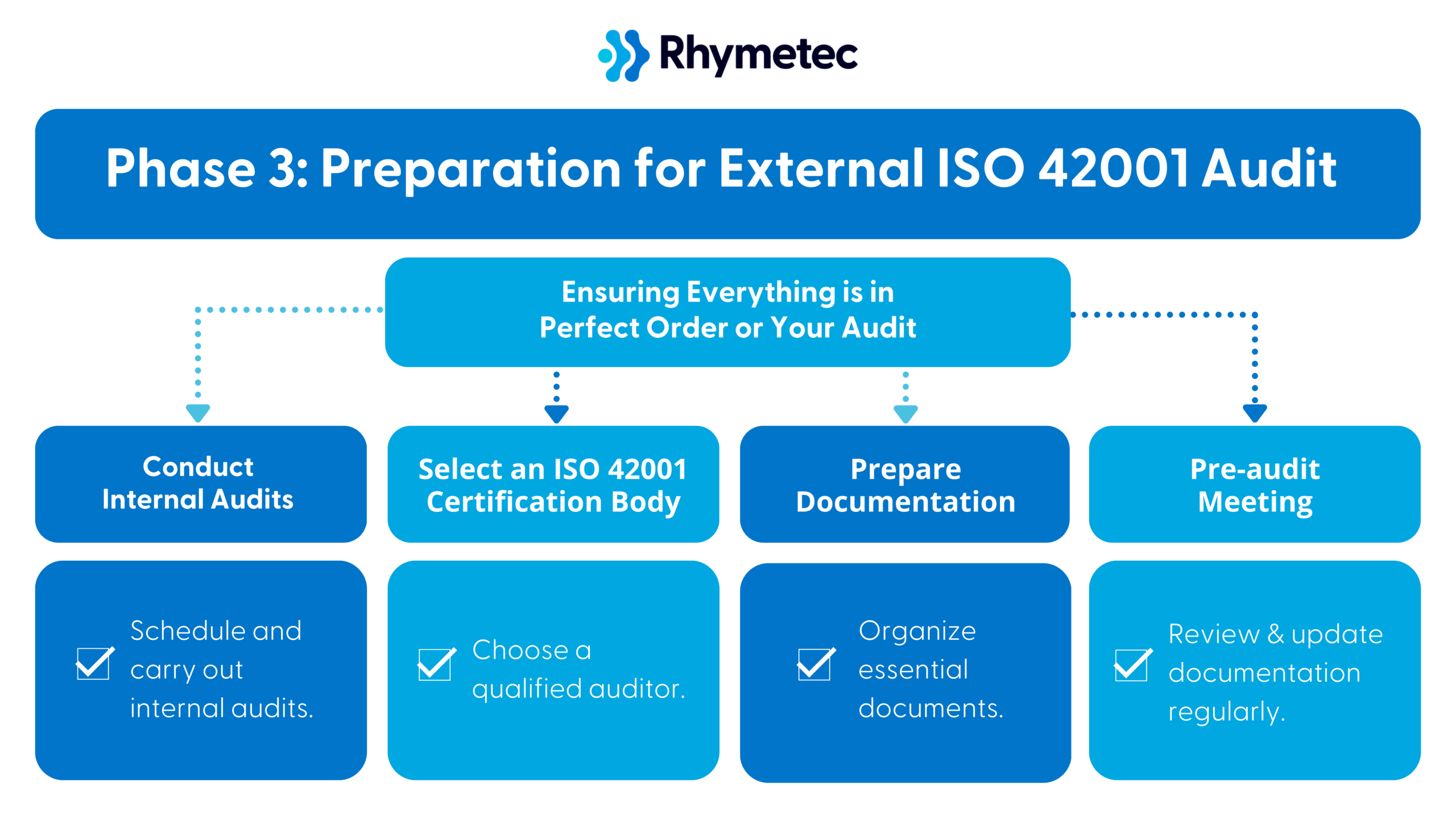
1. Conduct Internal Audits
Schedule and carry out internal audits.
ISO internal audits identify any gaps in compliance and provide recommendations for improvements before your external audit. It serves as a trial run, providing insights into potential audit challenges and giving you a chance to address any issues.
2. Select an ISO 42001 Certification Body
Choose a qualified auditor.
Select an auditing firm that has been certified to offer ISO certifications and has demonstrated experience in assessing AI management systems. Your certification body must be accredited to guarantee a legitimate audit and certification.
3. Prepare Documentation
Organize essential documents.
Gather documentation that demonstrates your compliance with ISO 42001. Documents are to include policies, procedures, control implementation records, and evidence of your plans for continuous improvement efforts.
Make things as easy as possible for your auditors! Documents should be in a format that is readily available and organized for easy reference during the audit.
Review and update documentation regularly.
Regularly review your AIMS documentation to make sure it accurately reflects current AI management practices and that all modifications are recorded. Keep this documentation accessible to all relevant personnel and the auditing team.
4. Pre-audit Meeting
Set up an initial audit meeting.
Arrange a meeting with the selected certification body to discuss the audit process. Use this as an opportunity to understand the audit scope, methodology, and specific focus areas. You should also align expectations and clarify the audit schedule.
Compile key audit questions.
Beforehand, prepare a list of questions and points needing clarification. Cover logistical details, specific compliance queries, and any concerns about the AIMS implementation.
Discuss audit scope.
You'll want to clarify the detailed scope of the audit and confirm that both parties have a mutual understanding of the audit boundaries. The scope must cover all relevant areas of your AIMS.
Phase 4: Obtaining your ISO 42001 Certification
This final phase is where all of your preparation pays off.
Engaging fully with auditors transforms this process from a compliance exercise to a powerful tool for improving your operations and reputation. Undergoing your audit isn't just a badge for your business to put on your website; it's a statement that you take AI risks seriously and are ahead of the curve in managing AI responsibly.
Lastly, continually improving after the audit shows you're not just "checking a box" to get through an audit. Ongoing improvements post-audit strengthen trust among clients and partners and support compliance maintenance.
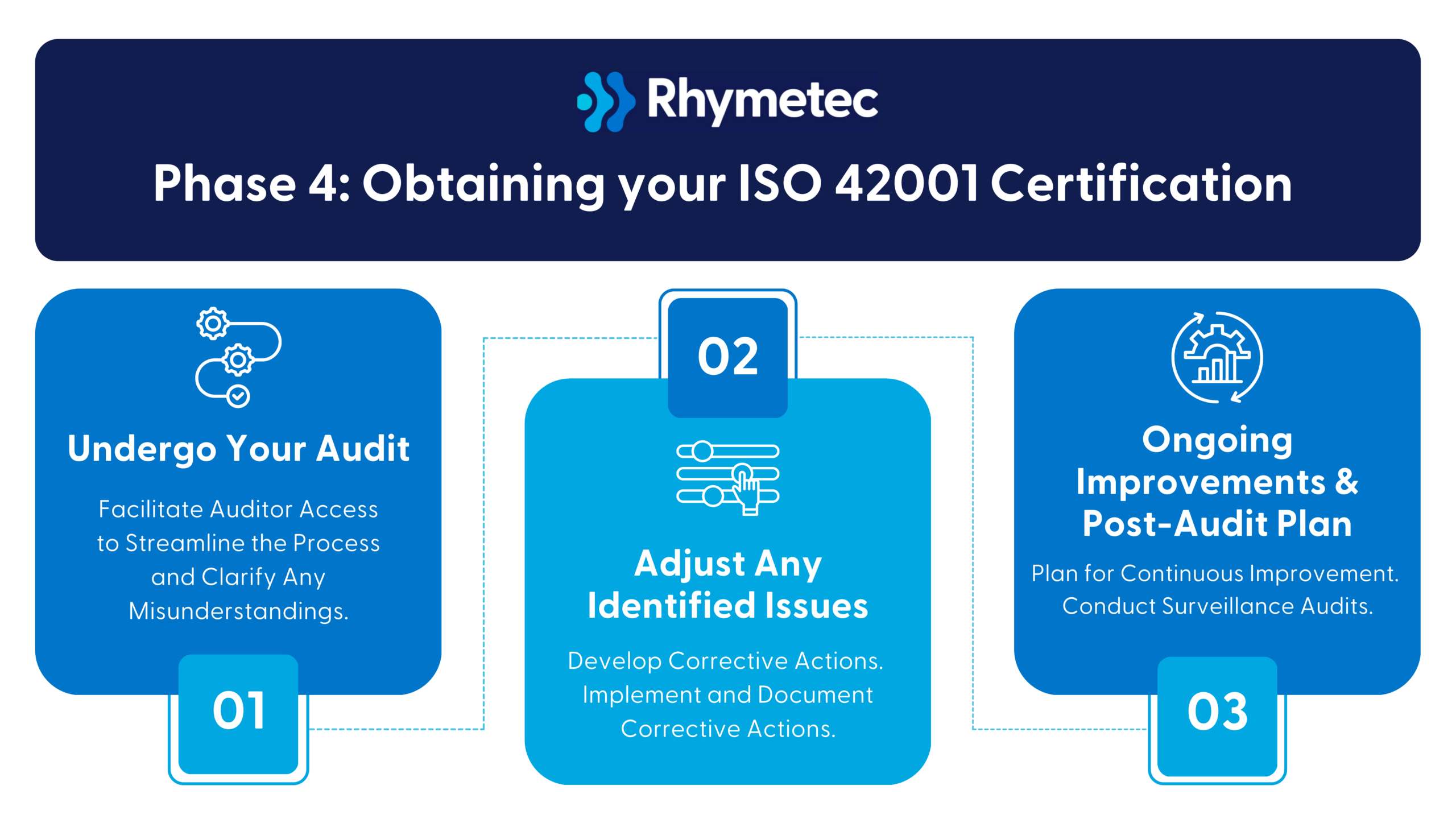
1. Undergo Your Audit
Facilitate Auditor Access.
Auditors need to have full access to all relevant sites, personnel, and documentation. Designate a team member to serve as a point of contact and participate in discussions with auditors to streamline the process and clarify any misunderstandings.
2. Address Any Identified Issues
Develop Corrective Actions.
Promptly create action plans for any non-compliance issues identified during the audit. Assign clear responsibilities and timelines for these actions.
Implement and Document Corrective Actions.
Execute the necessary corrective measures and document the processes. You will need this documentation during follow-up audits.
3. Ongoing Improvements & Post-Audit Plan
Plan for Continuous Improvement.
Develop a plan for continuous improvement based on audit findings.
Your post-audit plan should include updating training programs and communication with employees to address any changes. Schedule regular intervals to review the AIMS and identify opportunities to improve.
Conduct Surveillance Audits In Preparation to Re-certify Every 3 Years.
Lastly, keep in mind you will need future surveillance audits as part of your ongoing ISO 42001 process:
ISO 42001 requires recertification every 3 years to remain compliant. Surveillance audits are needed in between to ensure your organization is ready for the next official audit.
Immediate Benefits After Completing Your ISO 42001 Checklist
After you've completed all items in your ISO 42001 checklist and have your certification in hand, you will see a number of immediate benefits:
You will now be able to communicate, through verified third-party documentation, to your prospects and customers that your AI use follows the highest industry standards. You can use your certification to assuage any concerns your clients and prospects may have about AI. Being able to show them your documentation increases trust and can shorten your sales cycle. This is especially important given that there is growing concern over generative AI security risks.
Additionally, you will have peace of mind knowing that your risk is substantially reduced. The roadmap you now have for the strategic use of AI will serve as a business enabler as you continue to expand your AI offerings and break into new marketplaces.
For more information, check out our ISO 42001 Compliance FAQ for the most common questions our team at Rhymetec sees about ISO 42001 (Who Needs ISO 42001?, How Different Is ISO 42001 Vs. ISO 27001?, How Much Does ISO 42001 Certification Cost?, How Long Does ISO 42001 Certification Take?, and more), or contact our team today:
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business.
If your organization is interested in exploring compliance with AI standards, we now offer ISO/IEC 42001 certification readiness and maintenance services and are happy to answer any questions you may have on the ISO 42001 process.
Interested in reading more? Check out more content on our blog.
If there's one thing most people agree on in 2025, it's that we need strong regulations around artificial intelligence (AI). Nearly 80% of Americans want stricter regulations on the use of public data to train AI models, and surveys show a growing concern over AI jeopardizing our privacy.
Meanwhile, companies are barreling ahead: Over 56% of businesses use AI to improve business operations, and 83% of executives see AI as a strategic priority. The excitement around this technology and its innovative use cases is understandable, but integrating AI without slowing down to consider privacy, safety, and ethical concerns is risky.
Implementing an AI framework that directly addresses these issues is a major step companies can take to assuage concerns. Certification with ISO 42001 promotes responsible AI use and provides verified, documented evidence to stakeholders that you take AI risks seriously.

What Is ISO 42001?
ISO 42001 is a certifiable international standard providing guidelines for building and managing AI tools. It offers a repeatable framework from which organizations can build solid operational governance and management systems while promoting responsible AI usage.
The standard covers areas including security, privacy, and ethical practices. It specifies the requirements for creating a reliable AI program that, when developed with overall business goals and daily functions top of mind, can improve the safety of AI systems while also serving as a business enabler.
With AI becoming widely accessible since the introduction of tools like ChatGPT in 2022, the demand for security and privacy measures around AI has been amplified. Enter the role of AI frameworks - of which ISO 42001 is one of the most prominent.
ISO 42001 supports the development of AI that respects data security and user privacy, addressing the increasing public demand for transparency and accountability:
Why Is ISO 42001 Compliance Important?
A growing number of organizations seek to obtain ISO 42001 compliance for two primary reasons:
1. Certification as a Marketing & Reputation Management Tool: Compliance with ISO 42001 allows companies to communicate to their customers, prospects, and stakeholders that they adhere to the highest standards in AI use and development.
Organizations can use their certification to reassure clients and prospects. ISO 42001 certification acts as a mark of credibility, signaling that the organization has taken steps to implement best practices as laid out by an industry gold standard framework.
This builds trust with stakeholders concerned about the potential impacts of AI and can shorten the sales cycle. If a prospect asks about your organization's AI practices, being able to show a certification is a powerful tool.
2. To Guide Strategic Implementation of AI: Companies seek to leverage the roadmap offered by ISO in a meaningful way that leads to AI-related strategies that ultimately serve as business enablers.
ISO 42001 certification not only supports compliance with other regulatory and legal requirements but also positions you to fully reap the business benefits of responsible AI use. By following ISO 42001, companies reduce security risks, optimize decision-making processes, foster customer trust, and ultimately drive business growth and sustainability.
Who Needs ISO 42001 Compliance?
ISO 42001 is particularly useful for companies:
- Developing new AI features
- Creating AI-powered products
- Acting as AI producers, service providers, or end-users
Companies must be prepared to make changes to their products as AI technology evolves. Adherence to ISO 42001 largely offsets the amount of time you'll need to spend implementing changes down the road while reducing risk long-term.
The AI ecosystem can be categorized into three roles:
- AI Producers: Companies like Microsoft, OpenAI, and Anthropic that build and sell foundational AI models.
- Service Providers: Organizations that consume these models from producers, customize them, and then sell them downstream.
- Customers and Users: The end-users and businesses that utilize AI services and products.
ISO 42001 can apply to any business interacting with others in this ecosystem. Organizations in each of these three roles can benefit from establishing an AI management system as per ISO 42001 guidelines, and focusing on areas such as data provenance, the handling of training data and algorithms, and the outcomes produced by AI systems.
Encouraging organizations to think deeply about the potential impacts of AI for everyone in their ecosystem is one of the main purposes of frameworks like ISO 42001.
How To Get ISO 42001 Certification: How Easy Is It?
One major misconception about ISO 42001 is that it focuses solely on the security and privacy of AI systems. In reality, the standard encompasses a border range of considerations, including ethical practices, fairness, bias resolution, and understanding the overall impact of AI systems.
Security alone is actually a small component in the context of the entire framework.
At a high level, achieving ISO/IEC 42001 certification includes several steps:
1. Gap Analysis
Conducting a gap analysis identifies the differences between your organization's current state and where you need to be to meet the requirements of ISO 42001.
2. Implementation
Based on the gap analysis, the next step is to implement changes to align with ISO 42001 controls. This could include everything from revising policies to updating procedures and training employees.
3. Internal Audit
Before seeking external certification, conducting an internal audit helps ensure you meet all requirements and are ready for the external audit.
4. External Audit
An accredited certification body performs your external audit, determining whether or not you obtain certification at that time.
Depending on factors like company size and infrastructure, this process can be complex and time-consuming. However, it ultimately strengthens your organization's AI governance and management practices, reducing risk and saving time and money down the road.
How Different Is ISO 42001 Vs. ISO 27001?
Organizations with ISO 27001 certification may assume that transitioning to ISO 42001 compliance is straightforward. However, ISO 42001 is fundamentally different from ISO 27001, despite their complementary nature from a high-level structure perspective.
While ISO 27001 centers around information security management systems (ISMS), ISO 42001 is highly specialized in the scoping of AI systems. The good news is that ISO 42001 is designed to integrate smoothly with existing ISO frameworks, including ISO 27001. The new framework is designed to be easily integrated for organizations that already have an ISO framework.
All of the ISO frameworks are designed in a way that allows them to act as building blocks for each other. The areas in which they diverge, meanwhile, leave opportunities for organizations to adapt controls to their specific needs and environments.
As an example, both ISO 27001 and 42001 require a risk assessment. However, even if you've completed your risk assessment for ISO 27001, you would still need to identify risks specific to AI systems for 42001.
The impact assessment of ISO 42001 goes beyond security and privacy, encompassing broader aspects such as the ethical implications and the societal impact of AI. This expanded focus means that the way controls are operationalized will both diverge from and build on ISO 27001.
How Much Does ISO 42001 Certification Cost?
Let's break down the costs:
Direct Costs
Hiring an accredited certification body to conduct the audit is a primary cost. Depending on the size and complexity of your organization, this can range from $5,000 - $20,000. This fee typically covers the initial certification audit and any follow-up assessments.
Implementing ISO 42001 requires time and effort from your team. You may need to allocate significant internal resources to manage the project, which can translate into measures like hiring temporary staff to handle regular duties.
Many startups choose to hire consultants.
Consulting fees can range from $10,000 - $50,000, depending on the level of support you need. Consultants assist with gap analysis, control implementation, and preparation for your audit.
Indirect Costs
There are potential costs around employee training and awareness, with the goal of making sure everyone understands their role in working towards ISO 42001 compliance. Technology upgrades represent another indirect cost. You may need to invest in new software or upgrade existing systems to meet ISO 42001 requirements. Costs here can vary greatly depending on your technology stack.
Lastly, there are costs associated with ongoing maintenance. Maintaining ISO 42001 certification requires regular audits and continuous improvement. Budget for annual internal audits and surveillance audits, which can cost between $3,000 - $10,000 per audit per year, and allocate resources for ongoing training and process updates.
Cost-Benefit Analysis
While the costs may seem significant, consider the benefits: ISO 42001 certification can improve your company's reputation, build customer trust, and open doors to new markets. It mitigates risks associated with AI, potentially saving money in the long run by avoiding costly security issues and reputational damage.
How To Implement ISO 42001: Critical Components of Building an AIMS & Demonstrating Compliance
Implementing ISO 42001 involves establishing an AI Management System (AIMS) that aligns with the standard's requirements and fits the context of your organization. The framework is structured around 10 clauses, similar to other ISO management systems, and includes annex controls that can be operationalized differently depending on the organization.
Below are 6 key components of meeting ISO 42001 compliance:
1. Management Commitment
Leadership must define AI policies, set objectives that align with the strategic direction of the organization, and make resources available for the implementation and maintenance of the system.
2. Risk Assessment and Impact Analysis
Unlike traditional frameworks that focus on security and privacy, ISO 42001 requires a broader impact assessment. A core part of the framework involves identifying and evaluating AI-related risks across areas, including environmental impact and ethical considerations.
3. ISO 42001 Annex Controls
The annex of ISO 42001 provides specific controls that need to be implemented, which can be adapted to the context of the organization. For example, this may include guidelines around data provenance, with the goal of making sure training data and AI algorithms are not biased.
4. Operational Planning, Documentation, and Training
Documenting everything pertaining to processes for the effective operation of the AIMS is another key step. Processes need to be clearly defined and laid out for all employees, so they can be consistently followed.
All staff involved in the AIMS need to have the necessary skills and knowledge. Appropriate training and resources need to be provided to support this.
5. Monitoring and Measurement
Mechanisms to monitor the performance of the AIMS over time are another key component of ISO 42001 compliance. Such measures can take the form of regular audits and assessments to see if the system remains effective and aligned with requirements. Any issues identified should be addressed promptly.
6. Continuous Improvement
A process must be established to regularly review and update the AIMS to reflect changes in technology, regulatory requirements, and organizational goals. This iterative approach allows you to stay ahead of emerging risks and challenges.

How Long Does ISO 42001 Certification Take?
With managed security services providers like Rhymetec, it takes anywhere from 4 - 6 months for the preparation and readiness portion of ISO 42001 compliance.
This timeline varies depending on organization size and the complexity of their AI systems. If an organization has already implemented ISO 27001, the process will be on the faster end, with many controls needing to be tweaked rather than built from scratch.
Several scoping factors determine how long your timeframe will be for the audit, such as the number of employees, complexity factors, and organizational role (producer, provider, developer, or user of AI). As a rough estimate, you can expect the certification audit by an accredited body to take 4 - 8 weeks.
About Rhymetec
Our mission is to make cutting-edge cybersecurity available to SaaS companies and startups. We've worked with hundreds of companies to provide practical security solutions tailored to their needs, enabling them to be secure and compliant while balancing security with budget. We enable our clients to outsource the complexity of security and focus on what really matters – their business.
If your organization is interested in exploring compliance with AI standards, we now offer ISO/IEC 42001 certification readiness and maintenance services and are happy to answer any questions you may have.
The advent of generative AI has been a wake-up call for risk management and information technology professionals. GenAI applications have been notably compared to the invention of the internet, computing, and fire, depending on who you ask.
At the same time, concerns over the risks of AI continue to grow, with many governments and organizations concerned over implicit bias trained into the models and the lack of transparency into how the models output answers.
This article examines the new era of AI regulation augured by one of the first AI frameworks, ISO 42001. We will begin by outlining how GenAI works and identifying a few fundamental issues with current systems. Following that, we'll do a synopsis of the ISO 42001 framework, as well as two other AI frameworks, before concluding with what organizations can expect going forward.
How Do Language Models Work At A High Level?
To understand why we need to manage risk around generative AI, it's first important to understand how they work at a basic level. Let's take large language models (LLMs) as an example, as they are currently all the rage among companies adopting AI.
LLMs are AI applications built on the machine learning paradigm of deep learning. To be simplistic, language models are trained to predict the next token, which you can think of as the next word:
Imagine you are asked to complete the sentence, "I'm feeling very under the _."
Your brain probably filled in the word "weather" to complete the sentence, almost automatically. AI language models are trained on unimaginably large corpora of information, with the full contents of the internet being a starting but not ending point.
The training data serves as a guide, providing language models with a statistical way to identify the fundamental data structures within language. LLMs then essentially optimize through a process called stochastic gradient descent to identify the next most likely word in every sentence and every paragraph, and can do this at scale across incredibly complex prompts.
AI & Transparency
Many claim that "we don't understand how AI works." This is both true and not true. At a conceptual level, we absolutely understand how AI works. Language models are trained across unimaginably large data sets to complete the next token using what amounts to complex matrix multiplications.
At a granular level, AI language models are a black box. To illustrate the point, let's imagine you have implemented a large model to help screen for healthcare fraud. Now imagine that after hundreds of thousands of case reviews, you notice that the language model flags people named "Amy" for fraud at 3000% the rate of every other first name.
Understanding that the model is optimizing for the next token prediction doesn't do you much good. Trying to understand why the language model is singling out Amy is like taking a satellite photo of New York City and asking why you can't use that to predict where there are going to be traffic accidents on any given day. The level of complexity is unimaginably great.
Generative AI, Bias, and AI Frameworks and Regulations
GenAI applications reflect many of the biases, errors, and cognitive traps that the average human falls into. And given the lack of transparency, this also means that we can't even understand why a language model is exhibiting bias. At the same time, the public's trust in AI is waning, with surveys showing there is an increasing concern about losing privacy.
Questions with unsatisfactory answers abound:
How do we address AI systems perpetuating existing biases present in their training data, leading to discriminatory outcomes? AI systems require vast amounts of data to work. How is our personal information being collected, stored, and used?
How are AI companies addressing the risk of their technologies being used to create misinformation? AI models require huge computational resources and massive energy consumption - what are doing to mitigate their impact on carbon emissions?
In an attempt to assuage such concerns, enter the era of AI frameworks, standards, and regulation. This can generally be marked with the creation of three new standards: ISO/IEC 42001, the EU AI Act, and the NIST AI Risk Management Framework.
1. ISO/IEC 42001
ISO 42001 is the first AI Management Systems framework to be published. The goal is to allow companies to proactively certify they are using AI safely and establish company-wide guidelines for managing AI applications. The framework directly addresses many of the concerns around AI and transparency, bias, and ethics:
The Documentation of AI Systems & Algorithmic Transparency
Organizations should maintain detailed documentation of their AI algorithms, data sources, and decision-making processes.
Recommendation engines, for example, collect data on user behavior, such as past purchases, search queries, browsing history, and more that is then used by an AI algorithm to generate recommendations for users.
Under ISO 42001, companies that deploy AI-driven recommendation engines (such as Netflix's personalized show/movie recommendations) must document the types of data from consumers it uses, the algorithm's logic, and how recommendations are generated.
Furthermore, AI systems must be designed to provide explanations for their decisions that are understandable to non-experts. For instance, an AI used for loan approval must provide applicants with a clear explanation of the factors that influenced their application decision, such as income and credit score.
Data Privacy and Security
Under ISO 42001, measures to protect data should be integrated into the use of AI. There are many factors to consider before implementing AI into systems and applications.
Furthermore, security measures mapped onto ISO 42001 data privacy and security controls help meet compliance with industry-specific data protection regulations such as HIPAA. Under both HIPAA and ISO 42001, for example, measures an AI-driven health app might take would be to encrypt user data both at rest and in transit and implement strict access controls to protect sensitive health information.
Ethical Principles Controls Under ISO 42001
ISO 42001 controls emphasize accountability and human oversight of AI. Part of this entails a clear assignment of roles and responsibilities for AI system outcomes. As an example, a company could designate a Data Protection Officer repsonsbile for overseeing the ethical use of AI and handling any issues.
AI Frameworks & Continuous Improvement Controls
One of the core tenets of ISO 42001 is continuous improvement.
Organizations should be continuously monitoring AI performance to identify areas for improvement. For instance, a healthcare AI system used for diagnosis should continuously monitor for accuracy and be updated based on the latest medical research.
2. The EU AI Act
The EU AI Act is the world's first comprehensive AI law. It was passed by the EU parliament in March 2024 and will shortly be adopted as EU law. Understanding the implications of this act is critical for businesses, as it directly addresses common concerns about the use of AI:
Risk-Based Classification
The EU AI Act introduces a risk-based classification system to regulate AI systems according to the level of risk they pose to individual users and society more broadly. The aim is to strike a balance between innovation and the need for safety and ethical considerations.
In practice, this means categorizing AI systems into four risk levels: unacceptable risk, high risk, limited risk, and minimal risk. Each category entails specific requirements to address the potential impact of the AI system. More stringent regulations are applied to AI technologies that could significantly affect human rights, safety, and well-being, while allowing a greater degree of flexibility for lower-risk applications.
An AI system controlling autonomous vehicles would be naturally considered high risk and would need to comply with stringent safety standards. Meanwhile, an AI-driven spam filter or an AI being used to help personalize content would be considered minimal risk and face less strict requirements.
Transparency, Accountability, & Data Governance
Organizations must disclose when AI is used and provide transparent information about its functionality. For example, an e-commerce website using a chatbot has to disclose to users that it's an automated system.
The EU AI Act also contains requirements around high-quality data management practices to prevent biases. A real-life example of this is that AI recruitment tools must be trained on diverse and representative datasets, with training data to include a wide range of demographic information to prevent bias against any particular group.
3. NIST AI Risk Management Framework
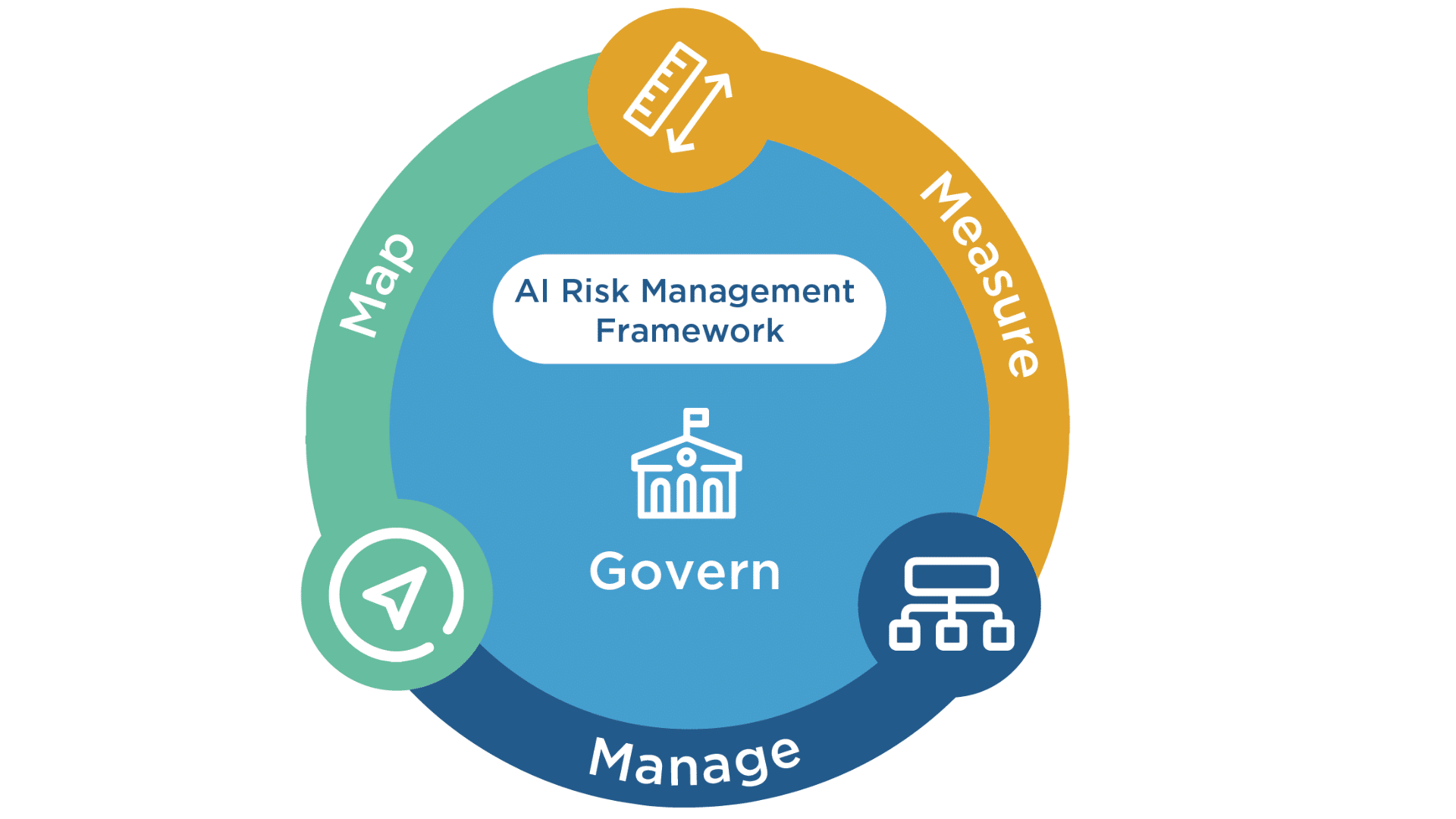
Image Source: NIST AI Risk Management Framework
The NIST AI Risk Management Framework is a voluntary, flexible framework for managing AI-related risks. It focuses on several key areas:
Governance: A Common Core Tenet of AI Frameworks
The role of governance is central under the NIST AI Risk Management Framework. This is unsurprising, as there has been a similar focus in other recent frameworks, such as Version 2.0 of the NIST Cybersecurity Framework with the addition of the NIST governance section.
Company leadership must establish procedures to oversee AI development and use. As an example, a marketing agency could document all of its AI usage policies so that employees understand if/how AI tools should be used for daily tasks such as copywriting, generating images, and social media posts.
Similar to ISO 42001 and the EU AI Act, the NIST AI Risk Management Framework also emphasizes the importance of assigning clear responsibilities for AI risk management. Businesses should designate a team member, such as the head of IT, to oversee AI usage and projects.
Risk Identification
Pinpointing the potential risks and impacts associated with AI systems is another key component of the NIST AI framework. This can take the form of conducting a simple risk assessment. For instance, an online retailer may evaluate the risks of using an AI chatbot for customer service to provide clarity on the following questions:
Are there scenarios in which the AI may fail to understand complex customer queries? How often is this projected to occur, and what would be the impact on customer satisfaction? How often might the chatbot provide incorrect information?
These are important questions to answer.
Tracking Performance Metrics & Bias Assessments
Lastly, the NIST AI framework requires organizations to assess their AI systems regularly and enact corresponding improvements. Companies should develop key performance indicators (KPIs) that are used to measure AI accuracy, performance, and bias.
Specific KPIs obviously vary depending on the industry. Let's take a healthcare provider as an example:
A medical clinic using an AI application for diagnostic support may examine the accuracy rate as a KPI by comparing AI diagnostic results with diagnoses made by human doctors. Another KPI they might assess could be false positive/negative rate - the number of instances where the AI system incorrectly identifies an illness where there is none (false positive) or misses a diagnosis (false negative).
Assessing the reliability and fairness of AI systems is a cornerstone of the three AI frameworks we've gone over in this article. By measuring outcomes, organizations can enable their AI applications to continuously improve and deliver desired results while alleviating concerns from prospects, customers, and partners.

Concluding Thoughts On AI Frameworks
The three AI frameworks discussed in this article share several common goals and approaches:
Each framework emphasizes a risk-based approach that prioritizes risk remediation based on the potential impact of AI systems. Additionally, they each stress the importance of making AI systems transparent and explainable. There is a shared emphasis on the need for ethical AI development to protect individuals and society, and each framework underscores the importance of governance in its own way.
Lastly, ISO 42001, the EU AI Act, and the NIST AI Risk Management Framework all focus on the role of continuous improvement: Adherence to AI frameworks is an ongoing process that involves embedding security functions into daily business operations. AI technologies are swiftly evolving, and organizations must be prepared to pivot their approach and adapt their policies based on change.
By implementing these frameworks, organizations can be better equipped to manage the risks associated with AI, answer their customers' and prospects' concerns about AI, and ensure their use of AI is safe and responsible.
About Rhymetec
Our experts have been disrupting the cybersecurity, compliance, and data privacy space since 2015. We make security simple and accessible so you can put more time and energy into critical areas of your business. What makes us unique is that we act as an extension of your team. We consult on developing stronger information security and compliance programs within your environment and provide the services to meet these standards. Most organizations offer one or the other.
From compliance readiness (SOC 2, ISO/IEC 27001, HIPAA, GDPR, and more) to Penetration Testing and ISO Internal Audits, we offer a wide range of consulting, security, vendor management, phishing testing services, and managed compliance services that can be tailored to your business environment.
Our team of seasoned security experts leverages cutting-edge technologies, including compliance automation software, to fast-track you to compliance. If you're ready to learn about how Rhymetec can help you, contact us today to meet with our team.
Interested in reading more? Check out other articles on our blog:
- AI In Cyber Defense: Pioneering The Future of Security
- Security vs. Compliance? A False Dichotomy
- How AI Is Disrupting Our Industry, and What We Can Do About It